Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
| Virus Name | XHAMSTER Ransomware |
| Infection symptoms | All images, videos and documents append “.XHAMSTER” extension and cannot be opened by any program! |
| Type of threat | Ransomware, cryptovirus, file-locking virus |
| File Extension | .XHAMSTER |
| Encryption type | AES algorithm using 256-bit key. |
| Ransom Note | _readme.txt |
| Amount of Ransom | determined by the hacker |
| Contact | ICQ@xhamster2020 |
| Genealogy | Phobos Ransomware Family |
| Aliases | Win32.Neshta.A; Win32:Apanas [Trj]; Ransom:Win32/; AI:FileInfector.D5C3B0640E; Neshta.Virus.FileInfector.DDS
more detections in VirusTotal |
| Distribution | Spam email attachments, RDP, pirated software, torrent websites, phishing sites, malicious weblinks etc… |
| Remediation Tool |
In order to completely remove ransomware from your computer, you will need to install an antivirus software. We recommend using SpyHunter |
| Recovery Tool |
The only effective method to restore files is to copy them from a saved backup. If you don’t have a suitable backup, you may use third-party recover software such as iBeesoft Data Recovery |
How to Remove .XHAMSTER File Extension Ransomware?
A virus known as XHAMSTER ransomware can encrypt all personal files on your computer, rendering them all inaccessible. This specific variation of the XHAMSTER file virus is a member of the Phobos ransomware family. When it infects a system, it locks all of the data using military-grade encryption and appends a lengthy extension to each file carrying the victim’s ID, the hackers’ ICQ username, and a marker identifying the existence of XHAMSTER ransomware. For instance, a file called “It would become “1.jpg.id[C291B210-3542].[ICQ@xhamster2020] instead of “1.jpg.” XHAMSTER, “and the labels for all other affected files would be the same. Additionally, the ransomware leaves ransom-demanding notes (info.hta and info.txt) on the infected machine, asking the user to pay a fee in exchange for a tool that would unlock the locked files.
The main objective of the XHAMSTER ransomware is to hold the victim’s files hostage in order to extract money from them. The data is locked using 256-bit AES encryption, and only the attackers’ private key can be used to unlock the files. They provide the option to buy this key and the decryption program from them, but they want a hefty ransom in return.

Demands of XHAMSTER virus:
The precise sum that victims must pay as ransom is not stated in the ransom note delivered by the XHAMSTER ransomware. The amount will, however, depend on how quickly the victims establish contact with the assailants, it is stated. Only Bitcoin payments will be recognized. In order to demonstrate that the hackers have the capability of decrypting all compromised data, the letter also instructs users to contribute up to 5 files for free decryption. These files shouldn’t include any significant or valuable information, and they shouldn’t be larger than 3MB. The same ICQ account that may be seen in the names of the encrypted files is where victims are instructed to get more information.
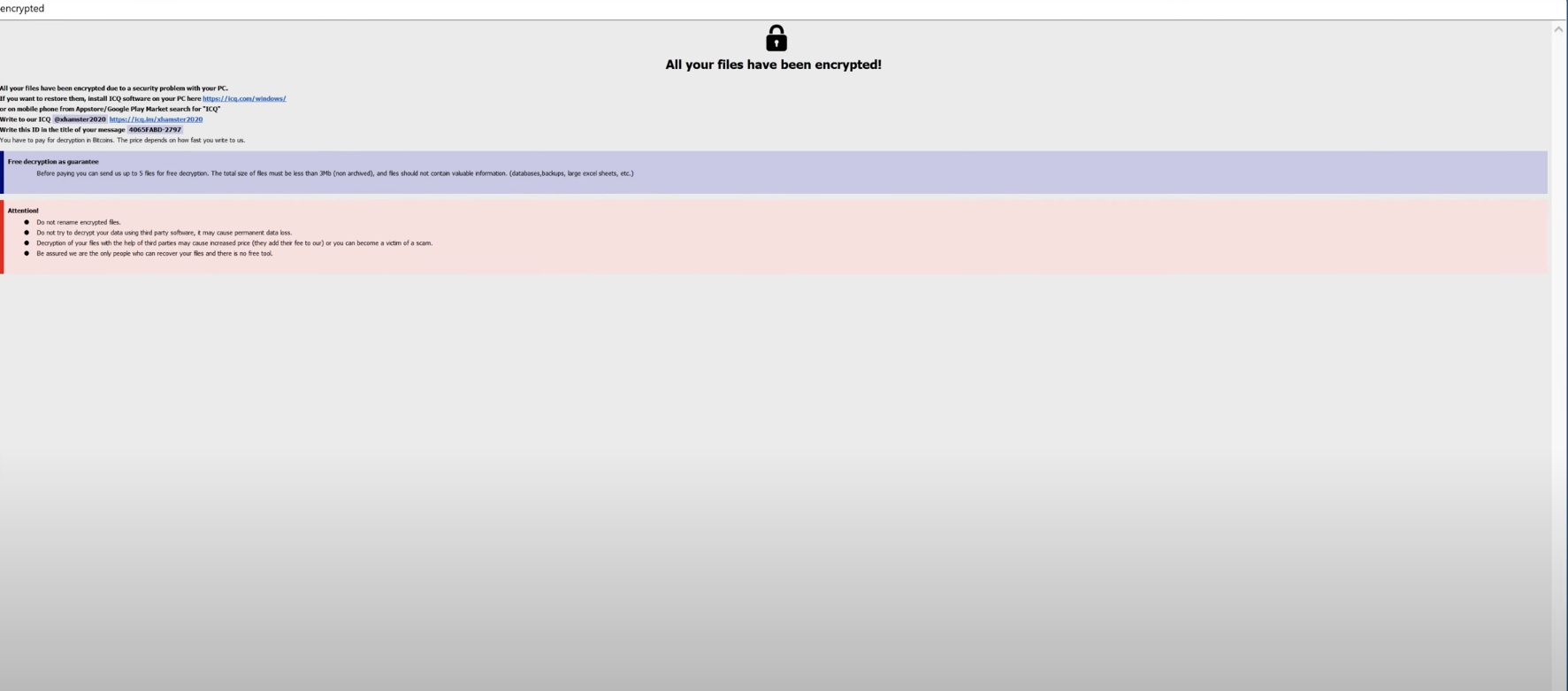
Example of a ransom note and alert message from the XHAMSTER Ransomware
All your files have been encrypted! All your files have been encrypted due to a security problem with your PC. If you want to restore them, install ICQ software on your PC here https://icq.com/windows/ or on mobile phone from Appstore/Google Play Market search for “ICQ” Write to our ICQ @xhamster2020 https://icq.im/xhamster2020 Write this ID in the title of your message – You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. Free decryption as guarantee Before paying you can send us up to 5 files for free decryption. The total size of files must be less than 3Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.) Attention! Do not rename encrypted files. Do not try to decrypt your data using third party software, it may cause permanent data loss. Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam. Be assured we are the only people who can recover your files and there is no free tool.
Where does the XHAMSTER ransomware originate from, and how can we avoid getting infected again?
XHAMSTER ransomware is a particularly aggressive and prevalent type of malware that can be spread through questionable downloaded software or software installation bundles. In order to make files inaccessible and force victims to look for a solution through decryption or restoring from a backup copy, it has the ability to rename files by adding the developer’s information and a new file extension. Our research and technical investigation revealed that no third-party tools are able to decode files encrypted by XHAMSTER, giving victims limited options.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
XHAMSTER is a ransomware threat that, like many others, may spread quickly through spam emails and their attachments, including PDF files, ZIP files, RAR files,.exe executable files, JavaScript files, and even dangerous Microsoft Office documents. It can also spread via compromised websites that provide fraudulent software downloads or activation tools or through dubious online sources. These websites frequently provide the impression that they are reliable or trustworthy in order to deceive users into downloading dangerous files.
Many malicious downloads that spread the XHAMSTER ransomware also have a Trojan horse payload that can silently load onto a computer without the user or administrator being aware of it. In these situations, it’s possible for victims to be infected without realizing it until they receive the ransom warning; by that time, it might be too late to stop the XHAMSTER ransomware from carrying out its attack.
It’s crucial to refrain from downloading dubious software files or installation bundles from third-party sites or those that contain undesired content in order to safeguard yourself from infection with the XHAMSTER ransomware and other dangerous malware. Additionally, spam emails and attachments should always be avoided, even if they seem to be authentic or to come from a reputable source. It is essential to remove any suspicious emails or attachments as soon as you come across them. Last but not least, it is a good idea to routinely backup your crucial data in case of an attack or other occurrence that results in data loss.

Why is .XHAMSTER File Extension dangerous?
Ransomware is particularly dangerous for two reasons:
- First, it encrypts your data and locks them away behind strong encryption algorithm.
- Second, the hackers behind ransomware may not unlock your files even after you pay the ransom.
It is important to remove .XHAMSTER file extension virus once found on the computer. This infection is created for the purpose of generating money for its creators. It does it by encrypting all user’s files and after that asking to pay a ransom in order to decrypt them. There is no guarantee that you could get your files back even if you do what this malicious application requires from you, so removing .XHAMSTER file extension virus is essential.
Do not pay for XHAMSTER ransom!
Please, try to use the available backups, or Decrypter tools

.XHAMSTER File Extension Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover .XHAMSTER File Extension Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with .XHAMSTER File Extension encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate .XHAMSTER File Extension encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
Do NOT send money for decrypt of “XHAMSTER” files!
The cyber criminals behind XHAMSTER ransomware guarantee to send you the code after you pay. However, all you’ve got is a promise from bad people. You have no warranty whatsoever. We recommend not to rely on words of internet criminals. If you pay this will continue to happen.

STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software like iBeesoft Data Recovery to try recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.
- If by any chance you did not have internet access when the encryption took place, you can try to recover them by using Emsisoft Decryptor for STOP Djvu decryption tool using the Emsisoft Decryptor for STOP Djvu.
- Wait for Antivirus companies to create an XHAMSTER file decryptor.