Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove ODCODC Ransomware?
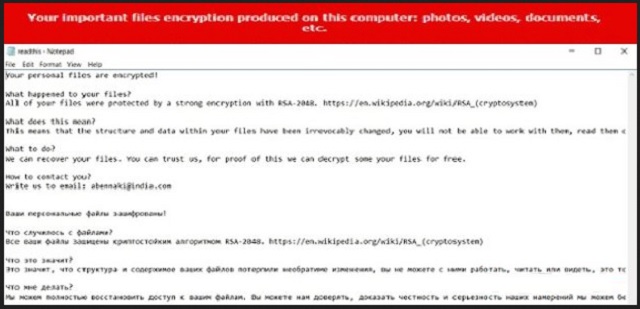
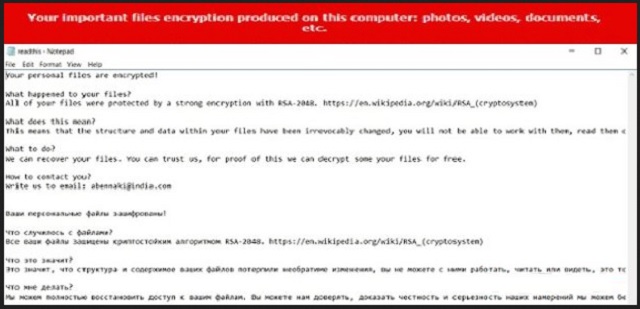
Reader recently start to report the following message being displayed when they boot their computer:
Your personal files are encrypted!
What happened to your files?
All of your files were protected by a strong encryption with RSA-2048. https://en.wikipedia.org/wiki/RSA_(cryptosystem)
What does this mean?
This means that the structure and data within your files have been irrevocably changed, you will not be able to work with them, read them or see them, it is the same thing as losing them forever, but with our help, you cant restore them.
What to do?
We can recover your files. You can trust us, for proof of this we can decrypt some your files for free.
How to contact you?
Write us to email: abennaki@india.com
Ваши персональные файлы зашифрованы!
Что случилось с файлами?
Все ваши файлы зашищены криптостойким алгоритмом RSA-2048. https://en.wikipedia.org/wiki/RSA_(cryptosystem)
Что это значит?
Это значит, что структура и содержимое ваших файлов потерпили необратиме изменения, вы не можете с ними работать, читать или видеть, это тоже самое, что потерять их бесповоротно, но, с нашей помощью, вы можете их все восстановить.
Что мне делать?
Мы можем полностью восстановить доступ к вашим файлам. Вы можете нам доверять, доказать честность и серьезность наших намерений мы можем бесплатной расшифровкой нескольких файлов.
Как с вами связаться?
Напишите нам на почту: abennaki@india.com’
As you could imagine, this message doesn’t indicate anything good. Quite the opposite, actually. Seeing such a warning means you’ve fallen victim to the most dreadful kind of virus currently on the Internet. Ransomware. ODCODC Ransomware, to be more specific. Being among the newest ransomware-type infections out there, this particular virus has two versions. There’s only one difference between them that’s worth mentioning and we’ll explain it later on in this article. Now, what is ransomware? A virulent PC infection which first encrypts your personal files, then asks for a ransom in order to restore your infected data. This is an extremely convenient way for cyber criminals to blackmail PC users. Therefore, keep in mind that this entire scheme was created solely so hackers could steal your money. Are you willing to get involved in hackers’ trickery? No? Then keep on reading. Like many similar parasites, ODCODC Ransomware uses the RSA-2048 encrypting algorithm. Once it gets installed, the virus gets activated almost immediately. It performs a thorough scan on your device searching for files with specific extensions. Pictures, videos, MS Office documents, music, presentations – basically anything of value you may have stored on your PC gets encrypted. Obviously, some immensely important data that you really need could get locked as well. As the name implies, ODCODC Ransomware adds a .odcodc appendix to the files it modifies. When you notice this brand new, random extension, you could be absolutely positive that your personal information is now inaccessible. Your computer won’t be able to recognize this file format and, ultimately, you won’t be able to use your data. ODCODC Ransomware also includes an email address to the new extension your infected files now have. On theory, you’re supposed to use this email address to contact ODCODC Ransomware’s developers. Yes, that means you would be contacting hackers. Why would you do that? Because crooks promise you a unique decryption key in exchange for a (hefty) sum of money in Bitcoin. Remember, the RSA-2048 encrypting cipher is extremely complicated. Hackers rely on the fact many people would prefer to pay the ransom and regain access to their data. The problem is, that’s not how any of this works. As you already know, hackers aren’t exactly famous for following the rules. They have absolutely no reason whatsoever to keep their end of the bargain so don’t even consider giving your money away. It will be a terrible mistake and you know it.
How did I get infected with?
ODCODC Ransomware is usually disguised as a Word document. It travels the Web via spam email-attachments or spam messages that careless PC users rush to open. Our advice for you is to always stay away from anything suspicious-looking in your mailbox, especially if the sender is unknown. Don’t hesitate to delete such an email because there might be a vicious infection hidden inside of it. Other popular infiltration techniques online include corrupted torrents, malicious websites, third-party commercials, fake software updates, compromised freeware/shareware bundles, etc. As you can clearly see, the Web is infested with malware and hackers have various methods to choose from in order to spread it. Don’t overlook any threat online and make sure you constantly take care of your computer. It is much easier to prevent virus installation than to remove a parasite later on. Don’t neglect you own safety and don’t let hackers fool you.
Why is ODCODC dangerous?
As soon as your personal files get encrypted, you’ll see the following message: “Кодирование успешно завершено!” More often than not, ODCODC Ransomware actually deletes itself after it’s done locking your data. However, that doesn’t even remotely solve the problem with your unreadable, inaccessible, useless files. You’re supposed to pay a ransom. ODCODC Ransomware drops a readthis.txt file on your desktop and in all folders which contain modified data. This .txt file comes in both English and Russian and claims that the only way to restore your files is by following hackers’ rules. As we mentioned already, the ODCODC Ransomware virus has two versions and each one of them adds a different email address at the end of your files’ names – either abennaki@aol.com or abennaki@india.com. Apart from that, the two versions of this parasite are identical. Stay away from both email addresses and don’t try to negotiate with hackers; it’s a battle you can’t win. Remember that this is just a nasty attempt for a cyber fraud. Instead of giving your money away (which would guarantee you nothing), do the right thing. Follow our detailed removal which you’ll find down below and uninstall the virus for good.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
ODCODC Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover ODCODC Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with ODCODC encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate ODCODC encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.