Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Johnycryptor@hackermail.com Ransomware?
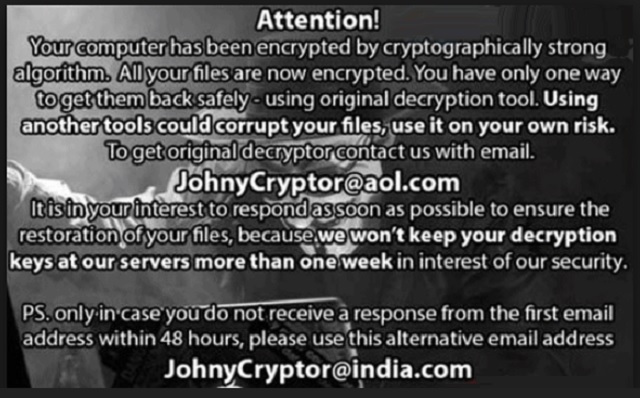
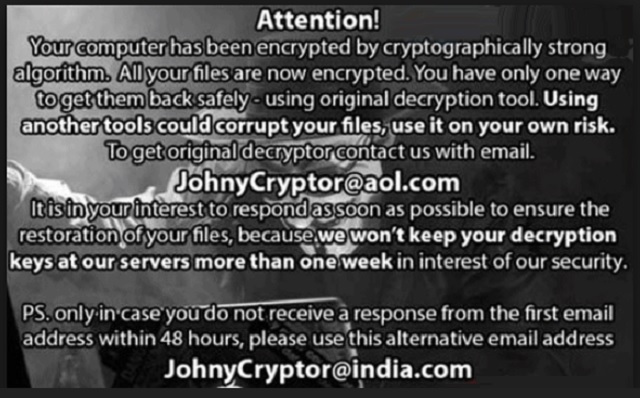
Reader recently start to report the following message being displayed when they boot their computer:
Your computer has been encrypted by cryptographically strong algorithm.
All your files are now encrypted. You have only one way to get them back safely – using original decryption tool. Using another tools could corrupt your files, use it on your own risk. To get original decryptor contact us with email. Johnycryptor@aol.com It is in your interest to respond as soon as possible to ensure the restoration of your files, because we won’t keep your decryption keys at our servers more than one week in interest of our security.
PS. only in case you do not receive a response from the first email address within 48 hours, please use this alternative email address Johnycryptor@india.com
Johnycryptor Ransomware is now updated. Its brand new version is more aggressive, more malicious and more destructive. As if it wasn’t a pest before. This is actually a member of the infamous Troldesh/Shade Ransomware family. The virus uses an AES CBC 256-bit encrypting cipher and RSA-2048 key. Just like all file-encrypting infections out there, Johnycryptor locks your files. Thanks to its strong encrypting algorithm, you’re denied access to your personal data. Pictures, music files, MS Office documents, favorite videos, etc. – all of it falls victim to the parasite. Hackers don’t play around when it comes to ransomware. It goes without saying there might be some immensely important data on your device. That gets encrypted too. Do you see why ransomware has earned the title “worst infection on the Internet”? File-encrypting viruses could cause great harm by locking your files. Johnycryptor utilizes an asymmetric algorithm so it generates two keys. The public one encrypts your data. The private one sets it free. You’ll notice something is wrong with your files if you take a look at their names. Instead of its original extension, the target data now has a new one. A malicious one. Your computer won’t be able to recognize this bizarre file format. As a result, you won’t be able to use or even view your very own personal data. Your files’ names now include an ID, the johnycryptor@hackermail.com email address, and the .xtbl extension. That’s how you know they’re inaccessible. Anything the virus locks, it holds hostage. As mentioned, Johnycryptor generates a private key which allows you to unlock your information. The thing is, hackers aren’t willing to give this key for free. They demand a certain sum of money in Bitcoin (popular online currency). In exchange for your money, you’re supposed to regain access to your encrypted files. The ransom varies between 0.5 Bitcoins (3OO USD) and 1.5 Bitcoins (900 USD). Yes, the privilege to use your own files could cost you 900 dollars. Does it seem like a fair deal? Nothing is fair in the world of cyber infections. Johnycryptor is just the nth attempt for a fraud so don’t even consider paying the money.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How did I get infected with?
One thing is for sure – you didn’t download this program voluntarily. Ransomware doesn’t even need your cooperation; it uses your haste. For example, the virus might have sneaked in as a fake software update or via a malicious torrent. Ransomware often applies some of the oldest infiltration methods. Chances are, you got stuck with Johnycryptor after you clicked open a corrupted email. Spam email-attachments are a particularly effective method to compromise your PC. Messages from unknown senders are equally unreliable. Always remember that preventing installation is much easier than having to delete a virus. The Johnycryptor Ransomware may also get attached to freeware/shareware bundles. In addition, it could get installed with the help of a stealthy Trojan horse. If you come across this infection, check out the PC for more parasites. You might have many more viruses to worry about. Last but not least, stay away from unverified websites and third-party pop-ups. Don’t underestimate any cyber threat and watch out for viruses on a daily basis. There’s no such thing as being too cautious online.
Why is Johnycryptor@hackermail.com dangerous?
While encrypting your data, the virus creates a “How to decrypt your files.txt” file. As you figured out already, it contains payment instructions. Now, you will find this .txt file on your desktop. The PC background gets modified as well. Hackers aren’t trying to be subtle. They’re trying to catch your full attention so they could scam you. According to this ransom message, you only have one week to make the payment. Crooks promise you a decryptor – a unique combination of symbols that will free your files. However, you’d be making a deal with hackers. To say the least, they aren’t famous for being honorable people. Crooks are trying to blackmail you, remember? Not only do they encrypt your files but also attempt to steal your money. Quite a combination, right? Hackers provide you two email addresses – johnycryptor@hackermail.com and an alternative one (johnycryptor@india.com). Stay away from both. This whole thing is a clever way for crooks to extort money from gullible PC users. Do not let hackers involve you in their cyber fraud. Get rid of the virus instead and don’t sponsor their malicious business. Keep your Bitcoins. To delete the parasite manually, please follow our detailed removal guide down below.
Johnycryptor@hackermail.com Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Johnycryptor@hackermail.com Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Johnycryptor@hackermail.com encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Johnycryptor@hackermail.com encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.