Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Crypt888 Ransomware?
Crypt888, also known as Mircop, falls under the umbrella of ransomware. In case, you’re unfamiliar with such tools, they’re a menace. They’re arguably the worst cyber threat out there. Why? Well, they make it personal. They don’t just target your system and worsen its performance. They also target your data. Every last bit of information you keep on your PC has a big red circle on it. Once the ransomware program invades your computer, it doesn’t take long before it strikes. The tool encrypts every file you have. Pictures, videos, music, documents, etc. It all falls under the infection. Once the tool adds the extension at the end if each of your files, they’re no longer accessible. The file extension solidifies its keep. Then the only way to free your files is with a decryption key. And, you’ve guessed it. It costs money. To get the key, you have to transfer money to the people behind Crypt888. Whatever you do, do NOT pay the ransom! That would only worsen your predicament! Do NOT pay! Your data is not worth even half the trouble that paying will bring you. So, do yourself a favor, and forsake your files. It’s a difficult decision to make but it’s the right one.
How did I get infected with?
Ransomware applications cannot enter your system without permission. For them to enter, you gave to allow it. They’re required to ask whether you agree to install them. If you deny them, they cannot get in. But if you consent, brace yourself for trouble. It would surprise you how many users agree to install such tool. And, they don’t even realize it. Do you know why that is? Most users are careless. They aren’t as attentive as they should be when installing tools or updates. And, that’s when such infections attempt infiltration. They seek your approval at your most distracted point. In other words, they turn to freeware, spam email attachments, bogus updates. That’s why it’s crucial to read the terms and conditions with care. To take your time instead of rushing. Choose vigilance over distraction. Maybe that way, you’ll spot the cyber menace trying to slither into your PC, and stop it. Remember that even a little extra attention can save you a ton of troubles.
Why is Crypt888 dangerous?
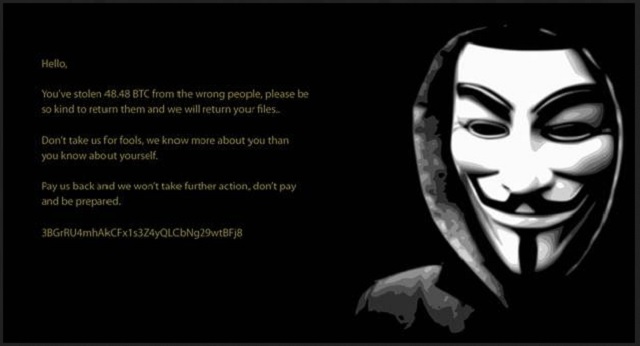
Crypt888 goes to work shortly after infiltration. After the last invasion stage is complete, it starts with the encryption process. As was already mentioned, it attacks every single file you have. Nothing is safe, and nothing is beyond its reach. Once your data gets locked, the ransom note appears. It takes over your Desktop, and pops up as a TXT file in each of your folders. It’s a standard message. It explains your predicament. How you’re enjoying the presence of a ransomware in your PC. How it has locked your data. How you cannot free them without a decryption key. And, how you have to pay a ransom to get said key. It also contains instructions on how to do that. Crypt888 asks for payment in Bitcoin. About 0.8 BTC, to be exact. And, it’s no small fee you need to pay. A single Bitcoin rounds at about 550 US Dollars. But you should know that the amount of the ransom is NOT why you shouldn’t pay. Even if Crypt888 asked for a dollar or a cent, it’s still ill-advised to pay. Why? Well, think of it this way. When you transfer the requested sum, you give your personal and financial details. And, these people who unleashed Crypt888 on you see it. They have access to it. You open the door to your private life to these people. And, once opened, you cannot close it. Do you think that will end well for you? Cyber criminals having access to your privacy? Don’t take chances. Don’t pay. After all, you can replace data. Can you say the same for privacy?
Crypt888 Removal Instructions
STEP 1: Kill the Malicious Process
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 3: Locate Startup Location
STEP 4: Recover Crypt888 Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Crypt888 encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Crypt888 encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.