Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Search.myspeedtestxp.com took over your homepage and you cannot remove it.
Search.myspeedtestxp.com is a browser hijacker. Do you suddenly find your preferred search engine and homepage switched to Search.myspeedtestxp.com? You don’t remember approving this change, and yet there it is! Every time you try to go online it’s right in front of your eyes. And, soon after the page appears, it starts messing up your browsing entirely. First of all, you need to realize that the site is just the ‘face’ of your actual threat, which is a malicious tool using it as a shield to hide behind. That tool managed to slither into your system, most likely due to your carelessness and is now beginning its reign of terror. Oh, yes. The endless redirects are just the start of your troubles. What follows this unexpected and undesired reshuffle are countless more. That’s because once the hijacker settles on your PC, it’s free to implement any and all changes it so desires, like installing more malware. That’s right. If the malware, you already have somewhere on your PC, wishes to, it can open the door for as many other such tools. And, the issues don’t stop there. You’ll also deal with a pop-up ad bombardment, frequent system crashes, a slower computer performance, and, what’s worse, a security threat. Understand this. The hijacker will wreak havoc for as long as you let it, so don’t! Stop it before it causes irrevocable damages to your system. Delete the malware behind Search.myspeedtestxp.com as soon as you see the page taking over your default search engine and homepage. You won’t regret it, and your future self will be immensely grateful for this timely reaction.
How did I get infected with?
The tool that hijacked your browser, and continuously forced Search.myspeedtestxp.com on you, is a master in the arts of deception. It fools you into agreeing to its installation without you realizing it. That may seem doubtful, improbable, or even impossible, but it’s not. Through slyness and subtlety, the tool tricks you into giving it the green light and enters as you hold the door for it – looking right at it but not seeing it. How can that be? Well, it’s pretty straightforward. Since the hijacker is bound to ask, and get, your permission for its installation, it has come up with a multitude of ways to covertly do that, and sneak in undetected. More often than not, it pretends to be a bogus system or program update, like Java or Adobe Flash Player. The hijacker can also hitch a ride with freeware or spam email attachments, as well as hide behind corrupted sites or links. Above all else, you need to realize that each mean of invasion relies on your distraction, haste, and naivety. So, perhaps, if you’re a bit extra attentive and not throw caution to the wind, you’ll manage to prevent the hijacker from slithering in and infecting your PC. Remember, attention is imperative!
Why is this dangerous?
Well, Search.myspeedtestxp.com is not called a ‘hijacker’ just for not. Once it slithers into your PC, it hijacks your browser and replaces your …Then the ads start popping up.Oh, yes. Apart from the never-ending redirects to the…page, you’ll also be forced to put up an ever-flowing waterfall of pop-up advertisements.Think about that. Not only will you have to bear unwanted and unrequested redirects, but to that, you’ll have to add enduring a never-ending bombardment of obnoxious ads. How long do you think you’ll be able to take that infuriating disturbance before it strikes the last nerve and stretches the limits of your patience to the fullest? It will hardly take long. But even if you disregard all other issues, the biggest, most severe one, remains – the security threat. Once a hijacker settles on your PC, it begins to take note of your browsing activities. It keeps track of every move you make online, and when it deems it has gathered enough data, sends it to the people behind it. Are you okay with that? Are you going to allow a malevolent tool to steal your personal and financial information, and give it to strangers with questionable intentions? Are you willing to risk your private life for a tool that’s so far from worth it? Think long and hard before you answer that question. It’s your decision to make but here’s some advice: don’t hold onto the hijacker! The negatives from keeping it on your PC far outnumber the positives.Do yourself a favor and get rid of the hazardous tool as soon as it first imposes Search.myspeedtestxp.com on you.
How to Remove Search.myspeedtestxp.com virus
If you perform exactly the steps below you should be able to remove the Search.myspeedtestxp.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Search.myspeedtestxp.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Search.myspeedtestxp.com from Add\Remove Programs
STEP 2: Clean Search.myspeedtestxp.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Search.myspeedtestxp.com leftovers from the System
STEP 1 : Uninstall Search.myspeedtestxp.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
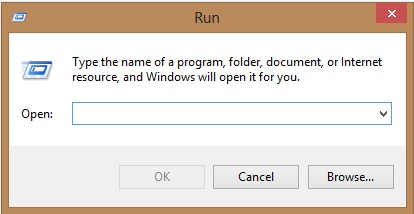
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Search.myspeedtestxp.com homepage from Chrome, Firefox and IE
-
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Search.myspeedtestxp.com by clicking on the little recycle bin
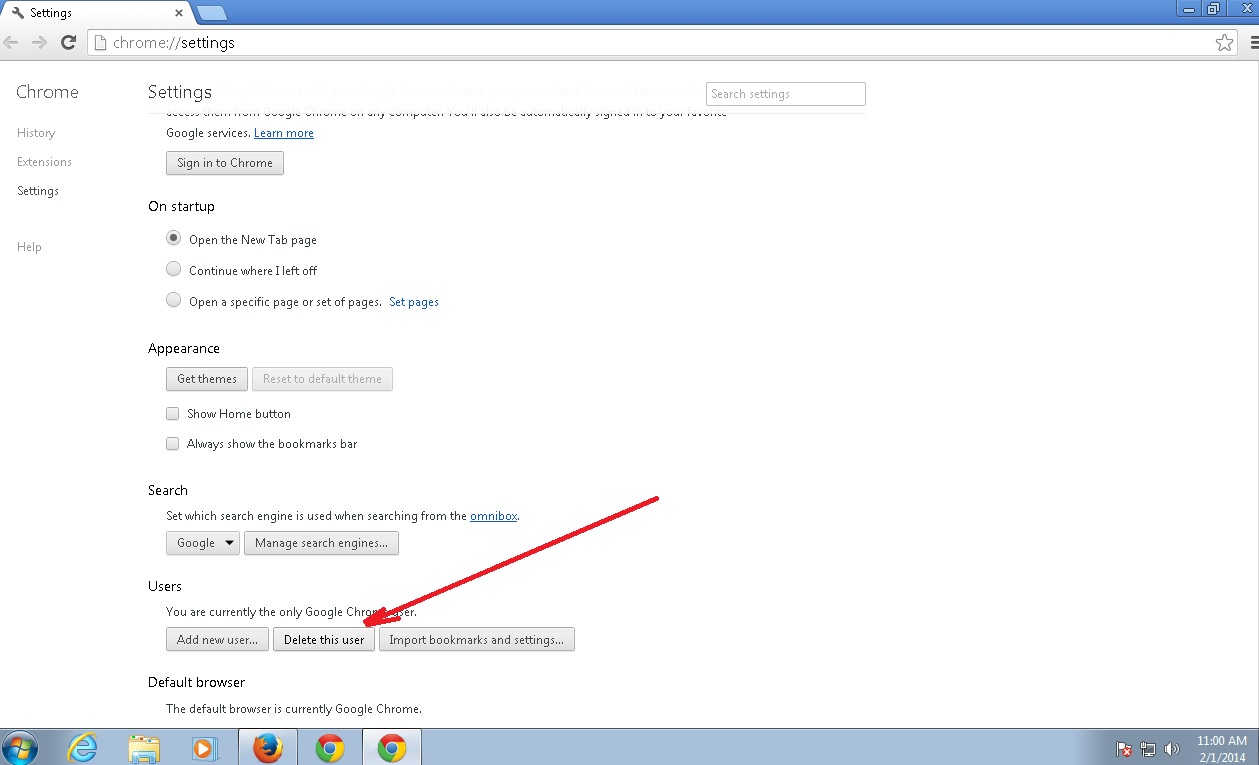
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
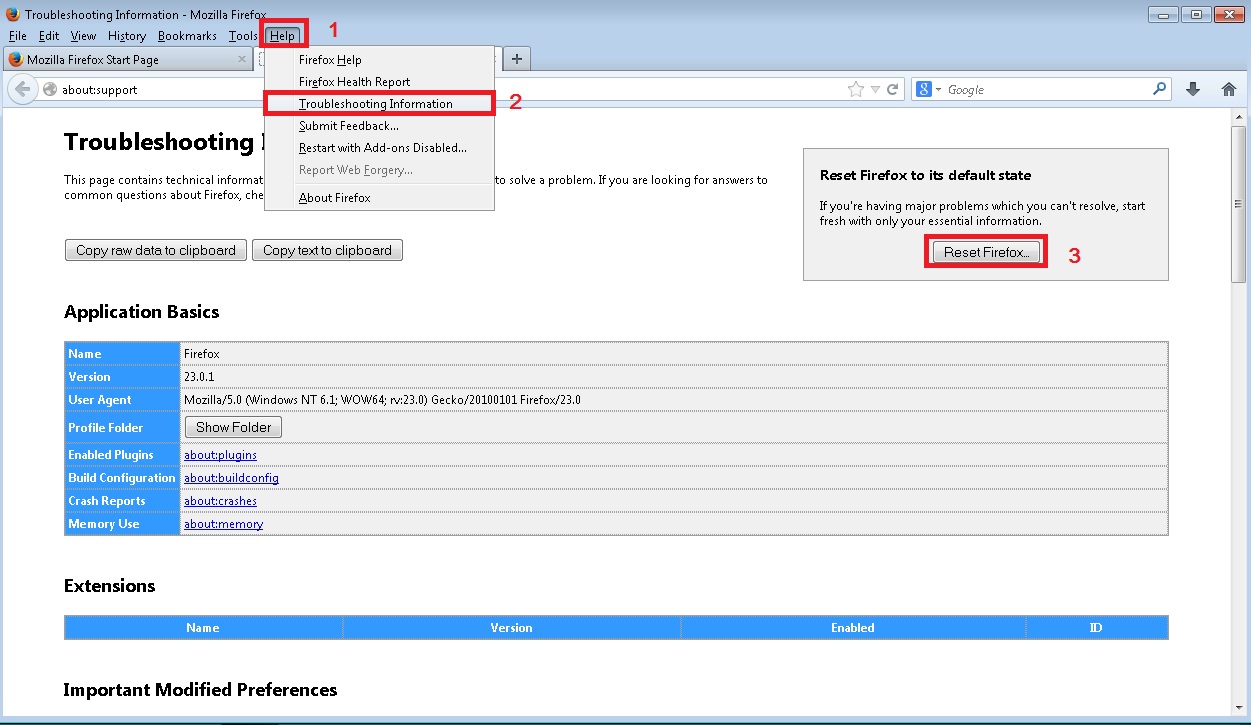
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
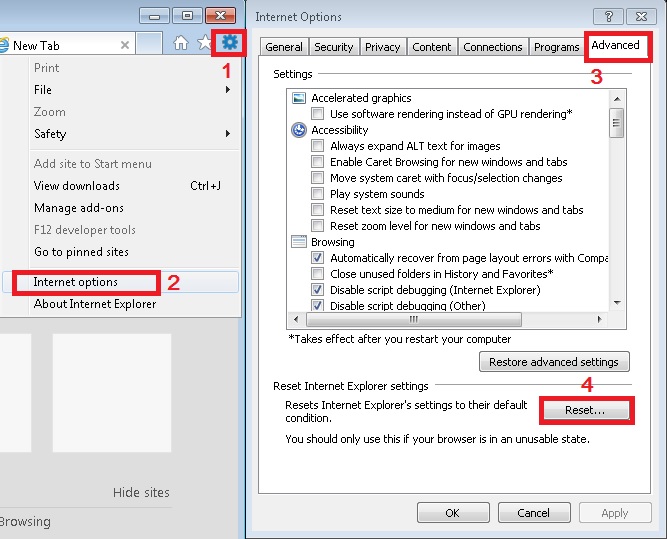
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove Search.myspeedtestxp.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.