Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove U85foldero.com pop-up? This page includes detailed U85foldero.com Removal instructions!
U85foldero.com seems like your average website but it’s much more than that. It’s a big bright neon sign that your system’s well-being is in danger! It’s a warning that your personal and financial information are in jeopardy! The page indicates that your computer is no longer infection-free. Think of U85foldero.com as the face of an adware program. The application slithers into your system, and the site is its way of cluing you into its existence. Don’t ignore its clue. Instead, act on it! If you don’t, you WILL regret it. There’s an entire myriad of reasons to get rid of the adware, you’re stuck with. The one reason, towering over all the rest, has to do with your privacy. The infection threatens to steal your private details. And, then proceeds to expose them to unknown individuals with malicious intentions. All adware-type tools follow the same design. They sneak into your system, and begin to spy on you. The applications keep track of your browsing habits, and catalog every move you make. After they determine they have enough data gathered, they hand it over to the people behind them. Strangers with agendas. Once they have access to your private information, they can use it as they see fit. Can you imagine the repercussions that entails? If you wish to protect your privacy from these cyber criminals, take action. And, do it before it’s too late. The more you delay, the more trouble comes your way. The sooner you find and delete the adware tool, lurking behind U85foldero.com, the better.
How did I get infected with?
U85foldero.com pops up on your screen after your PC gets infected with adware. But, here’s the thing. An adware tool cannot install itself without user’s permission. In other words, you permitted the infection’s install. Odds are, you don’t remember doing iy because you didn’t realize it at the time. But you did. Let’s elaborate. An adware is bound to ask whether you agree to allow it into your system, yes. But it doesn’t have to do it openly. That’s the loophole most cyber threats take advantage of. They have found an entire array of ways to ask permission under the radar. For example, they hide behind freeware. Or, corrupted sites or links. Or, hitch a ride with spam email attachments. Or, pretend to be a fake update. Like, Adobe Flash Player or Java. So, while you believe you’re installing an update, you’re not. In actuality, you’re giving the green light to a dangerous infection out to exploit you any way it can. If that’s something, you’d rather avoid, turn to caution. Distraction, naivety, and haste are NOT your friends. They ease the invasion of threats like adware. Instead, turn to vigilance and due diligence. Take your time to read the terms and conditions when installing updates or freeware. Don’t just agree to everything, and hope for the best. Carelessness leads to infections. Caution helps keep them away.
Why is this dangerous?
Once the adware dupes you into allowing it into your system, it goes to work. It doesn’t take long before you see the effects of its stay. Soon after infiltration, issues begin to pop up. Adware applications are immensely meddlesome. One of the first intrusions, you suffer from, has to do with your homepage and search engine. The tool replaces your default ones, and places U85foldero.com in their stead. Every time you open your browser, you get redirected to the site. If you search the web, the link is among the suggested results. If you do anything online, the website pops up. You can’t escape seeing U85foldero.com. And, it’s not alone. There’s a never-ending stream of pop-up ads that accompanies the constant redirects. Just try to imagine what your browsing experience becomes with all these disruptions. It’s an utter mess. But that’s just the beginning of your grievances. Since the intrusions are incessant, they lead to further troubles. Due to all the interruptions, your system starts to crash more often. Your computer’s performance slows down to a crawl, as well. When you add to these issues, the security risk, the choice gets made for you. The adware, using U85foldero.com as a shield to hide behind, has no place on your PC. Locate its exact lurking spot as soon as possible. Then, once you find where it’s hiding, delete it! To leave the adware in your system is a mistake. One, you’d regret for sure.
How to Remove U85foldero.com virus
The U85foldero.com infection is specifically designed to make money to its creators one way or another. The specialists from various antivirus companies like Bitdefender, Kaspersky, Norton, Avast, ESET, etc. advise that there is no harmless virus.
If you perform exactly the steps below you should be able to remove the U85foldero.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Please, keep in mind that SpyHunter’s scanner tool is free. To remove the U85foldero.com infection, you need to purchase its full version.
STEP 1: Track down U85foldero.com in the computer memory
STEP 2: Locate U85foldero.com startup location
STEP 3: Delete U85foldero.com traces from Chrome, Firefox and Internet Explorer
STEP 4: Undo the damage done by the virus
STEP 1: Track down U85foldero.com in the computer memory
- Open your Task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Carefully review all processes and stop the suspicious ones.

- Write down the file location for later reference.
Step 2: Locate U85foldero.com startup location
Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
Clean U85foldero.com virus from the windows registry
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to: %appdata% folder and delete the malicious executable.
Clean your HOSTS file to avoid unwanted browser redirection
Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:

STEP 3 : Clean U85foldero.com traces from Chrome, Firefox and Internet Explorer
-
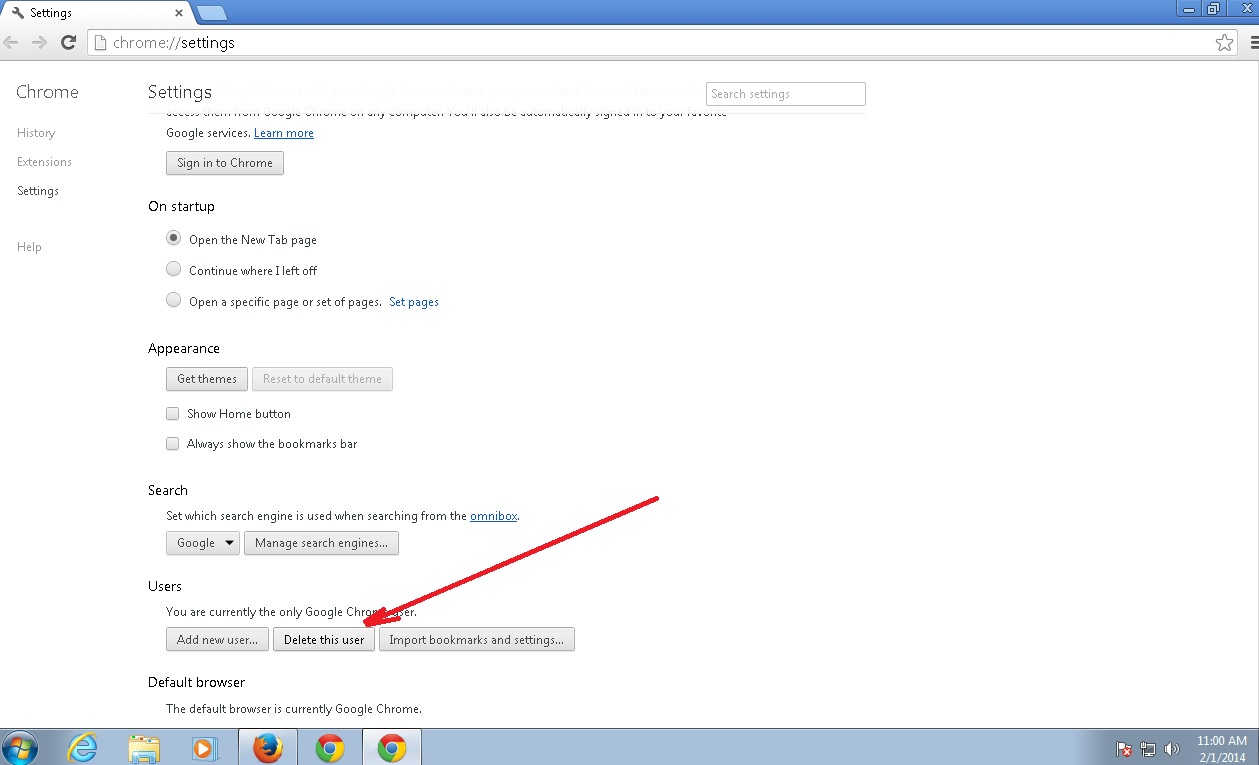
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the U85foldero.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
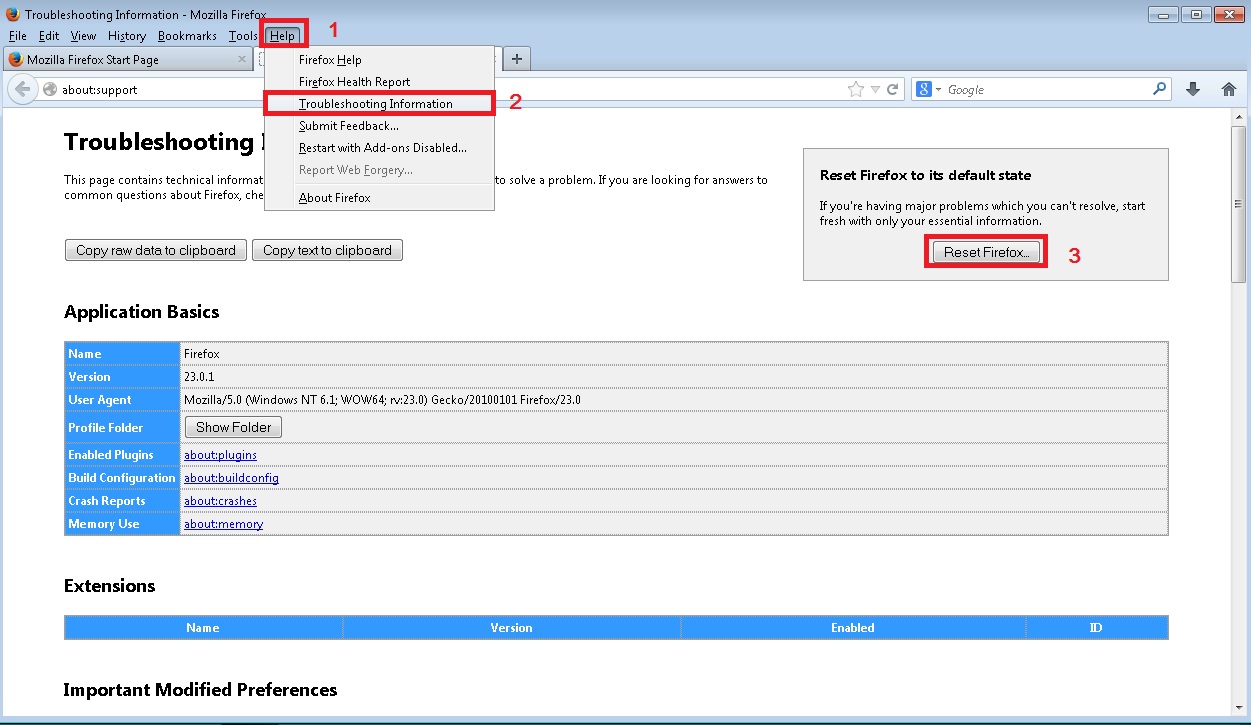
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
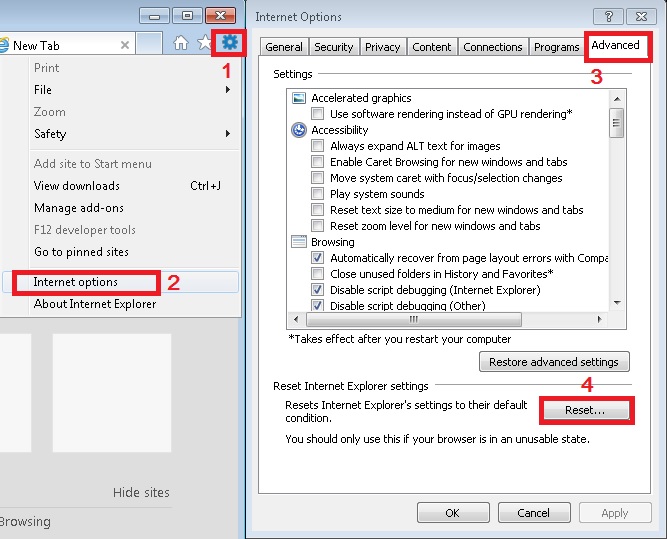
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
Step 4: Undo the damage done by U85foldero.com
This particular Virus may alter your DNS settings.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for U85foldero.com, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
You must clean all your browser shortcuts as well. To do that you need to
- Right click on the shortcut of your favorite browser and then select properties.
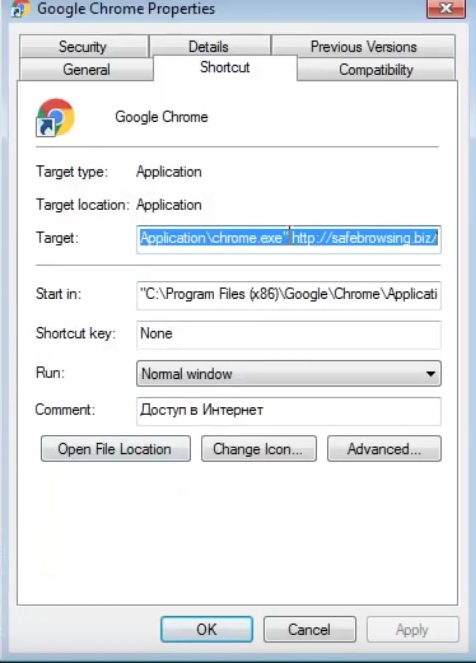
- in the target field remove U85foldero.com argument and then apply the changes.
- Repeat that with the shortcuts of your other browsers.
- Check your scheduled tasks to make sure the virus will not download itself again.
How to Permanently Remove U85foldero.com Virus (automatic) Removal Guide
Please, have in mind that once you are infected with a single virus, it compromises your system and let all doors wide open for many other infections. To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.