Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove Link2captcha.top ads? This page includes detailed Link2captcha.top Removal instructions!
While browsing the internet, our researchers came across the link2captcha.top website and discovered it to be a malicious page. Through bogus CAPTCHA verification, it disseminates browser notification spam and can route visitors to potentially dangerous websites. Many people use redirection from websites that use malicious advertising networks to visit websites like link2captcha.top. Users should use caution when exploring the web and be aware of potentially dangerous websites. It is advised to routinely update your antivirus software and to be cautious of unexpected pop-ups or warnings to prevent falling prey to these types of pages. Avoiding clicking on strange or dubious links might also assist in preventing you from visiting dangerous websites. The IP address and geolocation of the visitor can have an impact on the behavior of malicious websites like link2captcha[.]top. The content that appears on these sites can be determined by this information. We discovered two different versions of the link2captcha.top website during our examination. Both used false CAPTCHA verification by showing visitors images of robots and asking them to click the “Allow” button. However, users would unintentionally permit link2captcha.top to send browser notifications by attempting to pass this bogus test. These notifications may contain advertisements for risky software, malware, and internet scams. Using websites like link2captcha.top can have detrimental effects on your system, as well as violate your privacy and cause you to lose money and lose your identity. It is important to use caution when using the internet and to avoid interacting with websites.
Link2captcha.top is a website meant to trick users into clicking the Allow button, send unwanted browser alerts, and reroute users to dubious, dangerous, and fraudulent websites.

How did I get infected with?
You may have become infected with malware from a rogue webpage like link2captcha[.]top in a few different ways. Some common ways include:
- By clicking on a malicious link or ad that redirected you to the website.
- By downloading software or visiting a website that was infected with malware and then allowing it to infect your device.
- By not having up-to-date antivirus software installed on your device, which can leave it vulnerable to attacks.
It is important to be cautious when browsing the web and to avoid clicking on unfamiliar or suspicious links, downloading software from untrusted sources, and visiting websites that you believe may be harmful. Additionally, regularly updating your antivirus software can help protect your device from malware infections.
Why is having Link2captcha.top dangerous?
Having the browser hijacker Link2captcha.top on your computer can be troublesome for a number of reasons. First off, it can slow down your computer and divert you from your browsing because it constantly displays advertisements and pop-ups on your online browser. This could result in increased data usage and reduced battery life for laptop users. Additionally, the hijacker can keep tabs on your online behavior and capture private information about you, such as your search history and browsing habits, which it can then resell to third-party advertisers for money. Your privacy could be compromised, and the likelihood of identity theft could increase. Furthermore, some of the advertisements that Link2captcha.top shows may be harmful and tempt visitors to download more malware or undesirable products.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Link2captcha.top virus
The Link2captcha.top infection is specifically designed to make money to its creators one way or another. The specialists from various antivirus companies like Bitdefender, Kaspersky, Norton, Avast, ESET, etc. advise that there is no harmless virus.
If you perform exactly the steps below you should be able to remove the Link2captcha.top infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
STEP 1: Track down Link2captcha.top in the computer memory
STEP 2: Locate Link2captcha.top startup location
STEP 3: Delete Link2captcha.top traces from Chrome, Firefox and Internet Explorer
STEP 4: Undo the damage done by the virus
STEP 1: Track down Link2captcha.top in the computer memory
- Open your Task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Carefully review all processes and stop the suspicious ones.

- Write down the file location for later reference.
Step 2: Locate Link2captcha.top startup location
Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
Clean Link2captcha.top virus from the windows registry
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to: %appdata% folder and delete the malicious executable.
Clean your HOSTS file to avoid unwanted browser redirection
Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:

STEP 3 : Clean Link2captcha.top traces from Chrome, Firefox and Internet Explorer
-
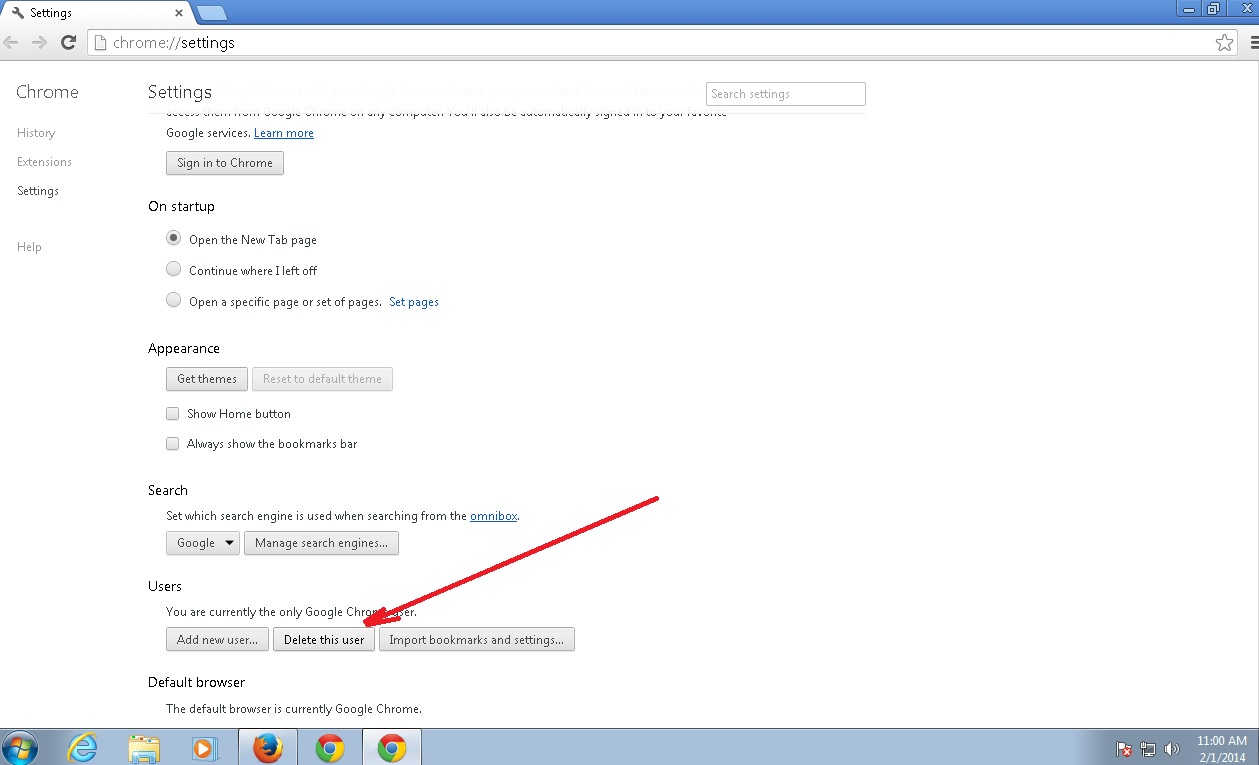
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Link2captcha.top by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
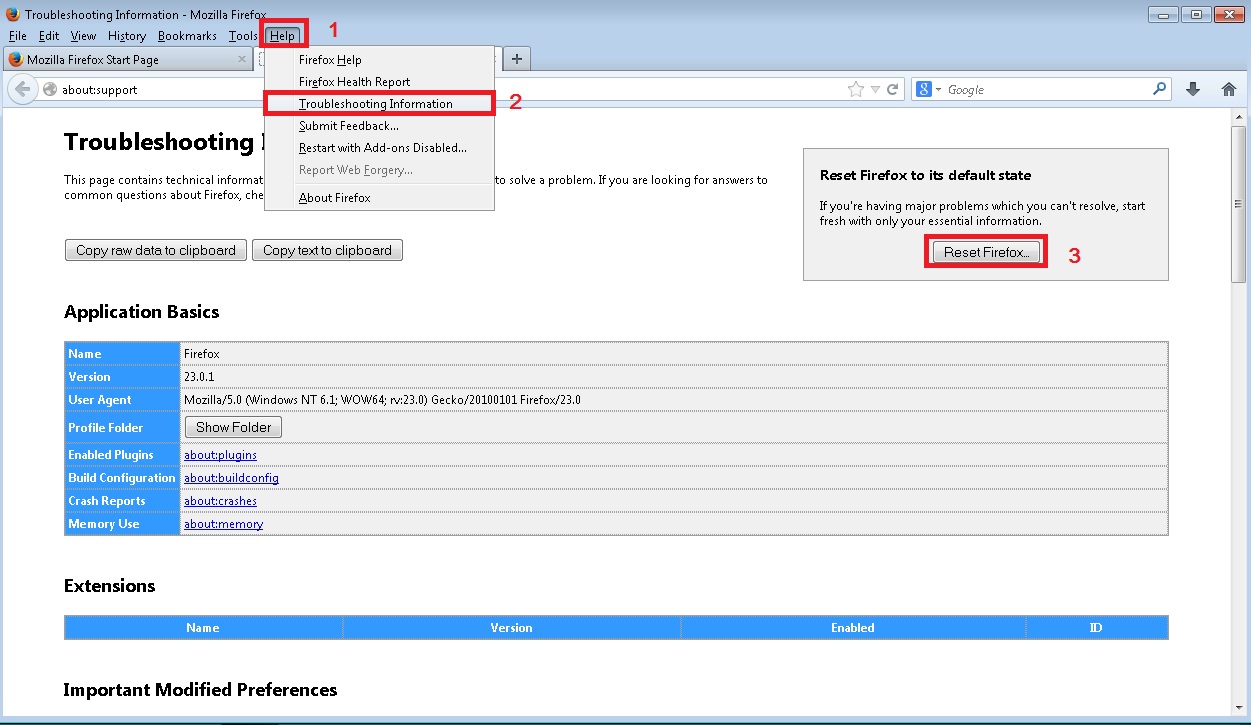
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
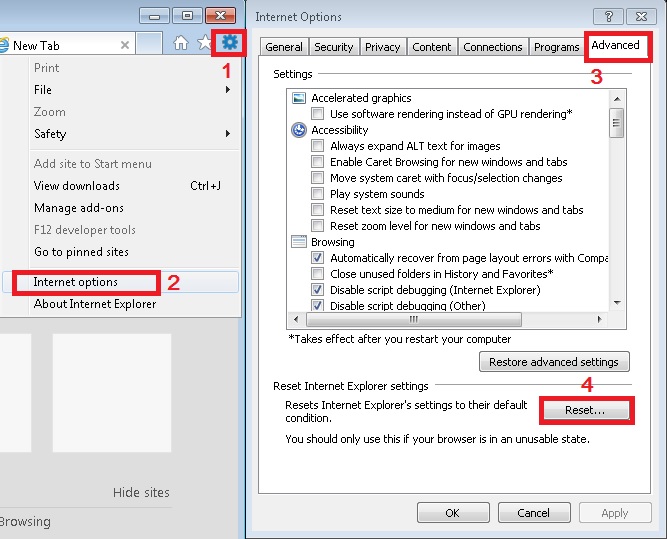
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
Step 4: Undo the damage done by Link2captcha.top
This particular Virus may alter your DNS settings.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for Link2captcha.top, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
You must clean all your browser shortcuts as well. To do that you need to
- Right click on the shortcut of your favorite browser and then select properties.
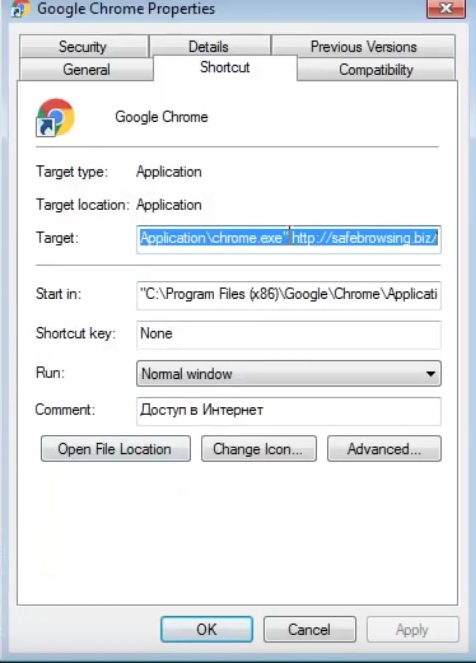
- in the target field remove Link2captcha.top argument and then apply the changes.
- Repeat that with the shortcuts of your other browsers.
- Check your scheduled tasks to make sure the virus will not download itself again.
How to Permanently Remove Link2captcha.top Virus (automatic) Removal Guide
Please, have in mind that once you are infected with a single virus, it compromises your system and let all doors wide open for many other infections. To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.