Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Rush Ransomware?
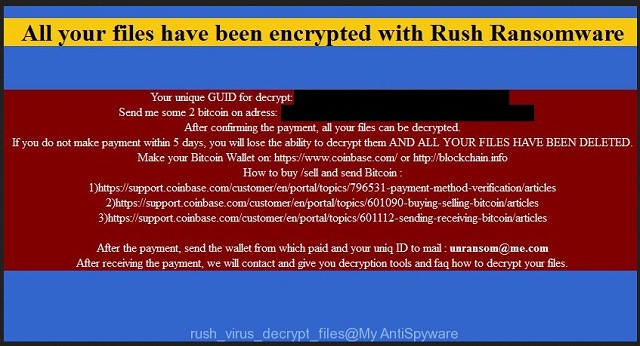
Reader recently start to report the following message being displayed when they boot their computer:
All your files have been encrypted with Rush Ransomware
Your unique GUID for decrypt xxx
Send me some 2 bitcoin on address: xxx
After confirming the payment, all your files can be decrypted.
If you do not make payment within 5 days, you will lose the ability to decrypt them AND ALL YOUR FILES HAVE BEEN DELETED.
Make your Bitcoin Wallet on: xxx
How to buy /sell and send Bitcoin : xxx
After the payment, send the wallet from which paid and your uniq ID to mai unausom@rne.com
After receiving the payment, we will contact and give you decryption tools and fag how to decrypt your files.
Ransomware is a hot topic in the world of parasites. It’s safe to say this type of malware is a hackers’ favorite at the moment. We prepare removal guides on various ransomware-type infections practically every day. There’s a reason why ransomware is on the rise at the moment. These programs are both very aggressive and absolutely devastating. Yes, you’ve come across one of the most virulent infections imaginable. Furthermore, you’ve accidentally installed in on your computer system. That means your situation is, to put it mildly, quite problematic. You’re now dealing with Rush Ransomware (also known as Sanction). This pest locks all your personal files, then demands a ransom in Bitcoin. By using a AES-256 asymmetric key, Rush Ransomware turns all your data into useless gibberish. And by “all your data” we mean literally all your data. Pictures, music, Microsoft Office documents, videos. Anything of value you might have stored on your PC gets encrypted. Do you now see why ransomware is so dreaded? This thing utilizes an asymmetric encrypting algorithm. It creates one public key (which locks files) and one private key (which unlocks files). In order to free your infected data, you need to put your hands on the private key. The problem is, hackers aren’t willing to give it for free. Crooks offer you a deal. You either wave your data goodbye or you pay 2 Bitcoin. For those of you who aren’t familiar with online currency, 2 Bitcoin equals over 1300 USD. What kind of pictures and music is worth 1300 USD, though? What’s even worse is that hackers have absolutely NO reason to free your files. You may give them all the money they ask for and still receive nothing in return. Remember, ransomware is just a clever way for hackers to steal your money. Don’t even consider paying the ransom because you shouldn’t sponsor crooks’ business. The Rush Ransomware adds a malicious file extension (.remind) to your files. Once you see this appendix, consider your personal data locked. As mentioned, the encrypting cipher used by this pest is very complicated. The problem is, you cannot trust hackers’ promises to unlock your data. You’d be making a deal with greedy and dishonest cyber criminals. Does that sound like a good idea? It isn’t.
How did I get infected with?
The most likely explanation of this program’s presence is a spam message. You should know that hackers still use some of the oldest tricks in the books. Hence, don’t overlook the giant threat they pose. Stay away from anything suspicious-looking in your inbox. Remember, spam messages from unknown senders and spam email-attachments are unreliable. Next time you stumble across something like this, delete it without opening. Also, keep an eye out for malicious torrents and random executables. More often than not, those are harmful. Ransomware travels the Web via unverified freeware/shareware bundles as well. Another possibility is that the virus got to you with the help of a sneaky Trojan horse. There are many infiltration techniques online and hackers are full of ideas how to spread malware. Make sure you always outwit crooks. Preventing virus installation is a much easier task than removing a virus later on.
Why is Rush dangerous?
The parasite firstly performs a thorough scan on your computer. This way it locates all your personal files. As we mentioned, next step is encryption. While locking your information, the virus drops .txt, .html and .bmp files. All three contain detailed payment instructions because that’s what ransomware aims for. You will find these files in all folders that contain encrypted data. As you could imagine, those are a lot of folders. Rush Ransomware takes down a huge variety of file formats. Obviously, some immensely important and valuable data may fall victim to the parasite as well. Ransomware is perfectly capable of causing irreversible damage. That’s why the last thing you do should be to encourage hackers. Do not give them your money. Crooks promise a decryption key (a unique combination of symbols). In reality, though, crooks are only interested in their illegitimate profit. If you let them blackmail you, they will. By adding .remind file extension, hackers try to play mind games with you. Giving into your anxiety and despair would cost you money, though. Therefore, don’t be gullible to think crooks are willing to help. Crooks are the ones who locked your data to begin with. Instead of paying the ransom, get rid of the ransomware. To delete it manually, please follow our comprehensive removal guide down below.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Rush Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Rush Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Rush encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Rush encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.