Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
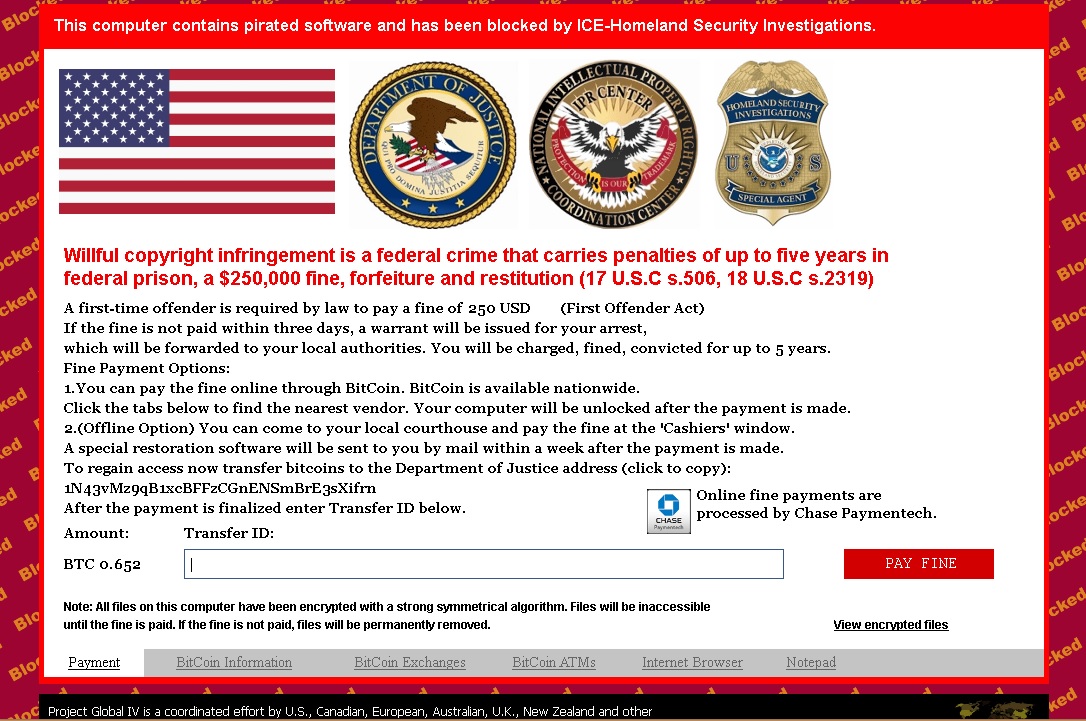
If you are seeing “This computer contains pirated software and has been blocked by ICE-Homeland Security Investigations” message – you are in a big trouble!
Ice-Homeland Ransomware is a nasty infection that will lock your screen and display the above message. A full screen message will appear saying that you have committed crimes associated with copyright and because of that you are due to pay a fine of $250. To make it even more realistic and scary, you are threatened with federal prison and some laws are quoted. What is more disturbing, however, is the fact that it also says in the message that all the files on your PC have been encrypted and that they will be permanently removed if you do not pay the fine. Still, we strongly advise you against paying any money to the unknown individuals behind this infection.
The main thing you should remember about the Ice-Homeland Ransomware is that it is you who allow it to enter the system. For example, when you open a spam email containing an attachment and decide to run the file, the infection gets installed automatically. The same happens when you download freeware from unreliable file sharing websites. The free app is bundled with the infection and gets installed along with it. Ice-Homeland Ransomware could also infiltrate your system after clicking some of the ads that pop up on dangerous web pages. In any of the cases it is possible to avoid infecting your system with Ice-Homeland Ransomware if you are more careful with the websites you browse and the content you download.
It is a very unpleasant experience to be infected with Ice-Homeland Ransomware as the consequences are usually damaging. If you did not back up your files before you were infected, you should know that you will lose them for good. This could be quite upsetting but it should not make you consider paying the requested fine. The cyber criminals responsible for the Ice-Homeland Ransomware infection are only interested in obtaining your money not in restoring your files, so there is no guarantee that you will have them decrypted after giving those people what they want. Also, the screen displaying “This computer contains pirated software and has been blocked by ICE-Homeland Security Investigations” will contain tabs for accessing Internet Explorer or connecting to online BitCoin vendors. You should not agree to exchange your money for BitCoins as Ice-Homeland Ransomware may record the banking details you enter, which may lead to money loss. All in all, you should immediately erase Ice-Homeland Ransomware if it lands on your system, and should properly protect your PC to prevent similar problems in future.
ICE-Homeland Ransomware Removal Instructions
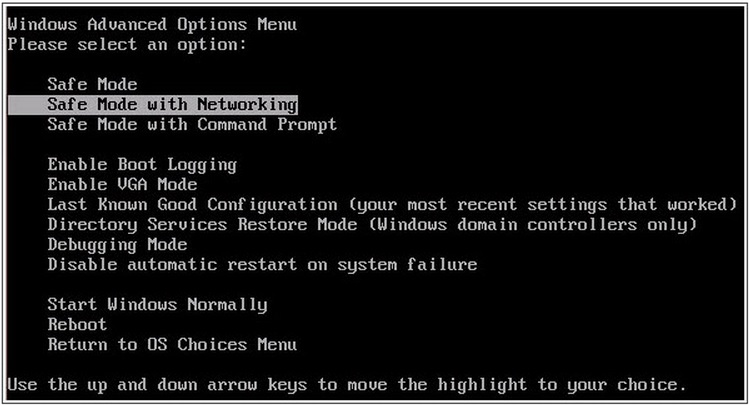
STEP 1: Start the infected Computer into Safe Mode with Networking
- Make sure you do not have any floppy disks, CDs, and DVDs inserted in your computer
- Restart the computer
- When you see a table, start tapping the F8 key every second until you enter the Advanced Boot Options
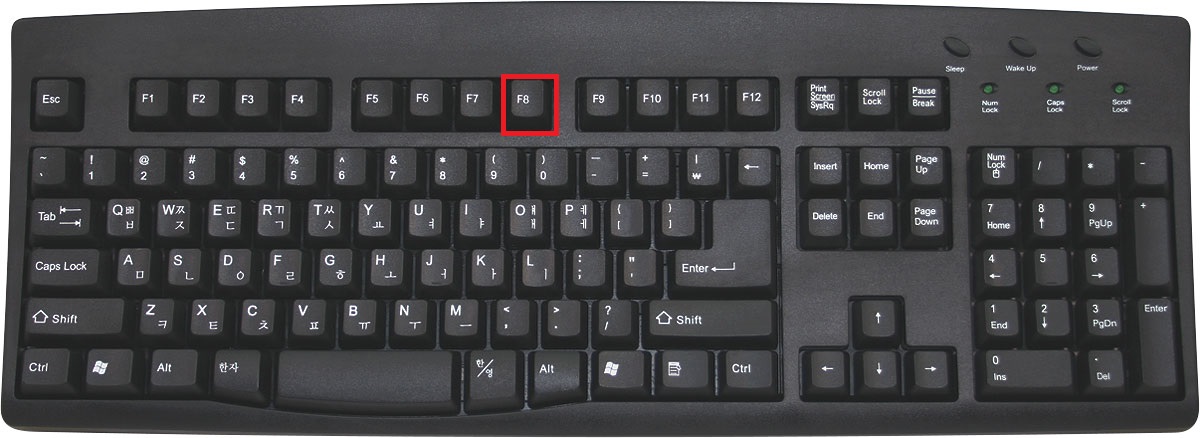
- in the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
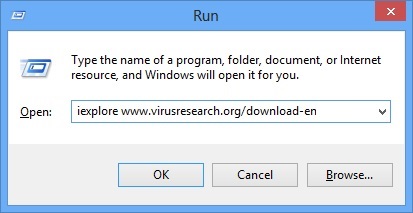
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type iexplore www.virusresearch.org/download-en
- Internet Explorer will open and a professional scanner will prompt to be downloaded
- Run the installer
- Follow the instruction and use the professional malware removal tool to detect the files of the virus.
- After performing a full scan you will be asked to register the software. You can do that or perform a manual removal.
Remove “This computer contains pirated software” Virus Manually
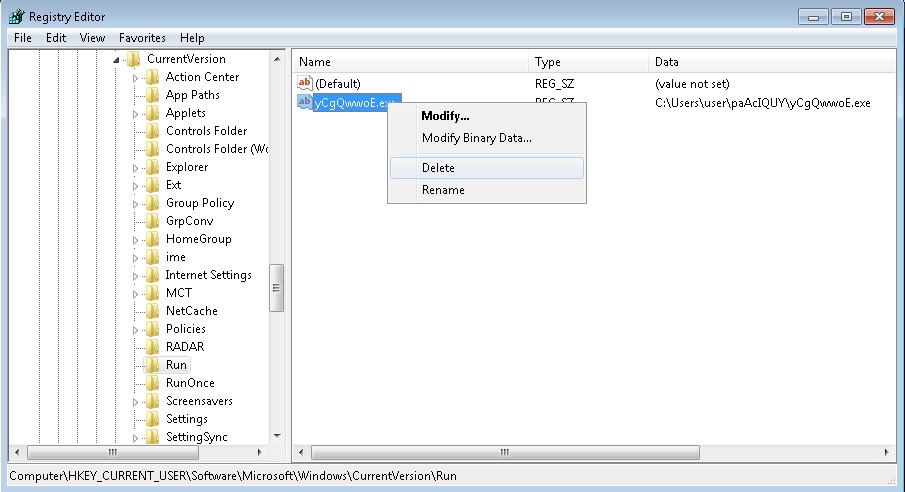
You need to delete the following files and registry keys. These were in our case:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run:yCgQwwoE.exe
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
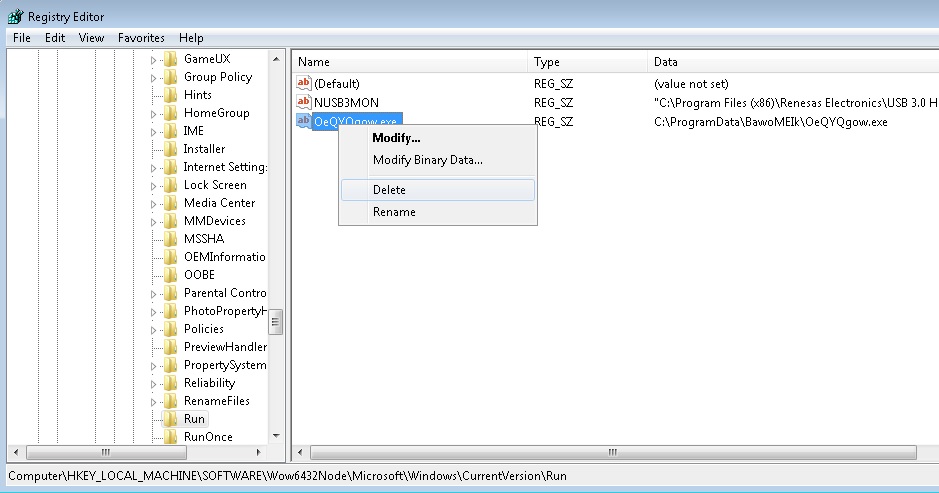
HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run:OeQYQgow.exe
Delete the following service:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\AIEcwsDJ
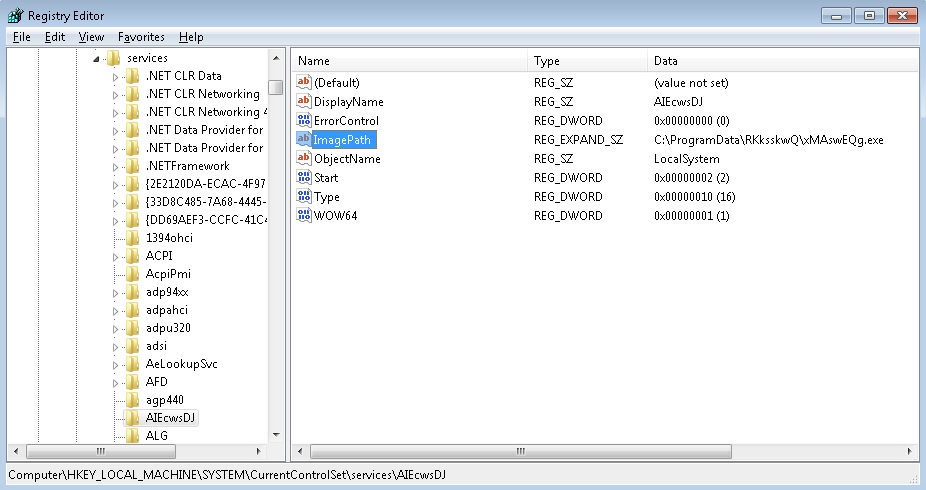
Navigate to your program data folder and delete the executable. Please, not that you need to enable hidden files.
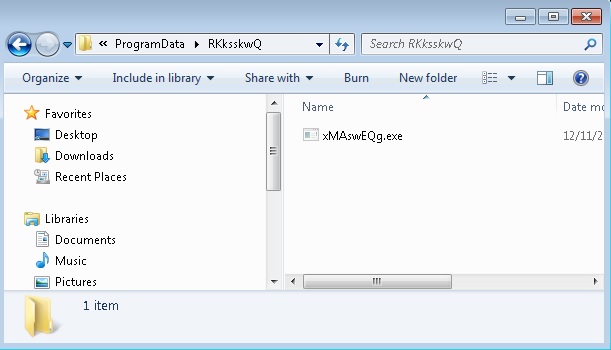
You can alternatively use your msconfig to disable the execution point of the virus. Please, have in mind that the names in your machine might be different as they are generated randomly, that’s why you run the professional scanner to identify the files.
It is always a good idea to use a reputable anti-malware program after manual removal, to prevent this from happening again.