Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Payms Ransomware?
Reader recently start to report the following message being displayed when they boot their computer:
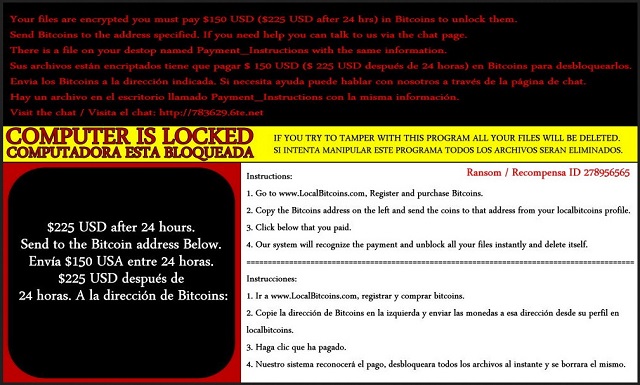
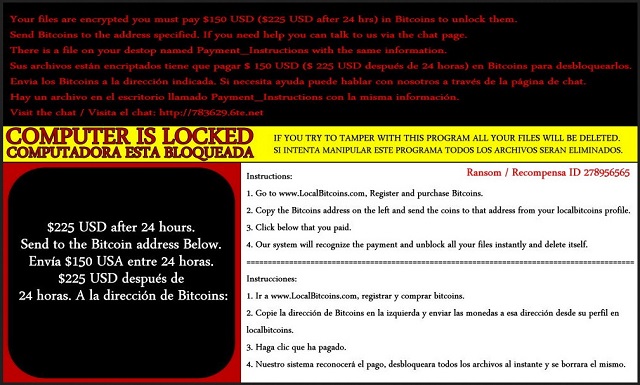
Your files are encrypted you must pay $150 USD ($225 USD after 24 hrs) in Bitcoins to unlock them. Send Bitcoins to the address specified. If you need help, you can talk to us via the chat page. There is a file on your desktop named Payment_Instructions with the same information.
Sus archivos estan encriptados tiene que pagar $ 150 USD ($ 225 USD despues de 24 horas) en Bitcoins para desbloquearlos. Envia los Bitcoins a la direccion indicada. Si necesita ayuda puede hablar con nosotros a traves de la pagina de chat. Hay un archivo en el escritorio llamado Payment_Instructions con la misma informacion.
Visit the chat / Visita el chat: http://783629.6te(.)net
COMPUTER IS LOCKED. IF YOU TRY TO TAMPER WITH THIS PROGRAM ALL YOUR FILES WILL BE DELETED.
COMPUTADORA ESTA BLOQUEADA. SI INTENTA MANIULAR ESTE PROGRAMA TODOS LOS ARCHIVOS SERAN ELIMINADOS.
Instructions:
1. Go to www.LocalBitcoins(.)com, Register and purchase Bitcoins.
2. Copy the Bitcoins address on the left and send the coins to that address from your localbitcoins profile.
3. Click below that you paid.
4. Our system will recognize the payment and unblock all your files instantly and delete itself.
=======================================================================
Instrucciones:
1. Ir a www.LocalBitcoins(.)com, registrar y comprar bitcoins.
2. Copie la direccion de Bitcoins en la izquierda y enviar las monedas a esa direccion desde su perfil en localbitcoins.
3. Haga clic que ha pagado.
4. Nuestro sistema reconocera el pago, desbloqueara todos los archivos al instante y se borrara el mismo.
Payms belongs to the extensive, and dreaded, ransomware family.Yes, it’s a ransomware tool, which is arguably the worst type of cyber infection you can catch. And, that’s a title well-deserved, according to most. As the very name lets on, it’s a tool, which demands you pay a ransom. But not before slithering into your system undetected via slyness and subtlety, and encrypting every single file you keep on your computer. That’s right. The infection invades your PC and then locks all of the data that you have stored on it. Once its encryption process is complete, it proceeds to fill you into your predicament, and what you must do to get out of it, which is, to put it plainly – pay up. Yes, Payms demands payment. So, if you are to free your files from its captivity, you must comply. Otherwise, you’ll never see your data again. And, you better be sure the tool means it. If you do not transfer the original amount it requests, it deletes some of your files and increases the sum. In a nutshell, the tool backs you up into a corner and extorts you for money. But, here’s the deal, even if you ignore all the red flags and pay, there’s a chance you sill won’t regain control of your data. Do you know why that is? Because these are unreliable people, who, unsurprisingly, cannot be trusted to keep their end of the bargain. Even if you comply with each of their requirements, they can still double-cross you. In fact, it would be shocking if they don’t! Remember that these are individuals, who invaded your system, encrypted your files, demanded payment for their release, and gave you a time limit to go through with it. Do you honestly believe them to be people, who’ll keep their promises?
How did I get infected with?
Payms doesn’t just appear on your computer as if by magic. There’s nothing magical about it. The tool gained entry via deception and trickery. More specifically, by preying on your carelessness. Yes, ultimately, you’re to blame for its infection. If you were more cautious and vigilant, perhaps you wouldn’t be in your current predicament. However, don’t judge yourself too harshly. Ransomware tools are quite masterful when it comes to finding a way to your system. They employ every known trick in the book to slither past you undetected and make your PC their new home. More often than not, they turn to the usual antics, which involves exploiting your gullibility, haste, and distraction. That’s nothing new or innovative as the technique is employed by most (if not all) cyber threats. The infection hides behind freeware, spam email attachments, corrupted links, or websites. It can also pretend to be a fake system or program update, like Adobe Flash Player or Java. And, even though, the harmful program enters in front of your very eyes, you still don’t see it. Not until you turn on your PC to the dreadful warning that all of your data is encrypted. If you wish to avoid ever seeing that message, make sure to be more thorough! Vigilance and caution are your friends, while gullibility and haste are not. Remember that infections prey on carelessness, and don’t provide it. Sometimes even a little extra attention can go a long way, and save you a ton of issues.
Why is Payms dangerous?
Once Payms sneaks into your system, it goes to work. Every picture, document, video, music file, everything that you have stored on your computer falls under its control. It locks your files and makes it impossible for you to open them. The tool usually solidifies the encryption by adding an extension, which renders them utterly inaccessible. It can be anything between paymrss, paym, payrms, payms, paymst, or pays. And, once it slaps it on, that’s it. No matter how many time you rename your file, it won’t change anything. It won’t work. The ransomware program makes it known that the only way to release your data from its keep is to comply with its demands. And, they are clearly listed in the “Payment_Instructions.txt” file. There you will find what it asks of you, and how you can accomplish it. You’ll see the file on your desktop, and it contains a message in both English and Spanish, announcing that you must transfer $150 in BitCoins if you are to see your data again. If you delay or refuse to pay, within 24 hours, the payment is increased up to $225. Follow experts advice, and don’t comply! If you do, you’ll only find yourself in a worse situation. Do you know why? Well, it’s pretty straightforward. If you decide to transfer the money, you’ll have to input your private details so the payment can be completed. You do NOT want to do that! That will give access to your private life to unreliable, malicious unknown individuals, who, it’s safe to say, will use that information for their gain with no regards to your best interests. Are you going to stand by as strangers with agendas benefit from your personal and financial information? Don’t! And, the worst part is, despite all the risk, odds are, it still won’t work! Even if you pay these people, there are no guarantees they’ll send you a working decryption key, or a key at all! Furthermore, even if the exchange goes smoothly and you free your files, there’s nothing to stop the tool from kicking in the very next day and encrypt everything again, thus, sending you back to square one. So, as hard as it may seem, discard your data! Don’t pay. Don’t comply. Pick privacy over data. Say goodbye to your files as they are replaceable. Can you say the same for your personal and financial information?
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Payms Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Payms Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously.
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Payms encryption Virus.
- Right click on the process.
- Open File Location.
- End Process.
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect.
STEP 2: Reveal Hidden Files
- Open any folder.
- Click on “Organize” button.
- Choose “Folder and Search Options”.
- Select the “View” tab.
- Select “Show hidden files and folders” option.
- Uncheck “Hide protected operating system files”.
- Click “Apply” and “OK” button.
STEP 3: Locate Payms encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”.
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM].

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.