Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove PERL File Extension Ransomware?
Readers recently started to report the following message being displayed when they boot their computer:
!!! IMPORTANT INFORMATION !!!
All your files are encrypted.
Decrypting of your files is only possible with the private key, which is on our secret server.
To receive your private key follow one of the links:
1. http://uk74sqtx2ynr2nzb.onion.gq/?id=[Redacted] 2. http://uk74sqtx2ynr2nzb.onion.nu/?id=[Redacted] 3. http://uk74sqtx2ynr2nzb.onion.cab/?id=[Redacted] 4. http://uk74sqtx2ynr2nzb.onion.to/?id=[Redacted]
If all of this addresses are not available, follow these steps:
1. Download and install Tor Browser: https://www.torproject.org/download/download-easy.html
2. After a successful installation, run the browser and wait for initialization.
3. Type in the address bar: uk74sqtx2ynr2nzb.onion/?id=[Redacted] 4. Follow the instructions on the site.
!!! Your personal identification ID: [Redacted] !!!
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
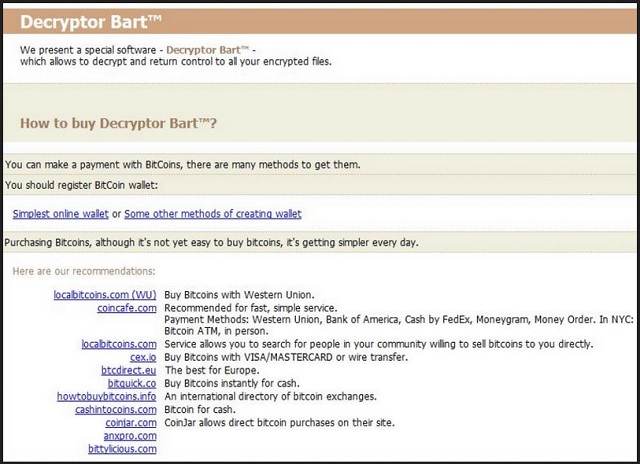
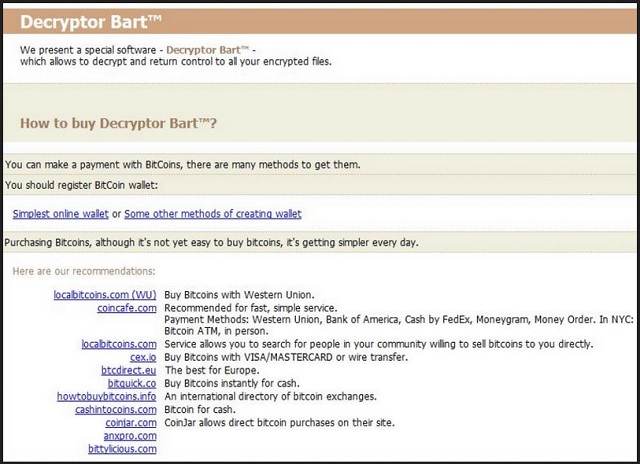
The PERL File ransomware is perceived as the third version of the Bart ransomware. And, though, some things have changed, it’s not so different from its predecessors. As you might have guessed, the name of the latest Bart variant derives from the extension it adds to each file. After encryption, you find each picture, video, document, etc., with an added .perl extension. For example, if you had a song called “best,” you’ll find it as “best.perl.” And, once ‘perl’ gets added to your files, that’s it. The encryption is complete, and your files are rendered inaccessible. You cannot open them anymore. And, moving or renaming the won’t help. They’re locked. The only way to free them, and make use of them once more, is with a unique key. If you want your data back, you have to pay ransom. If you do, the kidnappers send you your decryption key. And, after you apply it, your files are no longer under PERL’s control. Supposedly. That’s a hypothetical scenario, since you have NO guarantees that your compliance helps. None. In fact, from what we’ve established, it only makes your situation worse. When dealing with a ransomware tool, you shouldn’t reach out to the people behind them. Don’t contact them in any way. Don’t email them, call them, nothing! And, above all, do NOT transfer funds to them! These are extortionists. Cyber criminals with agendas that are questionable, to say the least. Do you believe that if you follow their demands, they’ll keep their promises? Don’t be naive. They seek monetary gain. They don’t care about you or your data. Once they get your money, chances are, they WILL double-cross you. The odds are not in your favor. So, as difficult as it may seem, don’t follow their instructions. Don’t comply. Say goodbye to your data. It’s far better to lose your files than the alternative you face should you comply.
How did I get infected with?
It may seem like the PERL file ransomware just showed up one day, and went to work, but that’s not the case. There was a lot leading up to your files’ encryption. Like, you installing the ransomware yourself. Oh, yes. You agreed to install the nasty infection. It inquired whether you consent to allow it into your PC, and you did. Ransomware tools are bound to seek user’s permission. Your permission. They have to get it before they install themselves. In other words, if your files get locked with the ‘perl’ extension, it’s because you installed the PERL ransomware. And, you probably don’t remember doing it. That’s because the tool doesn’t come out in the open, and seek access. Oh, no. It does it in the sneakiest way possible. It turns to every trick in the book. Like, freeware, bogus updates, spam email attachments, corrupted links, etc. But there’s one key ingredient without which it cannot succeed in its sneakiness. And, that’s your carelessness. Ransomware programs rely on your distraction, naivety, and haste. So, don’t provide them. Instead, be extra vigilant and thorough. Take your time to do your due diligence. Sometimes even a little extra attention today can save you a ton of troubles tomorrow.
Why is PERL File Extension dangerous?
Just like the other Bart variants, the PERL infection encrypts your data using the RSA-4096 cipher. And, make no mistake. It targets everything. All your data is under fire. Nothing is beyond the tool’s reach as it distinguishes between over 140 distinct file types. So, once it slithers into your PC, it locks everything. After it’s done, and the ‘perl’ extension gets added, it displays its demands. They’re just as outlandish as those made by its predecessors. The tool asks for 3 Bitcoins, or about 2000 dollars, as ransom payment. As incentive, it threatens to permanently delete files if you attempt something cheeky. Like, trying to decrypt your data yourself. The tool claims that once you pay up, it will send you a decryption key. With that key, you can free your files. But, here’s the thing. The key remove the encryption. It does not remove the infection itself. So, the ransomware will still be there. And, what’s to stop it from striking again an hour after decryption? Or, a day? A week? Nothing. The infection is free to encrypt your data any time it so chooses, and you’ll be back to square one. Only this time, you’ll have less money. And, what’ worse, your privacy will be exposed. Think about it. When you transfer the ransom payment, you leave your personal and financial details. And, the people behind the infection can access them. Are you okay with that? Malicious individuals having your private life at their disposal? Don’t allow that to happen. Don’t pay the ransom. Just forsake your files. After all, files are not as important as privacy. If you think otherwise, by all means, comply. Pay these people, and take your chances. But you won’t like the outcome. Make the safer, wiser choice. Pick privacy over pictures. Files are replaceable. Can you say the same about your private life?
PERL File Extension Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover PERL File Extension Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with PERL File Extension encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate PERL File Extension encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.