Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Shark Ransomware?
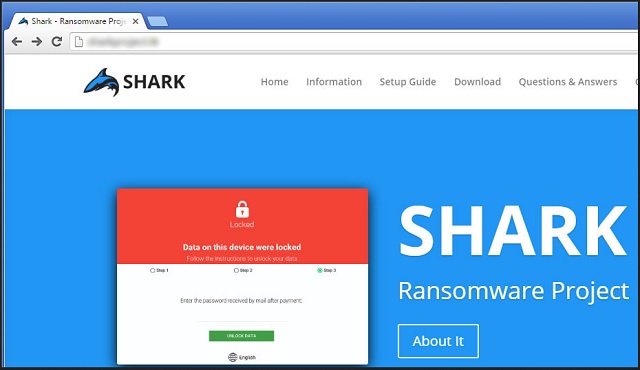
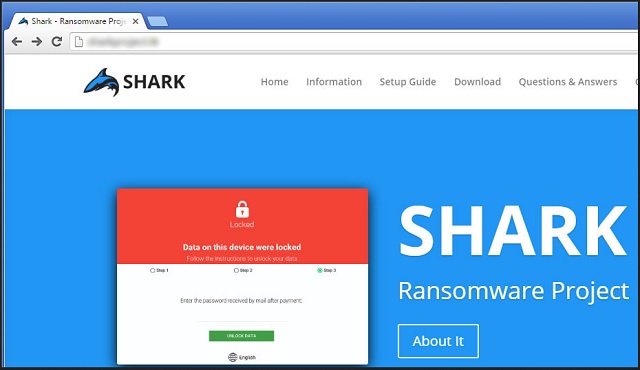
The Shark Ransomware project allows you to create ransomware. Just think about it. You now have the power to build your very own destructive, devastating parasite. Ransomware is probably the worst type of virus that’s roaming the Web. And, thanks to Shark Ransomware, you’re able to customize it and spread it online. As you could imagine, that would turn you into a cyber criminal. There are people out there who don’t mind being outside the law, though. Those are the people you should be worried about. Shark Ransomware basically gives anyone the chance to wreak havoc. Malevolent people have the opportunity to create ransomware. You see why this is dangerous, don’t you? Ransomware is a PC virus that encrypts personal data. These programs rename the files you have stored on the computer. By using a complicated encrypting algorithm, ransomware locks your data. It turns all your pictures, videos, music, etc. into unreadable (and unusable) gibberish. Then the virus display a ransom note and demands money in order to set your files free. This is nothing but a clever attempt for an online fraud. Now, back to your problem. The Shark Ransomware pest is quite different from what we’re used to seeing. For starters, it isn’t hosted on an anonymous TOR network like most infections. It has a public website instead. The virus also exhibits one more specific trait that should be mentioned. It belongs to one particularly problematic branch of ransomware programs. It’s called RaaS (Ransomware-as-a-Service) and doesn’t aim for anonymity. Quite the opposite; it attempts to attract new distributors of the virus. Take the infamous Petya and Mischa RaaS, for instance. RaaS programs are on the rise right now so keep in mind how troublesome they might be. Shark Ransomware is no exception. Once you visit its website, you will notice a Download button. By clicking it, you install a zip file named PayloadBundle.zip. It contains a .txt ransom message and the malicious Shark.exe executable. In the zip file you will also find a ransomware builder itself named Payload Biulder.exe. This pest lets you create a customized version of a particularly nasty program. You choose the target files, the target countries, the exact sum of the ransom and the language. Furthermore, you need little or no knowledge at all in order to customize the virus. Yes, it’s that simple. And, as you could imagine, Shark Ransomware is used for evil. All you need to do is pay a certain sum of money to this infection’s developers. They receive 20% of the profit your ransomware gains. This way, hackers not only spread their malicious programs on the Internet. They also trick gullible PC users into gaining dubious profit online. RaaS programs are notoriously harmful so don’t waste time. If you find yourself stuck with Shark Ransomware, take action immediately.
How did I get infected with?
Chances are, the ransomware was sent straight to your inbox. Stay away from spam messages and spam email-attachments in the future. Those two might be among the oldest infiltration methods, but they’re still effective. Furthermore, all kinds of parasites travel the Web this way. You could easily infect your PC with all viruses you could possibly imagine. To prevent this, watch out for malware. Always be careful what you give green light to and don’t overlook hackers’ creativity. Other popular techniques are malicious torrents, dangerous executables, illegitimate websites. The Web is full of threats so be cautious. Pay attention to your safety; this should be your number one priority online. Last but not least, avoid unverified freeware and shareware bundles. You must know that the programs there usually include at least one unwanted intruder. Unless you deselect it on time, you may compromise your own computer.
Why is Shark dangerous?
Shark Ransomware is an incredibly dangerous tool if it gets into the wrong hands. This pest provides endless possibilities for both cyber criminals and their affiliates. As we mentioned, Shark Ransomware is available for anyone to download. Its main goal is to blackmail people by encrypting their personal files. This parasite adds a “.locked” extension to the target data. The minute you come across this malicious file appendix, know you’re in trouble. Ransomware holds your data hostage and demands that you pay a hefty sum of money in bitcoin. It also promises some decryption key in exchange for the ransom. However, there’s no guarantee hackers will grant you any decryptor. All they’re interested in is their profit. Hence, the sooner you uninstall Shark Ransomware, the better. To do so manually, please follow our detailed removal guide. You can find it down below.
Shark Removal Instructions
STEP 1: Kill the Malicious Process
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 3: Locate Startup Location
STEP 4: Recover Shark Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Shark encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Shark encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.