Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly DnsSignal.com took over your homepage and you cannot remove it.
DnsSignal.com is a hazardous domain. Its appearance on your screen is a sign of trouble. If it pops up, you’re in for a bad time. Why? Well, you’ve managed to catch a cyber threat. That’s right. There’s an infection, lurking somewhere on your computer. And, the website is its way of revealing its existence. It’s a warning. Don’t ignore it! Act on it! DnsSignal.com popping up is the same as a browser hijacker writing on your desktop “I am here.” Yes, DnsSignal.com indicates the presence of a browser hijacker. And, in case you’ve missed it, that’s not good. Having such a program on your PC leads to repercussions. And, ones, which you won’t enjoy. A hijacker brings a variety of issues. And, keeps on bringing them each day you allow it to remain. That’s why experts advise towards the immediate deletion of the malicious tool. Find where the cyber threat is hiding on your PC. And, delete it at once! Think of DnsSignal.com as the ‘face’ of the menace that you’re stuck with. The infection is using the page as a front, to lurk behind. It’s a big, bright neon sign that there’s trouble ahead. The sooner you acknowledge that and act, the better. Protect yourself and your system from the clutches of the nasty hijacker! As soon as the site shows up, take action!
How did I get infected with?
DnsSignal.com only appears if you have a browser hijacker on your computer. And, those don’t just show up out of the blue, either. These cyber threats require user’s permission to enter. Your permission. They have to ask you whether you agree to install them or not. If you deny them – no admittance. But, usually, you comply. And, you don’t even realize it. Confused? Well, it’s pretty straightforward. Infections, like the one behind DnsSignal.com, do indeed have to seek your approval. But they don’t have to do it openly. So, they do it covertly. They tend to sneak in undetected by using the old but gold methods of infiltration to trick you. In other words, they invade your PC by hiding behind corrupted links or sites. Or, by hitching a ride with freeware or spam email attachments. Or, by posing as a bogus update. Whichever method they turn to, it relies on carelessness. So, don’t be careless! Be more vigilant and thorough! Don’t rush and always do your due diligence. Even a little extra caution goes a long way.
Why is this dangerous?
Once the hijacker settles, you’re in for a whirl of troubles. All of a sudden, you’ll see DnsSignal.com incessantly! It will take over your screen. It will replace your default search engine and homepage. And, it will do so without your knowledge or consent. Yes, the tool is not bound to seek your permission on anything once it has obtained it in regards to its installation. And, that’s a pretty scary thought, don’t you think? If the infection chooses to, it can easily install more unwanted tools. It can approve their installment, and you’ll just have to deal with it afterward. And, how long do you think your system will endure a cyber threat invasion? How long before The Blue Screen of Death? Albeit a minor chance of that occurring, you still have to take it into account. But the malware risk and the possibility of the dreaded blue are just some of the threats you’ll face. Because of the hijacker, you’ll also enjoy frequent system crashes. Your computer will slow down to a crawl. Each time you surf the web, you’ll get flooded with pop-up ads. As well as redirected to DnsSignal.com. Your browsing will never be the same. But all that pales in comparison to the worst part of having a hijacker as a house guest. These infections are programmed to spy on you. Yes, they monitor your browsing activities. But they don’t stop there. Oh, no. They keep a thorough record of your every online move. And, when they determine they have enough data, they send it to the people that published them. Unknown third parties. Are you willing to grant access to your private life to such individuals? Are you prepared to place your personal and financial details into their hands? The hands of strangers with questionable intentions, to say the least? Think long and hard before you answer. Both your and your system’s future rest on your response.
How to Remove DnsSignal.com virus
If you perform exactly the steps below you should be able to remove the DnsSignal.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The DnsSignal.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall DnsSignal.com from Add\Remove Programs
STEP 2: Clean DnsSignal.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove DnsSignal.com leftovers from the System
STEP 1 : Uninstall DnsSignal.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
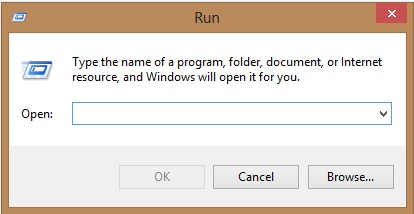
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove DnsSignal.com homepage from Chrome, Firefox and IE
-
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the DnsSignal.com by clicking on the little recycle bin
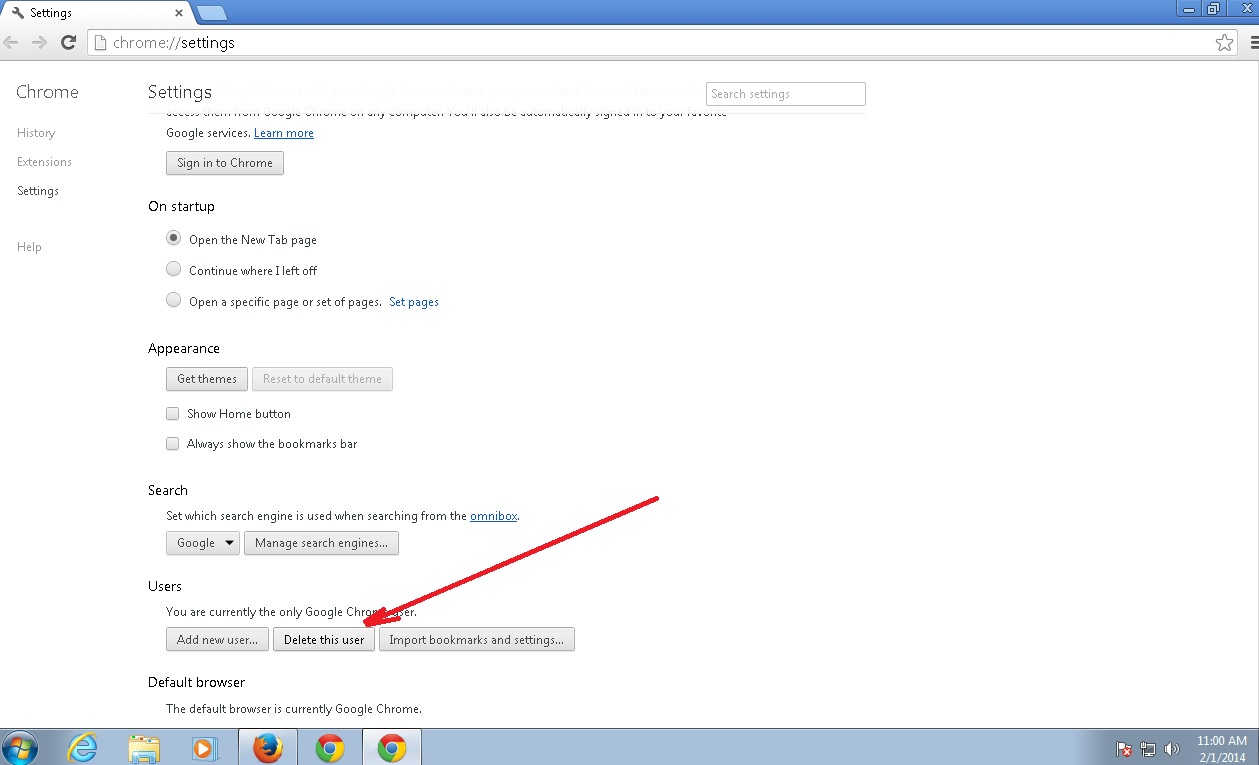
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
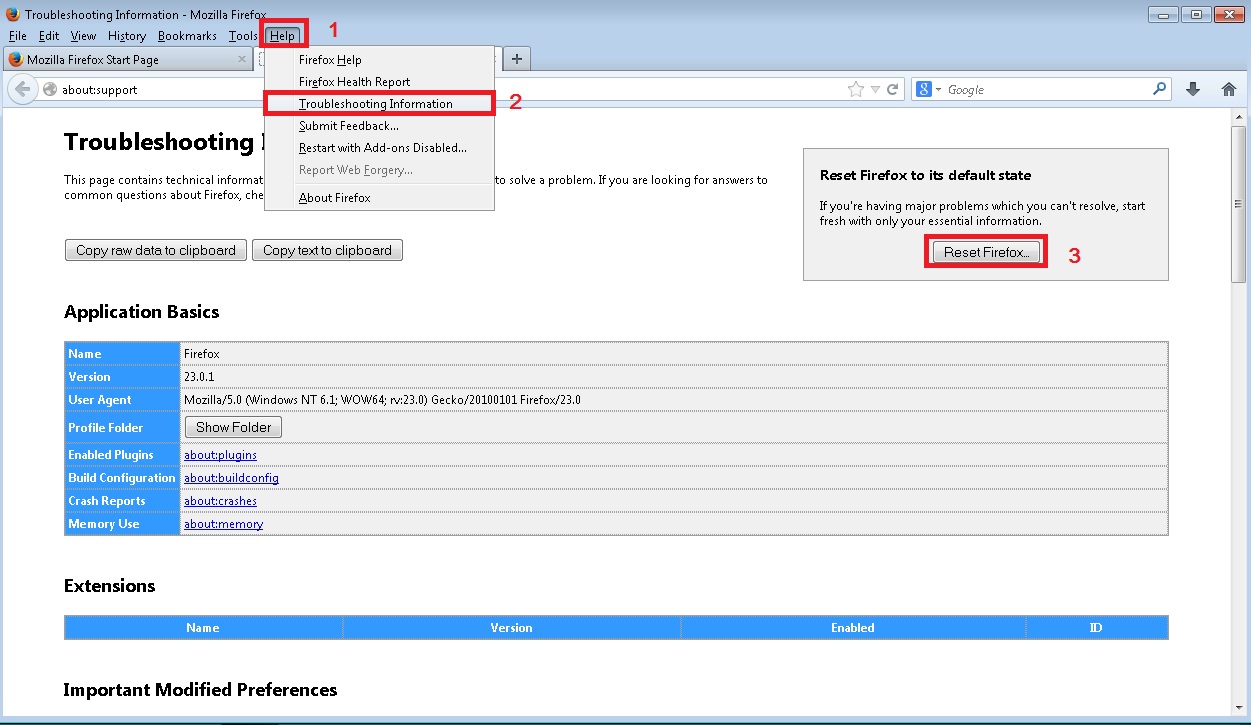
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
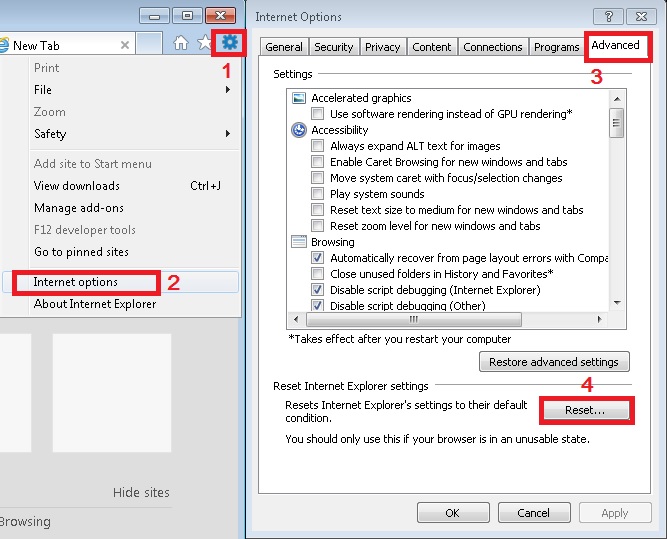
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove DnsSignal.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.