Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Makdonalds@india.com Ransomware?
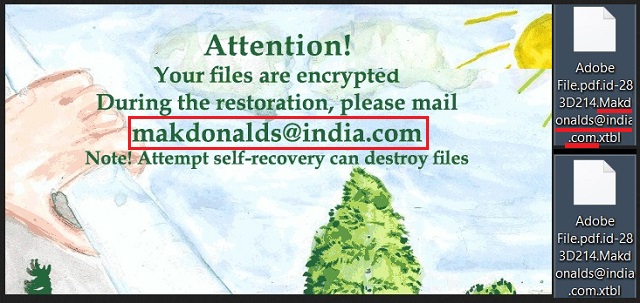
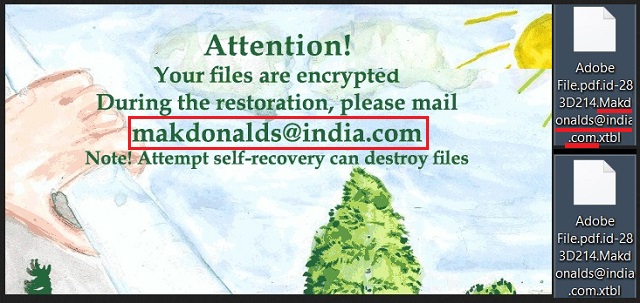
Reader recently start to report the following message being displayed when they boot their computer:
Attention!
Your files are encrypted
During the restoration, please mail
makdonalds@india.com
Note! Attempt self-recovery can destroy files
Makdonalds@india.com is an email address, associated with a dangerous infection. There’s a new ransomware application, plaguing users and wreaking havoc on their systems. If it invades your PC, you’re in for a bad time. After the tool slithers its way in undetected, it encrypts every single file you have. When it finishes with the encryption, it displays a message. A ransom note. It details your predicament, and gives you instructions. If you wish to free your files, you have to pay a ransom. One of the steps you have to take includes contacting the kidnappers via the email address. If you decide to comply, you have to send the kidnappers an unique ID key to Makdonalds@india.com. You’ll find the key in the ransom note. After you do that, you’re one step closer to regaining control over your data. However, we advise against it. Do NOT comply with these people’s demands! If you contact them and transfer the requested ransom, you’ll only worsen your situation. And, compliance doesn’t guarantee you the decryption of your files. Heed experts’ advice, and stay away from the email. It may seem harsh but forsake your files. They’re not worth the risks, posed by the ransomware. Do the wiser, more difficult choice, and say goodbye to your data.
How did I get infected with?
Ransomware doesn’t just pop up out of the blue one day. It’s just sneaky enough to invade your system without you even realizing. It usually turns to the old but gold methods of infiltration to succeed. That includes hitching a ride with spam email attachments or corrupted links. It can also pretend to be a bogus update. Like, Adobe Flash Player or Java. Or, it can hide behind freeware. That’s one of the easiest access points. For reasons beyond comprehension, users choose to throw caution to the wind during its install. And, instead of relying on due diligence, they leave it all to chance. It’s hardly a surprise that it’s a horrible strategy. One, which tends to result in unwanted malware finding its way on your PC. If you wish to avoid getting stuck with ransomware, don’t rely on luck. Don’t give into gullibility, haste, and distraction. Instead, take your time and be extra vigilant. Even a little extra attention goes a long way.
Why is Makdonalds@india.com dangerous?
After the infection slithers into your PC, it goes to work. Ransomware tools are immensely invasive. One of the first intrusions, they enforce, is to rearrange system settings. The tool meddles, and makes its stay permanent, so that even if the PC shuts down, it remains. But it hardly stops there. It carries on with implementing its programming. The infection encrypts every file you have on your PC. Nothing is beyond its reach. Pictures, videos, documents, music. Everything gets locked, and used against you. Your encrypted data is nothing more than a ploy for monetary gain. It’s a rather simple scheme. The kidnappers extort you for money. They promise that if you pay the ransom, you’ll receive the decryption key you need to free your files. But, ask yourself: Can you trust extortionists? Do you honestly expect these people to keep their end of the bargain? Don’t be naive. There are so many ways the exchange can go wrong. And, even if everything goes right, you still lose. Do you know why? Well, by paying the ransom, you give these people access to your private life. They’ll have your personal and financial information at their disposal. Do you think that’s a risk worth taking? No amount of pictures or music is worth that! Don’t gamble with your privacy! Files are replaceable. Your private life is not. Make the right choice. Forsake your data.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Makdonalds@india.com Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Makdonalds@india.com Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Makdonalds@india.com encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Makdonalds@india.com encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.