Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Searchpause.com took over your homepage and you cannot remove it.
As you can probably tell, Searchpause.com is unreliable. This program promises to improve your browsing experience. In reality, it’s a deceptive, aggressive and harmful PC infection. Hackers don’t tend to tell the trust about the malware they develop. Therefore, it should come as no surprise Searchpause.com is malicious. It’s been classified as a browser hijacker. Have you had to deal with hijackers so far? Take your time to check out our article because you must know what you’re up against. Hijackers are relatively easy to tackle. Having said that, keep in mind Searchpause.com was created by crooks. It was designed to cause you harm. The sooner you take action and uninstall the parasite, the better. Procrastination will only make your cyber situation worse. Now, this program’s shenanigans begin as soon as your PC gets infected. You will notice several completely unauthorized changes in your browser settings. No, Searchpause.com doesn’t bother to ask for permission. Hackers are in charge now so your preferences simply don’t matter. Apart from the fact this is upsetting, it’s also dangerous. The virus messes with your default browser settings. It adds a malicious extension to your once trustworthy browsers. It also replaces both your homepage and search engine with its own domain. You may come across additional toolbars as well. Do you see why hijackers are named that way? Searchpause.com hijacks your entire browsing experience. This pest generates one very specific type of search results – sponsored ones. It goes without saying sponsored web links could be leading you straight to malware. Hijackers do not discriminate between real and fake links. Both kinds help crooks gain profit so you will be seeing both. The thing is, you can’t tell which is which until you click. Is clicking really a good idea, though? You’re one click away from more infections. Stay away from Searchpause.com’s bogus and unsafe search results. There are plenty of harmless search engines online; why stick to this one? The hijacker also redirects you and slows down your computer speed. Your overwhelmed browsers may start crashing and/or freezing too. To top it all, this nuisance jeopardizes your privacy by collecting personal data. There’s absolutely no reason to hesitate. Searchpause.com has to go.
How did I get infected with?
The most popular malware distribution method involves bundled software. Crooks rely on the fact most people skip installation steps. All that hackers have to do is attach the potential intruder to a bunch of programs. You do the rest by rushing the process. Next time you download freeware/shareware bundles, be careful. Avoid illegitimate websites and unverified software. More often than not, those are corrupted. Also, opt for the Advanced or Custom option in the Setup Wizard. This way you’ll be able to spot and deselect any potential intruder. Viruses also travel the Web via spam messages/email-attachments. Yes, crooks send malware straight to your inbox sometimes. Delete what you don’t trust and always keep an eye out for infections. To prevent infiltration is much easier than to delete malware afterwards. Make sure you protect your device from trouble.
Why is this dangerous?
Searchpause.com’s extension is compatible with some of the most commonly used browsers. You can’t surf the Internet without seeing random (and unsafe) web links. In addition, the hijacker may start generating corrupted pop-ups. These commercials are incredibly annoying, intrusive and hard to deal with. As mentioned, Searchpause.com redirects you to some specific websites. It also spies on your browsing-related activities. Consider your private life online no longer private. Hackers have free access to your IP addresses, search queries, usernames/passwords, browsing history. They will not think twice before selling your information. Thus, your sensitive data gets sent to third parties with highly questionable intentions. This might result in financial scams or even identity theft. To prevent these two frightening scenarios, get rid of the hijacker ASAP. There’s nothing to lose by deleting Searchpause.com. On the other hand, there’s quite a lot to gain. This program causes a poor PC performance and tests the limits of your patience. To delete it manually, please follow our detailed removal guide down below.
How to Remove Searchpause.com virus
If you perform exactly the steps below you should be able to remove the Searchpause.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Searchpause.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Searchpause.com from Add\Remove Programs
STEP 2: Clean Searchpause.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Searchpause.com leftovers from the System
STEP 1 : Uninstall Searchpause.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
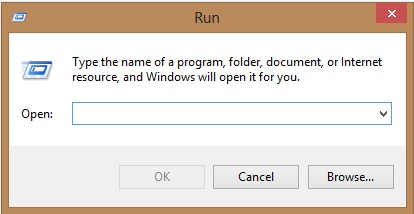
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Searchpause.com homepage from Chrome, Firefox and IE
-
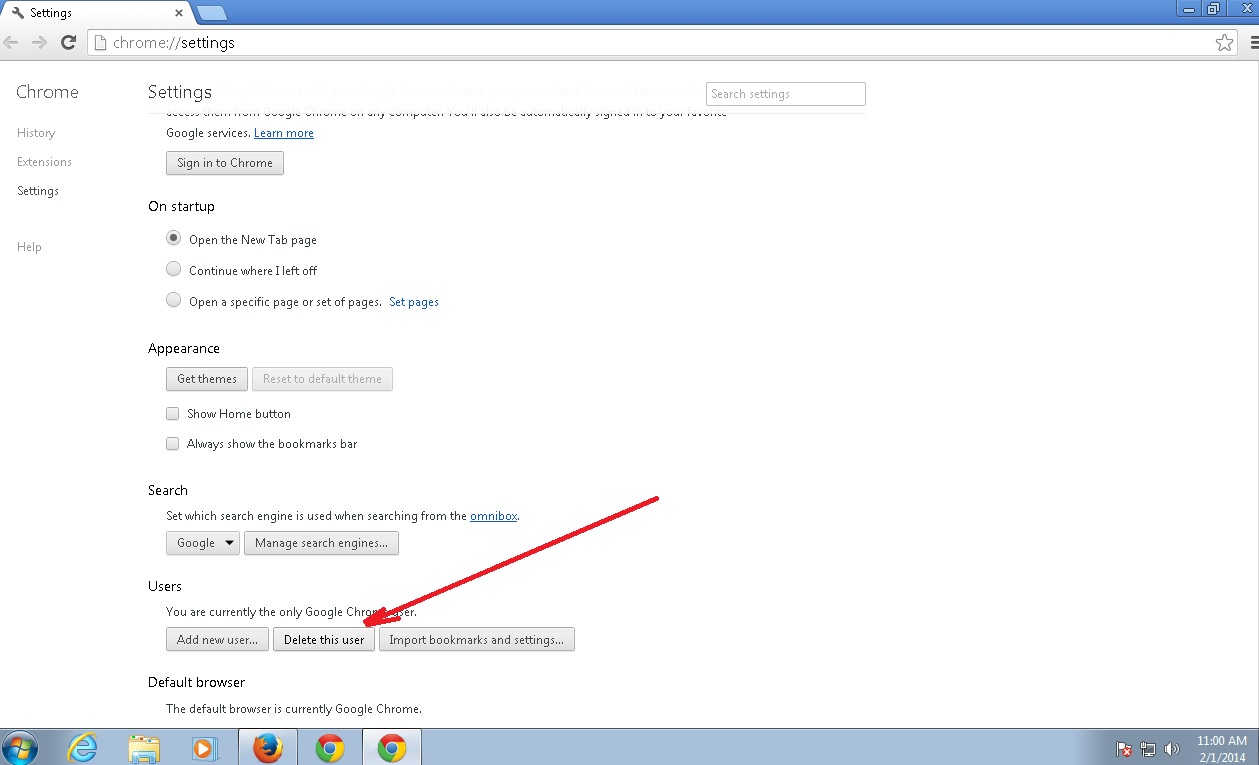
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Searchpause.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
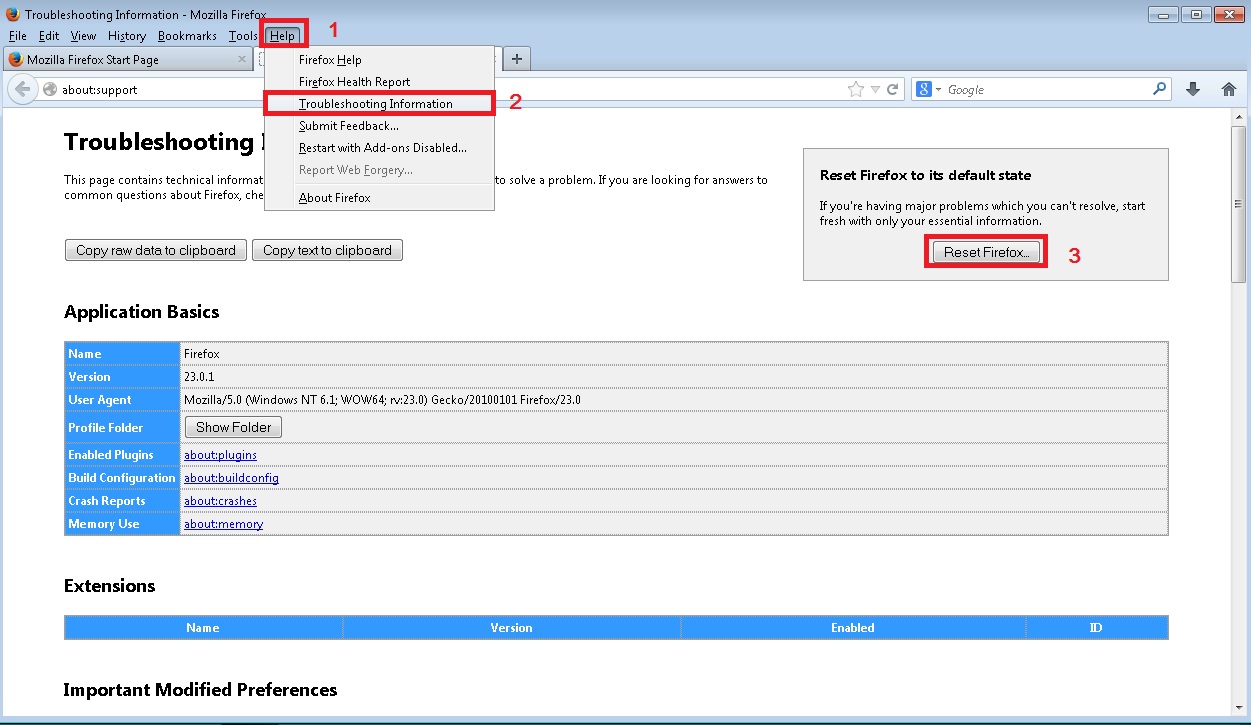
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
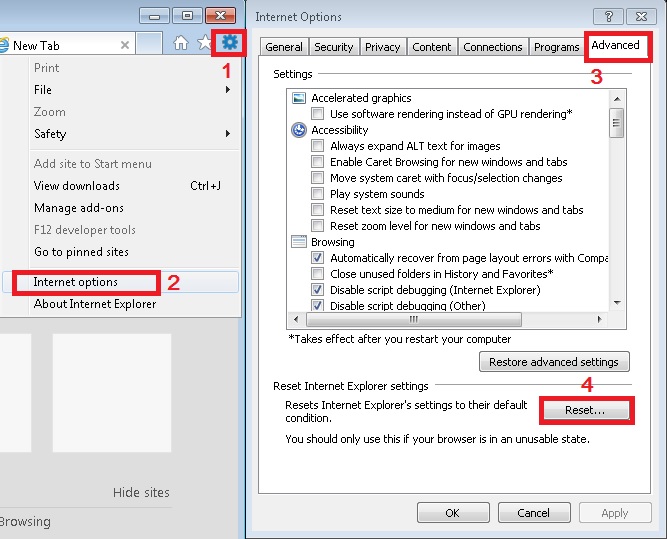
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove Searchpause.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.