Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Bad Rabbit Ransomware?
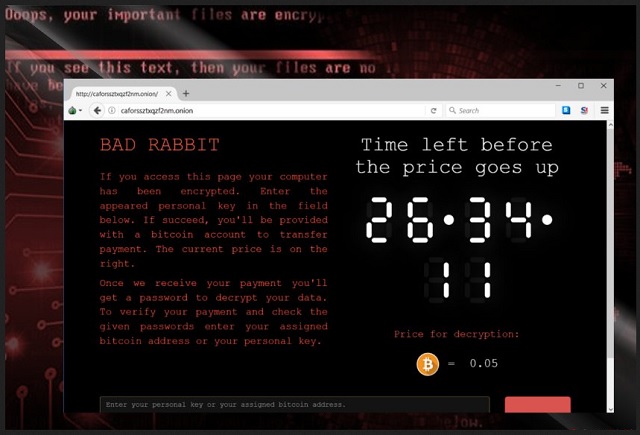
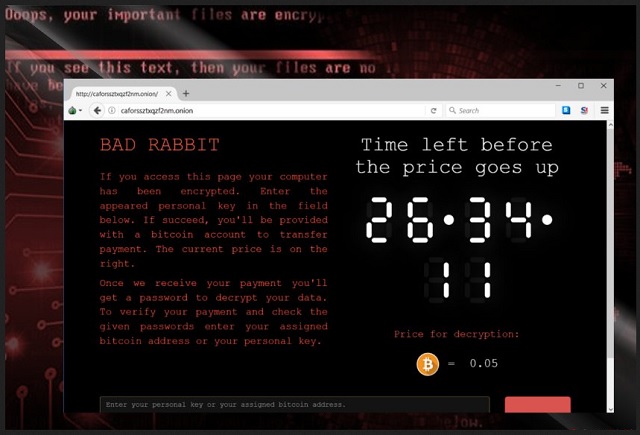
Readers recently started to report the following message being displayed when they boot their computer:
If you see this text, your files are no longer accessible.
You might have been looking for a way to recover your files.
Don’t waste your time. No one will be able to recover them without our
decryption service.
We guarantee that you can recover all your files safely. All you
need to do is submit the payment and get the decryption password.
Visit our web service at {onion web link}
Your personal installation key#1:
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
The U.S., Germany, Japan, Russia, Ukraine, Bulgaria, Turkey – these are just some of the countries Bad Rabbit Ransomware has reached. This program is spreading around the world like wildfire. It was firstly discovered on Tuesday and, as you can see, it’s already a global cyber threat. In fact, Bad Rabbit Ransomware is the third most harmful file-encrypting infection after Petya Ransomware and WannaCry Ransomware. In other words, you’re stuck with one particularly troublesome and dangerous parasite. Bad Rabbit Ransomware seems to be related to the Petya virus. It uses a complicated encrypting algorithm to lock the victim’s personal files. Once Bad Rabbit Ransomware encrypts your information, you can no longer use any of your files. Your data gets modified and effectively locked. Bad Rabbit Ransomware uses AES and RSA-2048 ciphers to encrypt all your personal, precious files. It targets your pictures, music, videos, documents, presentations, etc. Many people store important and often unique files on their computers. It goes without saying that hackers rely on the fact you’d want your encrypted data back. Thus, make sure you always have backup copies of your information. That is the most reliable way to protect yourself from ransomware’s attacks. Keep backups of your files because the Internet is filled with similar infections. Unfortunately, you may cross paths with ransomware again so don’t underestimate the threat these programs cause. Bad Rabbit Ransomware creates Readme.txt files which inform you about the encryption. This is where the scam begins. Cyber criminals only lock your data so they could attempt to blackmail you. Eventually, crooks aim for revenue. It is extremely important to keep in mind that you should never negotiate with hackers. No matter how worrisome your situation is or how anxious you feel, ignore the ransom notes. Hackers are trying to trick you into buying a decryption tool so don’t be naive. Instead of giving into your panic, tackle the ransomware ASAP.
How did I get infected with?
Like most ransomware viruses, this one travels the Web via fake software updates. It pretends to be an Adobe Flash file (“install_flash_player.exe”). Note that it only takes one wrong move to compromise your safety. You cannot afford a single moment of haste online because hackers will take advantage of it. Ransomware programs often get spread via spam messages and email-attachments too. Be careful what you click open as you might accidentally give green light to malware. At this point, it’s pretty clear some infections could cause you irreversible harm. To prevent virus infiltration, watch out for potential intruders. Put your security first and be cautious. Another popular method is called freeware/shareware bundling. When installing software bundles, take your time in the process. We’d recommend that you opt for the Custom/Advanced option in the Setup Wizard. Go through the Terms and Conditions as well. Remember, the key to your safety is your own care. Pay close attention to the programs you end up downloading and be attentive. Last but not least, stay away from questionable torrents, unverified websites as well as third-party pop-up ads.
Why is Bad Rabbit dangerous?
This nuisance also makes several Game of Thrones references. Even though its name doesn’t sound intimidating, Bad Rabbit Ransomware is destructive. The infection holds all your personal, favorite files hostage. It denies you access to your information and demands that you pay a ransom. According to the parasite’s ransom messages, that is the only way to restore your data. However, are really cyber criminals the people you should trust? As mentioned, crooks use ransomware viruses to extort money from gullible PC users. The sum hackers requite this time is 0.05 Bitcoin which is approximately 287 USD. Bear in mind that paying would make matters worse. Hackers have no reason whatsoever to keep their end of the bargain. You may end with your files still locked and your money gone. To prevent that, restrain yourself from following hackers’ instructions. Keep your Bitcoins and forget about the decryptor crooks promise. Delete the Bad Rabbit Ransomware right away. You will find our detailed manual removal guide down below.
Bad Rabbit Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Bad Rabbit Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Bad Rabbit encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Bad Rabbit encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.