Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove Blackfight.info pop-up ads? This article includes Blackfight.info Removal instructions!
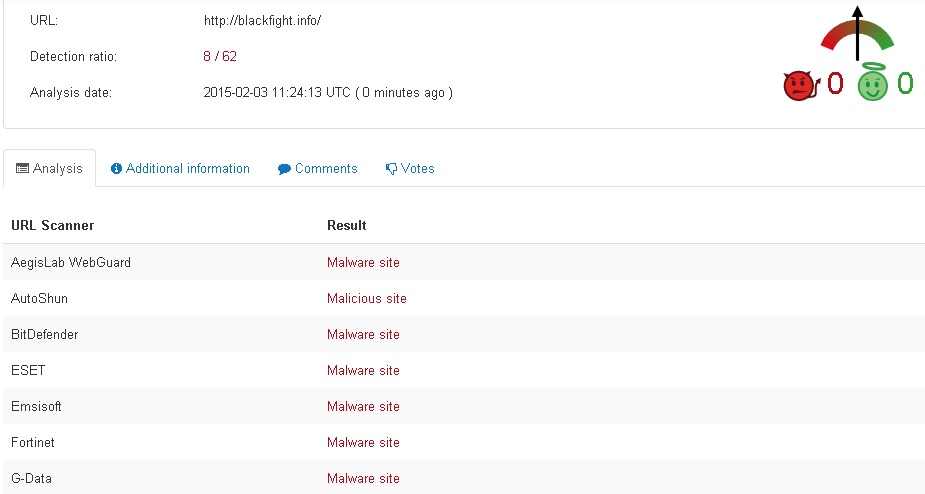
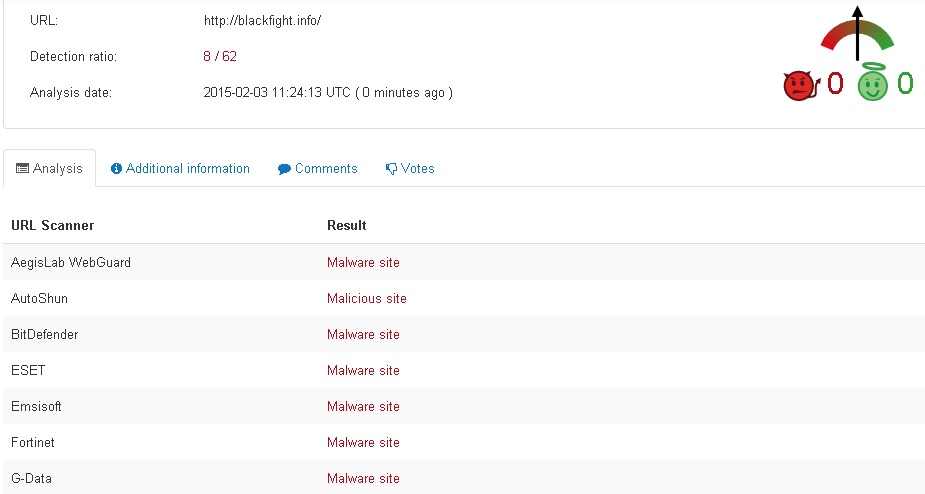
Blackfight.info is hosting malicious dll files. If you turn on your computer and when you try to browse the internet end up with numerous pop-ups from Blackfight.info, know that you’re dealing with a browser hijacker. You don’t remember approving the change, and you have no clue as to how you ended up with this application, but there it is. Even though, you don’t know it, you’re the reason you’re stuck with this harmful and intrusive add-on. That’s right. It duped you into allowing it in your system without you even realizing it, probably because you weren’t paying attention when you should have. Unfortunately, your distraction is going to cause you a whole bundle of troubles as Blackfight.info is a malicious unsafe and damaging program. If you wish to avoid having to deal with it and its daily messes, be sure to delete it the first chance you get. In the same IP address you can find reduled.info which along with Blackfight.info are hosting the following malicious dll files: StarterPro.dll, SystemAdvance.dll, SystemAide.dll, SystemAssister.dll, TerminusEdit.dll,
PathRunner.dll, BorderlineFoobar.dll, LibraryMaker.dll, SegmentAugmenter.dll and PathSystem.dll. there is no doubt that both websites are created with a single purpose – to distribute malware!
How did I get infected with?
Blackfight.info requires your permission for its installation, and it has come up with plenty of ways with which to deceive you into giving it. The application usually sneaks in undetected with the help of freeware. It provides possibly the easiest access point as most users rush through its installation and don’t pay nearly as much attention as they should. For some reason, they believe it’s a sublime idea to not read the terms and conditions, and just agree to everything in haste. Well, as surprising as it may seem, it’s not a sublime idea. Nothing good can come from, not knowing what the program is asking you to agree to, but still making the conscious choice to agree to it. Don’t throw caution to the wind and be more attentive! Some of Blackfight.info’s other preferred methods of infection include the use of corrupted links, corrupted websites, and spam email attachments. It can also pose as a false system or program update. If you wish to avoid getting stuck with this program, remember that a little extra attention can go a long, long way.
Why are these ads dangerous?
As soon Blackfight.info as slithers its way into your computer, it’s no longer bound to seek your permission before implementing changes. That means that it has the liberty to do whatever it feels like doing, whenever it feels like it. Just think of the magnitude of troubles that can cause you. For example, the program can decide to install more malware on your computer. And if one malevolent program can cause so much harm, just imagine what would be like if you were invaded by five more. How long do you think your system will last? But that’s just one of the “glorious” perks of having a hijacker in your system. Another is the incessant bombardment of pop-up advertisements. Every single time you attempt to browse the web, you will be greeted by a pop-up. Not only will that be incredibly infuriating, but it will also be extremely dangerous. That’s because the ads are highly unreliable and clicking on them may further damage your system. But the worst issue you’ll be faced with, courtesy of Blackfight.info, will be having your personal and financial information in harm’s way. The hijacker is programmed to spy on you and catalog every single move you make. Once it feels it has collected enough data on you, it proceeds to send it to the unknown wicked third parties who support it. Don’t jeopardize your privacy! Delete Blackfight.info at once!
How Can I Stop Blackfight.info Ads?
If you perform exactly the steps below you should be able to remove the Efix infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
STEP 1: Delete Unwanted software from your add/remove programs
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 2: Disable Blackfight.info from Chrome, Firefox or IE
STEP 3: Permanently Remove Blackfight.info leftovers
STEP 1 : Delete Blackfight.info from add/remove programs
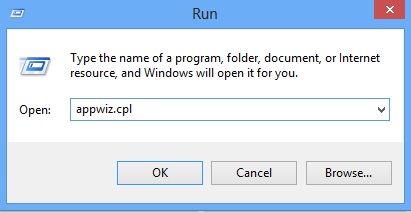
Simultaneously press the Windows Logo Button and then “R” to open the Run Command
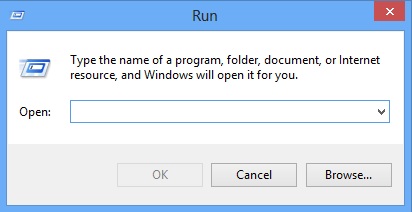
Type “Appwiz.cpl”
Locate the unwanted program and click on uninstall/change. To facilitate the search you can sort the programs by date. review the most recent installed programs first. In general you should remove all unknown programs.
STEP 2 : Remove Blackfight.info from Chrome, Firefox or IE
Remove from Google Chrome
- In the Main Menu, select Tools—> Extensions
- Remove any unknown extension by clicking on the little recycle bin
- If you are not able to delete the extension then navigate to C:\Users\”computer name“\AppData\Local\Google\Chrome\User Data\Default\Extensions\and review the folders one by one.
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
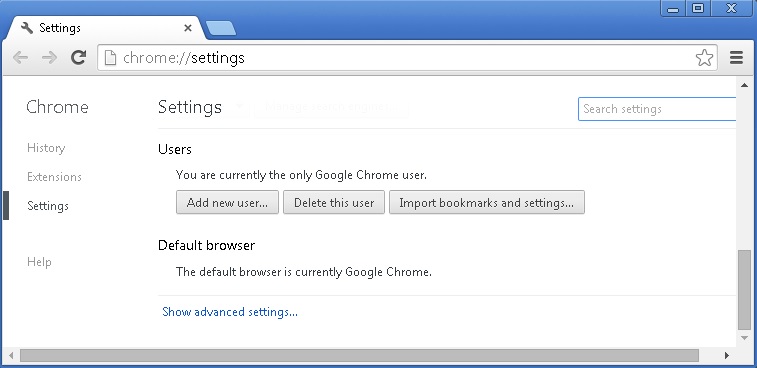
- If you are using the latest chrome version you need to do the following
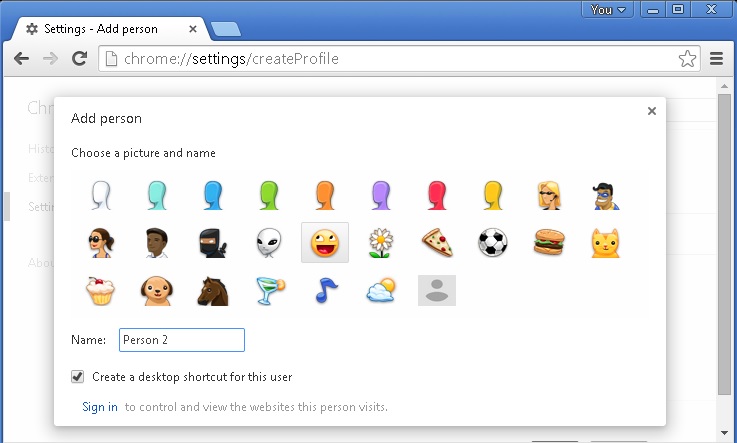
- go to settings – Add person
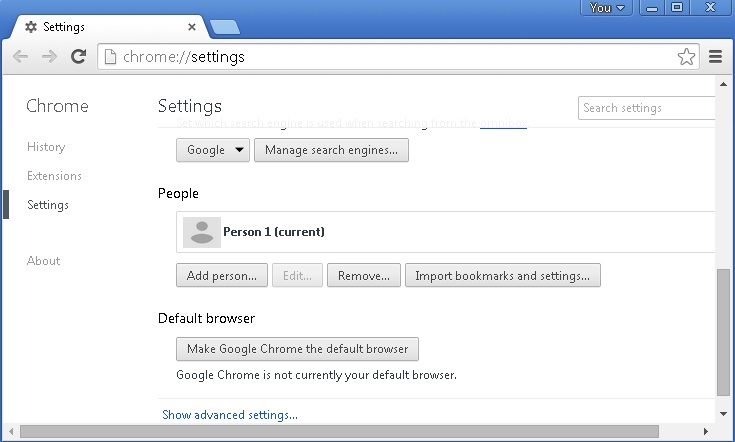
- choose a preferred name.
- then go back and remove person 1
- Chrome should be malware free now
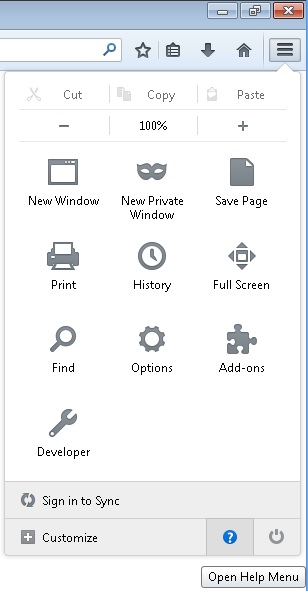
Remove from Mozilla Firefox
- Open Firefox
- Press simultaneously Ctrl+Shift+A
- Disable and remove the unwanted add on
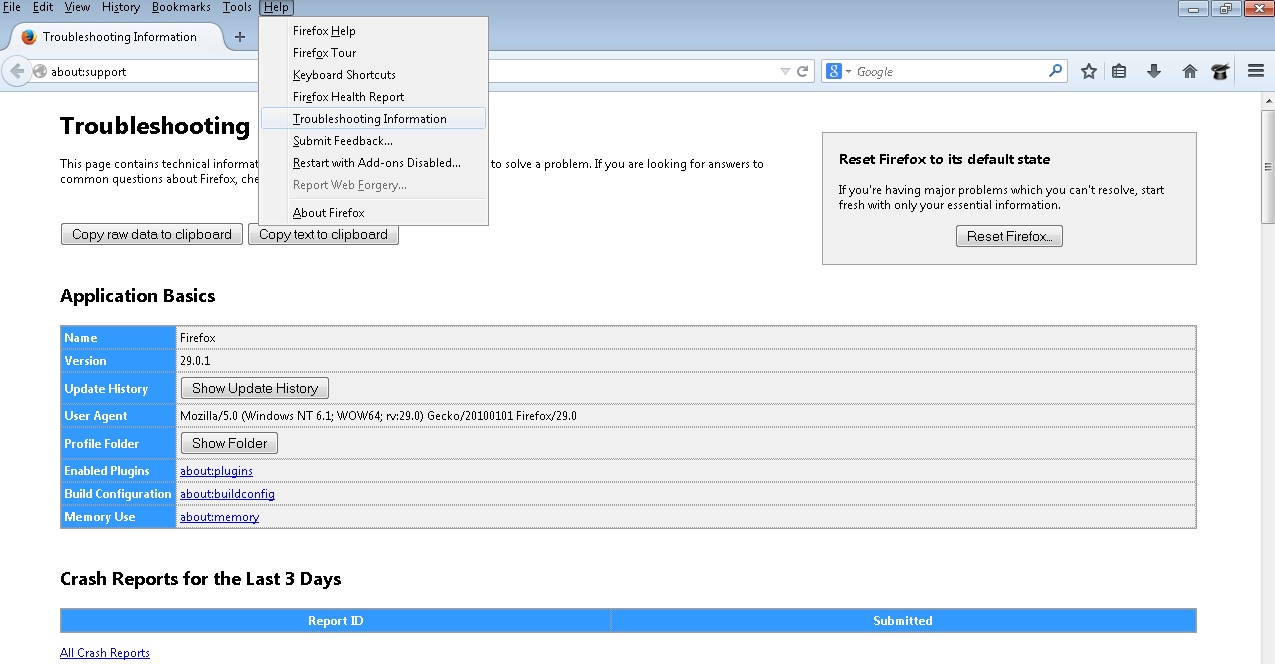
- Open the Firefox’s Help Menu
- Then Troubleshoot information
- Click on Reset Firefox
Remove from Internet Explorer
- Open IE
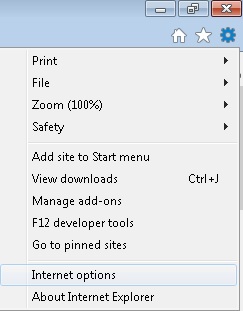
- On the Upper Right Corner Click on the Gear Icon
- Go to Toolbars and Extensions
- Disable any suspicious extension.
- If the disable button is gray, you need to go to your Windows Registry and delete the corresponding CLSID
- On the Upper Right Corner of Internet Explorer Click on the Gear Icon.
- Click on Internet options
- Select the Advanced tab and click on Reset.
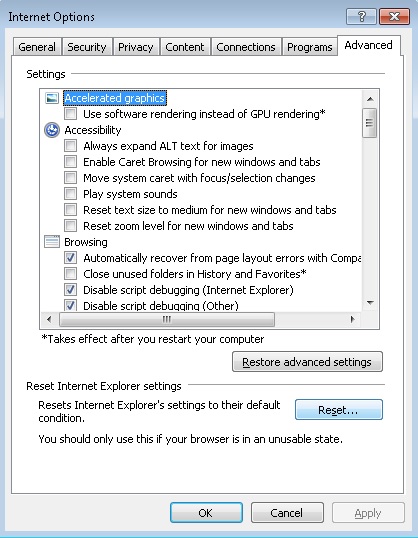
- Check the “Delete Personal Settings Tab” and then Reset
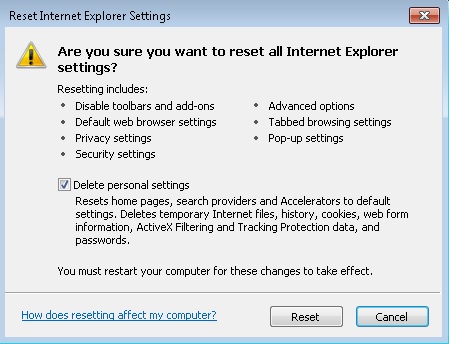
- Close IE
Permanently Remove Blackfight.info Leftovers
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify any registry leftovers or temporary files.