Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove Searchgle.com scam? This page includes detailed Searchgle.com Removal instructions!
Even heard of phishing sites? Searchgle.com is one such site. They’re called that for a reason. They bait you. They fool you into doing something, you’ll later regret. To trust something that shouldn’t be trusted. Don’t be the fish that bites! Be smarter than the catch of the day. The site is the mere tip of the iceberg of dangers, lurking beneath the surface. It’s a slippery slope to trust the site. That opens the door to a myriad of grievances. You jeopardize your system’s well-being, as well as your privacy. To rely on the unreliable leads to an avalanche of consequences. Redirects to more suspicious sites. A bombardment of pop-up advertisements. Frequent system crashes. A slower computer performance. A severe risk of more malware installs. A possibility of getting stuck with The Blue Screen of Death. And, above all, getting your personal and financial data stolen and exposed. Whichever way you look at it, Searchgle.com does not deserve your trust. So, don’t grant it. Think of the page as a door, you mustn’t open. You won’t like where it takes you.
How did I get infected with?
Searchgle.com shows up after malware infiltrates. A malicious cyber threat managed to invade your system. And, you’re now starting to suffer the repercussions. The page is among the first visible consequences. How do you suppose the infection slithered into your PC? Cyber threats have to get approved in. They have to ask the user for permission on their admission. And, proceed with install, only after receiving it. In other words, you green-lighted the tool behind Searchgle.com. If you hadn’t, the page wouldn’t pop-up at all. Do you remember the exchange? Can you recall the infection asking permission, and you complying? It’s not surprising if you don’t. Malware doesn’t choose the straightforward approach. It seeks entry in the sneakiest way possible. So sneaky that if you’re not cautious enough, it slips by you. Spam email attachments, freeware, fake updates. The list is extensive. There are many methods, infections can use. But all share a common characteristic. They rely on your naivety, haste, and distraction. So, don’t grant them. Instead of throwing caution to the wind, be extra thorough. Vigilance goes a long way. Even a little extra attention helps to keep an infection-free PC. Choose caution over carelessness.
Why are these ads dangerous?
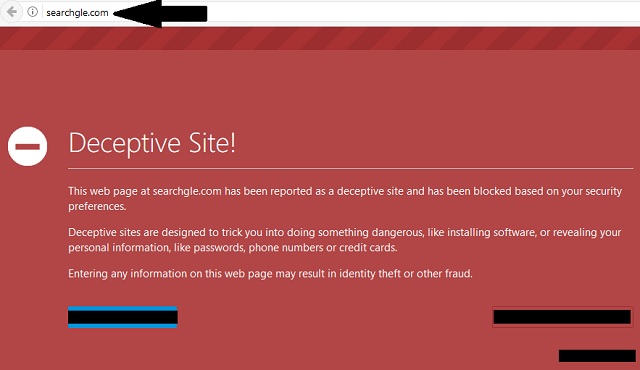
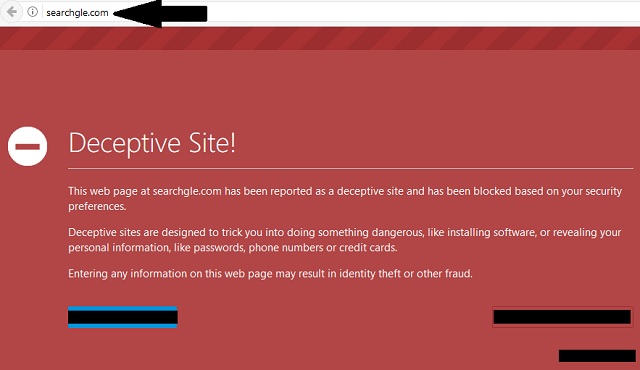
If you visit the Searchgle.com website, you see red. Your entire screen turns into a warning. You get greeted with text that tries to protect you from the hazardous page. It states, you’re dealing with a “deceptive site!” One, which might “trick you into doing something dangerous.” You find an entire list of dangers, you face, courtesy of the page. Like, installing unreliable software and getting your privacy stolen. Yes, to trust the site is to have your privacy exposed. If you go down that path, you might as well say goodbye to your private life. It won’t remain private for long. The cyber criminals behind Searchgle.com get a hold of your sensitive information. Passwords, credit cards, phone numbers, bank account/s. All your personal and financial details end up falling into their hands. That’s a valid possibility. It’s not a matter of if, it’s a question of when. Why take such a severe risk? Think about it. Even if the odds, of exposing your privacy to strangers, are close to 0.0001%, will you take them? Is it worth it? Is that a gamble, you justify taking? And, for what? Don’t expect to gain anything positive from the experience. Searchgle.com is a hazardous page. One, whose display leads to a plethora of problems. Do yourself a favor, and heed the warning. It can save you a ton of headaches and unpleasantness. You’ll earn the gratitude of your future self if you do. To discard it doesn’t earn you thanks. Only wrath and judgment. Do the right thing. Label Searchgle.com as dangerous, and avoid it like the plague. It’s for the best.
How Can I Remove Searchgle.com Ads?
If you perform exactly the steps below you should be able to remove the Searchgle.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
STEP 1: Uninstall Searchgle.com from your Add\Remove Programs
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 2: Delete Searchgle.com from Chrome, Firefox or IE
STEP 3: Permanently Remove Searchgle.com from the windows registry.
STEP 1 : Uninstall Searchgle.com from Your Computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command
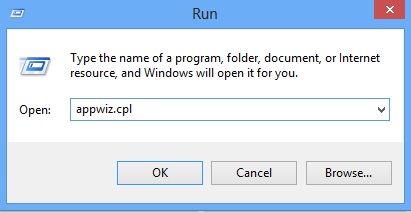
Type “Appwiz.cpl”
Locate the Searchgle.com program and click on uninstall/change. To facilitate the search you can sort the programs by date. review the most recent installed programs first. In general you should remove all unknown programs.
STEP 2 : Remove Searchgle.com from Chrome, Firefox or IE
Remove from Google Chrome
- In the Main Menu, select Tools—> Extensions
- Remove any unknown extension by clicking on the little recycle bin
- If you are not able to delete the extension then navigate to C:\Users\”computer name“\AppData\Local\Google\Chrome\User Data\Default\Extensions\and review the folders one by one.
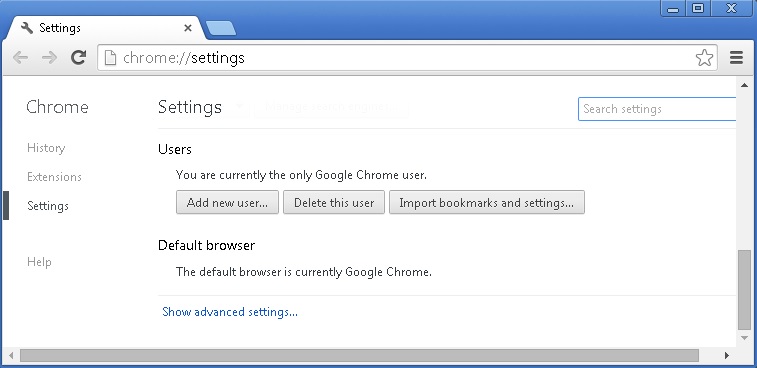
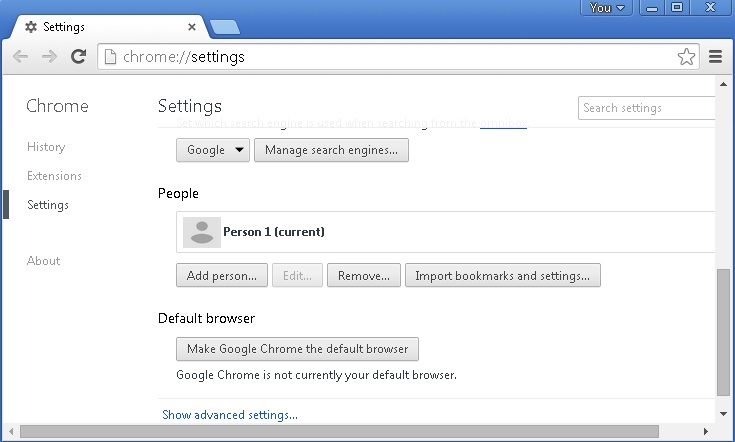
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
- If you are using the latest chrome version you need to do the following
- go to settings – Add person
- choose a preferred name.
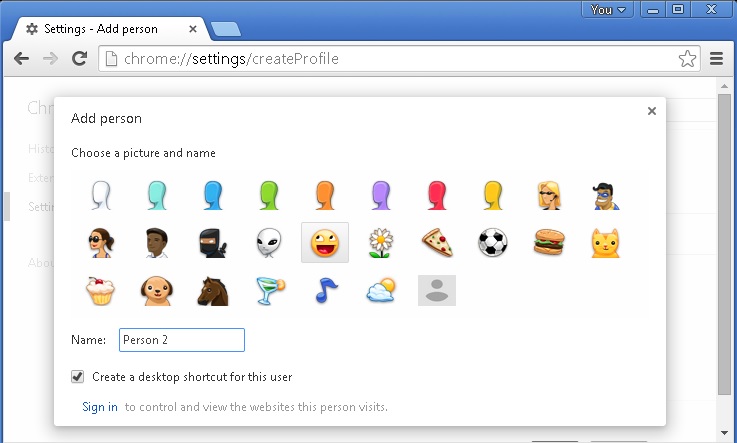
- then go back and remove person 1
- Chrome should be malware free now
Remove from Mozilla Firefox
- Open Firefox
- Press simultaneously Ctrl+Shift+A
- Disable and remove any unknown add on
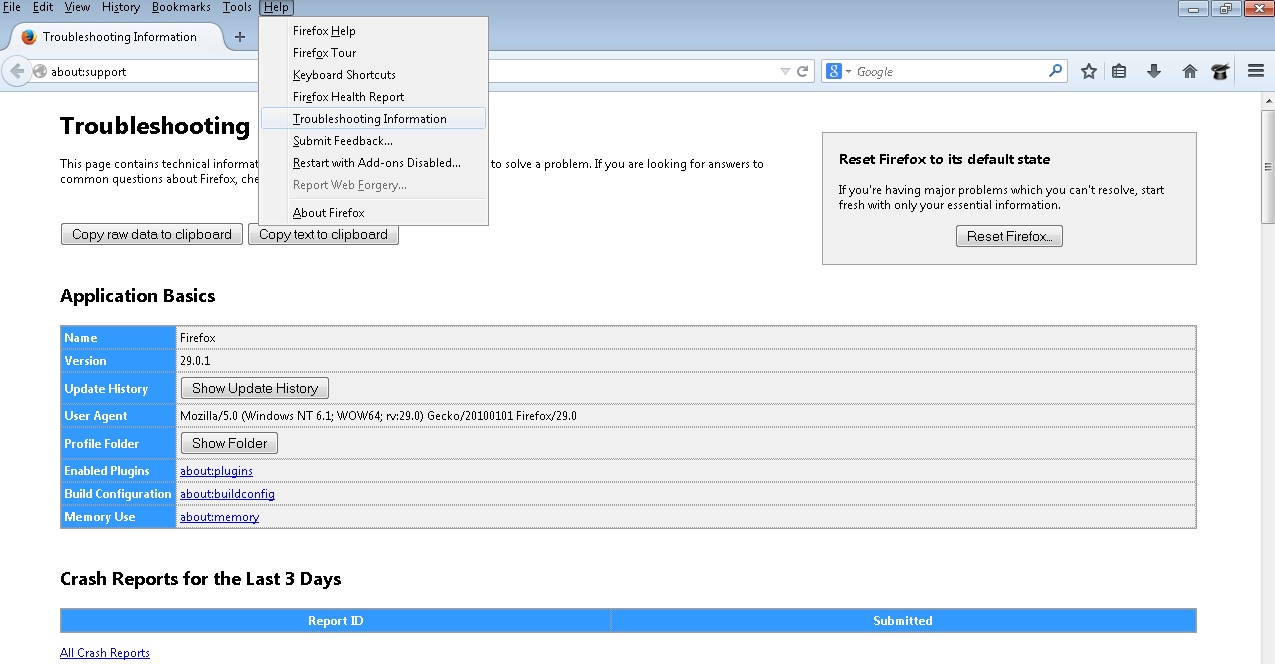
- Open the Firefox’s Help Menu
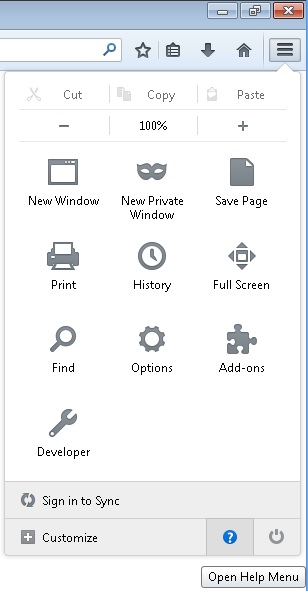
- Then Troubleshoot information
- Click on Reset Firefox
Remove from Internet Explorer
- Open IE
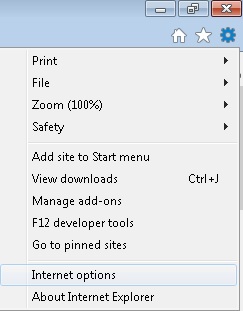
- On the Upper Right Corner Click on the Gear Icon
- Go to Toolbars and Extensions
- Disable any suspicious extension.
- If the disable button is gray, you need to go to your Windows Registry and delete the corresponding CLSID
- On the Upper Right Corner of Internet Explorer Click on the Gear Icon.
- Click on Internet options
- Select the Advanced tab and click on Reset.
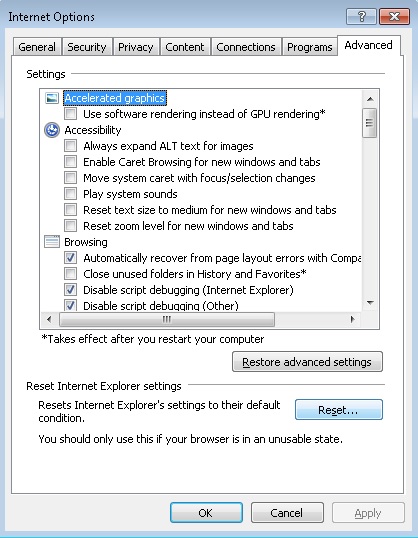
- Check the “Delete Personal Settings Tab” and then Reset
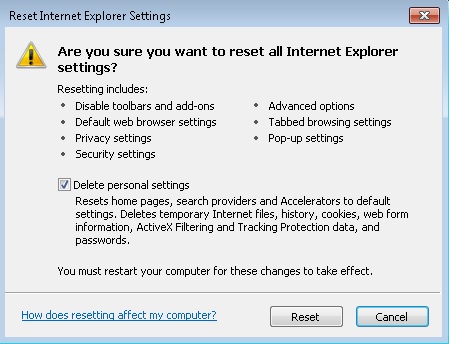
- Close IE
Permanently Remove Searchgle.com Leftovers
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify any registry leftovers or temporary files.