Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
This article is describing how you can make changes of your Windows Registry.
Additional information on how to view and modify the registryis available in the online Help topic in the Registry Editor (Regedit.exe). It is very IMPORTANT that you make a backup copy of the registry files (System.dat and User.dat) prior to trying anything with the registry.
WARNING: Using the Registry Editor incorrectly can cause serious troubles that may require you to reinstall your Operating System. There is no guarantee, that problems resulting from the incorrect use of Registry Editor, can be solved. Use Registry Editor at your own risk!
It is essential to make a backup of the Windows Registry before you modify anything. You can backup the entire Registry by copying System.dat and User.dat or by exporting a single section of the Registry using REGEDIT.
The Registry has a hierarchal structure, although it looks complicated the structure is similar to the directory structure on your hard disk, with Regedit being similar to Windows Explorer.Each main branch (denoted by a folder icon in the Registry Editor, see figure 1)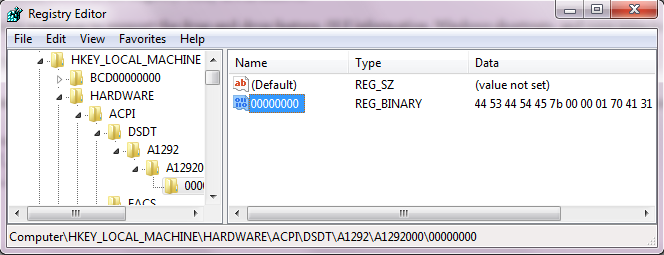 is called a Hive, and Hives contains Keys. Each key can contain other keys (sometimes referred to as sub-keys), as well as Values. The values contain the actual information stored in the Registry.
is called a Hive, and Hives contains Keys. Each key can contain other keys (sometimes referred to as sub-keys), as well as Values. The values contain the actual information stored in the Registry.
There are six main branches, each containing a specific portion of the information stored in the Registry. They are as follows:
- HKEY_CLASSES_ROOT – This branch contains all of your file association mappings to support the drag-and-drop feature, OLE information, Windows shortcuts, and core aspects of the Windows user interface.
- HKEY_CURRENT_USER – This branch links to the section of HKEY_USERS appropriate for the user currently logged onto the PC and contains information such as logon names, desktop settings, and Start menu settings.
- HKEY_LOCAL_MACHINE – This branch contains computer specific information about the type of hardware, software, and other preferences on a given PC, this information is used for all users who log onto this computer.
- HKEY_USERS – This branch contains individual preferences for each user of the computer, each user is represented by a SID sub-key located under the main branch.
- HKEY_CURRENT_CONFIG – This branch links to the section of HKEY_LOCAL_MACHINE appropriate for the current hardware configuration.
- HKEY_DYN_DATA – This branch points to the part of HKEY_LOCAL_MACHINE, for use with the Plug-&-Play features of Windows, this section is dymanic and will change as devices are added and removed from the system.
Each registry value is stored as one of five main data types:
- REG_BINARY – This type stores the value as raw binary data. Most hardware component information is stored as binary data, and can be displayed in an editor in hexadecimal format.
- REG_DWORD – This type represents the data by a four byte number and is commonly used for boolean values, such as “0” is disabled and “1” is enabled. Additionally many parameters for device driver and services are this type, and can be displayed in REGEDT32 in binary, hexadecimal and decimal format, or in REGEDIT in hexadecimal and decimal format.
- REG_EXPAND_SZ – This type is an expandable data string that is string containing a variable to be replaced when called by an application. For example, for the following value, the string “%SystemRoot%” will replaced by the actual location of the directory containing the Windows NT system files. (This type is only available using an advanced registry editor such as REGEDT32)
- REG_MULTI_SZ – This type is a multiple string used to represent values that contain lists or multiple values, each entry is separated by a NULL character. (This type is only available using an advanced registry editor such as REGEDT32)
- REG_SZ – A string value, normally stored and exposed in UTF-16LE (when using the Unicode version of Win32 API functions), usually terminated by a null character.
Other data types not available through the standard registry editors include:
- REG_DWORD_LITTLE_ENDIAN – A 32-bit number in little-endian format.
- REG_DWORD_BIG_ENDIAN – A 32-bit number in big-endian format.
- REG_LINK – A Unicode symbolic link. Used internally; applications should not use this type.
- REG_NONE – No type (the stored value, if any)
- REG_QWORD – A 64-bit number.
- REG_QWORD_LITTLE_ENDIAN – A 64-bit number in little-endian format.
- REG_RESOURCE_LIST – A device-driver resource list.
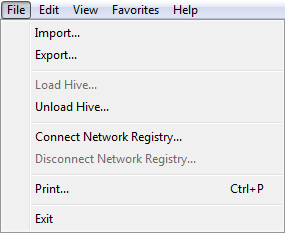
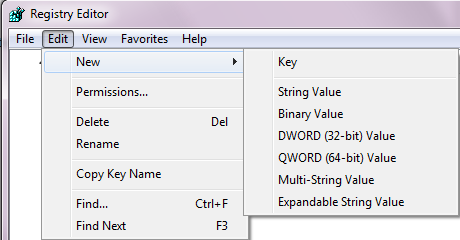
Regedit has some of the same menus that are so familiar throughout Windows. The menu bar can be seen near the top of Figure 1. Below there are the two most commonly used menus.
figure 2 figure 3
The File menu has the functions “Import” and “Export” that can be used to backup and restore individual Registry keys with REG files. The next section will have more detail about this important function.
As you would expect, the “Edit” menu is where commands are located for making changes to the Registry. Keys and values can be deleted, added, or renamed. (Permission settings on keys can also be edited but that is an advanced subject beyond our scope.) Another two very useful functions are “Find…” and “Find Next”. The Registry has thousands of keys and these search functions are very necessary. Unfortunately, the search function cannot find binary values or REG_DWORD entries. It searches key names, value names, and string data.
The Edit menu also contains a useful entry “Copy Key Name” that sends the path of the key to the clipboard, Since path names can be quite long, this can be very useful.
How to edit the Windows Registry without opening regedit.exe
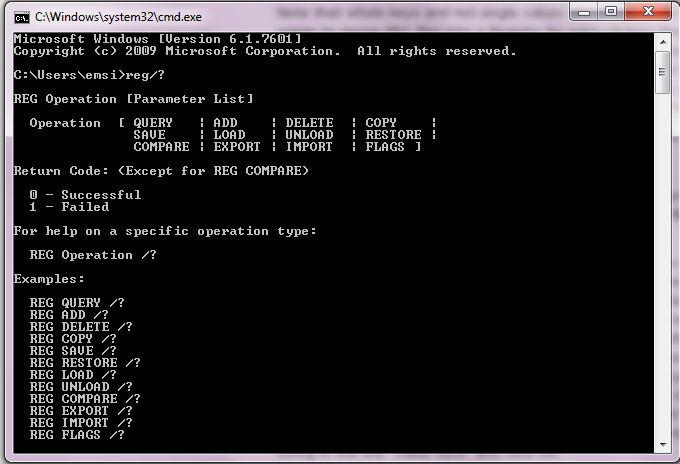
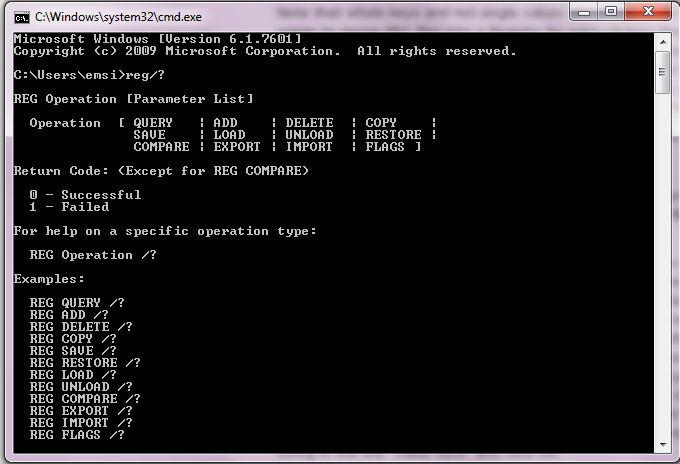
You can edit the Windows Registry with the help of Console Registry Tool or reg.exe. Reg.exe is a command-line utility with which you can perform almost all the task which you otherwise can with regedit.exe.
Reg.exe can be useful when you want to quickly make a change to the Windows Registry without opening registry editor and moreover and has the additional facility of being directly usable in scripts.
To run the reg.exe, open cmd, type reg /? and hit Enter. This will show you the parameter list, syntax & the return codes.
Read, Set or Delete registry keys and values, save and restore from a .REG file.
Syntax:
REG QUERY [ROOT\]RegKey /v ValueName [/s]
REG QUERY [ROOT\]RegKey /ve --This returns the (default) value
REG ADD [ROOT\]RegKey /v ValueName [/t DataType] [/S Separator] [/d Data] [/f]
REG ADD [ROOT\]RegKey /ve [/d Data] [/f] -- Set the (default) value
REG DELETE [ROOT\]RegKey /v ValueName [/f]
REG DELETE [ROOT\]RegKey /ve [/f] -- Remove the (default) value
REG DELETE [ROOT\]RegKey /va [/f] -- Delete all values under this key
REG COPY [\\SourceMachine\][ROOT\]RegKey [\\DestMachine\][ROOT\]RegKey
REG EXPORT [ROOT\]RegKey FileName.reg
REG IMPORT FileName.reg
REG SAVE [ROOT\]RegKey FileName.hiv
REG RESTORE \\MachineName\[ROOT]\KeyName FileName.hiv
REG LOAD FileName KeyName
REG UNLOAD KeyName
REG COMPARE [ROOT\]RegKey [ROOT\]RegKey [/v ValueName] [Output] [/s]
REG COMPARE [ROOT\]RegKey [ROOT\]RegKey [/ve] [Output] [/s]
Key:
ROOT :
HKLM = HKey_Local_machine (default)
HKCU = HKey_current_user
HKU = HKey_users
HKCR = HKey_classes_root
ValueName : The value, under the selected RegKey, to edit.
(default is all keys and values)
/d Data : The actual data to store as a "String", integer etc
/f : Force an update without prompting "Value exists, overwrite Y/N"
\\Machine : Name of remote machine - omitting defaults to current machine.
Only HKLM and HKU are available on remote machines.
FileName : The filename to save or restore a registry hive.
KeyName : A key name to load a hive file into. (Creating a new key)
/S : Query all subkeys and values.
/S Separator : Character to use as the separator in REG_MULTI_SZ values
the default is "\0"
/t DataType : REG_SZ (default) | REG_DWORD | REG_EXPAND_SZ | REG_MULTI_SZ
Output : /od (only differences) /os (only matches) /oa (all) /on (no output)
Notes:
Any of the above commands can be run against a remote machine by adding \\MachineName to the command line, assuming the Remote Registry Service is running.
Registry data stored under HKCU will be visible and writable by the currently logged in user.
Registry data stored under HKLM will be visible to all users and writable by administrators.
REG RESTORE has a tendency not to work, possibly due to firewall issues, Export and Import are much more reliable.
Backslash characters
The REG command will interpret \ as an escape for the character that immediately follows it.
To include a quote mark (“) in the data, prefix it with the escape character e.g. Here is \” a quote
This can cause problems with quoted directory paths because \” at the end of the line will be escaped.
To save a directory path with a trailing backslash (\) requires adding a second backslash to ‘escape the escape’
so for example instead of “C:\My Docs\” use “C:\My Docs\\”
Activate
To activate registry changes in HKEY_CURRENT_USER without logging off:
RUNDLL32.EXE, USER32.DLL,UpdatePerUserSystemParameters ,1 ,True
Examples
Adding and querying data:
REG QUERY HKCU\Console\ REG QUERY HKCU\Console /v ScreenBufferSize
REG ADD HKCU\Software\SS64 /v Sample /d "some test data" REG QUERY HKCU\Software\SS64 /v Sample REG ADD HKLM\Software\DiLithium /v WarpSpeed /t REG_BINARY /d ffffffff REG QUERY HKLM\Software\DiLithium /v WarpSpeed
Find the location of the Start Menu folder:
REG QUERY “HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders” /v “Start Menu”
List IE Proxy overrides:
REG QUERY “HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings” /v ProxyOverride
Save a directory/registry path that ends with a backslash:
Set _reg=HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\SS64.EXE\ Set _prog=C:\Program Files\SS64 App\ REG ADD "%_reg%\" /f /v "SS64.EXE" /t REG_SZ /d "%_prog%\"
Save a REG_Expand_SZ value of %systemroot%
REG ADD HKLM\Software\SS64 /v Path /t REG_EXPAND_SZ /d ^%systemroot^% REG COPY \\Wks580\HKCU\Software\SS64 HKCU\Software\SS64 REG COPY HKCU\Software\SS64 HKCU\Software\SS64Copy REG EXPORT HKCU\Software\SS64 C:\MyReg.REG REG IMPORT C:\MyReg.REG REG SAVE HKCU\Software\SS64 C:\MyRegHive.hiv REG RESTORE \\Wks580\HKCU\Software\SS64 C:\MyRegHive.hiv
Run a script at first logon (Run Once) to do this we edit the Default User profile by temporarily loading it as ZZZ:
REG LOAD HKU\ZZZ "C:\Documents and Settings\Default User\NTUSER.DAT" REG ADD HKU\ZZZ\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce /v newUserProfile /t REG_EXPAND_SZ /d "D:\setup.cmd" /f REG UNLOAD HKU\ZZZ
More examples are available via: REG QUERY /? REG ADD /? etc
And so we come to the end of unveiling of the mysteries of the Registry. Go ahead and edit, but be careful.