Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Time-to-read.ru took over your homepage and you cannot remove it.
The Time to Read tool is part of the browser hijacker family. And, if it invades your system, brace yourself! Prepare to “enjoy” an entire myriad of inconveniences and grievances. The hijacker throws you into a world of unpleasantness. Its meddling starts with the display of a page. Once the tool settles into your PC, it plagues your browsing with Time-to-read.ru. Think of the site as a front, a face. The hijacker uses it as a shield to conceal its presence. And, at the same time, by displaying the page, reveals itself. The site is its way of announcing its presence. After Time-to-read.ru, comes a variety of other issues. Understand that a hijacker is not a program you want on your system. It wreaks havoc, and makes a mess. The infection causes an avalanche of pop-up ads on your screen. It redirects you to Time-to-read.ru all the time. It implements reshuffles without asking for your consent, or bothering to inform you. And, those are the minor inconveniences! You face worse. The cherry on top is the security risk. The Time to Read tool jeopardizes your private life. It threatens to steal your private information, only to hand it to strangers. People, who then exploit it for their agendas. Ask yourself the following. Are you going to allow that? Are you willing to put your privacy on the line? And, for what? A dangerous, unreliable, harmful hijacker. After Time-to-read.ru takes over your screen, take action. Find the infection’s hiding place, and delete it. ASAP.
How did I get infected with?
If a hijacker is on your computer, it’s because you allowed it there. These programs need your consent before they install themselves. They cannot enter without your approval. They have to ask whether you agree to their admission, or no. And, judging by your predicament, you complied. But how? How do you imagine you consented to install a malicious tool, and not know it? Well, simple. You weren’t aware you were doing it. Hijackers don’t seem approval openly. They do it in the sneakiest way possible. They turn to spam email attachments, corrupted sites, it links. They can even pretend to be fake updates, like Adobe Flash Player or Java. That’s why vigilance is key. If you’re careful, and do your diligence, you might prevent the tool from slithering in. So, don’t rush. Don’t skip the terms and conditions. Don’t just say ‘Yes’ to everything. Instead of relying in chance, rely on vigilance. Don’t underestimate attentiveness. It goes a long way.
Why is this dangerous?
After the hijacker invades your system, its mess-making begins. It takes over your preferred homepage and search engine. And, all if a sudden, you find it as Time-to-read.ru. You weren’t asked to approve the change, and you weren’t informed about it. That’s how hijackers work. Once they’re in, they can perform changes. And, they don’t have to seek your permission. They just spring them on you. As a surprise. And, what a surprise it would be to turn on your PC, and find it brimming with malware. Yes, that can happen. It’s a valid possibility. And, what do you think happens after your system gets flooded with malicious infections? Well, one possible scenario is the dreaded blue. You can face The Blue Screen of Death. Yes, it’s a rather minuscule one, but it’s there. It exists! So, why take the chance, albeit an insignificant one? And, what about the security risk, mentioned above? Are you prepared to take that chance, as well? Will you let the hijacker steal your private data, and hand it to strangers? Because it will. Make no mistake. Hijackers, like Time to Read, are designed that way. They keep track of your browsing, and catalog your every online move. When they have enough, they hand it to the people that published them. Don’t let these people into your private life! Protect your personal and financial information! Find and delete the hijacker on your computer. Do it as soon as it reveals itself with Time-to-read.ru. Don’t waste time. The more time you waste, the worse your situation gets.
How to Remove Time-to-read.ru virus
If you perform exactly the steps below you should be able to remove the Time-to-read.ru infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Time-to-read.ru adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Time-to-read.ru from Add\Remove Programs
STEP 2: Clean Time-to-read.ru from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Time-to-read.ru leftovers from the System
STEP 1 : Uninstall Time-to-read.ru from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
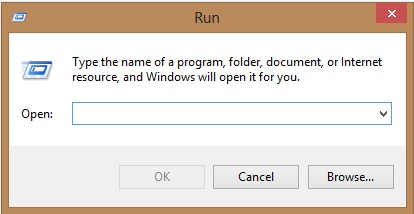
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Time-to-read.ru homepage from Chrome, Firefox and IE
-
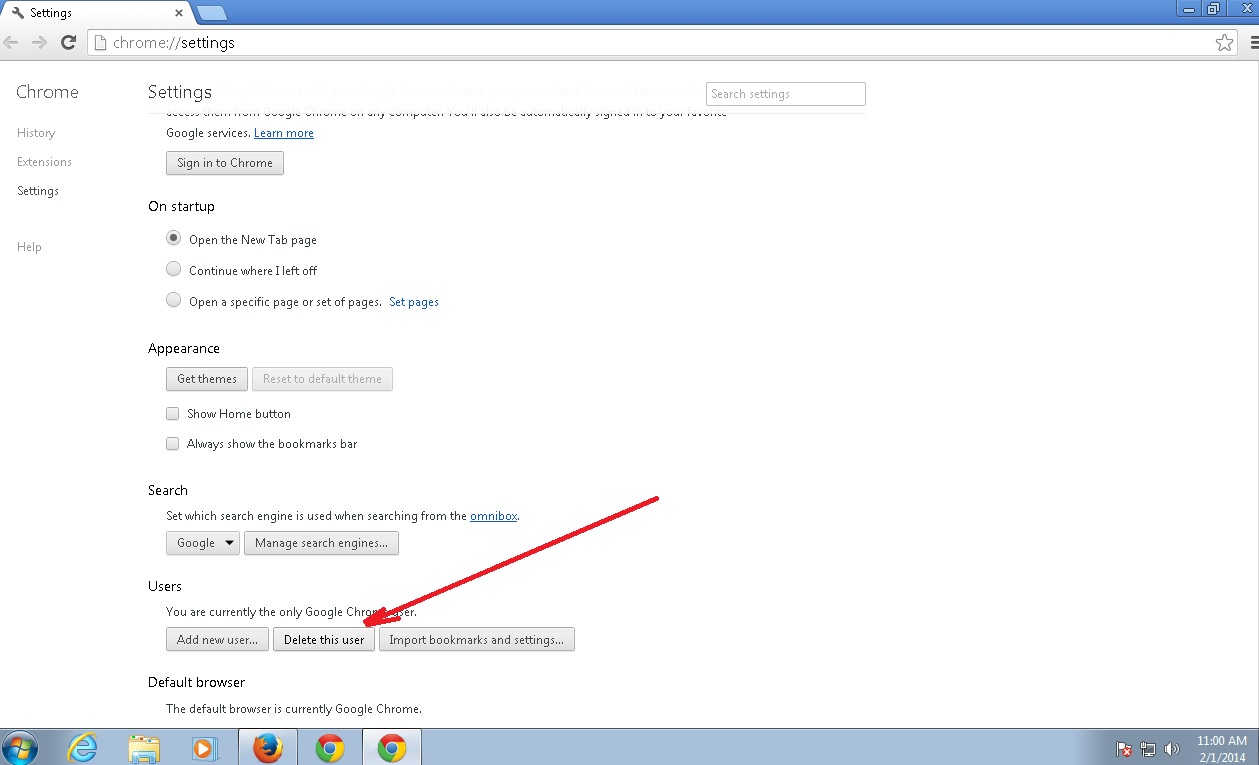
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Time-to-read.ru by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
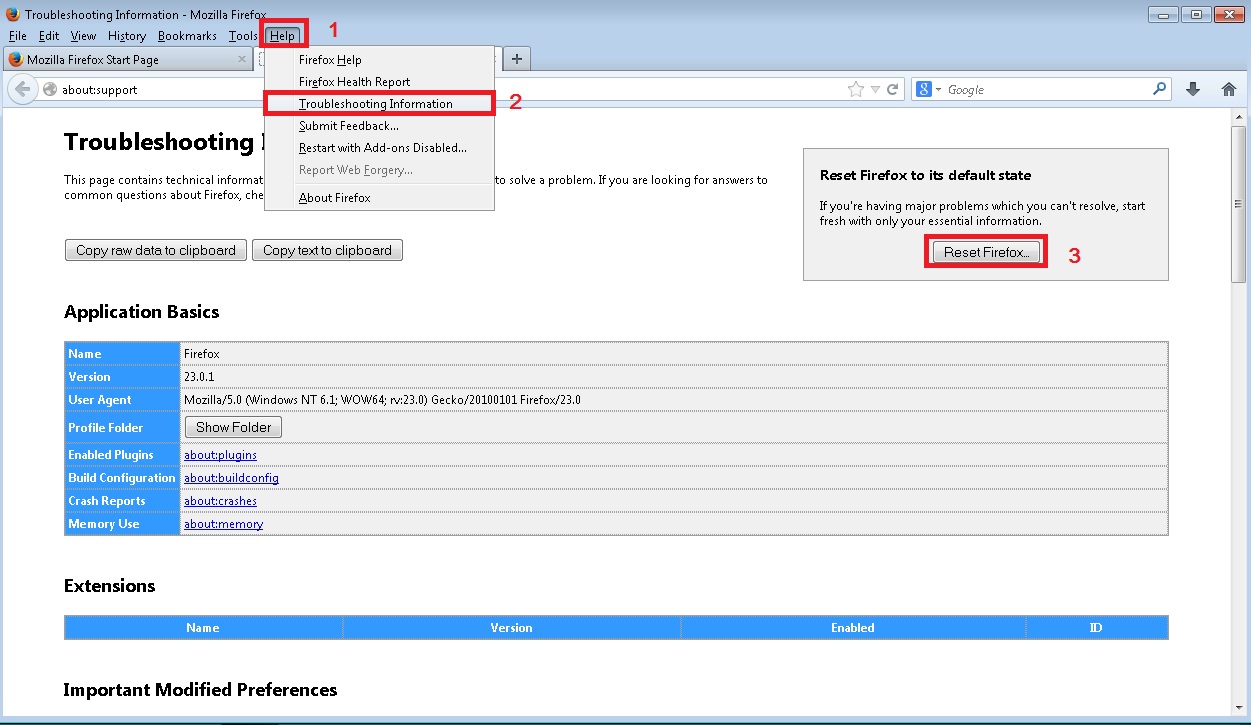
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
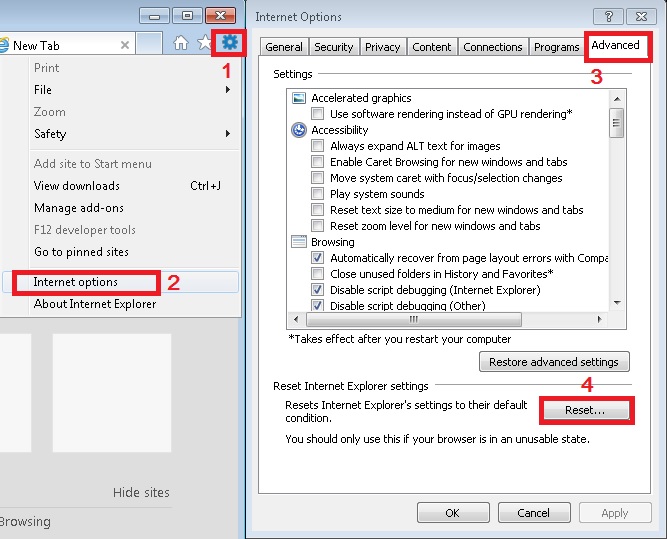
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove Time-to-read.ru Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.