Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove Xlsearch.net hijacker virus? This page includes detailed Xlsearch.net Removal instructions!
Xlsearch.net is not just a regular web page. It is the face of a nasty browser hijacker. This page will try to trick you into downloading software. Be careful. Your computer is already compromised with the xlsearch.net hijacker. You certainly don’t need another parasite on board. The good news is, the hijacker can be removed completely. There is a catch, of course. To remove it with ease, you must act promptly. Let it stay, and hell will rise. The malicious tool will bombard you with advertisements. You will see pop-up messages on websites that used to be ad-free. Coupons and great deals will blink in all imaginable colors. Every website you visit will be heavy on ad banners. Your browser will struggle to display any content correctly. These issues are just the beginning of a stream of problems. They are minor compared to what the hijacker is doing behind your back. This furtive utility is working on your CPU and uses a lot of RAM. It is slowing your computer down. Some older machines may freeze and crash frequently. This may lead to data loss. Also, the ads you are seeing may be malicious or they may be leading to dodgy websites. The hijacker uses a pay-per-click system. To guarantee its owners’ income, this tool will allow anyone to promote. Hackers get an advantage of such tools. They use hijackers to spread malicious content. If you click on a corrupted link on an ad, you will be taken to an infected website. There, a drive-by download can distribute a virus directly to your computer. Unfortunately, there is no way to tell which ads are legit and which are not. Try to avoid all commercials while the malicious app remains active on your device. This, however, is easier said than done. The hijacker will try to trick you into clicking on ads unintentionally. At the most unexpected times, it will open pop-up windows right under the cursor of your mouse. Do yourself a favor, remove the xlsearch.net hijacker ASAP!
How did I get infected with?
The xlsearch.net hijacker might have arrived as an extra app. Developers often attach additional programs to the installation files of many free tools. This method is known as bundling. It is quite common nowadays. This technique relies on your carelessness. When installing a program, opt for advanced installation wizard. This process may be presented as a suitable option for IT experts only. Yet, it is not complicated. Use it. Only under it can you see all additional tools that are about to be installed. Take your time. If you think that something looks suspicious, there probably is a good reason for that. Install only the tools you trust. Other malware distribution techniques use the same formula. Spam messages, fake software updates, and torrents, all these methods will fail if you are vigilant. Download your software from reliable websites only. Also, don’t skip the terms and conditions/EULA. This step is time-consuming and annoying, but it is the only way you can spot breaches. This is your computer. You are responsible for its security.
Why is this dangerous?
The xlsearch.net hijacker is exposing you to numerous risks. To select the right kinds of ads for you, this tool will monitor all your online activities. It won’t use the collected data for marketing purposes only. The malicious app will sell every bit of information to third parties. Anyone can be that third party. Including hackers. If you use your PC to make an online purchase, the hijacker will record your billing address and credit card details. Can you imagine the consequences if a hacker buys this data? Furthermore, the ads themselves can be dangerous. A corrupted ad can download a virus directly on your computer. And, of course, we must mention the annoyance the hijacker causes. You will start to avoid your own computer. This tool will slow it down to a crawl. Every time you go online, you will be drowned in a sea of ads. This is hard to be tolerated. The worst part is, the commercials will only become more aggressive. The longer this parasite remains on your machine, the more irritating the commercials will become. Luckily, you don’t need to put up with this. Use our guide and remove the xlsearch.net manually. If you prefer automated solutions, you can always download a trustworthy anti-virus program. The sooner you remove the hijacker, the better!
How to Remove Xlsearch.net virus
The Xlsearch.net infection is specifically designed to make money to its creators one way or another. The specialists from various antivirus companies like Bitdefender, Kaspersky, Norton, Avast, ESET, etc. advise that there is no harmless virus.
If you perform exactly the steps below you should be able to remove the Xlsearch.net infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Please, keep in mind that SpyHunter’s scanner tool is free. To remove the Xlsearch.net infection, you need to purchase its full version.
STEP 1: Track down Xlsearch.net related processes in the computer memory
STEP 2: Locate Xlsearch.net startup location
STEP 3: Delete Xlsearch.net traces from Chrome, Firefox and Internet Explorer
STEP 4: Undo the damage done by the virus
STEP 1: Track down Xlsearch.net related processes in the computer memory
- Open your Task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Carefully review all processes and stop the suspicious ones.

- Write down the file location for later reference.
Step 2: Locate Xlsearch.net startup location
Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
Clean Xlsearch.net virus from the windows registry
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to: %appdata% folder and delete the malicious executable.
Clean your HOSTS file to avoid unwanted browser redirection
Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:

STEP 3 : Clean Xlsearch.net traces from Chrome, Firefox and Internet Explorer
-
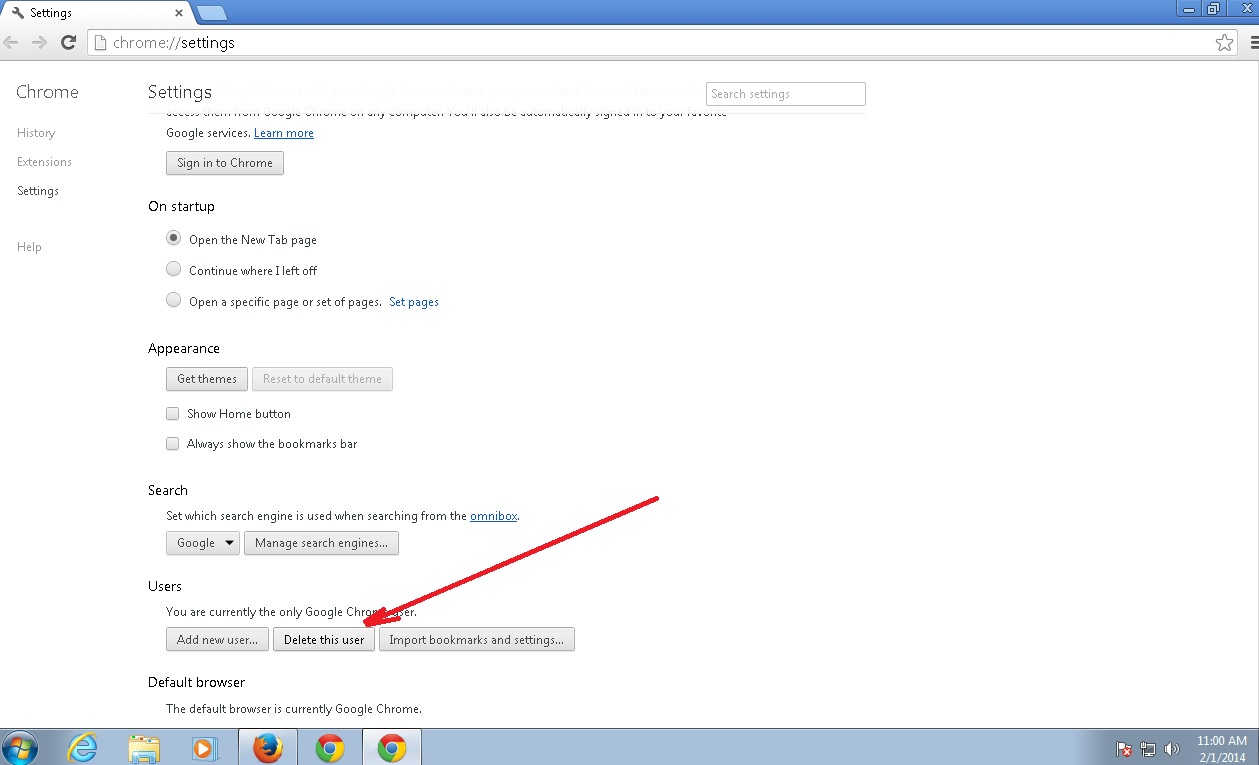
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Xlsearch.net by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
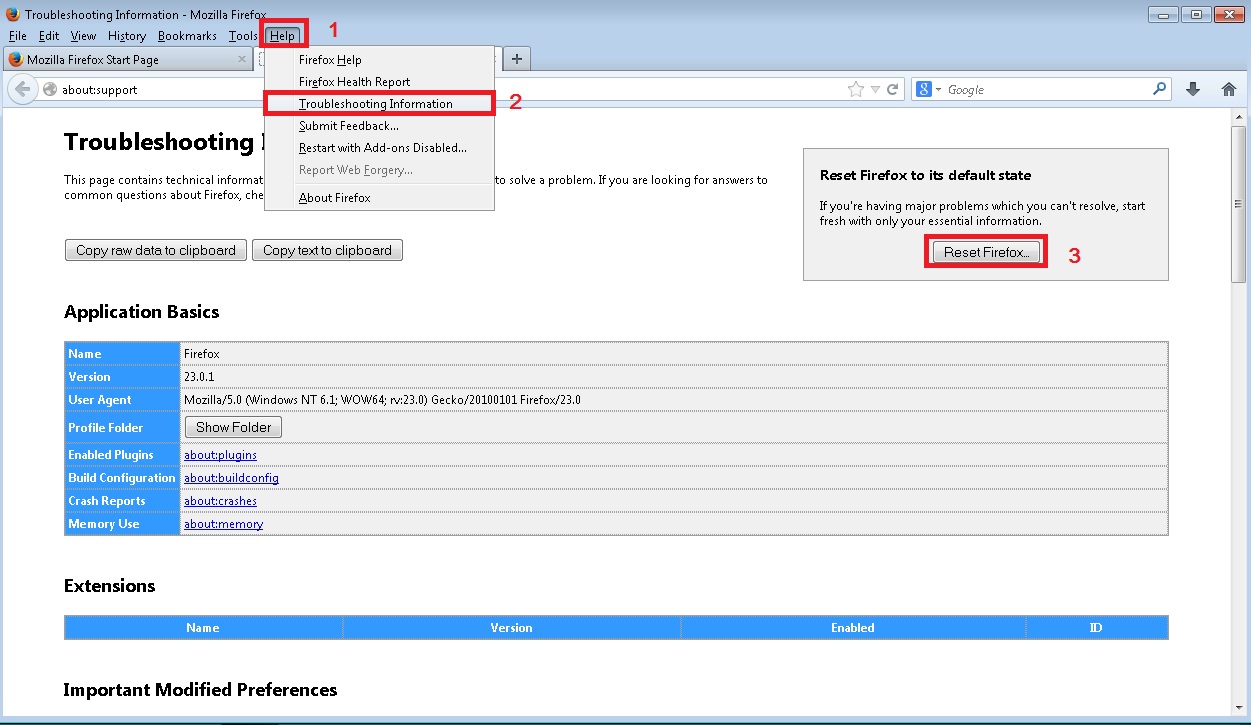
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
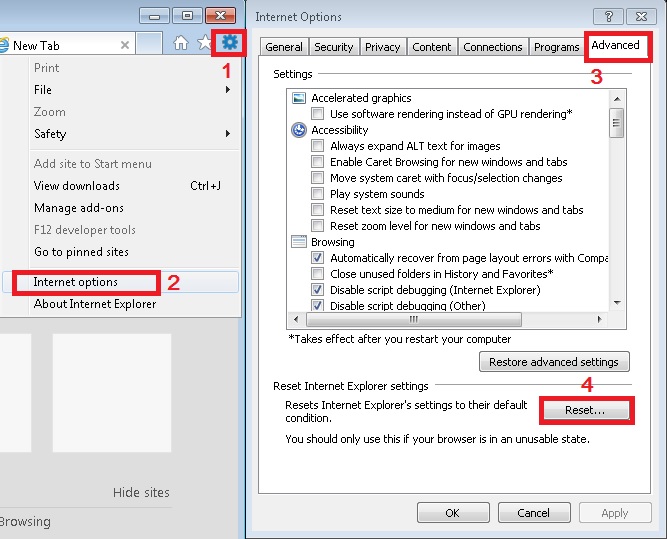
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
Step 4: Undo the damage done by Xlsearch.net
This particular Virus may alter your DNS settings.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for Xlsearch.net, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
You must clean all your browser shortcuts as well. To do that you need to
- Right click on the shortcut of your favorite browser and then select properties.
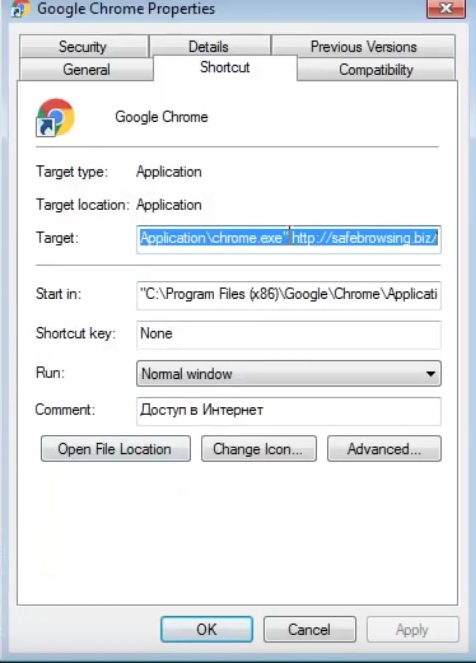
- in the target field remove Xlsearch.net argument and then apply the changes.
- Repeat that with the shortcuts of your other browsers.
- Check your scheduled tasks to make sure the virus will not download itself again.
How to Permanently Remove Xlsearch.net Virus (automatic) Removal Guide
Please, have in mind that once you are infected with a single virus, it compromises your whole system or network and let all doors wide open for many other infections. To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.