Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Datawait Ransomware?
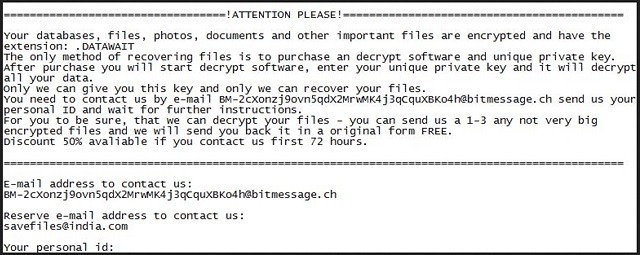
Readers recently started to report the following message being displayed when they boot their computer:
==================================================ATTENTION PLEASE!==================================================
Your databases, files, photos, documents, databases and other important files are encrypted and have the extension: .DATAWAIT
The only method of recovering files is to purchase an decrypt software and unique private key.
After purchase you will start decrypt software, enter your unique private key and it will decrypt all your data.
Only we can give you this key and only we can recover your files.
You need to contact us by e-mail BM-2cXonzj9ovn5qdX2MrwMK4j3qCquXBKo4h@bitmessage.ch send us your personal ID and wait for further instructions.
For you to be sure, that we can decrypt your files – you can send us a 1-3 any not very big encrypted files and we will send you back it in a original form FREE.
Discount 50% available if you contact us first 72 hours.
====================================================================================================
E-mail address to contact us:
BM-2cXonzj9ovn5qdX2MrwMK4j3qCquXBKo4h@bitmessage.ch
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Reserve e-mail address to contact us:
savefiles@india.com
Your personal id:
[redacted – contains 40 symbols]
Datawait Ransomware is yet another destructive virus. This pest sneaks into your system and wrecks everything. It corrupts your entire OS. The virus modifies the Registry, alters settings, corrupts directories, and starts malicious processes. This, of course, happens without any noticeable symptoms. You cannot catch the virus in time to prevent its infiltration. It spreads its corruption throughout and gets your system under control. Datawait Ransomware wastes no time and starts a file encryption process. The virus follows orders to kidnap your personal files and to blackmail you. Datawait is a cryptovirus which uses strong encryption algorithms to corrupt the user-generated files. It targets documents, media, databases, presentations, and archives. The virus adds the “.DATAWAIT” file extension at the end of each corrupted file. Thus, if you have a file named example.txt, the ransomware will rename it to “example.txt.DATAWAIT.” You can see the icons of your files, but you cannot view them. To restore your files, Datawait Ransomware urges you to contact its publishers via email. Do not follow the instructions! Don’t get in touch with these criminals. They know how to deceive people. These people are experienced manipulators. Don’t give them a way to contact you back. They’ll threaten and terrorize you. Unfortunately, there is no third-party file-recovery tool yet. If you, however, have file-backups, you can use them to restore your data. Just make sure that you’ve removed the virus before you start the recovery process!
How did I get infected with?
There are myriads of ways for Datawait Ransomware to infect your device. Torrents, fake updates, corrupted links, and, of course, spam emails are the most commonly used distribution strategies. You can never know where an infection might strike from. The distribution methods, however, are not flawless. They need help to succeed. They need you to let your guard down. Do not make the crooks’ job easier. Do not toss caution to the wind. No anti-virus app can protect you if you act recklessly. Only your vigilance is powerful enough to prevent infections. Choose caution over carelessness. One keeps the parasites away, the other – invites them in. Don’t visit shady websites. Download files from reputable sources only, and be very careful with your inbox. The good old spam messages are still the number one cause of virus infection. The scheme, however, is not what it used to be. The crooks no longer rely on malicious attachments. They still use them, but they also embed corrupted links. Did you know that you can download a virus with just one click? Do not interact with suspicious messages. Treat all unexpected emails as potential threats. If you receive an unexpected email, from your bank, for example, go to their official website. Compare the email addresses listed there to the questionable one. If they don’t match, delete the pretender immediately!

Why is Datawait dangerous?
Datawait Ransomware is a nasty infection. It sneaks into your system and corrupts your data. The virus wrecks your OS and threatens to delete your files if you don’t follow its instructions. This ransomware wants you to contact its owners via email. Don’t act impulsively! If you give into naivety, if you contact the criminals, you will get in bigger trouble. You are dealing with blackmailers. These people target your wallet and are ready to do whatever it takes to get what they want. They’ll threaten, humiliate, and terrorize you. They’ll play with your fears and lure you into unwanted actions. The crooks usually demand astonishing ransoms paid in Bitcoin. This currency is untraceable. If you send them Bitcoin, no one can help you get your money back. Not even the police! As for the decryption tool – the crooks usually ignore the victims once they get the money. You cannot expect them to keep their part of the deal. Even if they want to, they are very likely to be unable. There are cases where the victims paid the ransom only to receive partly working decryption tools. Furthermore, these tools restore your files, but they don’t remove the ransomware. Are you willing to restore your files only to get them re-locked hours later? Do not test your luck! Your best course of action is the immediate removal of Datawait Ransomware! The sooner this menace is gone, the better!
Datawait Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Datawait Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Datawait encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Datawait encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.