Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Jaff Ransomware?
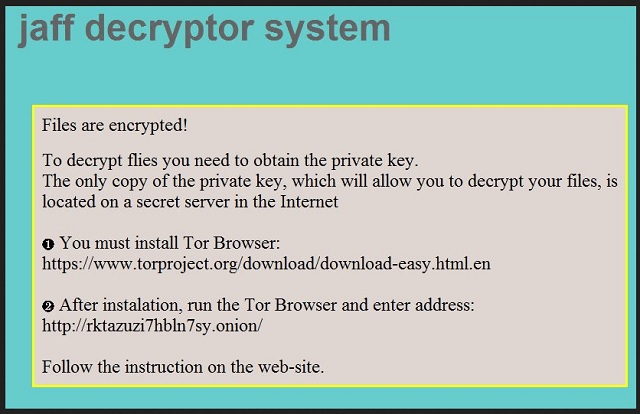
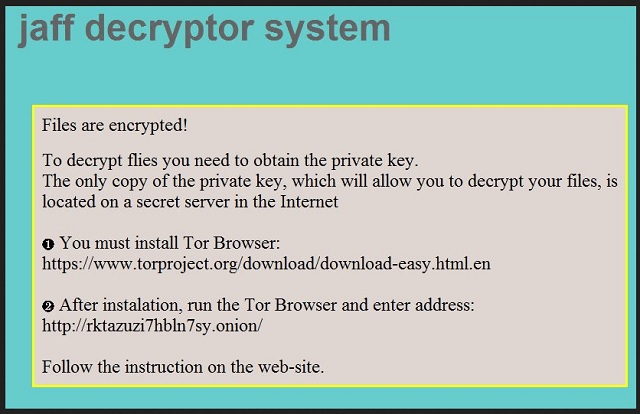
Readers recently started to report the following message being displayed when they boot their computer:
jaff decryptor system
Files are encrypted!
To decrypt flies you need to obtain the private key.
The only copy of the private key, which will allow you to decrypt your files, is
located on a secret server in the Internet
You must install Tor Browser:
https://www.torproject.org/download/download-easy.html.en
After instalation, run the Tor Browser and enter address:
http://rktazuzi7hbln7sy.onion/
Follow the instruction on the web-site.
Your decrypt ID: 1019218184
Jaff is the name of the newest member of the ransomware family. It can encrypt over four hundred file types, including .docx, .jepeg, .xml, .mp4, .pdf, .zip, .MPEG, etc. This means that all your precious pictures, videos, and documents will be locked. The virus will add the “.Jaff” extension to all encrypted files. Thus, if you have a file named example.pdf, the ransomware will rename it to example.pdf.Jaff. You will be able to see the icons of your files, however, you can’t open or use them. Jaff is a dangerous win-locker. It copies the design of the infamous Locky ransomware. Both viruses have almost identical ransom notes and payment instructions. Jaff is much more obnoxious, however. It holds your files as hostages and demands the impossible sum of 1.82 Bitcoins (about 3 227 USD) as a ransom. Such an enormous sum. The hackers behind Jaff are quite confident in themselves. Some versions of the ransomware demand more than 2 BTC. This is inconceivable. The ransom note will be displayed only after the encryption process is complete. To ensure that you read it, the virus will save it as three identical files: ReadMe.html, ReadMe.bmp, and ReadMe.txt. Unfortunately, Jaff can modify your system registry. The virus has deleted all shadow copies of your system. This makes file-recovery quite problematic. Therefore, consider discarding your files.
How did I get infected with?
Jaff relies on spam emails to travel the Internet. The scheme is simple. Scammers would send you an email on behalf of a well-known organization. They would also attach a corrupted Microsoft Office document. Once you download and open the attachment, you will discover something strange. There is a .pdf file embedded within the .doc file. It sounds complicated, but it is not. Pop-up windows will guide you through this process. Eventually, you will see a window that states that the document you are trying so hard to open is “protected”. At this point, you will be given the option to enable the editing of the file. If you do so, your computer will get infected. The ransomware will start its malicious activities. Other virus distribution techniques include torrents, corrupted ads, and fake software updates. Yet, if you are vigilant, you can prevent infections. Download software from a reliable website only. Don’t follow questionable links. And stay away from shady websites. Your caution today can spare you troubles in the future. You are responsible for your computer’s security. Do your due diligence. When installing a program, opt for an advanced option. Also, read the terms and conditions. Walk an extra mile when it is needed. In addition, keep your anti-virus up to date.
Why is Jaff dangerous?
This ransomware is blackmailing you. Yes, this is exactly what it does. It has managed to sneak into your machine unnoticed and wreaked havoc on it. Jaff holds your files as hostages and demands an enormous amount of money. Don’t contact the crooks. And don’t even think about paying the ransom. You are dealing with criminals. Nobody can guarantee you that they will send you a working decryption tool, if they send you anything at all. There are many cases when the victims paid the ransom but did not receive a key. Even if the hackers send you the decrypter, there is the chance that it is not working properly. Furthermore, this tool will restore your files. It will not remove the virus itself. The ransomware will re-encrypt your newly restored files. How many times are you willing to pay for your personal files? Your answer should be “zero”! You can’t win a game against criminals. Use a trustworthy anti-virus program and remove the ransomware. This virus has modified your system registry. This means that a system reboot won’t stop the ransomware. Jaff is loaded together with your OS. It is pointless to create new files. The ransomware will lock them too. Furthermore, if you connect an external memory to your PC, the virus will corrupt it. Therefore, do yourself a favor and delete this parasite immediately.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Jaff Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Jaff Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Jaff encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Jaff encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.