Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove AnonPop Ransomware (supportfile@yandex.com)?
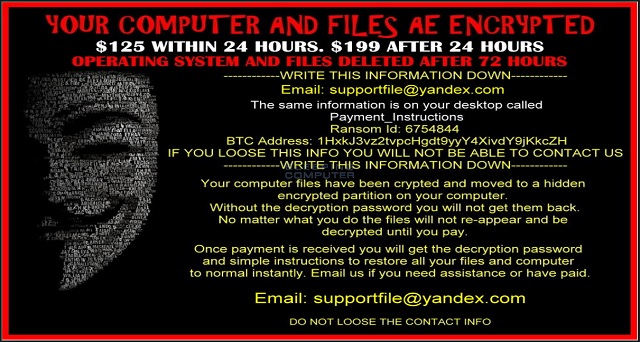
Reader recently start to report the following message being displayed when they boot their computer:
YOUR COMPUTER NAD FILES ARE ENCRYPTED
$125 WITHIN 24 HOURS. $199 AFTER 24 HOURS
OPERATING SYSTEM AND FILES DELETED AFTER 72 HOURS
————WRITE THIS INFORMATION DOWN————
Email: supportfile@yandex.ru
The same information is on your desktop called
Payment_Instructions
Ransom Id: XXXXXXXX
BTC Address: XXXXXXXXXXXXXXXXXX
IF YOU LOOSE THIS INFO YOU WILL NOT BE ABLE TO CONTACT
————WRITE THIS INFORMATION DOWN————
Your computer files have been encrypted moved to a hidden ENCRYPTED partition in your computer.
Without the decryption password you will not get them back.
No matter what you do, the files will not re-appear and be decrypted until you pay.
Once payment is received you will get the decryption password. and simple instructions to restore all your files and computer to normal activity. Email us if you need assistance or have paid.
Email: supportfile@yandex.ru
DO NOT Lose THE CONTACT INFO
Yes, there is such thing as a fake ransomware. As you could imagine, hackers are impressively creative when it comes to cyber infections. It’s only logical crooks would want to imitate their most devastating and problematic virus. Now, do you know what ransomware is? This is the virus that encrypts your personal files. Then it keeps them hostage until you pay a ransom in Bitcoin. At first sight, the AnonPop virus appears to be a real ransomware threat. A closer look at this infection, though, reveals that you’re dealing with something else. This is a deceptive malware. By pretending to be a ransomware parasite, it’s aiming at your bank account. That means the virus attempts to achieve the same malicious goal as ransomware. Stealing your money. However, you should never allow cyber crooks to gain profit at your expense. Don’t support hackers’ illegitimate business and don’t let this pest fool you. Fake AnonPop Ransomware claims it has locked your private files just the way ransomware does. You will come across a disturbing ransom message which claims you have 24 hours to complete the payment. As mentioned, though, Fake AnonPop Ransomware doesn’t actually encrypt your files. It deletes them. Before you freak out, you should know that there is a way to restore your data. Don’t panic. Make sure you remain calm and collect while dealing with the virus. Anxiety might cost you a hefty sum of money. As soon as the computer gets infected, Fake AnonPop Ransomware starts deleting your files. The parasite also begins to display pop-up messages in specific time intervals (every 4 minutes). In addition, Fake AnonPop Ransomware displays a ransom note on your desktop. You see, this program doesn’t even allow you to access your start menu. The virus demands $125 in exchange for a decryption password. It goes without saying this is a lie. Fake AnonPop Ransomware has already deleted your files so why pay ransom? You will receive absolutely nothing even if you make the payment on the spot. Apart from the obvious fact hackers would get your money, they would also get access to your bank account data and private details as well. Stay away from the supportfile@yandex.com email and prevent further harm. Also, remember those deleted files of yours? There are plenty of file recovery tools online that could restore your data. Furthermore, they will restore it without you paying $125.
How did I get infected with?
Fake AnonPop Ransomware is spread online as a .zip archive. You might think you’re opening a PDF file but in reality, you’re giving green light to the parasite. Next time you spot some questionable email or message in your inbox, simply delete it. One single careless click could result in some long hours of dealing with a pesky online virus. Keep in mind how dangerous spam is and be cautious. Also, the parasite might have gotten installed via some freeware or shareware bundle. Those are among the most popular malware distribution techniques online. Avoid such unverified bundles and always check out all programs thoroughly beforehand. Make sure you’re perfectly aware what you end up stalling and what you don’t. Ransomware also gets downloaded with the help of a Trojan, via fake torrents and bogus software updates. Long story short, there are many ways to compromise your PC. Be careful online and protect your safety.

Why is AnonPop dangerous?
As mentioned, Fake AnonPop Ransomware is dangerous. Even though this infection doesn’t encrypt files, it might still be able to trick you into paying a ransom. The very last thing you should do is to follow hackers’ instructions, though. Remember, there’s no decryption password. There’s also no decryption. Ignore crooks’ empty promises and threats; get rid of the virus instead. It’s important to keep in mind you could easily restore your private information WITHOUT paying anything. This virus is quite different from the real ransomware-type infections out there. It’s not even half as dangerous if you take action on time. Then why would you procrastinate? All pop-ups this infection displays are equally misleading and deceptive. Don’t contact hackers and don’t be gullible to think you could trust them. The sooner you uninstall this nuisance, the better. In order to delete Fake AnonPop Ransomware manually, please follow our removal guide. You will find it down below.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
AnonPop Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover AnonPop Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with AnonPop encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate AnonPop encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.