Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove Webaccesses.net ads? This page includes detailed ads by Webaccesses.net Removal instructions!
An adware has infiltrated your system. It did so via slyness and subtlety, and slithered past you undetected. And, since it snuck in unnoticed, it uses the Webaccesses.net site to reveal itself. Consider the website the tool’s grand announcement. Once you spot it, acknowledge the presence of adware on your PC. Accept that the nasty threat lurks somewhere on your computer, find where, and delete it. The sooner you do, the more issues you’ll avoid. And, the more you extend its stay, the worse your predicament gets. The infection not only causes your system’s performance to deteriorate. It also threatens your privacy. Yes, the program follows instructions to spy on you. It begins its espionage, after it invades. The tool tracks your every move, and keeps a record of it. Then, once it determines it has gathered enough information, it sends it. To whom? Well, to the cyber criminals, responsible for the adware’s release. In other words, unknown individuals with malicious intentions. Not people, you can trust with such sensitive details. Keep your personal and financial data safe. Don’t allow the adware enough time to fulfill its thieving agenda. Delete it as soon as you become aware of its stay. The page’s appearance is a sign to urge you into action. So, heed it, and act. Do your best to discover the infection’s exact hiding place, and delete it on discovery.

How did I get infected with?
Webaccesses.net shows up, because the adware forces it on you. But what about said adware? How does it end up on your computer? Do you recall installing it? Odds are, you don’t. But that doesn’t change the fact that you did. Don’t be too hard on yourself, though. Let’s explain. The adware tool has to ask whether you, the user, agree to install it. Only if you do, can it enter your PC. The infection does its best to gain consent, and avoid rejection. To improve its chances, it resorts to trickery. Yes, it does seek your approval. But, no, it doesn’t do it outright. If it did, that leaves too much to chance. So, instead, it turns to the old but gold invasive methods. And, preys on your distraction, haste, and naivety. It hides behind freeware, fake updates, corrupted links, spam emails. It has an array of tricks it can resort to. But neither trick can prove successful, if you’re thorough. So, be thorough! If the tool needs your carelessness to sneak into your system, don’t provide it. Take the opposite approach, and be extra cautious. Even a little extra attention goes a long way, and can save you a ton of troubles. Carelessness invites them in. Make the right choice.
Why is this dangerous?
Webaccesses.net becomes a constant presence on your screen. The adware turns it into your shadow. No matter what you do, it finds a way to display it. Open a new tab? Webaccesses.net is there. Type a search? It’s among the suggested results. Do anything at all, and you get stuck with ‘Connecting to Webaccesses.net.’ Or, ‘Waiting for Webaccesses.net.’ You get put through a bombardment of ads, on a daily basis. And, each one reads ‘Brought to you by Webaccesses.net.’ Banner, pop-up and in-text ‘Ads by Webaccesses.net.’ The adware intrudes on your activities all day, every day. And, that doesn’t go without consequence. Your system starts to suffer frequent crashes. Lagging turns into a daily occurrence, as well. Add to all that unpleasantness, the security hazard, and it’s quite evident. The infection has no place on your computer. Do your best to remove it the first chance you get. And, spare yourself the avalanche of frustration, you’ll otherwise experience. Find and remove the adware ASAP.
How to Remove
virus
The Webaccesses.net infection is specifically designed to make money to its creators one way or another. The specialists from various antivirus companies like Bitdefender, Kaspersky, Norton, Avast, ESET, etc. advise that there is no harmless virus.
If you perform exactly the steps below you should be able to remove the Webaccesses.net infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Track down Webaccesses.net in the computer memory
STEP 2: Locate Webaccesses.net startup location
STEP 3: Delete Webaccesses.net traces from Chrome, Firefox and Internet Explorer
STEP 4: Undo the damage done by the virus
STEP 1: Track down Webaccesses.net in the computer memory
- Open your Task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Carefully review all processes and stop the suspicious ones.

- Write down the file location for later reference.
Step 2: Locate Webaccesses.net startup location
Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
Clean Webaccesses.net virus from the windows registry
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to: %appdata% folder and delete the malicious executable.
Clean your HOSTS file to avoid unwanted browser redirection
Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:

STEP 3 : Clean Webaccesses.net traces from Chrome, Firefox and Internet Explorer
-
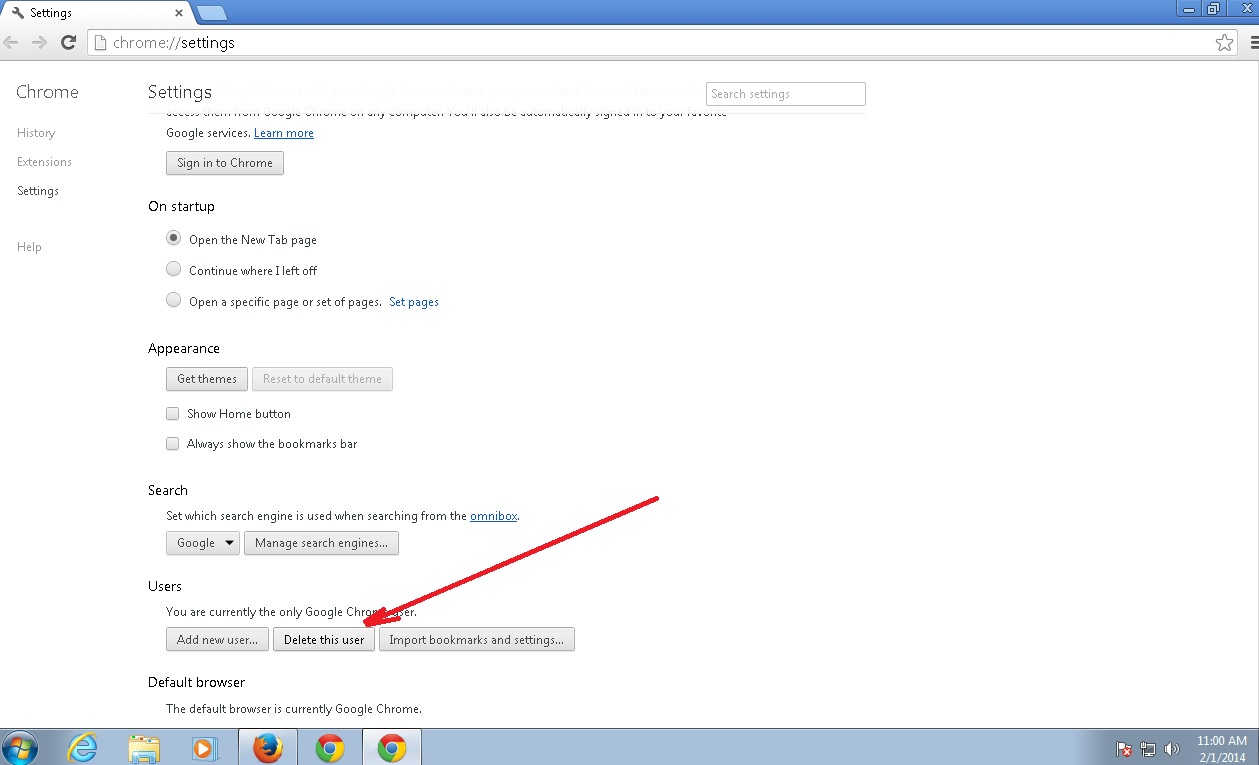
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Webaccesses.net by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
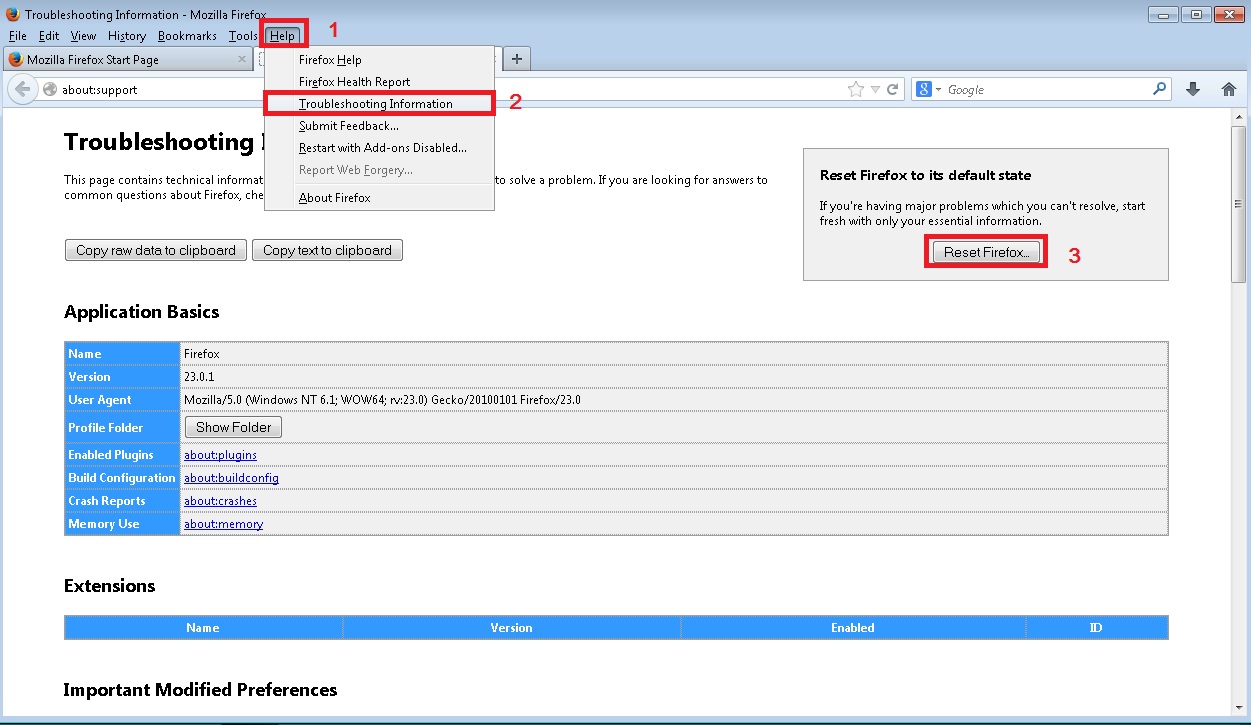
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
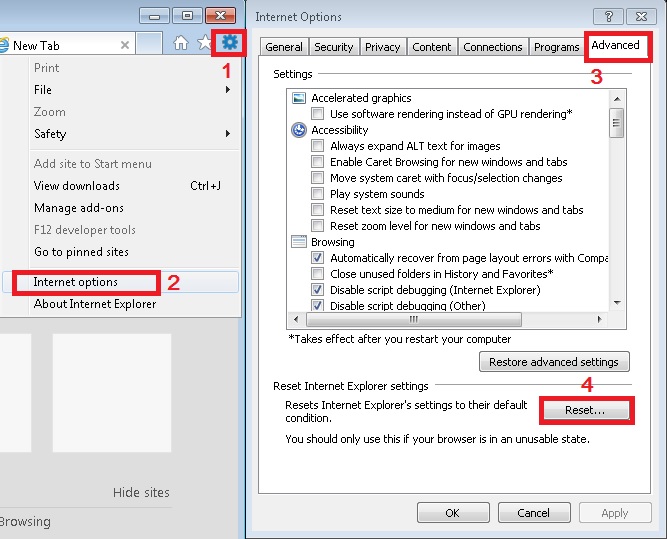
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
Step 4: Undo the damage done by Webaccesses.net
This particular Virus may alter your DNS settings.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for Webaccesses.net, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
You must clean all your browser shortcuts as well. To do that you need to
- Right click on the shortcut of your favorite browser and then select properties.
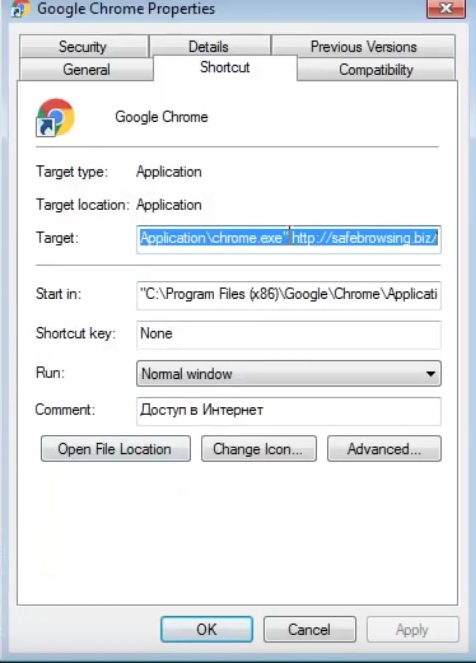
- in the target field remove Webaccesses.net argument and then apply the changes.
- Repeat that with the shortcuts of your other browsers.
- Check your scheduled tasks to make sure the virus will not download itself again.
How to Permanently Remove Webaccesses.net Virus (automatic) Removal Guide
Please, have in mind that once you are infected with a single virus, it compromises your system and let all doors wide open for many other infections. To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.