Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Cerber 4.1.1 Ransomware?
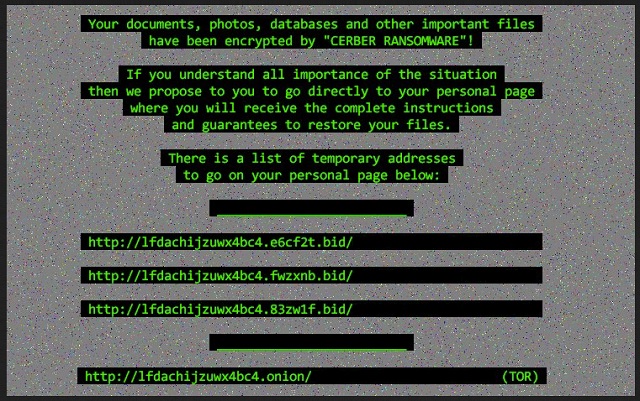
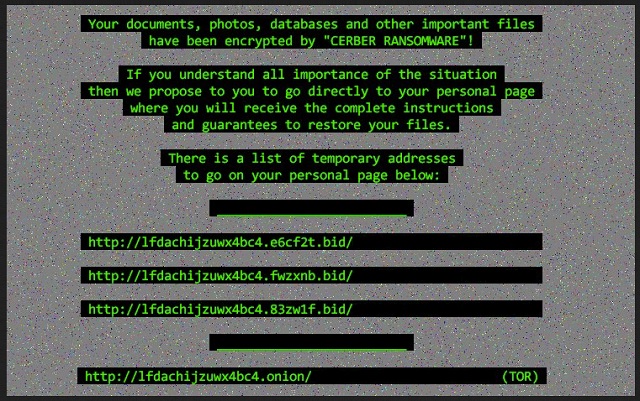
Readers recently started to report the following message being displayed when they boot their computer:
Your documents, photos, databases and other important files have been encrypted by “Cerber ransomware 4.1.1”!
[…]
There is a list of temporary addresses to go on your personal page below:
The notorious Cerber Virus is back – stronger and shiftier than ever. To say that hackers are interested in this program would be quite an understatement. Crooks are focused on it. Cerber has already established itself as a particularly dangerous infection. Hence, hackers constantly try to make it even more devastating and problematic. So far, looks like they’re succeeding. Today’s article is all about Cerber’s latest version named Cerber 4.1.1. It uses a complicated encrypting cipher to lock your personal files. All of them. There’s a reason why the Cerber virus is so immensely dreaded. This pest goes after a huge percentage of formats including music, pictures and documents. The problem is, you’ve probably stored some important data on your computer. Ransomware doesn’t discriminate between precious and minor files. It encrypts both. Cerber 4.1.1 renames the target files thus making them unreadable. The virus also adds some bizarre extension once encryption is complete. That is how you know your private information is inaccessible. Unfortunately, this program’s encrypting algorithm is strong. Cerber 4.1.1 utilizes the AES or RSA ciphers and effectively locks your files. Then it holds them hostage and attempts to blackmail you. You see, ransomware has one purpose only. File-encrypting programs lock private data because that would make many people panic. And, once you panic, you no longer think logically. That is precisely what hackers are aiming for. Ransomware-type programs are just clever cyber scams so you must be careful. If you give into anxiety and despair, you might lose a hefty sum of money. Now, how does the scheme work? In the process of encrypting your data, Cerber 4.1.1 adds .txt files. Those are your payment instructions. You will find the .txt files in all folders that contain encrypted data. The virus also modifies your default PC wallpaper. All of this is part of the program’s trickery. By forcing its ransom notes on you, Cerber 4.1.1 is trying to deceive you. In the ransom messages you’ll read that there is a special decryptor for your files. However, it doesn’t come for free. Crooks promise this decryption key in exchange for some Bitcoins (online currency). The sum demanded varies but it’s rarely less than 0.5 Bitcoin (361 USD). It goes without saying that making a deal with cyber criminals is a terrible idea. There’s no guarantee crooks will keep their end of the bargain. Therefore, paying may significantly worsen your already pretty bad situation.
How did I get infected with?
Ransomware is just a PC program. It must get installed properly before it starts harassing you. For example, the virus might have been attached to a fake email or message. Be careful what you click open as it might be corrupted and very dangerous. More often than not, spam email-attachments are unreliable. Infections pretend to be perfectly legitimate mail but you should know better than that. Keep an eye out for potential intruders and take your time. Rushing does guarantee you speed but it leaves your PC vulnerable. Other infiltration methods involve exploit kits, bogus software updates and malicious torrents. Ransomware is extremely secretive and sneaky. It lands on board in silence. The Cerber 4.1.1 malware might have also been bundled with other programs. Stay away from unverified freeware/shareware bundles in order to protect your device. Last but not least, avoid illegitimate websites and third-party pop-ups. Make sure your PC system remains infection-free; you won’t regret it.
Why is Cerber 4.1.1 dangerous?
Ransomware is a complete and utter pest. Not only does it lock your files but it demands money from you. Furthermore, even paying the entire ransom doesn’t guarantee you anything. Crooks’ very last concern are your encrypted files. As mentioned, they are after your money. To prevent getting scammed, restrain yourself from paying. Why give hackers your Bitcoins? Those are the people who locked your data in the first place. Do they really deserve to be rewarded for that? Every single cent they gain will be used to develop more infections. As a result, more people will fall victims to this aggravating fraud. Our advice is to get rid of the parasite instead of giving your money away. Make the right decision and don’t be gullible. To delete Cerber 4.1.1 manually, please follow our removal instructions down below.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Cerber 4.1.1 Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Cerber 4.1.1 Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Cerber 4.1.1 encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Cerber 4.1.1 encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.