Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Masterlock@india.com Ransomware?
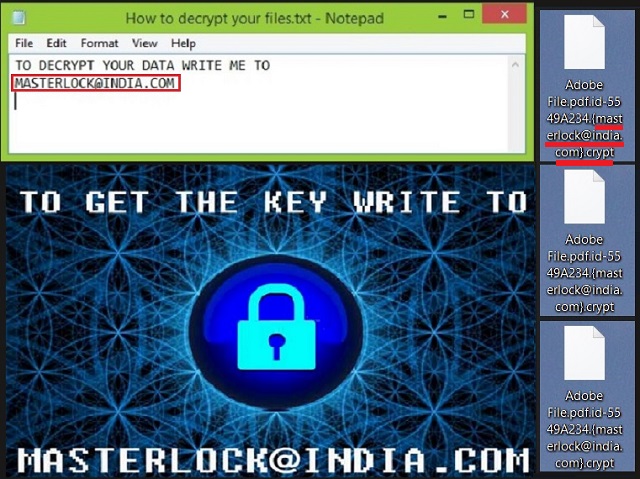
Reader recently start to report the following message being displayed when they boot their computer:
TO DECRYPT YOUR DATA WRITE ME TO
MASTERLOCK@iINDIA.COM
or
TO GET THE KEY WRITE TO
MASTERLOCK@iINDIA.COM
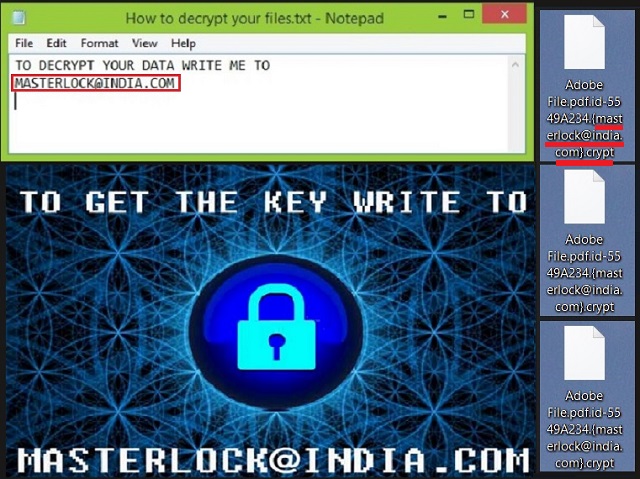
If you had to pick the worst type of cyber threat, roaming the web, which one would it be? Adware? Hijacker? Trojan? Or, would you go with ransomware? If you’ve ever found yourself the victim of the latter, you’ll know that it wins the title, hands down. Most users crown it the worst because if you’re stuck with it, you’re doomed. Yes, that’s a bit of an exaggeration. But it’s true. There is no way you can win a face off with a ransomware. Each way you spin it, you lose. The game is rigged against you from the start. Let’s get into the whole process. How the tool operates, how it invades your PC, its end-game, everything. And, let’s look at once particular ransomware, the MasterLock one. If it slithers into your PC, it encrypts all your files, and attaches an extension at the end. Say, you have a video named “summer.” After the infection’s done with it, it’ll be “.masterlock@india.com.crypt.” Once the extension gets added, your files are inaccessible. And, they’re no longer under your control. The infection takes them hostage, and uses them to extort you for money. It promises to release them once you pay, but do you believe them? Are these people even remotely trustworthy? We’re talking about strangers, who infected your system with a cyber plague. Took over your data. Locked it. And, demanded payment for its release. Do you think these are people, who keep their word? Don’t be naive. They will NOT keep their end of the bargain. They’ll trick you. They don’t care about your files. They only care about your money, and if they get it or not. Do NOT pay these cyber criminals! It only worsens your situation if you do.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How did I get infected with?
Ransomware tools often slither into your PC via spam email attachments. But they can do so with the help of any of the old but gold means of invasion. In other words, they can hide behind freeware. Or, corrupted sites or links. Or, pretend to be bogus updates. Like, Adobe Flash Player or Java. So, for example, while you may be convinced you’re installing updates, you’d be wrong. In reality, you’re giving the green light to a dangerous application. That is if you’re not careful enough to spot the deception. Understand that vigilance and attention are imperative when dealing with updates or tools. Don’t just rush through their installment. Take your time, be thorough, do your due diligence. Read the terms and conditions. Don’t just say ‘Yes’ to everything, and leave your fate to chance. Instead of relying on luck, rely on caution! Be more careful. Don’t allow malware to slip through the cracks, your distraction makes. Even a little extra attention goes a long way, and can save you a ton of troubles.
Why is Masterlock@india.com dangerous?
After the infection settles in your system, it goes to work. It targets every single file you have stored on your computer. It adds an extension at the end of each one, and locks it. Once your data gets locked, the extortion begins. The infection leaves a TXT file in every one of your folders. And, also replaces your Desktop picture with one it created. They’re concise and to the point. The message it leaves it along the lines of: “Your data is encrypted, contact me to decrypt it.” And, it leaves the Masterlock@india.com email address. Once you email these people, they reply back with a lengthy message. It explains your predicament. How you got infected with a cyber threat that encrypted your data. How if you wish to free it, from its clutches, you have to pay a ransom. And, how once you do, you’ll receive the necessary decryption key. Supposedly, after that, all will be well. Well, guess what? It doesn’t work that way. The most peculiar aspect of the reply is that these people make it out as if they’re not the bad guy in your story. As if something else is causing you distress, and they’re the hero, coming to help. It’s rather ridiculous. The requested ransom amounts to 3 Bitcoins. And, considering one is equivalent to about $600, that’s no small sum! But, here’s the thing. Even if it were just $1, we still advise you NOT to pay. Do you know why? If you comply and pay the ransom, you open a door to your privacy. Once opened, it cannot close. These people, the kidnappers, will have access to your personal and financial details. Do you think that will end well? Hardly. Do yourself a favor, and forsake your files in the name of your privacy. Data is replaceable. Can you say the same about the latter?
Masterlock@india.com Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Masterlock@india.com Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Masterlock@india.com encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Masterlock@india.com encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.