Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Loadstart.net took over your homepage and you cannot remove it.
One of the newest cyber infections out there is called loadstart.net. This pest sneaks onto your machine and starts wreaking havoc immediately. Have you ever had to deal with browser hijackers so far? You have to now. Loadstart.net is a typical member of the nasty hijacker family. That means you’re stuck with a stubborn, obnoxious, unpredictable and dangerous parasite. It goes without saying that you have to take action ASAP. The more time loadstart.net spends on board, the more damage it could cause. Hence, do not hesitate and don’t overlook the immense threat loadstart.net poses. It’s up to you to do the right thing so get rid of the parasite. For starters, this program messes with your default browser settings. It sneakily modifies both your preferred browser homepage and favorite search engine. Why? So it could replace them with its own domain. However, loadstart.net is light years away from being harmless. This search engine will not enhance your browsing experience. Regardless of what hackers promise, keep in mind that we’re talking about a hijacker. A virus. A harmful program developed by greedy cyber criminals. There’s simply no plausible scenario in which keeping the parasite would be a good idea. Once this nuisance hijacks your browsers, it starts forcing web links on you. Stay away from anything generated by the virus, though. Loadstart.net serves hackers’ malicious purposes so it can’t be beneficial for you. On the other hand, this infection will cause quite a headache. All web links displayed by the virus are supposed to be safe, accurate search engines. They aren’t. This program generates sponsored and unreliable web links instead. Not only does the hijacker lie to your face but it also jeopardizes your safety at the same time. If you click the wrong link, you might compromise your PC further. The thing with hijackers is, they don’t discriminate between safe and corrupted links. Furthermore, there’s no telling which is which until you click. This is how you might end up on some highly questionable websites full of malware. Yes, loadstart.net brings infections straight to your PC screen. To prevent more harm, avoid all links this infection bombards you with. In addition, the virus spies on your browser-related activities. It collects all the personal information that it could get and sends it to hackers. As you could imagine, such a trick will not end well for your privacy. To top it all, loadstart.net slows down the PC and turns browsing the Internet into a cyber nightmare.
How did I get infected with?
Hijackers travel the Web the same way most parasites do. That means loadstart.net landed on board without your active cooperation. Malware relies on your distraction and haste online instead. The most popular infiltration technique involves program bundles. You see, installing a whole bunch of programs at once is super convenient for PC users. It is also super convenient for cyber criminals. All that hackers have to do is attach some malicious “bonus” to the bundle. You do the rest by skipping installation steps and not paying attention. Keep in mind that freeware/shareware bundles could turn out to be very dangerous. Opt for the Advanced option in the Setup Wizard; this will allow you to be in control. Next time you download such bundles, take your time to check out all programs thoroughly. You won’t regret it. Infections also get spread online via spam messages/emails, third-party pop-ups, illegitimate pages, etc. There are various distribution methods out there so watch out for malware.
Why is this dangerous?
Loadstart.net starts harassing you as soon as it lands on your PC system. The hijacker modifies your browser settings. It adds a dangerous extension to them thus taking control over your activities. The plugin itself is compatible with some of the most commonly used browsers on the Web. Google Chrome, Mozilla Firefox and Internet Explorer all victims to the hijacker. They now generate suspicious, unsafe web links. Also, you might come across random toolbars or product commercials. Restrain yourself from clicking anything displayed by this pest of a program. The virus constantly redirects you. As mentioned, loadstart.net jeopardizes your privacy as well. It spies on your browsing history, IP addresses, passwords/usernames, etc. However, if you’re especially unlucky, the virus will collect bank account data too. The loadstart.net hijacker may cause financial scams or even identity theft. Take measures before it’s too late. To delete loadstart.net manually, please follow our detailed removal guide down below.
How to Remove Loadstart.net virus
If you perform exactly the steps below you should be able to remove the Loadstart.net infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Loadstart.net adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Loadstart.net from Add\Remove Programs
STEP 2: Clean Loadstart.net from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Loadstart.net leftovers from the System
STEP 1 : Uninstall Loadstart.net from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
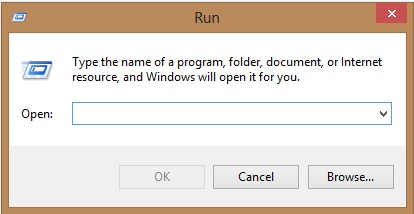
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Loadstart.net homepage from Chrome, Firefox and IE
-
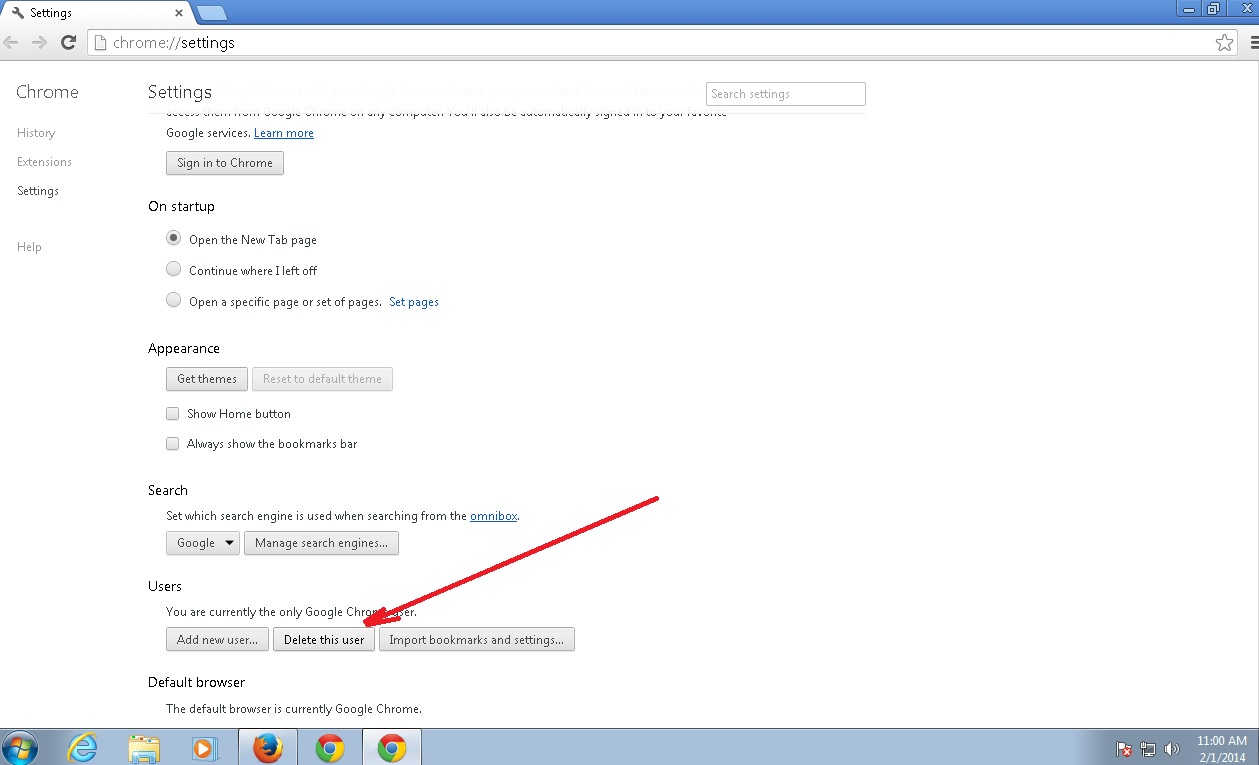
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Loadstart.net by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
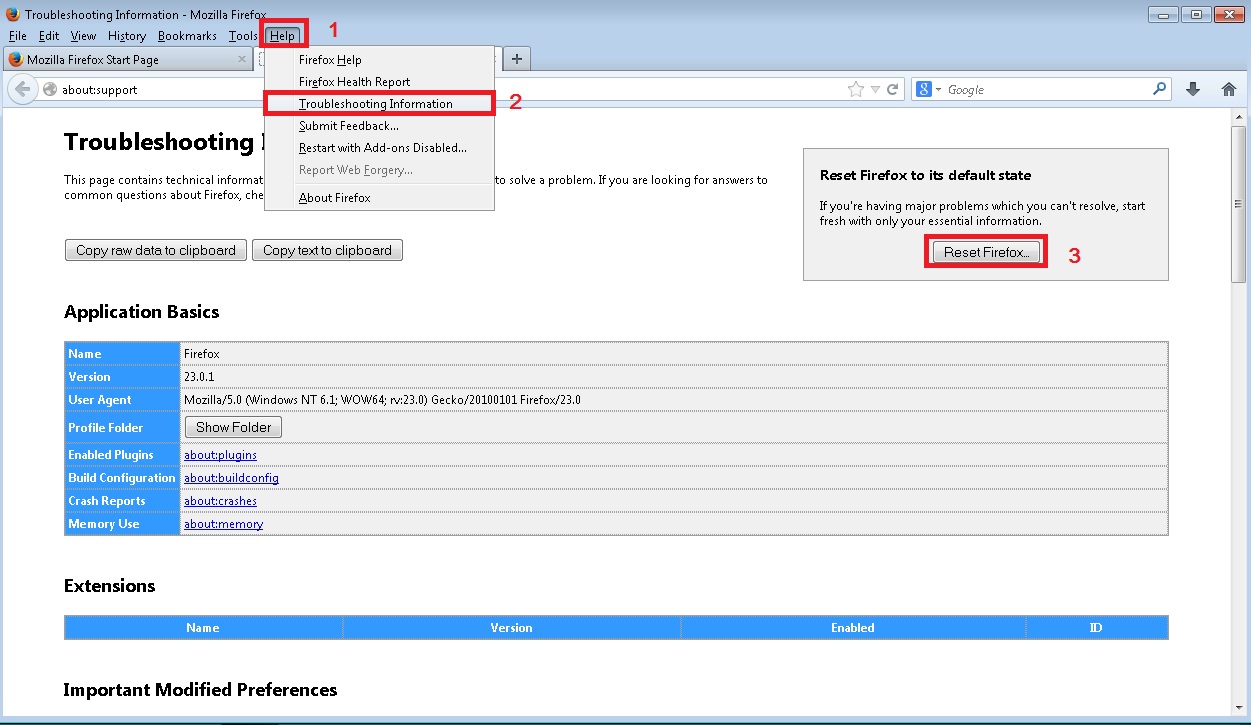
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
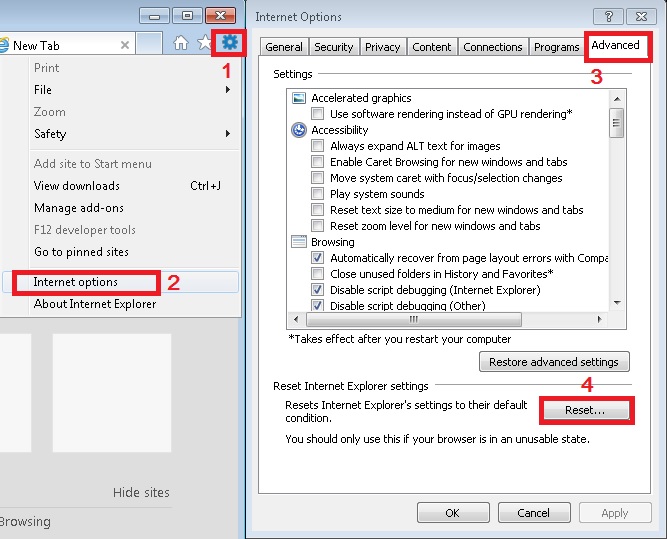
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
Make sure your Windows HOSTS file is clean
- open your explorer and Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:

You need to remove the poisoned IPs and save the HOSTS file.
Check your internet connection settings
- Right-click on the active Network Adapter, Click on Properties
- Navigate to Internet Protocol Version 4 (ICP/IP), click Properties.
- Click on Advanced and then navigate to the DNS TAB. The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
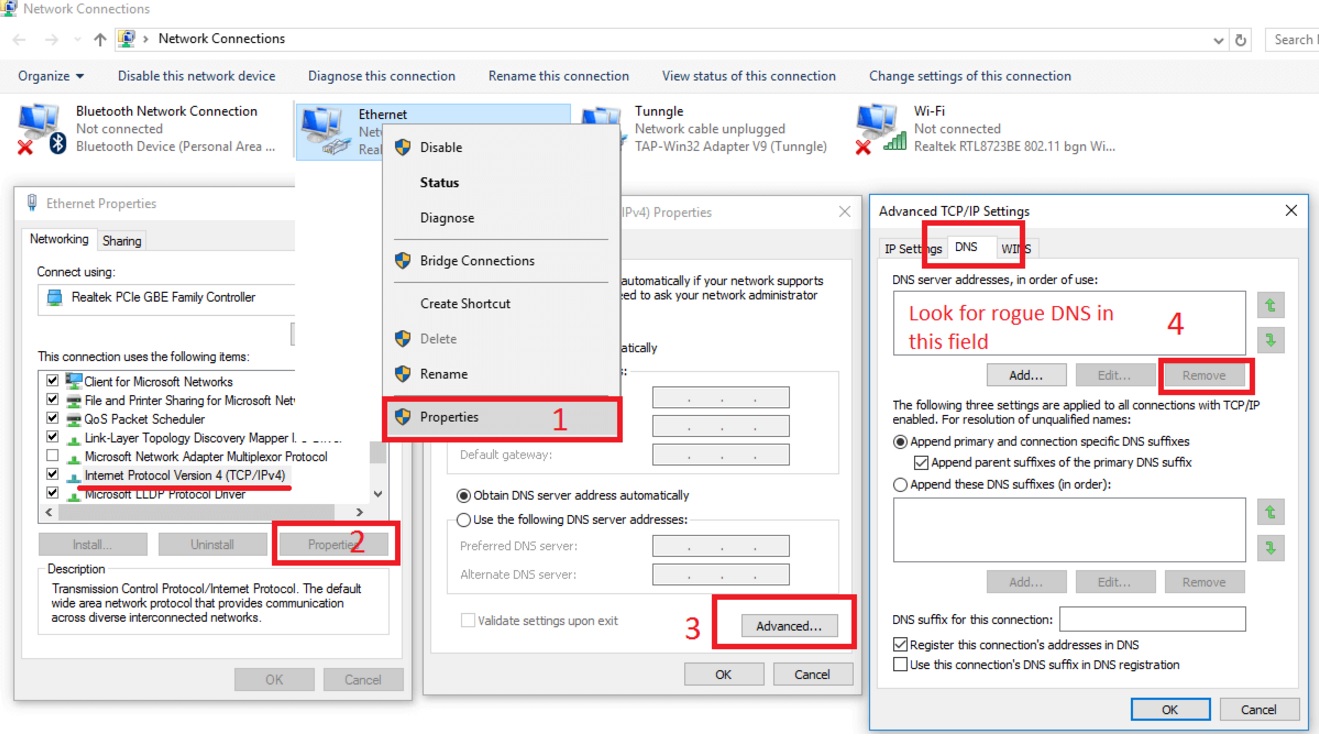
Double check your proxy settings as the malware is capable of modifying them.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for example, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
How to Permanently Remove Loadstart.net Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.