Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Searchnu.com took over your homepage and you cannot remove it.
Searchnu.com is a page, which you do NOT ever want to come across it. Why? Well, it’s a malicious domain. And, it indicates the presence of a cyber threat on your computer. That’s right. If it pops up, then your PC is no longer infection-free. A browser hijacker managed to slither its way inside. The Searchnu.com site acts as a front, a face if you will, to the hijacker. The web menace uses it as a shield to lurk behind and wreak havoc. Since it sneaks into your system undetected, the page is its big bright neon sign. It’s the tool’s way of announcing its presence. It’s a warning. And, you better not ignore it. Act on it! Think of Searchnu.com as a harbinger of trouble. If it takes over your screen, you’re in for a bad time. That’s because the hijacker, it’s concealing, will wreak havoc on your system. It will bombard you with issues on a daily basis. And, it won’t stop its mess-making until you get rid of it. That’s right. The more time you allow the infection on your PC, the more opportunities it has to cause issues. So, find its exact hiding place and delete it upon detection! Don’t waste any time removing it. Because you can be sure, the tool won’t waste any time causing you grievances and headaches.
How did I get infected with?
The Searchnu.com page appears after your system has been compromised. It cannot appear unless you’re the victim of an infection invasion. And, hijackers cannot enter your computer unless you give them the green light. They have to ask whether you agree to install them. And, for they to invade your PC, you have to consent. If you don’t – no admittance. So, seeing as how you’re stuck with a hijacker now, you apparently did. But how do you imagine you gave your ‘okay’ to such a threat? Odds are, you don’t even remember doing it. But you did. And, it’s because you were duped. Infections, like the one behind Searchnu.com, don’t just openly show up and ask for your compliance. They do it sneakily via trickery and finesse. Hijackers are masterful when it comes to fooling you. They turn to the old but gold means of deception and gain access to your PC while still keeping you oblivious. More often than not, they pretend to be fake updates. For example, they lead you to believe you’re updating your Java or Adobe Flash Player. But you’re far from it. Instead, you’re installing a malicious cyber threat. There are plenty of ways the tool can choose to dupe you into granting it permission to enter. But every one of them relies on your carelessness. So, don’t throw caution to the wind. Don’t rush, and don’t give into naivety. Always do your due diligence, and remember that even a little extra attention goes a long way.
Why is this dangerous?
The hijacker, using Searchnu.com as a front, was unleashed by Bandoo Media Inc. They’re a notorious entity and have earned their bad reputation. The malicious infection wastes no time once it sets foot into your system. Its mess-making begins straight away. Upon infiltration, you’ll come to find your default search engine and homepage replaced. As you can probably guess, they’ll be switched to Searchnu.com. You’ll see the site all the time – when you browse the web, open a new tab, all the time! But apart from the incessant display of the page, you’ll also be haunted by pop-up advertisements. That’s right. The redirects are accompanied by an ever-flowing waterfall of ads. So, once you catch a hijacker, your browsing is never the same. And, don’t think this continuous meddling goes unnoticed. The endless disruptions quickly lead to further trouble. For one, they cause frequent system crashes. And, also slow down your computer’s performance to a crawl. But these are just the minor inconveniences that you’ll face. Hijackers do much more than cause frustration and annoyance with their intrusions. The worst issue, you’ll deal with, is the security one. The infection behind Searchnu.com jeopardizes your private life. It places your personal and financial information on the line. That’s because it spies on you. It’s programmed to do so. It monitors your browsing activities and keeps a thorough record of your every move. When it deems it has collected enough data, it sends it to the third parties behind it. And, thus, strangers have access to your private life. The question is, are you going to allow that to happen?
How to Remove Searchnu.com virus
If you perform exactly the steps below you should be able to remove the Searchnu.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Searchnu.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Searchnu.com from Add\Remove Programs
STEP 2: Clean Searchnu.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Searchnu.com leftovers from the System
STEP 1 : Uninstall Searchnu.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
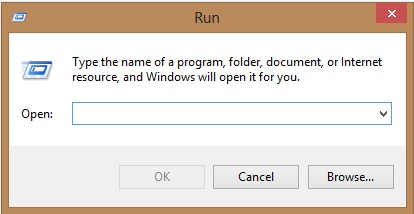
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Searchnu.com homepage from Chrome, Firefox and IE
-
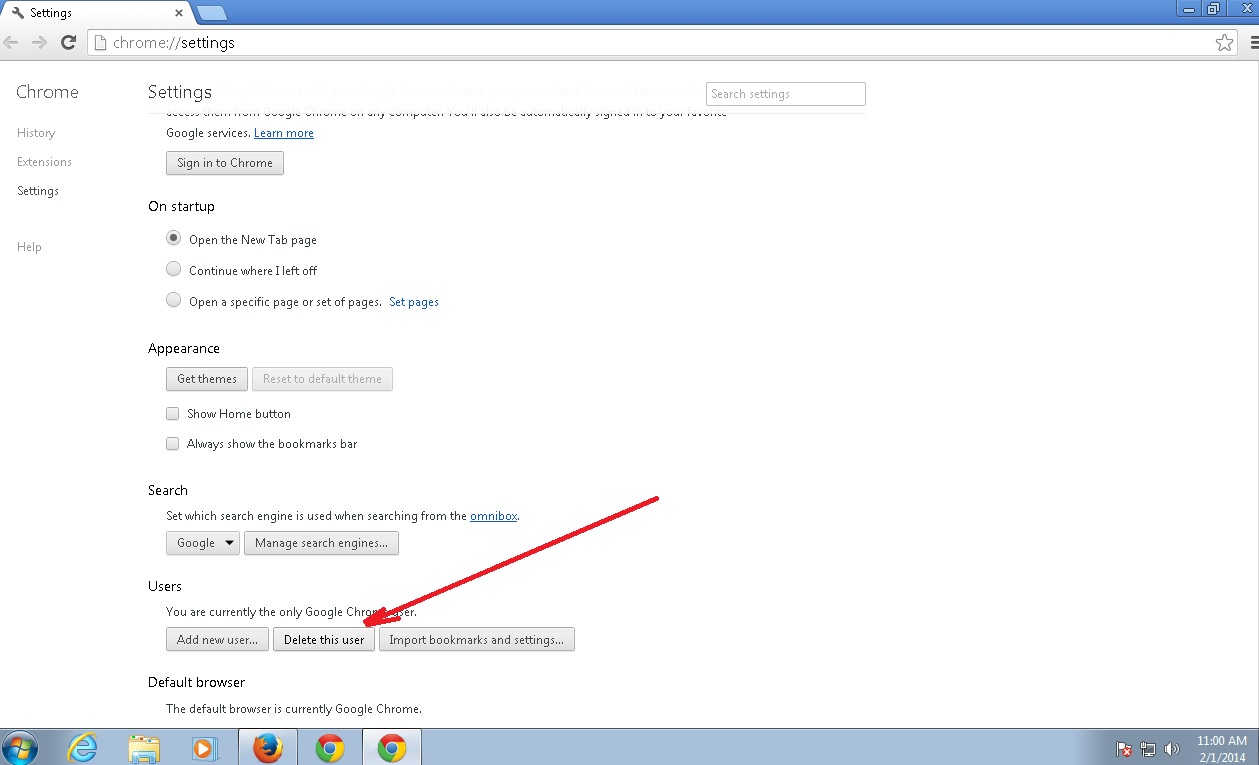
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Searchnu.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
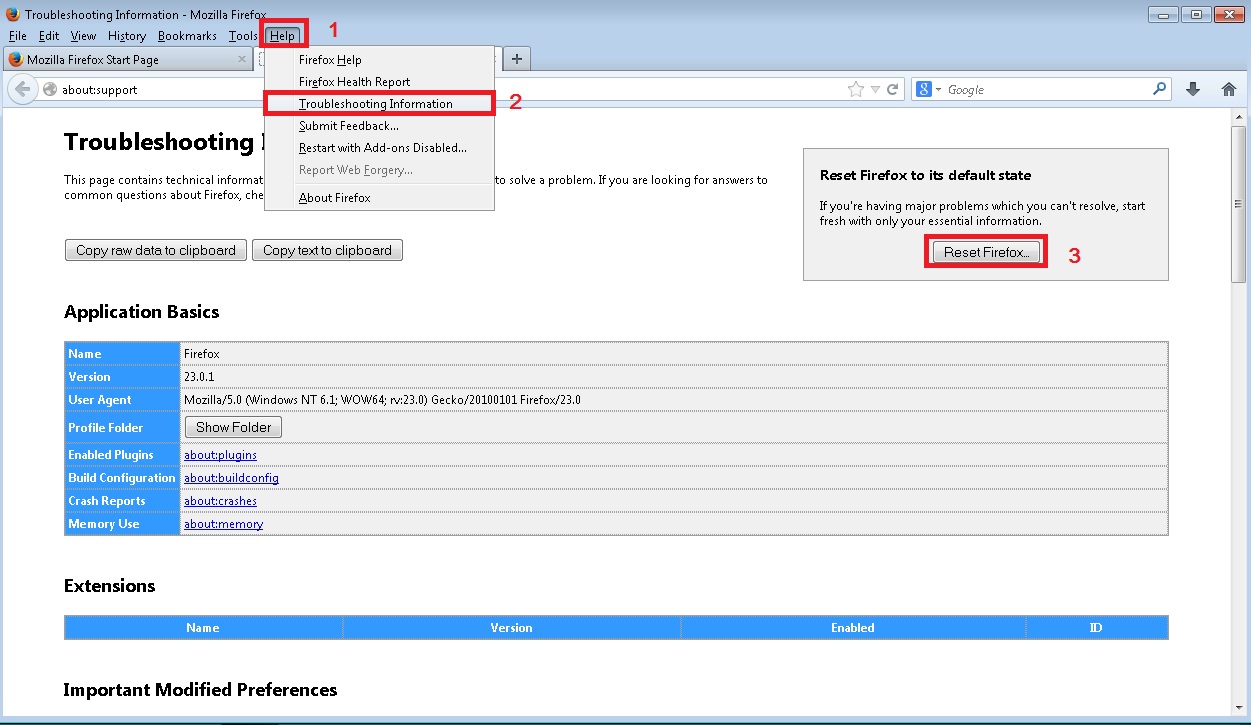
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
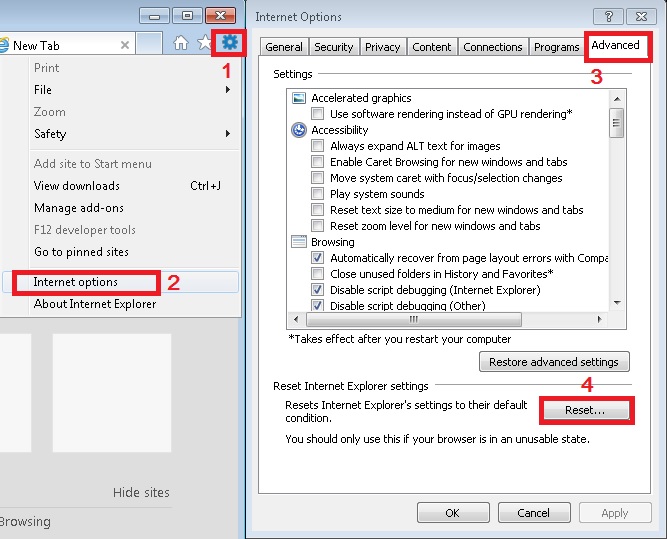
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove Searchnu.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.