Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Xorist Ransomware?
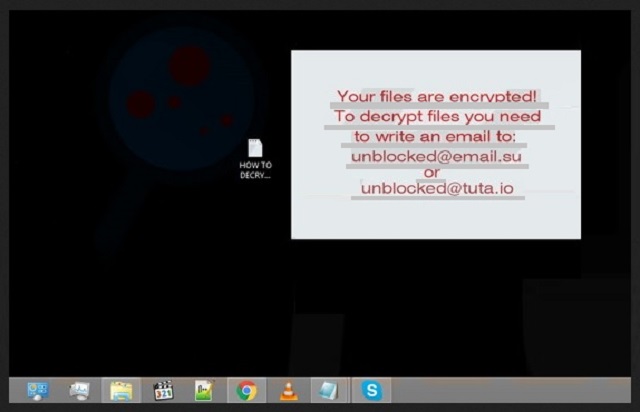
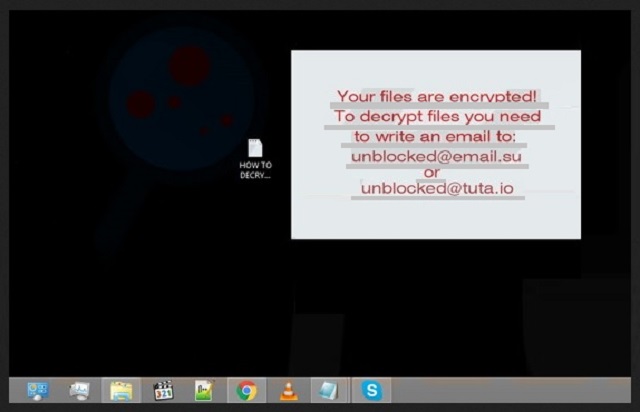
Reader recently start to report the following message being displayed when they boot their computer:
Attention! All your files are encrypted!
To restore your files and access them,
please send an SMS with the text XXXX to YYYY number.
You have N attempts to enter the code.
When that number has been exceeded,
all the data irreversibly is destroyed.
Be careful when you enter the code!
Xorist is part of the ransomware menace. That’s one of the worst cyber infections you can catch. It wreaks havoc on your system and is programmed to target your data. After the pesky ransomware gains access to your computer, it wastes no time and goes to work. And, do you know what that means for you? One day, you’ll turn on your PC, and find every single file, you have stored on it, encrypted, renamed and inaccessible. Xorist takes over. And, none of your data is safe as nothing is beyond the infection’s reach. It gets to every single file – pictures, videos, documents, music, etc. It changes the names by adding some unknown extension, which you don’t recognize. And, make no mistake. All your attempts at renaming it will be futile. You can try to change its current name as much as you want, but the file will remain locked. Usually, the malicious tool adds one of these extensions: 6FKR8d, EnCiPhErEd, 73i87A, p5tkjw, or PoAr2w. Here’s an example to clarify your situation. If you have a picture, named ‘awesome,’ after the ransomware is done with it, you’ll find it as ‘awesome.p5tkjw.’ The only chance of freeing your files from the dreaded infection is to comply with its demands. The malware’s requirements are displayed once the encryption is finished. Upon completion of the process, Xorist creates a text file, ‘How to Decrypt Files,’ and places it on your desktop. When you open it, you’ll see what it is that the ransomware asks of you. Experts’ advice is NOT to go through with the ransom. You need to realize this. Xorist is an untrustworthy, hazardous infection, designed and released by unreliable people. So, even if you fulfill your end of the bargain and pay the requested ransom, can you trust them to do the same? Think long and hard before you reply for there’s a .lot resting on your response. To pay up is to allow wicked strangers with agendas into your private life? No data is worth that. Pick your privacy over your data, and don’t pay. Files are replaceable. And, your privacy?
How did I get infected with?
Xorist doesn’t pop up out of the blue as if by magic. Oh, no. Like most infections, roaming the web, it uses the old but gold methods of infiltration to gain entry. It turns to slyness and subtlety, and since it’s positively masterful in the art of deceit, manages to sneak into your system and without you even realizing it at first. That’s right. The tool is so skilled in its trickery that it slithers in undetected. And, by the time you do become aware of its presence, it’s too late as the damage is already done. The pesky program’s usual antics involve hiding behind spam email attachments, corrupted links or sites, peer to peer networks (like Torrent), or freeware. The nasty ransomware can also hitch a ride in by pretending to be a bogus update, like Java or Adobe Flash Player. There is a common characteristic all of these methods share. Can you spot it? The pattern is that they all rely on your distraction, haste, and gullibility. Understand that cyber threats prey on your carelessness. If you don’t provide it, you increase your chances of keeping your system infection-free. Be more thorough and vigilant when downloading files from unreliable sources, don’t open emails from unknown senders, and do NOT open the attachments they contain. Be more careful and you’d be surprised how much trouble even a little extra attention can end up saving you.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Why is Xorist dangerous?
After Xorist activates and takes over your computer, you’re left with encrypted files, no Internet access, no way to open your Task Manager, and a text file on your desktop, named ‘ How to Decrypt Files.’ When you open it, you’ll understand what the infection requests you to do. Naturally, it demands money in exchange for the decryption key, which will free your files. The message claims that you have to contact the kidnappers via SMS by using the provided phone number. There’s also a specified text you need to send, and you have a limited number of attempts to do so. If you fail, you can’t contact these people, cannot get the key, and cannot release your files from their captivity. It’s the avalanche effect. Each time your text differs from the established pattern in the text file, the number diminishes. Xorist is created, using Encoder Builder, which is purchased from the dark web malware and exploit forums. The builder permits the cyber criminals to customize: they can input their message when demanding ransom, choose their file encryption algorithm (XOR or TEA), everything. After a simple configuration, these future file-kidnappers are given a ransomware executable file that they can distribute via the various methods of infiltrations, laid out in the previous paragraph. And, then they can make money off of your fear, panic, misery, rage, etc. You get the point. They customize the infection, release it on your computer, and wait around until you give them money or lose your files. But here’s the thing. Even if comply with every single one of their requirements, there are NO guarantees that you’ll regain your data. None whatsoever! After all, you’re dealing with sneaky, deceitful, wicked individuals, who seek to exploit you for profit. You can’t expect them to keep their word of providing you with the proper decryption key. And, in the off-chance that they do, and you free your files, what do you think will happen the very next day? There’s nothing stopping the ransomware from kicking right back in and encrypting everything. And, you’re back to square one. Only this time you have less money, and by paying the first time, you’ve opened the door to malicious strangers into your personal and financial information. Do you believe that will end well? Hardly. It’s a pretty lucrative extortion scheme for these people. And, just as it’s great for them, it’s horrendous for you. For you, it’s a lose-lose situation. So, don’t play the game at all. Choose your privacy over your data, and don’t pay. Files, you can replace. Privacy, on the other hand, no. Understand that once you grant access to your private details to these people, there’s no coming back from that. So, don’t.
Xorist Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Xorist Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Xorist encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Xorist encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.