Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove .Nbes File Extension Ransomware?
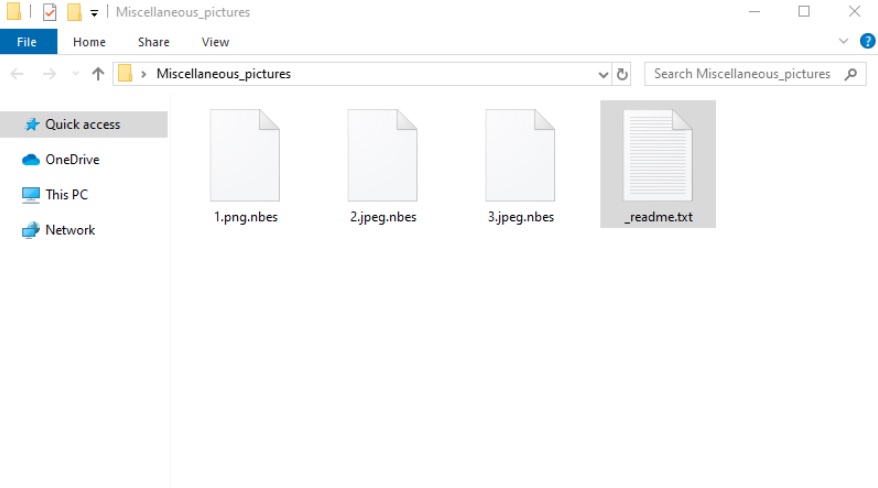
Nbes virus is a name of a ransomware malware. These programs follow the same design, and act in a pretty much identical manner. And, all these applications are an utter plague on your system. The ransomware menace uses trickery to gain access to your PC. Then, once its in, corrupts it through and through. Nbes uses AES cryptography to encrypt every file you have. Everything you keep on your computer gets locked. Documents, pictures, music, videos. Nothing escapes the infection’s reach. The tool attaches a special “.Nbes”extension at the end of each of your files. And, once it’s in place, that’s it. Your files get rendered useless. You cannot open them, and any action in attempt to salvage them is pointless. The only option for release, the ransomware leaves you, is payment. It states so in the ransom note it leaves you. It’s a READ_ME.txt file, you find in every affected folder, as well as on your Desktop. Its contents are rather standard. The note clues you into your current situation. It states your system suffers a ransomware infection. And, if you want to remove the encryption it imposed, you must pay a ransom. Do NOT pay these people a dime! Even if the requested amount wasn’t so outrageous, experts still advise against payment! It only worsens your predicament. Heed their word, and discard your data. Say goodbye to your files, and move on. Next time, make back-ups, so you don’t suffer such a loss. It may seem like a harsh advice, but it’s the best course of action, you can take.
How did I get infected with?
Ransomware tools like Nbes are rather sneaky. They’re deceptive and invasive. More often than not, you don’t realize they’re on your computer until they strike. And, they manage that via trickery and deceit. Though, these tools need user’s permission to get it, they still tend to enter undetected. How? Well, they fool you. They prey on your carelessness, and manage to dupe you. You agree to let them in without even knowing it. And, that’s because you’re careless at a time you should be extra cautious. For example, when you install supposed updates or tools. Freeware and fake updates are among the most common means of infiltration. But whichever method, the tool turns to, it’s useless without your carelessness. After all, if you’re thorough enough, you can catch it in the act. And, foil its attempts at slithering in. If you give into naivety and haste, however, don’t get surprised to find malware on your PC. And, the ransomware kind are, arguably, the worst to get stuck with. If you want to keep Nbes away from your system, be careful. Try to be more vigilant when dealing with freeware, or anything else you allow into your system. Due diligence is imperative in the fight against infection. Since they prey on carelessness, don’t grant it! Always choose caution over distraction, naivety, and haste. You won’t regret it.
Why is .Nbes File Extension dangerous?
Once Nbes locks your data, you’re in quite the conundrum. You face a choice. To pay or not to pay. And, we say: Don’t. Do not pay these people anything for you WILL regret making that decision. And, here’s why. Think about what happens after you transfer the money. You rely on cyber criminals to go through with what they promised. Do you think it’s wise to wait on extortionists to keep their end of the bargain? It’s rather unlikely that they will. But, even if they do send you something, following payment, don’t get your hopes up. What if the decryption key, they gave you, doesn’t work? What’s if it’s the wrong one? And, even if it’s the right key, what happens next? You apply it, and your files get unlocked. And, then? The decryption key removes the encryption, not the encrypter. Nbes still lurks somewhere on your computer. You have zero guarantees that it won’t strike again. It could be an hour after decryption, a day, a week, a month. It can happen. And, if it does as it likely will, will you pay again? How much money are you prepared to throw at these people before you accept the inevitable? That your data is just not worth it. Not to mention, payment equals you giving access to your privacy to strangers. Yes, when you transfer the ransom, you private personal and financial details. Information, which the cyber criminals can then access and exploit. Needless to say, that’s not a desirable outcome. Protect your privacy from the clutches of cyber kidnappers! When you find Nbes has taken over your system, cut your losses. Discard your data in the name of your private life. After all, privacy is irreplaceable. And, files are.
.Nbes File Extension Removal Instructions
STEP 1: Kill the Malicious Process
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 3: Locate Startup Location
STEP 4: Recover .Nbes File Extension Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with .Nbes File Extension encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate .Nbes File Extension encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software like Data Recovery Pro to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.


