Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Unlock26 Ransomware?
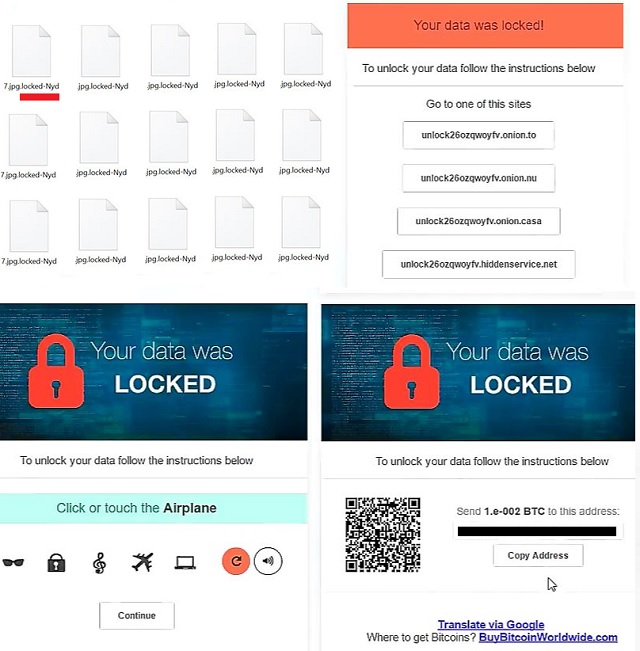
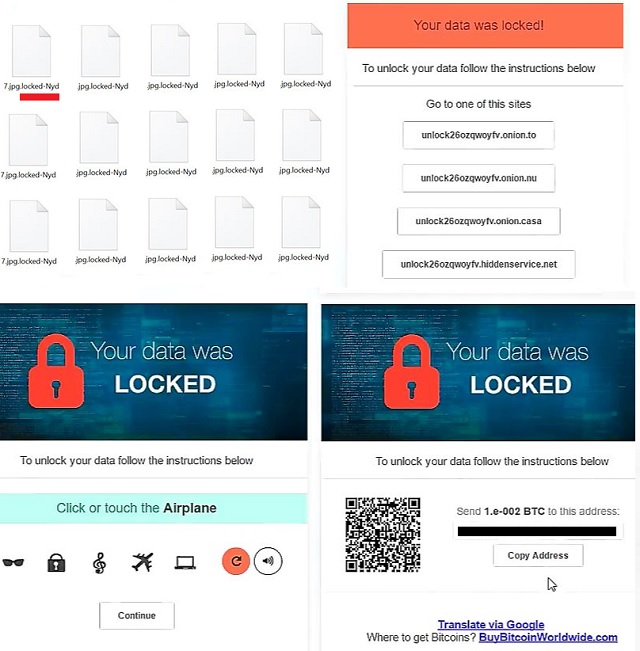
Readers recently started to report the following message being displayed when they boot their computer:
To unlock your data follow the instructions below
Send 1.e-002 BTC to this address:
1BX9ktr9wXkuBeBb7fo1p5ZPkc4J5F9Fub
Unlock26 is a dreadful program that pushes you into a whirl of problems and unpleasantness. It falls under the umbrella of ransomware, and it’s hazardous. Ransomware applications are notorious among web users. They invade your system via deception and trickery. And, once they enter your system, take over. They encrypt every bit of data you keep, and demand payment for its release. So does Unlock26. It backs you into a corner. Whatever you do, don’t comply with the cyber extortionists behind the tool! Compliance only worsens your predicament. If you are thinking how it can even get worse, it can! There is a way! If you comply, and pay up, you expose your private information. Then, cyber criminals get a hold of your personal and financial details. And, that’s a whole different type of ‘dangerous.’ Don’t let that scenario unfold. Protect yourself. You may have lost your data to these cyber kidnappers. But, at least, keep your privacy private. Minimize the damage, the ransomware plague makes. Forsake your files in the name of your security. Losing your data is the lesser of two evils.
How did I get infected with?
Unlock26 slithers into your system via slyness and subtlety. It turns to the old but gold methods of invasion to gain entry. But without you, it cannot succeed in its sneakiness. Let’s elaborate. The tool needs one crucial ingredient for its success. Your carelessness. It needs you to throw caution to the wind, and give into naivety. It needs you distracted, and in a rush. It makes its infiltration that much easier. Only because the invasive methods it turns to work best with you careless. If you’re vigilant enough, you can catch the program attempting its invasion. And, prevent it. But if you aren’t thorough, odds are, it will slip past you. The most preferred methods include spam email attachments and freeware. Also, corrupted links or websites. And, also, fake system or program updates. Like, Java and Adobe Flash Player. Always read the terms and conditions when installing tools or updates. Don’t underestimate the impact of due diligence. Choose caution over carelessness. One leads to an infection-free PC. The other leads to hassles and headaches.
Why is Unlock26 dangerous?
Unlock26 is yet another file-encrypting program, roaming the web and plaguing users. It’s an utter dread. It targets every bit of information, you have on your computer. Pictures, videos, music, documents. Nothing escapes its clutches. Unlock26 uses RSA-2048 key to lock everything. With the AES CBC 256-bit encryption algorithm, it takes control of your data. It attaches a special extension at the end of each of your files. Thus, solidifying its keep over them. For example, say, you have a picture called ‘summer.jpg.’ After the tool’s done with it, you find it renamed. It’s ‘summer.jpg.locked-dmx.’ Once the attachment gets put into place, you cannot open your files anymore. Moving or renaming them does nothing. The only way, to regain control, is compliance. The program leaves a message on your Desktop. As well as an HTML file, containing its demands in each of your folders with locked data. It bears the name ReadMe-Nyd.HTML, and seeks a ransom of about $60. That’s 0.06 in Bitcoins. As was already explained, payment is an ill-advised strategy. Think about it. You have zero guarantees it will work. You’re going on the word of nasty cyber criminals. Do you honestly believe these people will keep their word? That, they’ll hold their end of the bargain? Don’t be naive! You’ve already lost your files. Don’t lose your privacy, as well. Discard your data. It’s the better alternative.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Unlock26 Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Unlock26 Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Unlock26 encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Unlock26 encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.