Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
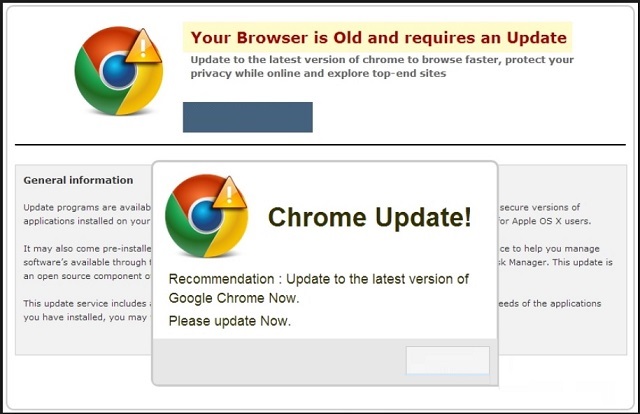
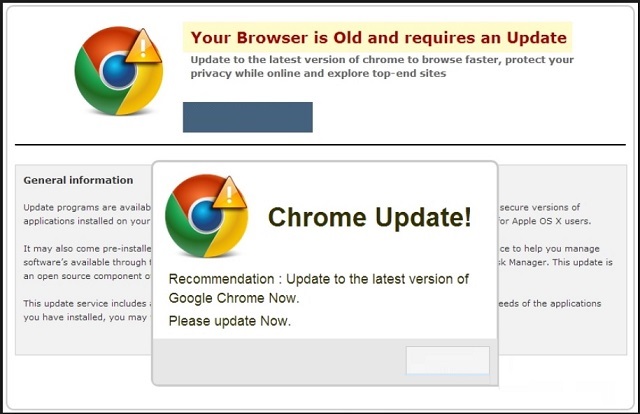
Can’t Remove Chrome_update.bat Scam? This page includes detailed Chrome_update.bat Removal instructions!
The Chrome_update.bat pop-up is part of the PUP family. It’s quite an extensive one, and it harbors many cyber threats. The one, you’re currently stuck with, mustn’t be ignored. The pop-up begins to take over your screen when there’s an infection, lurking on your PC. It could be an adware, a browser hijacker, or any similar nuisance. Chrome_update.bat is associated with an adware-type application. And, that’s bad news. PUP adware is a dangerous threat. Don’t underestimate the hassles it can (and will) put you through! Sch programs are intrusive and cause an abundance of damages. They put you through cyber hell and threaten your privacy. Oh, yes. They not only disrupt your browsing on a daily basis but also spy on you. Adware keeps track of your online habits. It collects data from you. Data, which it later sends to unknown third parties. That’s right. It hands your personal and financial information to strangers. People with questionable agendas. The question is, are you going to allow that?
How did I get infected with?
The Chrome_update.bat pop-up doesn’t simply show up out of the blue one day. It sure seems that way, but things are not as they appear. If the pop-up is displayed, there has to be an infection on your PC, forcing it on you. Otherwise, it cannot take over your screen. So, it’s safe to assume there’s a PUP on your PC. If there weren’t, you wouldn’t be in your current predicament. But how do you suppose the infection got into your system? After all, adware-type applications require your sign of approval to enter. In other words, you have to permit their installation. And, they have to ask for it. But don’t think they just come out in the open and do it. Oh, no! They do it with finesse through slyness and subtlety. More often than not, via the old but gold means of infiltration. That includes using freeware as a shield to lurk behind. Or, hitching a ride with spam email attachments, corrupted links, or sites. Also, adware can pretend to be a bogus update. Like, Java or Adobe Flash Player. But whichever method it chooses to turn to, it relies on your carelessness. If you’re not careless, you significantly increase your chances of catching it trying to slither in. And, consequently, preventing it from doing so. Be more thorough and vigilant! Don’t give into naivety and haste. Even a little extra attention goes a long way.
Why are these ads dangerous?
If Chrome_update.bat pops up on your screen, you’re in trouble. Brace yourself for a bad time as there’s adware on your PC. It snuck in undetected, and the pop-up is its way of revealing its presence. That’s a warning. And, it’s best not to ignore it but act on it! As soon as Chrome_update.bat appears, accept your system is no longer infection-free. And, do your best to rectify that! The sooner you find and delete the cyber threat, the better. Adware-type programs are a menace. They’re a plague to your browsing and a threat to your privacy. As was already mentioned, they spy on you. They steal your private information and hand it to unknown individuals. Imagine strangers having access to your personal and financial details. The repercussion will hardly be of a pleasant variety. And, apart from that quite severe threat, you’ll also face an entire myriad of other ones. Issues, which are considered minor but are no less harmful and annoying. You’ll witness a flood of pop-up advertisements. An ever-flowing waterfall will come your way each time you surf the web. You’ll get redirected to unreliable websites, which pose a malware risk. Your computer’s performance will slow down to a crawl. Your system will begin to crash all the time. Think about what you’ll gain from leaving the adware on your PC. Nothing positive! Nothing but headaches and grievances. Adware applications are invasive and harmful. They’re not worth keeping. The same goes for the one, which is forcing Chrome_update.bat on you. Do NOT allow it to stay even a second longer after you become aware of its presence. Delete it upon detection! Avoid the unpleasantness! You won’t regret it, and your future self will be thankful.
How Can I Remove Chrome_update.bat Virus?
If you feel technical enough you may proceed with Manual Virus Removal
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
If you perform exactly the steps below you should be able to remove the infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with the Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate the Virus startup location
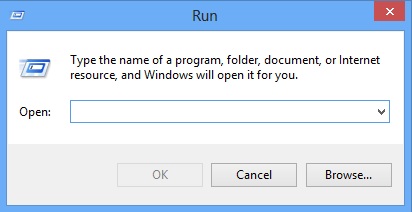
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4 : Uninstall unknown programs from Your Computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command
Type “Appwiz.cpl”
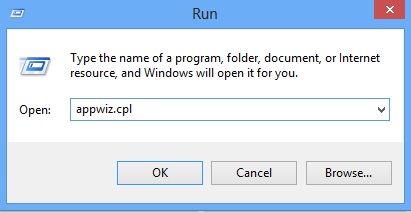
Locate the any unknown program and click on uninstall/change. To facilitate the search you can arrange the programs by date. review the most recent installed programs first. In general you should remove all unknown programs.
STEP 5 : Remove add-ons and extensions from Chrome, Firefox or IE
Remove from Google Chrome
- In the Main Menu, select Tools—> Extensions
- Remove any unknown extension by clicking on the little recycle bin
- If you are not able to delete the extension then navigate to C:\Users\”computer name“\AppData\Local\Google\Chrome\User Data\Default\Extensions\and review the folders one by one.
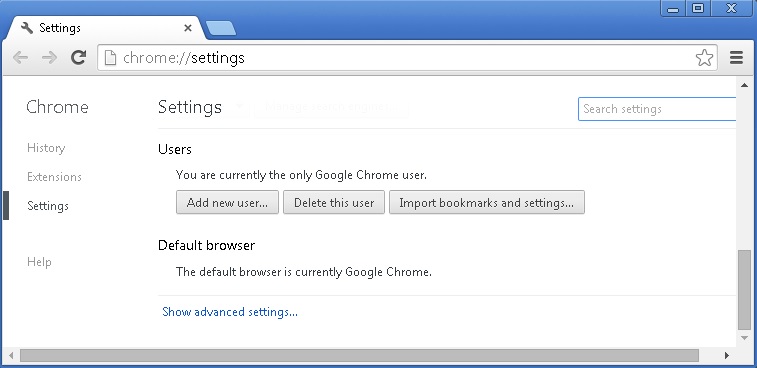
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
- If you are using the latest chrome version you need to do the following
- go to settings – Add person
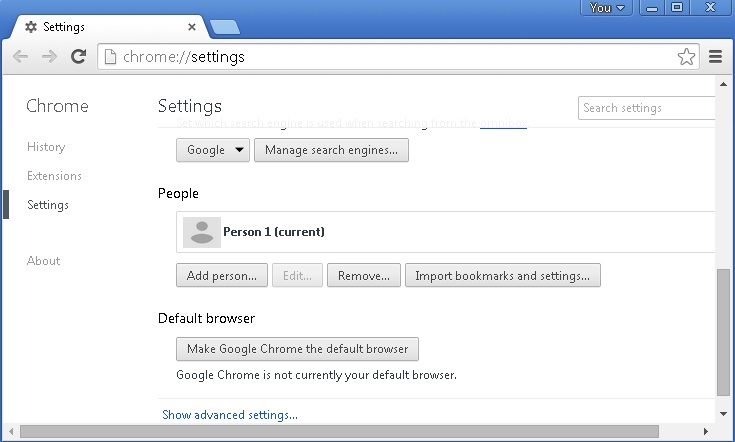
- choose a preferred name.
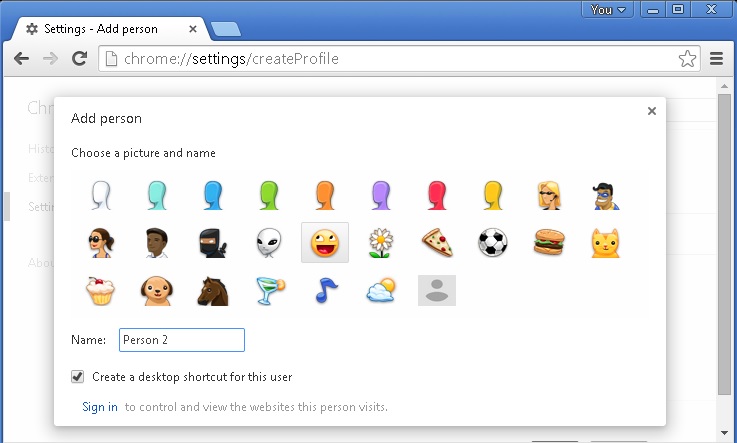
- then go back and remove person 1
- Chrome should be malware free now
Remove from Mozilla Firefox
- Open Firefox
- Press simultaneously Ctrl+Shift+A
- Disable and remove any unknown add on
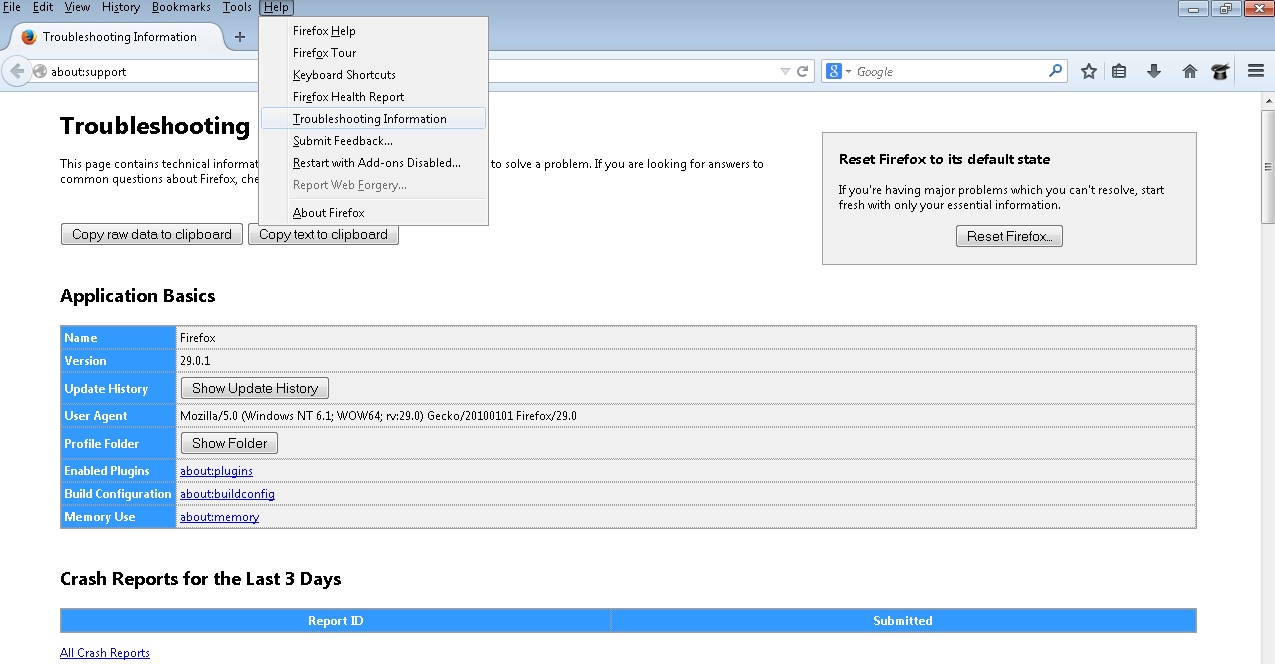
- Open the Firefox’s Help Menu
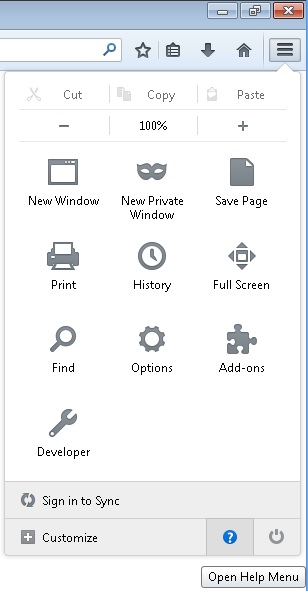
- Then Troubleshoot information
- Click on Reset Firefox
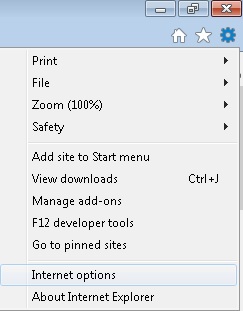
Remove from Internet Explorer
- Open IE
- On the Upper Right Corner Click on the Gear Icon
- Go to Toolbars and Extensions
- Disable any suspicious extension.
- If the disable button is gray, you need to go to your Windows Registry and delete the corresponding CLSID
- On the Upper Right Corner of Internet Explorer Click on the Gear Icon.
- Click on Internet options
- Select the Advanced tab and click on Reset.
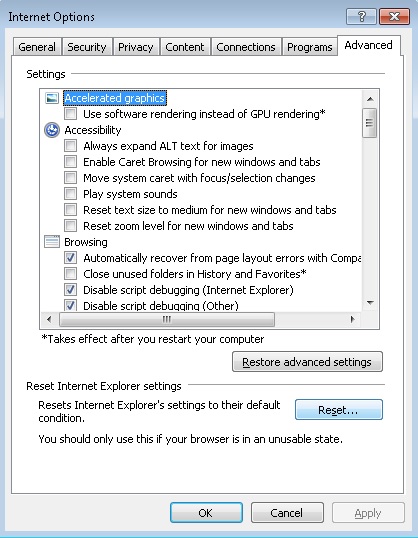
- Check the “Delete Personal Settings Tab” and then Reset
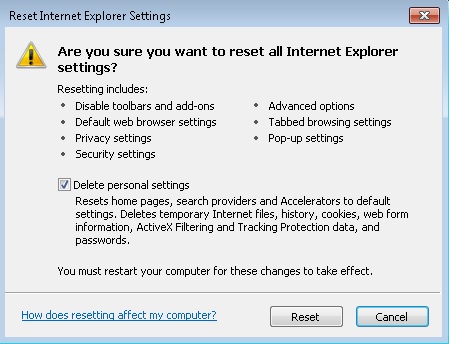
- Close IE
STEP 6: Make sure your Windows HOSTS file is clean
- open your explorer and Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:

If you are uncertain about the IPs below “Localhost” contact us in out google+ profile and we will try to help you.
STEP 7: Check your internet connection settings
- Right-click on the active Network Adapter, Click on Properties
- Navigate to Internet Protocol Version 4 (ICP/IP), click Properties.
- Click on Advanced and then navigate to the DNS TAB. The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
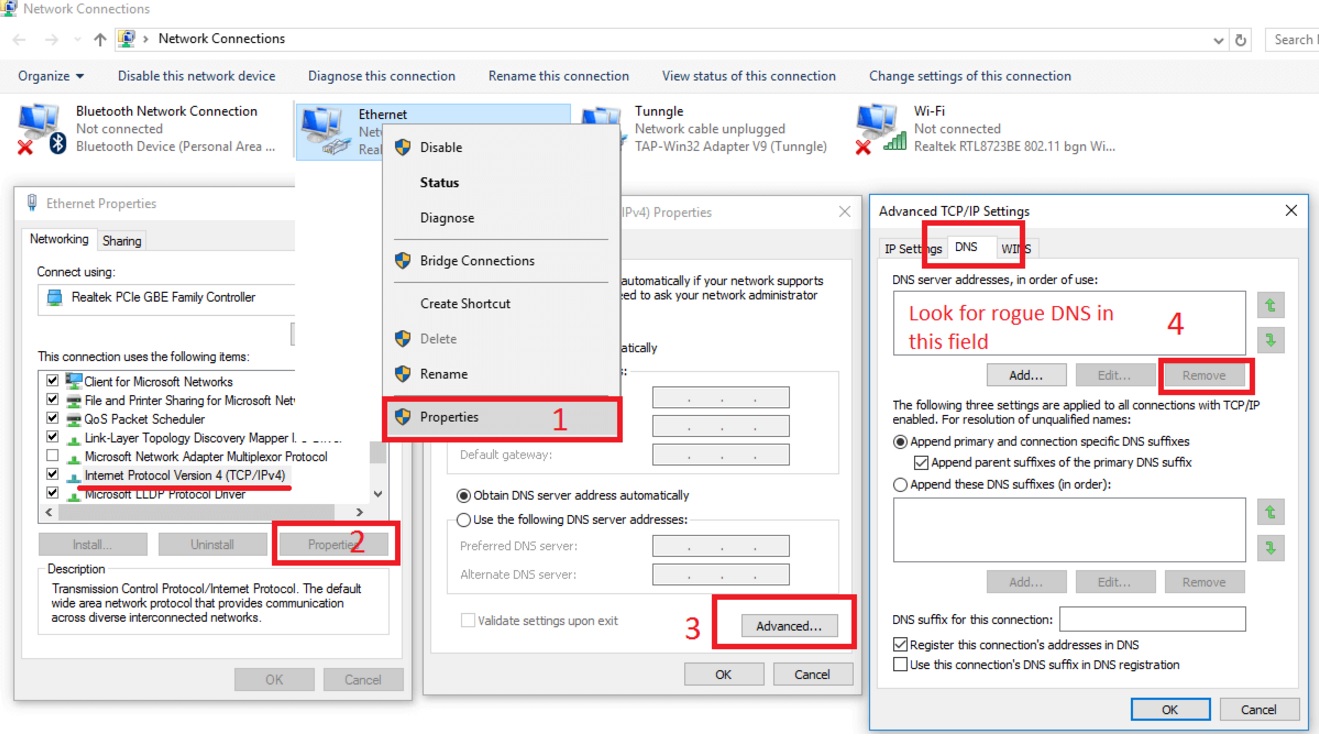
Double check your proxy settings as the malware is capable of modifying them.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for example, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
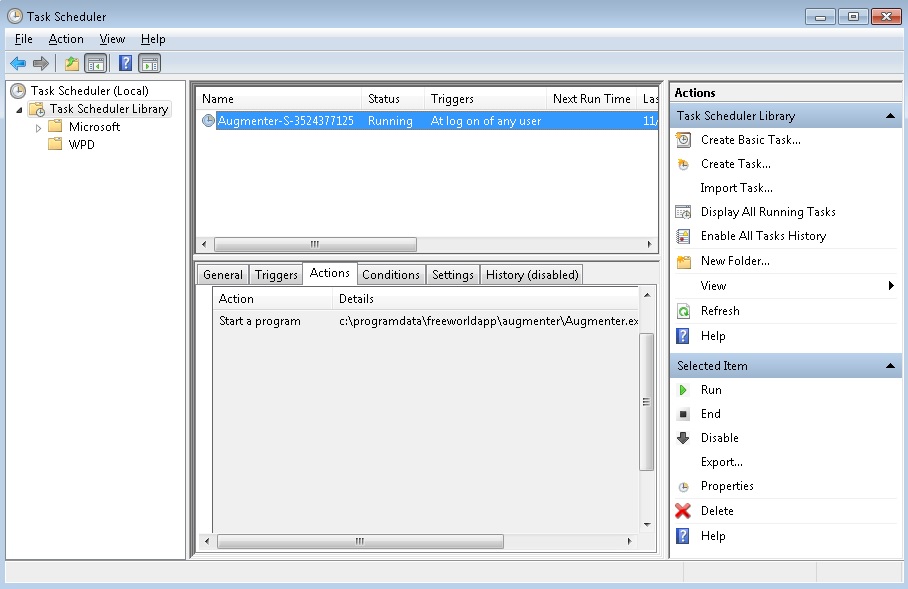
STEP 8: Check your Scheduled Tasks
- Open your windows task scheduler and delete any suspicious program. Usually, adware applications hide their droppers in here. Even if you remove the whole infection from the system files – the dropper will regenerate everything and the nightmare will start again.
Step 9: Check for Virus Leftovers
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify any registry leftovers or temporary files and to prevent this from happening again.