Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove .Gesd File Extension Ransomware?
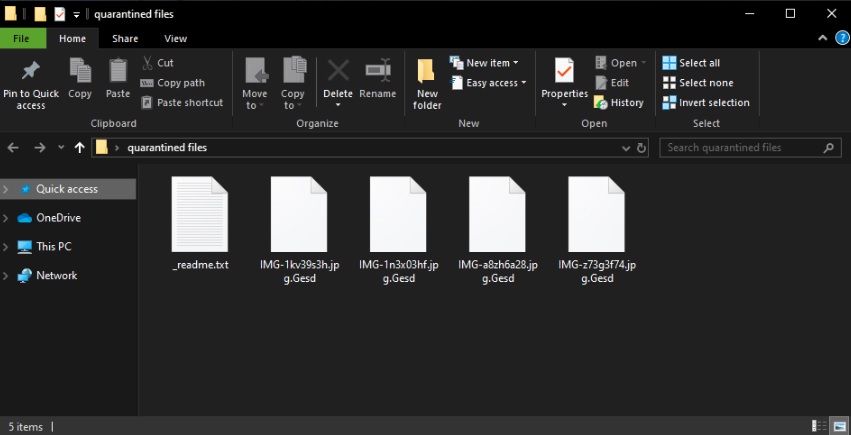
File .Gesd virus falls under the category ransomware. It is a sophisticated malware that targets your files. Virus sneak into your PC undetected and spread corruption throughout your entire system. It alters the setting, modify the registry, and begin the process hazardous. This, of course, occur without any noticeable symptoms. You can not catch a virus in time to limit corruption. .Gesd ransomware designed for stealth. Without triggering the alarm, detection and user-generated destroying data. This virus after your pictures, music, databases, archives, documents. This malicious ransomware uses advanced encryption mechanism to lock the file and to restrict access to you. You can still see the icon of your files, but can not view or edit them. Everything that has a “.Gesd” extension can not be used. The only way to get your data back pay ransom amazing. That is the nature of the ransomware. It spoils everything and promises a solution if you follow the demands of its operator. Do not give up! Do not open your wallet. You deal with criminals. These people are famous because of two intersections of their victims. They promise a solution, but they rarely give results. Do not act! Use your time. Consider throwing your files. If you have a backup, you can use it to restore your data. Before you try any of the operation, though, remove the virus!
How did I get infected with?
Links, false Corrupted updates, malicious websites, pirated software. There are myriads of virus distribution ways. Viruses such as .Gesd ransomware, however, tend to browse the web hidden in spam messages. It is true! The good old spam emails are still used to distribute viruses. Their system, however, is not as simple as it was. Hackers use not only corrupted files, but also malicious links. They use deceptive language to trick you into clicking. Do not make their job easier. A little attention can save you an avalanche of problems. Treat all unsolicited messages as potential threats. Whether an e-mail or instant message, always take a minute to verify the sender. If, for example, you receive an unexpected email from an organization, visit their official website. Compare email addresses that are listed in the suspect. If they do not match, remove the Pretender. You can also enter suspicious addresses into a search engine. If they were used for dubious activities, someone could have complained online.

Why is .Gesd File Extension dangerous?
.Gesd ransomware is a nightmare. As soon as it sneaks into your computer, corruption follows. The virus wastes no time and encrypts your data. Databases, documents, pictures. There are no immune files. The virus locks everything and makes your PC as good as useless. You can’t download or create new files as they get locked immediately. You can only browse the Web. That is dangerous, though. The virus lurks in the shadows. You can’t trust your compromised PC with sensitive operations such as online banking. The virus, of course, promises a solution if you comply with the hackers’ demands. Paying, however, is not advisable. Don’t give into naivety. These experienced criminals know what they are doing. The hackers demand Bitcoin. This currency is untraceable. Once you transfer the money, they are gone. You can’t ask for a refund if something goes wrong. And that is inevitable. Practice shows that hackers tend to ignore the victims once they receive the ransom. There are cases when the victims paid just to be blackmailed for more. There are also instances when the victims received nonfunctional decryption tools. Don’t waste your time and money. Paying the ransom won’t accomplish anything. You will get nothing in return! Your best course of action is the immediate removal of the virus. Find where .Gesd ransomware hides and delete it upon detection. That’s your best and only course of action!
.Gesd File Extension Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 4: Recover .Gesd File Extension Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with .Gesd File Extension encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate .Gesd File Extension encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software like Data Recovery Pro to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.