Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Grod Ransomware?
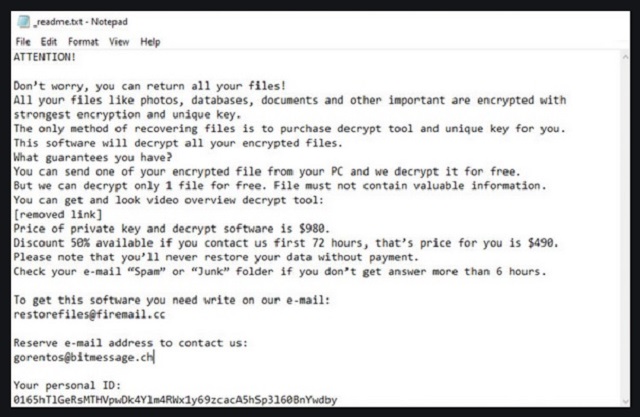
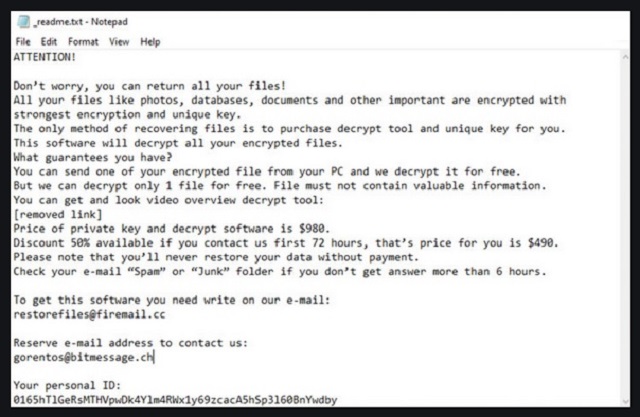
Readers recently started to report the following message being displayed when they boot their computer:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-7YSRbcuaMa
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
restorefiles@firemail.cc
Reserve e-mail address to contact us:
gorentos@bitmessage.ch
Your personal ID:
–
Grod is yet another variant of the STOP/DJVU cyber menace. The ransomware infiltrates your system, via slyness and subtlety. And, as soon as it settles, corruption ensues. The tool uses RSA encryption algorithm to lock your data. Yes, it locks every file, you keep on your computer. That includes, pictures, music, videos, archives, documents. Everything falls under the ransomware’s control. The Grod menace appends the ‘.grod‘ extension, at the end of each file. Thus, solidifying its grip over everything, you have on your PC. As an example, a photo called ‘yes.jpg‘ becomes ‘yes.jpg.grod.’ Once that happens, it’s no longer accessible. You can’t open it or use it. The only way to change that, and regain control, is via a special key. “The only method of recovering files is to purchase decrypt tool and unique key for you.” To get aid decryption key, you have to pay a ransom. It will cost you $980. To further entice you into paying, the Grod infection offers a discount. “Discount 50% available if you contact us first 72 hours, that’s price for you is $490.” Don’t fall for that. The ransomware spins a web of lies, and hopes you fall for it. Heed experts’ advice, and don’t pay these people a dime. Don’t contact them. Don’t reach out to them at all. They may claim that compliance solves your problems, but that’s not the case. Compliance is not the way to go. If you do comply, you’re setting yourself up for regret. Don’t do it.
How did I get infected with?
The Grod threat uses deception to invade. It turns to the old but gold invasive methods. And, above all, preys on your carelessness. Its usual antics include the following. Pretending to be a fake system or program update. Like, Java or Adobe Flash Player. Lurking behind corrupted links, sites or torrents. Or, using freeware and spam emails. These are among the most common tricks, Grod can resort to. And, even though, it appears like it has its pick, all these tricks share a common need. Neither one can prove successful, if you’re careful. The infection relies on your distraction, haste and naivety. It needs you t skip doing any due diligence. To rely on luck, and leave your fate to chance. If you do, you increase the odds of its successful infiltration. So, don’t! Don’t oblige but, instead, take the opposite approach. Take the time to be extra vigilant. Remember tat attention goes a long way, and can save you a ton of issues. Caution helps you to keep infections out of your system. And, carelessness leads to Grod slithering its way in. Make the right choice.
Why is Grod dangerous?
After Grod strikes, and locks everything up, it leaves you a note. A ransom note, called “_readme.txt.” It opens with “Don’t worry, you can return all your files!” The cyber criminals behind it, aim to curate a false sense of security. Don’t buy into it. You’re dealing with people, who encrypted your files. People, who are trying to extort you for money over their release. Don’t allow them to profit off of your fear and gullibility. As stated, compliance will bring nothing but regret your way. Do yourself a favor, and don’t take that path. Shall we examine your options, if you do? Say, you pay up. Then what happens? You wait to receive the decryption key that was promised. But what if they don’t send it? They gave you zero guarantees that after payment is complete, you’ll get it. All you got was their word. And, cyber kidnappers are hardly people, you can trust to keep their promise. They can choose to double-cross you, get your money and send you nothing. And, even if they do send you a key, it can prove useless. It can be the wrong key, one that fails to unlock your files. There are too many variables, when it comes to dealing with these people. Take no chances! Don’t comply. It’s a tough call to make, but it’s the right one. There aren’t enough ways to stress this. To comply is a mistake. Don’t make it.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Grod Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Grod Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Grod encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Grod encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.