Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove CryptoViki Ransomware?
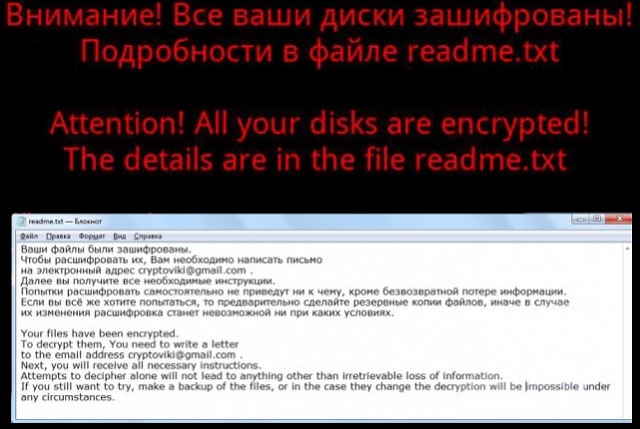
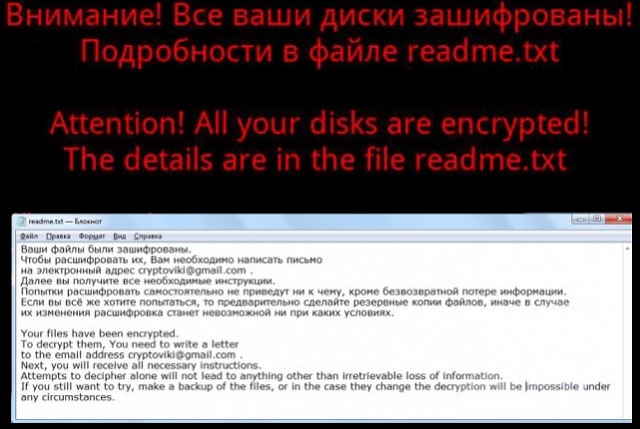
Readers recently started to report the following message being displayed when they boot their computer:
Ваши файлы были зашифрованы.
Чтобы расшифровать их, Вам необходимо написать письмо
на электронный адрес cryptoviki@gmail.com .
Далее вы получите все необходимые инструкции.
Попытки расшифровать самостоятельно не приведут ни к чему, кроме безвозвратной потере информации.
Если вы всё же хотите попытаться, то предварительно сделайте резервные копии файлов, иначе в случае их
изменения расшифровка станет невозможной ни при каких условиях.
Your files have been encrypted.
To decrypt them, You need to write a letter
to the email address cryptoviki@gmail.com .
Next, you will receive all necessary instructions.
Attempts to decipher alone will not lead to anything other than irretrievable loss of information.
If you still want to try, make a backup of the files, or in the case they change the decryption will be
impossible under any circumstances.
As you probably know, CryptoViki Ransomware is a dangerous file-encrypting virus. This infection belongs to the most problematic and troublesome family of parasites. In other words, you’ve downloaded a notoriously pesky infection. CryptoViki Ransomware follows the classic ransomware pattern. You shouldn’t expect any originality out of this parasite. What you should expect out of it is to encrypt your private data. As soon as the virus gets installed, it scans your PC searching for data to lock. Unfortunately, ransomware always finds what it looks for. CryptoViki Ransomware targets a huge variety of file formats. That includes photos, music, videos, MS Office documents, presentations, etc. Every single file you’ve stored on board falls victim to the ransomware. Thanks to its thorough scan, the virus locates all your private information. Then CryptoViki Ransomware uses a strong encrypting cipher to turn your files into gibberish. As a result of its trickery, you will be denied access to your data. Your own data stored on your own computer. It goes without saying how irritating that is. Not to mention, how unfair it is. Ransomware gets developed to serve one very simple purpose. The parasite encrypts your files solely to get you to panic. After all, many people would give into panic seeing their files get locked out of the blue. Hackers will take advantage of your despair so do not let cyber criminals fool you. Once CryptoViki Ransomware encrypts your files, it adds the .viki extension to them. For instance, Birthday2017.mp4 gets renamed to Birthday2017.mp4.viki. That means the original format of your data gets changed and the PC can’t recognize the new one. Eventually, you’re left unable to access or use any of your precious files. If you thought that was bad, wait till you hear the rest of it. CryptoViki Ransomware drops readme.txt files in all folders that contain encrypted data. The parasite might also modify your desktop wallpaper. Hence, you’re seeing hackers’ ransom instructions all the time. Obviously, that’s what they are aiming at. The more often you see ransom notes, the more likely it is that you’ll agree to pay. You can see the scam already, can’t you? Restrain yourself from paying anything because hackers aren’t the right people to negotiate with. Crooks are trying to trick you into giving your Bitcoins away. However, paying the ransom doesn’t guarantee you anything. You may receive no decryptor at all and your files may remain unusable.
How did I get infected with?
There are many popular techniques out there. Perhaps the most commonly used one when it comes to ransomware involves fake emails. Bear in mind that sometimes hackers may sent malware straight to your inbox. It is entirely up to you whether the parasite will be let loose or the bogus email will get deleted. Protecting your machine is indeed much easier than removing infections. Do yourself a favor by paying attention in advance. Be careful what you click open and stay away from random email-attachments/messages. Delete what you don’t trust instead of testing your luck out. Also, avoid illegitimate websites and the programs they offer. Ransomware travels the Web via exploit kits, bogus software updates and malicious torrents. As you can see for yourself, these parasites have plenty of techniques to choose from. The only way to make sure your machine doesn’t end up infected is by paying attention. Be very careful what you click and/or download. Your caution will pay off in the long run so don’t be negligent. Trust us when we say, you have nothing to lose by taking care of your safety. On the other hand, you do have a lot to lose.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Why is CryptoViki dangerous?
CryptoViki Ransomware makes it impossible for you to use your files. As mentioned, the virus renames all your data thus inevitably causing a mess. Hackers also attempt to convince you that you have to buy a unique decryptor in order to free your files. However, does making a deal with crooks really sound like a good idea? It would be a terrible mistake so don’t be naive. Those are the people who encrypted your files in the first place. They have absolutely no reason to keep their end of the bargain. Ignore the parasite’s stubborn ransom notes and don’t let hackers scam you. CryptoViki Ransomware is shamelessly trying to blackmail innocent PC users. The sooner you uninstall this pest of a program, the better. Please follow our detailed manual removal guide. You will find it down below.
CryptoViki Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover CryptoViki Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with CryptoViki encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate CryptoViki encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.