Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove Cryptoloot.pro? This page includes detailed Cryptoloot.pro Removal instructions!
Cryptoloot.pro malware is a parasite that steals your computer resources. It follows programming to turn your machine into a miner. This malware takes advantage of a new concept called “drive-by-mining.” The idea is that when you visit a website that used this technology, a small percentage of your CPU power (usually around 30%) gets employed for coin mining. In exchange for your contribution, you don’t get bombarded with online ads. The coin mining should stop when you exit the website. That, sadly, is not the case with Cryptoloot.pro. This menace doesn’t stop mining. It doesn’t even limit its resource consumption. The malware takes everything your device has to offer and leaves nothing for you. It overloads your CPU and causes overheating and crashes. Not to mention the underperformance. The malware makes your system very slow and unresponsive. You will notice that your apps take forever to load, that they freeze and crash, that errors pop up out of the blue. Do not put yourself through this torture. Don’t tolerate the miner. Find where Cryptoloot.pro hides and remove it upon detection.

How did I get infected with Cryptoloot.pro?
Cryptoloot.pro sneaks into your computer when you visit websites that use drive-by-mining. Don’t imagine a cyberattack, though. The miner needs you, the user, to approve its access. It usually does so through notifications that urge you to “Approve” or “Accept” its services. Sadly, the malware doesn’t disclose its functions properly. Sometimes it doesn’t even ask but lures you into clicking on corrupted notifications. The malware tricks its victims into installing it. It preys on your naivety! Do not make its job easier. Choose caution over carelessness. Your vigilance is powerful enough to prevent infections. Even a little extra attention can spare you an avalanche of problems. So, don’t be lazy! Always take the time to do your due diligence. Don’t follow questionable links. Make sure you know what you approve on your computer. Download software and updates from reliable, preferably official, sources only. And, of course, forget about the “Next-Next-Finish” setup strategy. Most of the apps we download off the web come bundled with bonus software. If you don’t pay attention to the fine print, you are very likely to install malicious extras. Do not rely on luck! If available, use the advanced/custom setup option. Deselect the unwanted extras and go through the terms and conditions. If you can’t read the whole document, scan it with an online EULA analyzer. Don’t hesitate to abort the installation if you notice anything suspicious!
Why is Cryptoloot.pro dangerous?
Cryptoloot.pro is a menace. It sneaks into your computer and ruins your user experience. The malware steals your computer resources and leaves you with a slow, unresponsive computer. It causes annoying performance issues, as well as threatens to shorten your CPU’s lifespan significantly. The thing about coin mining is that this process overloads your CPU and causes overheating. By using your processor under high temperatures for prolonged periods, you risk serious hardware damage. Cryptoloot.pro, however, doesn’t care about your device. It doesn’t pause its mining processes. The longer it mines, the bigger the profit. Its operators don’t take any risks. It’s you the one who might end up with an irreparable device. And that’s just the tip of the iceberg. The increased electricity consumption is also worth mentioning when talking about coin mining. Don’t be surprised when your next electricity bill arrives. The coinminer is very likely to affect it. Do not put yourself through this. Don’t sponsor cybercriminals. Your best course of action is the immediate removal of the malware. Take action as soon as you notice Cryptoloot.pro. Remove this intruder ASAP!
How Can I Remove Cryptoloot.pro?
If you perform exactly the steps below you should be able to remove the Cryptoloot.pro infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
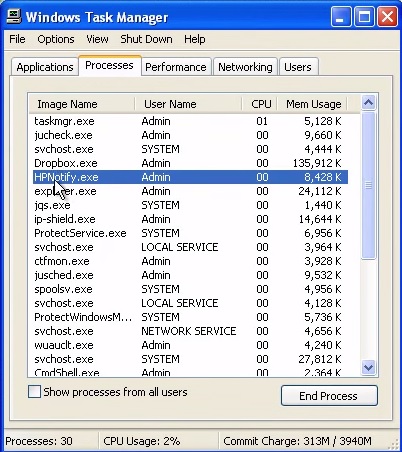
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of Cryptoloot.pro.exe and kill it
- Open your windows registry editor by typing”regedit” in the windows search box
Navigate to (Depending on your OS version)
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
and delete the display Name: Cryptoloot.pro
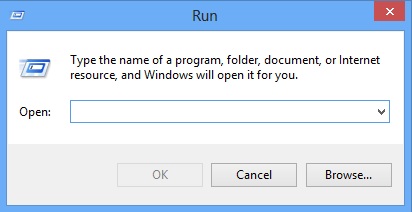
Simultaneously press the Windows Logo Button and then “R” to open the Run Command
Type “Appwiz.cpl”
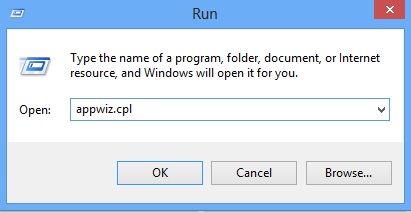
Locate the Cryptoloot.pro program and click on uninstall/change. To facilitate the search you can sort the programs by date. Review the most recent installed programs first. In general you should remove all unknown programs.
Navigate to C:/Program Files and delete Cryptoloot.pro folder. Double check with any antimalware program for any leftovers. Keep your software up-to date!