Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Zeta Ransomware?
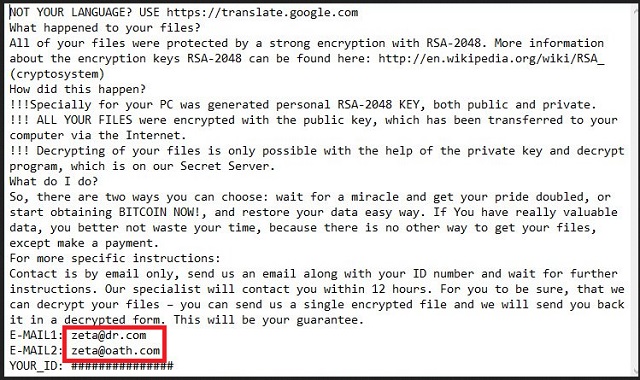
Reader recently start to report the following message being displayed when they boot their computer:
NOT YOUR LANGUAGE? USE https://translate.google.com
What happened to your files?
All of your files were protected by a strong encryption with RSA-2048. More information about the encryption keys RSA-2048 can be found here: http://en.wikipedia.org/wiki/RSA_(cryptosystem)
How did this happen?
!!!Specially for your PC was generated personal RSA-2048 KEY, both public and private.
!!! ALL YOUR FILES were encrypted with the public key, which has been transferred to your computer via the Internet.
!!! Decrypting of your files is only possible with the help of the private key and decrypt program, which is on our Secret Server.
What do I do?
So, there are two ways you can choose: wait for a miracle and get your pride doubled, or start obtaining BITCOIN NOW!, and restore your data easy way. If You have really valuable data, you better not waste your time, because there is no other way to get your files, except make a payment.
For more specific instructions:
Contact is by email only, send us an email along with your ID number and wait for further instructions. Our specialist will contact you within 12 hours. For you to be sure, that we can decrypt your files – you can send us a single encrypted file and we will send you back it in a decrypted form. This will be your guarantee.
E-MAIL1: zeta@dr.com
E-MAIL2: zeta@oath.com
YOUR_ID:{user’s custom identification number}
The Zeta infection is part of the ransomware family. It’s a dreadful infection, whose presence on your computer only leads to grievances and headaches. That’s because ‘ransomware’ is arguably the worst type of cyber threat, which you can catch online. And, there’s a reason for that. These tools are notoriously invasive and dangerous. They’re programmed to target your private data – all of the pictures, music, documents, videos, everything! They take it hostage by encrypting it, and making it impossible for you to open or access them in any way. And, once your data is under their control, they present you with a choice. You can regain control of your files by paying a ransom for their release, or lose them forever. Oh, yes. Once the infection slithers into your PC and encrypts every single file, it demands you pay a certain amount of money (usually in Bitcoin), if you ever wish to see your data again. So, the tool does provide you with one way to access your files – pay up. But, here’s the thing, and this is the question you truly need to ask yourself: can these people be trusted to keep their end of the bargain? And, here’s your answer as provided by experts: No. We’re talking about malicious people, who have designed a hazardous cyber threat, and unleashed it onto the web so it can carry on and corrupt every user it comes into contact with. So, ever if you pay (which you definitely must NOT!!!), there are utterly NO guarantees that will lead to the release of your data. It’s just as likely that you pay and merely end up with less money and still encrypted files. Only, apart from having less funds, by transferring the money to these strangers, you provide them with your personal and financial information. To put it mildly, that is NOT something you want to happen. Don’t allow wicked people access to your private life! Don’t pay the ransom! Pick privacy over pictures. Your files aren’t worth the danger, which you’ll face if you attempt to save them from their kidnapper. Don’t risk it, and make the more difficult but wise choice. Discard your data.
How did I get infected with?
Ransomware infections, like Zeta, are immensely crafty. They’re so skilled in the arts of deceit that they have no trouble fooling you into permitting them into your system. Oh, yes! YOU allow the tool into you computer. Zeta is bound to seek permission before it enters, and unless you grant it – no admittance. And, seeing as how you’re reading this article, it’s safe to assume that you complied with its inquiry. However, don’t beat yourself up too hard. After all, don’t think the tool openly comes out and asks you. As was already explained, it’s crafty! It employs every known trick in the book to dupe you into giving it the green light without you even realizing it. Zeta usually sneaks in undetected by hitching a ride with spam email attachments or freeware, hitching a ride with corrupted sites or links, or pretending to be a bogus update. If you wish to keep Zeta, or any other cyber threat like it, away from your PC, be more cautious! Infections prey on carelessness, so don’t provide it. Be more thorough and vigilant, and always do your due diligence as even a little extra attention can go a long, long way.
Why is Zeta dangerous?
The Zeta ransomware tool encrypts every single file you have stored on your computer using RSA-2048 key (AES-CBC 256-bit encryption algorithm). To complete the process, it adds the .id_email_zeta@dr.com.scl extension. Once the file is renamed, it can no longer be accessed. And, that won’t change no matter how many times you change its name. You’ll quickly come to the realization that the only way to save it is to apply the decryption key. And, to get the key, you have to pay the ransom, which Zeta demands. After the encryption is finished, Zeta will create a HELP_YOUR_FILES.txt file, which will explain the situation you’re in, and what you must do to get out of it. You’ll see the file in every encrypted folder, as well as on your desktop. And, just to truly stress that you’re under siege by a ransomware tool, Zeta will switch your desktop wallpaper to HELP_YOUR_FILES.png. The sum, which is demanded of you ranges between 0.5-1.5 Bitcoin. That’s equivalent to $225.18 – $675.53. As you can see, that’s no small amount of money. The ransom gap is so big, because Zeta tends to increase the sum as time goes by. In other words, the more you delay payment, the more money you’ll be asked to transfer. That’s just another way to get you to panic and pay up, but here’s what: Don’t pay these people. You’ll regret it if you do. There are several possible outcomes, following payment, and they all end badly for you. Don’t give these people money and access to your private details. It’s not worth the gamble. It may seem harsh, but forsake your files in the name of your privacy. It’s for the best.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Zeta Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Zeta Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Zeta encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Zeta encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.