Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Atom Ransomware?
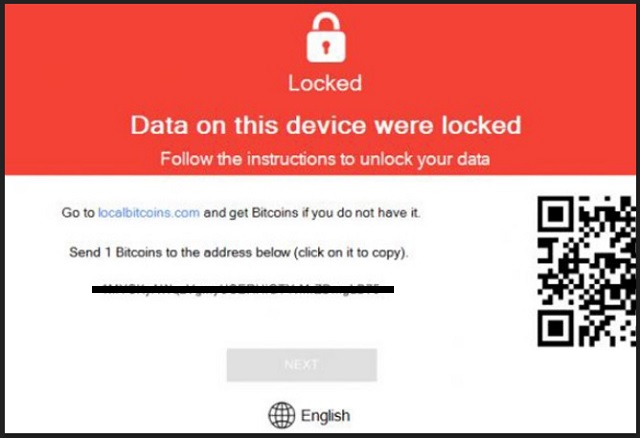
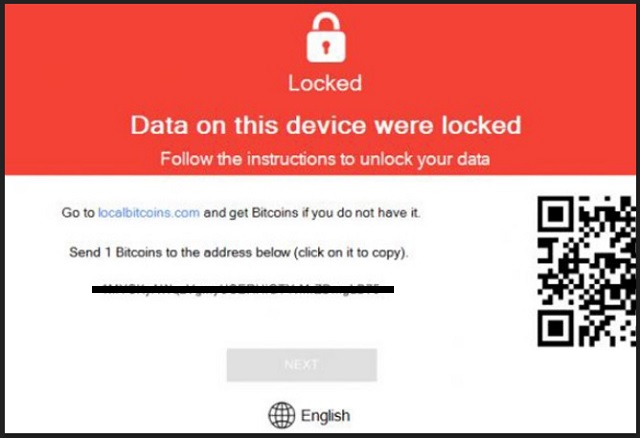
Reader recently start to report the following message being displayed when they boot their computer:
Locked
Data on this device were locked
Follow the instructions to unlock your data
Time left: N/A
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Atom is the name of a new ransomware-type infection, plaguing web users. It’s an updated version of the Shark ransomware, which was also quite the menace. Atom offers a web-based platform of sorts. You can use it to customize the infection’s executables. And, then unleash new custom variants of it onto the web. In other words, Atom’s selling point is that allows users to create their own ransomware. People, who have no computer programming knowledge. No previous skills in generating such cyber threats. Atom helps them make a cyber plague with which they can extort you for money. That’s the end game of all ransomware tools. Monetary profit. So, once the people create their monster, they set it free, and wait. It doesn’t take long before they claim victims with their newly-created menace. And, subsequently, make money. But don’t think Atom’s developers have designed Atom the way it is, because they want to help others make money. Oh, no. Don’t be naive. They also make money through them. They claim a slice of their pie. Let’s elaborate. Yes, Atom can be downloaded for free from its official website. But the ones, who download it, do end up paying. That’s because its developers ask for a 20% commission on each payment you collect, using their product. So, if you use Atom to create a ransomware-type threat, and claim victims. Twenty per cent of the money, you collect from said victims, goes to Atom’s developers. Needless to say, Atom is an utter plague. And, so are all ransomware infections. Ones, which spawn from it, and ones that don’t. If you find yourself stuck with such a nasty tool, do NOT pay! It’s better to lose every file you have on your PC than pay a dime to these strangers! Do NOT transfer any money to them!
How did I get infected with?
Ransomware usually sneaks in undetected with the help of slyness and subtlety. And, of course, the old but gold means of infiltration come in handy. Like most infections, the one you’re stuck with, invades your PC slyly. It slips through the cracks, provided by your carelessness. It preys on gullibility, distraction, and haste. That’s why it’s imperative NOT to provide them! Do the exact opposite! Instead of rushing, always take your time to be thorough. Don’t throw caution to the wind, but be even more vigilant! For example, when you’re installing a tool or an update, read the terms and conditions with care. Don’t just skip them, and agree to everything. Chance and luck are NOT your friends. Do not rely on them. But do you know what you can rely on? Due diligence and attentiveness. They can save you a ton of troubles and headaches.
Why is Atom dangerous?
Atom is a means for wannabe scammers to make money off of unsuspecting, naive users. We say ‘naive’ with purpose. If you believe that by paying, you’ll regain control of data, you’re fooling yourself. But we’re getting ahead of ourselves. Let’s start at the beginning. Once the ransomware invades your system, it goes to work. It encrypts each file you have on your computer via asymmetric cryptography. It locks your data by adding an extension at the end of each file and, thus, renders it inaccessible. So you can no longer open it. And, you can try to rename it, or move it, but it won’t change anything. Your files are beyond your control. The only way to release them from the infection’s clutches, is with a decryption key. But to get it, you have to pay a ransom. That’s how ransomware operates. It holds your data hostage, and extorts you for money. Once the encryption is done, the tool creates an executable named UNLOCK DATA. If you click it, it opens a pop-up that holds the infection’s ransom demands. The EXE file can be found in all your folders. The information there is scarce. It just says that your data is locked, and if you wish to unlock it, you have to pay up. There’s also a timer to put additional pressure on you. Supposedly, when it runs out, the decryption key gets deleted. And, subsequently, you lose your files. Do NOT give into the scare tactics! There is NO way you can win a fight against a ransomware application! The odds are not in your favor as the game is rigged against you from the start. There are so many ways the exchange can go wrong. But, even if everything goes right, you still lose. Because, here’s the thing. If you complete the transaction, and pay the ransom, you open a door you cannot then close. You give access to your personal and financial information to strangers with wicked intentions. Information, which they can use as they so wish afterwards. Don’t allow that to happen! It will NOT end well! So, whatever you do, do NOT pay the cyber criminals extorting you. It’s quite unpleasant to lose your data. But it’s much worse to lose your privacy.
Atom Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Atom Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Atom encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Atom encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.