Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Fantom Ransomware?
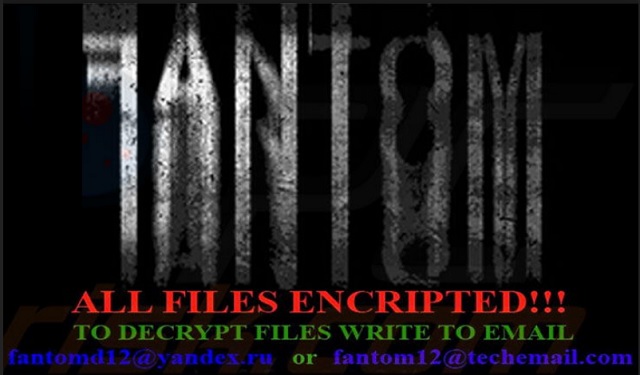
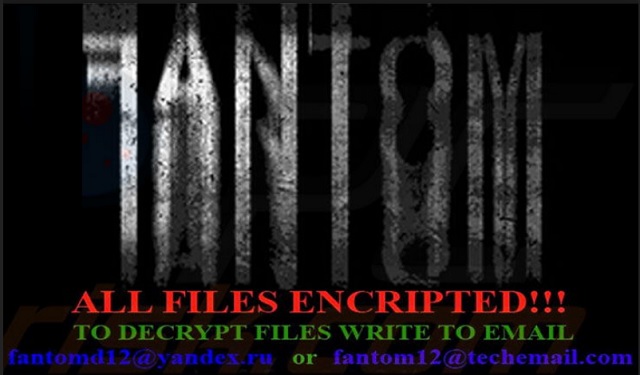
Reader recently start to report the following message being displayed when they boot their computer:
SDue encrypting was used algoritm RSA-4096 and AES-256, used for protection military secrets.
That means > RESTORE YOU DATA POSIBLE ONLY BUYING decryption passwords from us.
Getting a decryption of your files is – SIMPLY task.
That all what you need:
1. Sent Your ID_KEY on mailbox fantomd12@yandex.ru or fantom12@techemail.com
2. For test, decrypt 2 small files, to be sure that we can decrypt you files.
3. Pay our services.
4. GET software with passwords for decrypt you files.
5. Make measures to prevent this type situations again.
IMPORTANT(1)
Do not try restore files without our help, this is useless, and can destroy you data permanetly.
IMPORTANT(2)
We Cant hold you decryption passwords forever. ALL DECRYPTION PASSWORDS, for what wasn`t we receive reward, will destroy after week of moment of encryption.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
There’s a new ransomware program, roaming the web. It goes by the name Fantom, and it’s plaguing Internet users. As any such infection, it’s invasive and damaging. As you probably already know, ransomware targets your data. Once it slithers its way into your system, you’re in for a terrible time. And, it starts with a nasty surprise. After the tool settles on your PC, it doesn’t waste time to strike. Its programming kicks in shortly after infiltration. And, you experience the repercussions of a ransomware invasion. You face strangers, who are holding your files hostage, and demand a ransom for their release. The kidnappers encrypt your data and, thus, make it inaccessible. They offer you one, and only one, way to regain control over it – monetary payment. These people ask for a ransom in the rage of 0.5 to 1.5 Bitcoin. In case, you’re unfamiliar, that’s a lot of money. But even if it weren’t, we’d still advise you NOT to pay. Why? Well, it’s pretty simple. Payment only makes things worse. If you go through with the transaction, you throw yourself deeper into the abyss of disaster. So, don’t. It may seem difficult, but say goodbye to your data. It’s the safer, wiser choice to make. Don’t comply with extortionists’ demands. Don’t pay. Better be safe than sorry. You’ll see it’s the right choice to make in the long run.
How did I get infected with?
Fantom turns to the usual antics to invade your system. It tends to use the old but gold means of infiltration. And, it slithers its way in undetected. That’s right. You have no idea it’s on your PC until it acts up, and revels itself. But until that moment comes, you’re clueless. More often than not, the infection gains access by pretending to be a bogus update. For example, you may be utterly convinced you’re updating your Java, but you’d be wrong. In actuality, you’d be giving the green light to the dangerous Fantom menace. Star Wars puns aside, the ransomware is not to be trifled with. Don’t underestimate the damages its presence causes. Do your best to avoid them. If you wish to keep such nasty applications away from your system, try to be more careful when installing a tool or an update. Cyber threats prey on carelessness, so don’t provide it. Don’t rush and don’t throw caution to the wind. Naivety, haste, and distraction rarely lead to positives. Choose caution over lack thereof. Always do your due diligence, and remember that even a little extra attention goes a long way.
Why is Fantom dangerous?
Once the ransomware sneaks into your system, it goes to work. One day, as you’re using your computer, you encounter an unexpected interruption. Suddenly, you see a “Configuring critical Windows Updates” take over your screen. That’s Fantom. It’s making its move. It displays the message as a distraction while it’s going through with its programming. It encrypts your files while you’re lead to believe, updates are getting installed. The tool uses RSA-4096 and AES-256 encryption systems to lock every file you have on your PC. It solidifies its hold over your data by adding an extension at the end of each of your files. For example, if you have a picture called ‘winter.jpg,’ once the ransomware is done, you’ll see it as ‘winter.jpg.fantom.’ And, no matter how many times you rename or move it, you won’t be able to access it. It’s encrypted. And, the only way to remove said encryption is via a decryption key. It’s all explained in the DECRYPT_YOUR_FILES.HTML ransom note, which Fantom leaves on your screen. It contains instructions on the ransom exchange. And, also, explains that if you take longer than a week to complete the payment, you’ll lose your data. After the time limit passes the tool deletes the decryption key. And, you lose your files. The message, which Fantom leaves you, also threatens you not to try anything: “Do not try restore files without our help, this is useless, and can destroy you data permanetly.” It’s a misspelled hodgepodge but it does the trick. It gets the message across that payment is your only sure way to retrieve your data. But is your data worth ii, though? Even in the best-case scenario, you still lose. Think about it. Say, you pay up, get the key, apply it, and free your files. Then what? You still have a ransomware on your PC. It can still encrypt your data if it so decides. But the worst part, of paying these people, is the security risk. If you complete the transaction, you grant them access to your personal and financial details. Strangers with agendas will have your private life at their disposal. Do you think that will end well?
Fantom Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Fantom Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Fantom encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Fantom encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.