Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Serpent Ransomware?
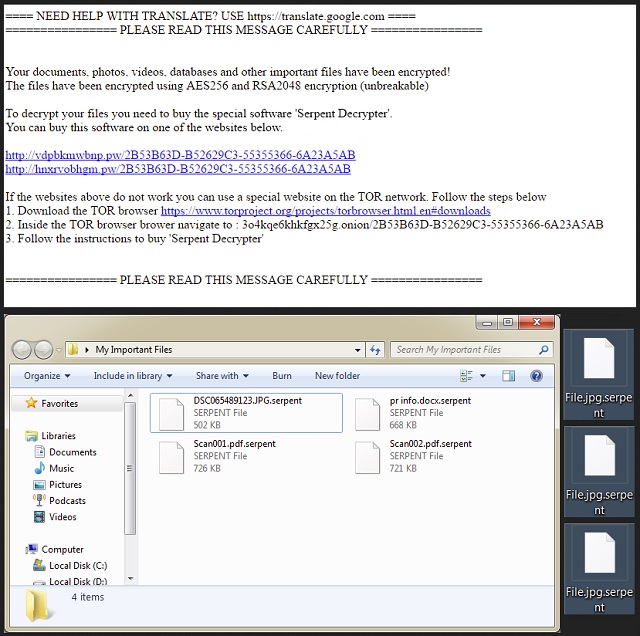
Readers recently started to report the following message being displayed when they boot their computer:
==== NEED HELP WITH TRANSLATE? USE https://translate.google.com ====
================ PLEASE READ THIS MESSAGE CAREFULLY ================
Your documents, photos, videos, databases and other important files have been encrypted!
The files have been encrypted using AES256 and RSA2048 encryption (unbreakable)
To decrypt your files you need to buy the special software ‘Serpent Decrypter’.
You can buy this software on one of the websites below.
hxxp://vdpbkmwbnp.pw/
hxxp://hnxrvobhgm.pw/
If the websites above do not work you can use a special website on the TOR network. Follow the steps below
1. Download the TOR browser https://www.torproject.org/projects/torbrowser.html.en#downloads
2. Inside the TOR browser brower navigate to : 3o4kqe6khkfgx25g.onion/
3. Follow the instructions to buy ‘Serpent Decrypter’
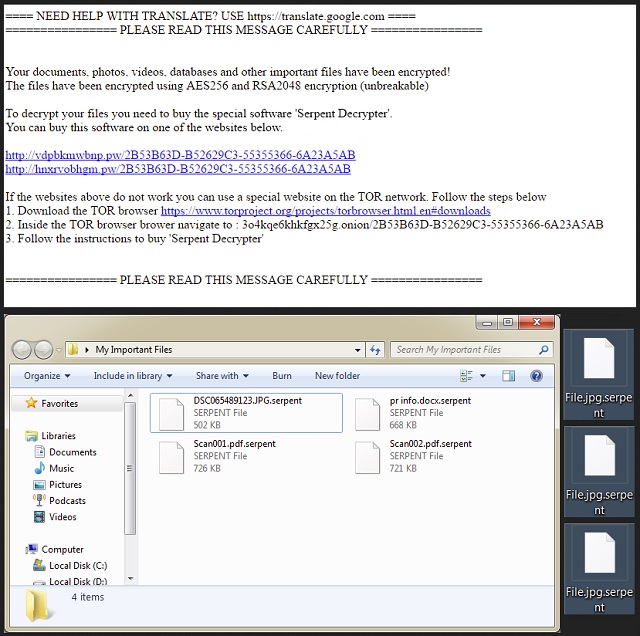
================ PLEASE READ THIS MESSAGE CAREFULLY ================
Serpent is a Danish ransomware-type infection. It’s actually quite similar to the Hades Locker parasite which we’ve already tackled. It also shows similarities with WildFire and Zyklon. Researchers stumbled across Serpent just a couple of days ago. It fully justifies the name that hackers chose to give the virus. This program also strictly follows the classic ransomware pattern. It slithers itself onto your machine completely behind your back. Obviously, hackers aren’t going to seek your permission to download ransomware. Would you agree to install the most vicious, aggressive and harmful type of virus? No? Then Serpent must have applied some sneaky technique to land on your PC. You will learn more about its infiltration methods if you keep on reading. As soon as the virus gets to you, it starts scanning your machine. This way, the ransomware locates your private files. We’re talking photos/pictures, videos, music, MS Office documents, etc. Now that Serpent has found your information, encryption begins. It’s safe to say this is the most unpleasant part of the whole scheme. Serpent Ransomware uses the RSA-2048 and AES-256 algorithm. As a result, it effectively locks all your files. Do you keen valuable information on your machine? Many people do. Unfortunately, not all of them have backups of their files. That makes such PC users perfect targets for ransomware. You see, these infections are nothing but clever attempts for a fraud. They encrypt your data only to trick you into paying for a decryptor. The parasite you’re stuck with right now adds a .serpent extension to your data. For instance, MyFavoriteSong.mp3 gets renamed to MyFavoriteSong.mp3.serpent. Seeing this appendix pretty much means it’s game over. The parasite denies you access to your very own files stored on your very own computer. As if that wasn’t nasty enough, Serpent also demands payment. This is what ransomware is all about – helping hackers gain illegitimate profit. As mentioned, crooks rely on the fact you would panic. While the virus is locking your data, it drops two files named HOW_TO_DECRYPT_YOUR_FILES_Dn6.txt and HOW_TO_DECRYPT_YOUR_FILES_Dn6.html. Those are your detailed payment instructions. Yes, you have to pay in order to view and use your encrypted files. It goes without saying how unfair that is. Serpent Ransomware adds its ransom notes to all folders that contain locked data. The parasite modifies your wallpaper too. To prevent getting scammed, don’t even consider paying.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How did I get infected with?
To determine how the ransomware got installed isn’t easy. Infections have a huge variety of techniques to choose from. However, there are a couple of especially popular methods. Number one technique involves spam email-attachments. This is also one of the oldest tricks out there. Do you often receive questionable emails or messages in social media? Unless you personally know the sender, stay away from them. You could never be sure that such a message/email is harmless. Put your safety and privacy first and don’t rush. Avoid illegitimate websites and torrents too. Ransomware is an extremely tricky kind of infection. It uses deceit to travel the Web so you only need one moment of haste to compromise your PC. Having to delete a virus, on the other hand, is a lot more time-consuming. You can now see for yourself how dreaded ransomware is. Make sure hackers never successfully cause you a headache. The virus could have also gotten installed with some help from a Trojan. That means you may have more infections on your computer system as well. Check out the device and don’t overlook any potential threat. There’s no such thing as being too cautious online.
Why is Serpent dangerous?
The virus demands money from you. According to its devious ransom messages, you will eventually receive a decryption key. You’d be making a deal with hackers, though. To say the least, they aren’t the most trustworthy people out there. Serpent’s decryptor will cost you 0.75 Bitcoins which equals 959 USD at the moment. If you don’t make the payment in the next week, the sum rises to 2.25 Bitcoins. That equals the impressive 2878 USD. Furthermore, paying guarantees you nothing. You could comply right away and still remain unable to free your encrypted data. Do not let this infection involve you in a cyber fraud and scam you. Delete the virus instead. You will follow our comprehensive manual removal guide down below.
Serpent Removal Instructions
STEP 1: Kill the Malicious Process
STEP 3: Locate Startup Location
STEP 4: Recover Serpent Encrypted Files
STEP 1: Stop the malicious process using Windows Task Manager
- Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
- Locate the process of the ransomware. Have in mind that this is usually a random generated file.
- Before you kill the process, type the name on a text document for later reference.

- Locate any suspicious processes associated with Serpent encryption Virus.
- Right click on the process
- Open File Location
- End Process
- Delete the directories with the suspicious files.
- Have in mind that the process can be hiding and very difficult to detect
STEP 2: Reveal Hidden Files
- Open any folder
- Click on “Organize” button
- Choose “Folder and Search Options”
- Select the “View” tab
- Select “Show hidden files and folders” option
- Uncheck “Hide protected operating system files”
- Click “Apply” and “OK” button
STEP 3: Locate Serpent encryption Virus startup location
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type “Regedit”
- WARNING! be very careful when editing the Microsoft Windows Registry as this may render the system broken.
Depending on your OS (x86 or x64) navigate to:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] or
[HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Windows\CurrentVersion\Run]
- and delete the display Name: [RANDOM]

- Then open your explorer and navigate to:
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you should run any professional scanner to identify malicious files.
STEP 4: How to recover encrypted files?
- Method 1: The first and best method is to restore your data from a recent backup, in case that you have one.

- Method 2: File Recovery Software – Usually when the ransomware encrypts a file it first makes a copy of it, encrypts the copy, and then deletes the original. Due to this you may try to use file recovery software to recover some of your original files.
- Method 3: Shadow Volume Copies – As a last resort, you can try to restore your files via Shadow Volume Copies. Open the Shadow Explorer part of the package and choose the Drive you want to recover. Right click on any file you want to restore and click Export on it.