Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Werd Ransomware?
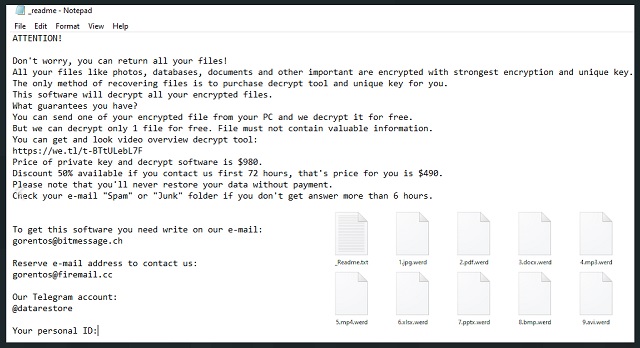
Readers recently started to report the following message being displayed when they boot their computer:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
*Redacted for security reasons*
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
To get this software you need write on our e-mail:
gorentos@bitmessage.ch
Reserve e-mail address to contact us:
gorentos@firemail.cc
Our Telegram account:
@datarestore
Werd File Virus is yet another ransomware. This parasite sneaks into your computer, spreads its roots throughout your entire OS, and corrupts your files. It, of course, does so in complete silence. The ransomware follows programming to avoid detection. It lurks in the shadows and runs its processes in the background. And if you are not sure, that’s bad! You can’t catch the virus in time to limit its corruption. Werd File Virus detects and encrypts your data without triggering any alarms. Pictures, music, databases, archives, documents – there is no immune file format. Werd File Virus puts your precious data under lock and key and drops a ransom note. A file named “_readme.txt” briefly explains your situation, as well as lists the hackers’ demands. The criminals want $490 paid in Bitcoin within 72 hours. They threaten to double the ransom if you don’t fail to meet the deadline. Do not swing into action, though. Take your time and consider the situation carefully. You are dealing with experienced manipulators who know how to push their victims into unwanted actions! Don’t make their job easier. Consider your options and their outcomes. Paying the ransom doesn’t guarantee you anything. The criminals tend to ignore their victims once they receive the money. Don’t sponsor cyber-criminals! Remove the ransomware. If you have backups saved on external devices, you can use them to restore your data. Just make sure that Werd File Virus is completely removed before you attempt any such activities!
How did I get infected with?
Fake updates, corrupted downloads, malicious bundles, pirated software – there are myriads of virus distribution methods. Werd File Virus, however, seems to rely on the classic spam messages. This virus travels the web camouflaged as invoices, canceled flight reports, receipts, warranties, and other bank documents. The crooks know how to trick you into downloading their files. You, of course, know better than to open random documents. You scan everything with an anti-virus app. These files, however, don’t perform suspicious activities. They don’t replicate nor start processes. Your program won’t flag them as malicious. Once you open them, however, you file viewer displays a pop up that asks you to enable the “Editing” mode. Don’t click on that button! If you do, a malicious script will execute and download the virus. Do not fall for the crooks tricks! Don’t make their job easier. Choose caution over carelessness. Your diligence can prevent infections. Even a little extra attention can spare you an avalanche of problems. Be wary of your inbox. Whether it’s an instant message or an email, treat all unexpected messages as potential threats. Always take a minute to verify their senders. If, for example, an organization sends you an unexpected email, go to their official website. Compare the email addresses listed there to the questionable one. If they don’t match, delete the pretender immediately. You can also enter the suspicious addresses into a search engine. Someone might have complained online if the email was used for shady activities.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.

Why is Werd dangerous?
Werd File Virus is a complete and utter menace. It sneaks into your computer, corrupts your data, and blackmails you. It wrecks your PC. You can’t access your documents. You can’t create new files, either. Everything you download or save gets corrupted. The virus pushes you into paying the ransom. Don’t give in! You are dealing with cyber-criminals. Practice shows that these people tend to ignore their victims once they receive the ransom. There are cases when the victims paid just to be blackmailed for more. There are also instances when the victims received nonfunctional or partly-functional decryption software. What will you do if you pay and something goes wrong? You can’t ask for a refund! No one can help you get your money back! The hackers want Bitcoin – an untraceable currency. There is no going back once you complete a transaction. So, don’t act impulsively. That’s what the crooks want. Paying the ransom is the worst you can do. Such actions will only encourage the hackers to continue with their criminal activities! Don’t sponsor them. Remove their virus. That’s your best and only course of action.
Werd Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Werd Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Werd encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Werd encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.