Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly www-homepage.com took over your homepage and you cannot remove it.
The thing about browser hijackers is that you immediately realize when your PC has been infected with one because the changes it makes to your browser settings are obvious. The main modifications affect your default homepage and search provider as they will be replaced as soon as the infection gains access to your browser. So, if Www-homepage.com suddenly appears in the place of your homepage and search engine, it is clear what you will have to deal with – a browser hijacker. Infections of this type are not only intrusive, but they will also endanger your system by exposing it to a number of dangerous threats. For this reason, the Www-homepage.com hijacker has to be eliminated right away.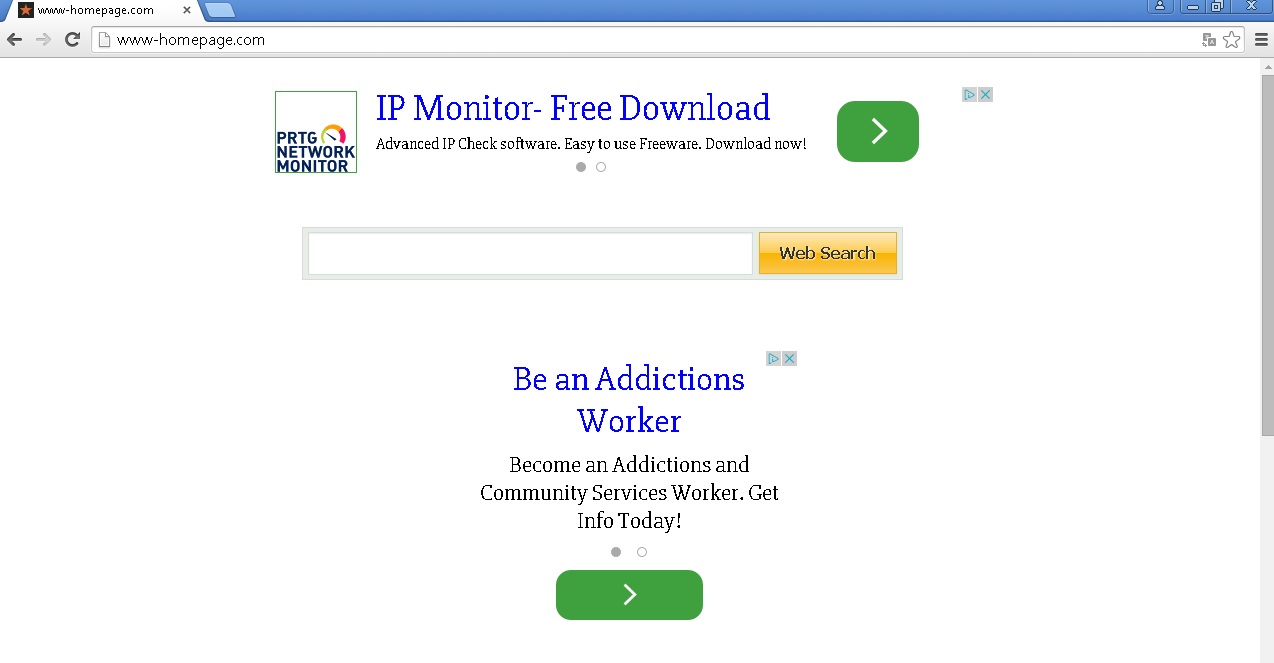
How did I get infected with?
Browser hijackers, adware programs, and potentially unwanted programs in general are all the same according to the way they are distributed. You can assume that such infections would not be spread officially or downloaded directly. In the majority of cases they arrive on the system attached to the installers of supposedly genuine free applications promoted at unknown file sharing website. Users often acquire such application without realizing the possible dangers to their virtual security. Another common mistake users make is clicking ads and links they see on questionable web pages. This way various infections are granted access to the PC and the consequences could be damaging.
Why is this dangerous?
Very often user think that they can remove Www-homepage.com by switching the browser or by opening a new tab. Of course, the hijacker is serious enough of an infection, so none of this works. Once it hijacks your browser, you will have no choice but to use Www-homepage.com if you want to browse the web. Although the search results it will provide you with may seem genuine, most of them will be sponsored and leading to suspicious websites. It is never a good idea to visit such websites, which is why relying on results by Www-homepage.com is out of the question. Another disturbing feature of the hijacker is its ability to record information about your system and browsing habits, which is another thing you should not tolerate. If Www-homepage.com has taken over your browser, make sure you do not use it until the infection is completely removed from it.
How to Remove Www-homepage.com virus
If you perform exactly the steps below you should be able to remove the Www-homepage.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Www-homepage.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Www-homepage.com from Add\Remove Programs
STEP 2: Clean Www-homepage.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Www-homepage.com leftovers from the System
STEP 1 : Uninstall Www-homepage.com from your computer
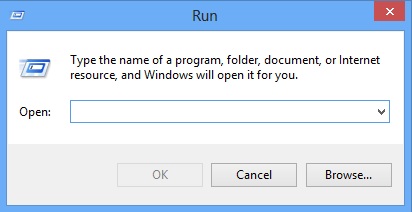
Simultaneously press the Windows Logo Button and then “R” to open the Run Command
Type “Appwiz.cpl”
Locate the Www-homepage.com search software and click on uninstall/change. In general you should remove all unknown programs.
STEP 2 : Remove Www-homepage.com homepage from Chrome, Firefox and IE
-
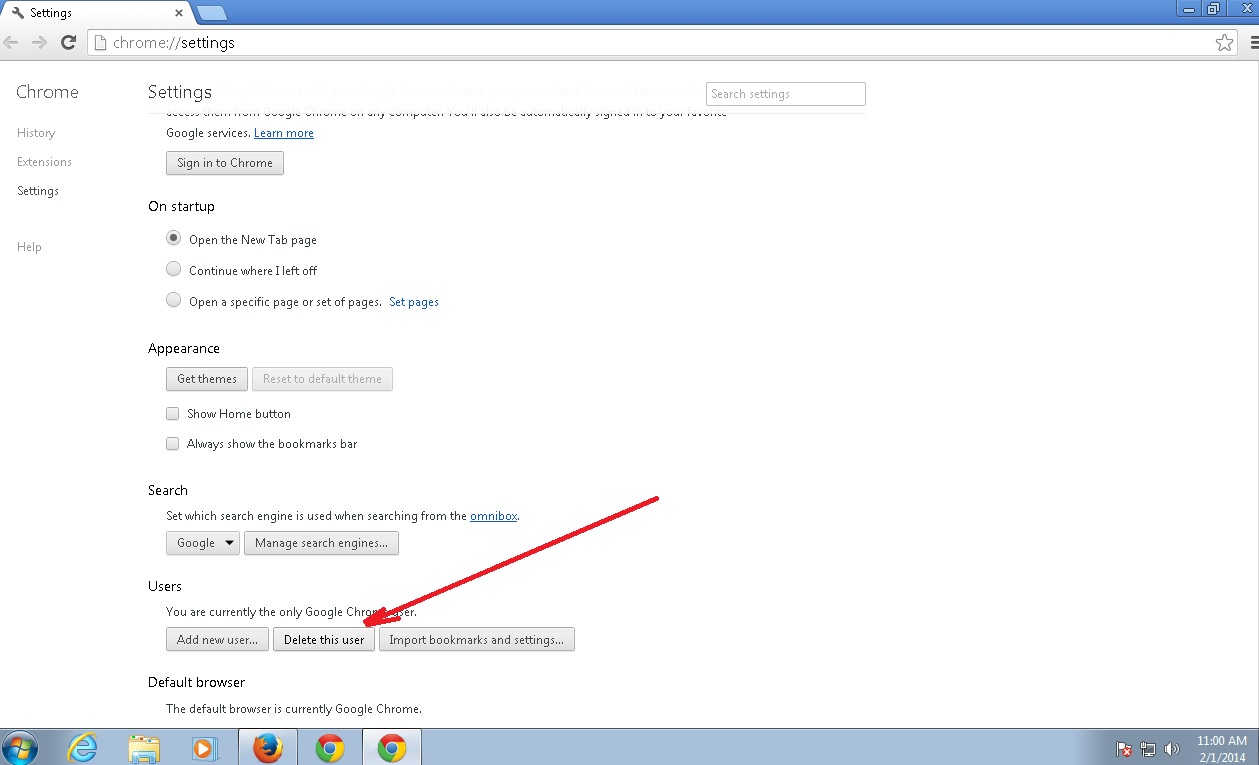
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Www-homepage.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
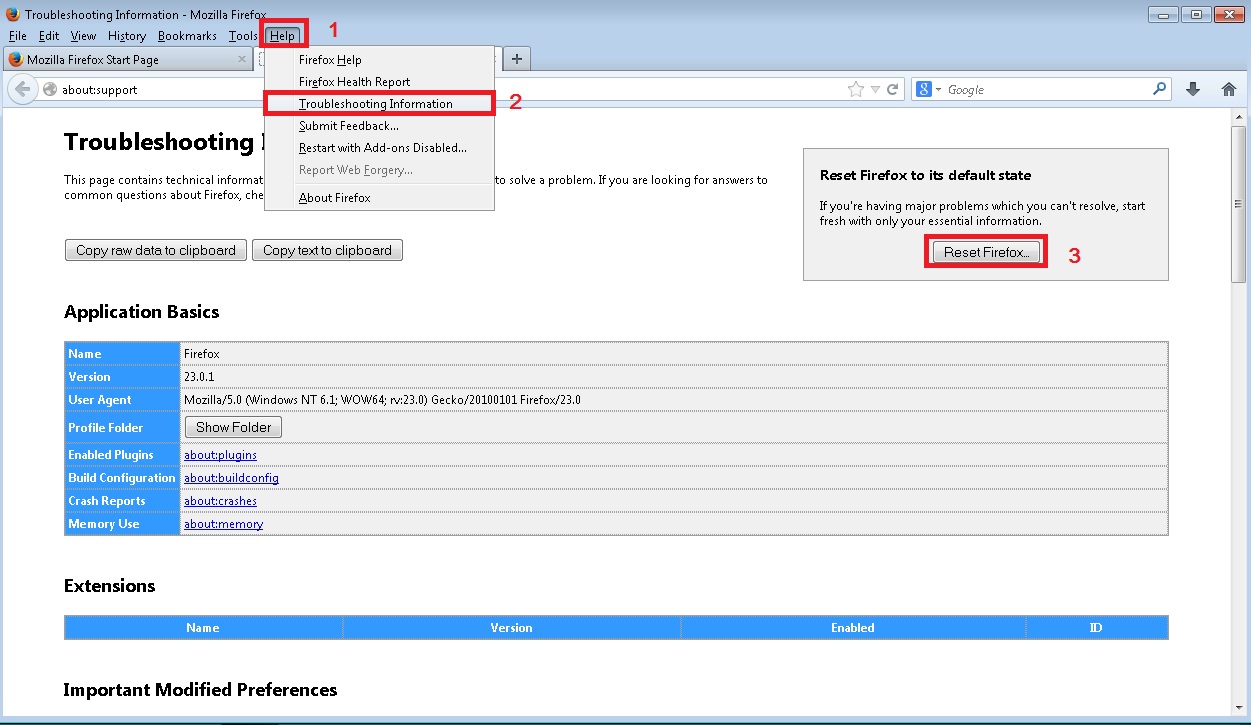
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
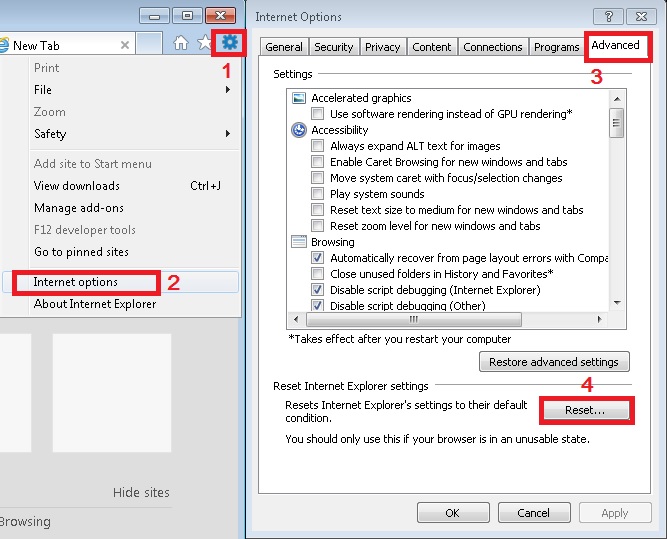
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove Www-homepage.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.