Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Search.siviewer.com took over your homepage and you cannot remove it.
Search.siviewer.com is a malicious page, which acts like a big, bright neon sign of the presence of a cyber threat on your computer. If you come across it, you’re in trouble as a browser hijacker has managed to slither its way in, and call your PC ‘home.’ The SIViewer tool is malicious, invasive, and highly damaging. It sneaks into your system undetected, and once it settles, proceeds to wreak havoc. It begins by taking over your screen completely. One day, you’ll find your homepage and default search engine have been replaced with Search.siviewer.com, but you had no say in the matter. And, that’s one of the worst aspects of getting stuck with a hijacker – it can implement changes without having to ask permission or inform you. For example, the nasty application can choose to open the door to countless malevolent programs, and you won’t even realize it until issues start popping up. How long do you believe your system’s well-being will survive under constant fire of malware? It will hardly take long before The Blue Screen of Death makes its appearance. But don’t think your problems will end there. Hijackers cause troubles for as long as they’re left to remain on your computer. That means that the longer you extend their stay, the more time, and opportunities they have to make a mess. Make no mistake! They’ll take each and one of them. So, do yourself a favor, and don’t permit the pesky SIViewer to stay even a second after detection. Take the Search.siviewer.com site as the warning, which it is, and act on it immediately. It’s for the best, and you won’t regret it.
How did I get infected with?
For Search.siviewer.com to take over, you have to permit the installation of the hijacker, which is using it as a front. Yes, you have to consent to its install. The tool is required to ask whether you agree to let it in or not, and if you deny it – no admittance. But seeing it as how you’re currently plagued by it, it’s safe to assume that you complied. Tools like the one you’re faced with are crafty. They resort to guile and finesse and fool you into permitting them in while keeping you oblivious to it. More often than not they turn to the old but gold means of infiltration. That includes hiding behind spam email attachments, freeware, corrupted sites or links. They can also pose as updates. For example, you may think you’re updating your Adobe Flash Player but, in reality, you’ll be installing the SIViewer tool. If you wish to prevent the application from entering, be more cautious. Don’t rush and don’t give into naivety and haste. After all, even a little extra attention goes a long, long way.
Why is this dangerous?
Search.siviewer.com will quickly become the bane of your browsing. Once the hijacker slithers into your system, its mess-making begins! At first, it’s manifested in its continuous meddling. It switches your homepage and search engine to Search.siviewer.com, and every chance you grant it, it WILL redirect you to the pesky page. So, every time you go online, you’ll see the site. But not just that. The website will be accompanied by an endless stream of pop-up advertisements. And, it won’t take long before the steady, constant appearance of the advertisements and the redirects leads to more damages. Due to the continuous disruption cause, your system will start to crash frequently, and your computer’s performance will slow down to a crawl. But the absolute worst part of having such a nasty cyber threat lurk on your PC is how it places your privacy at severe risk. The malicious program is designed to spy on you from the moment it enters your system. The tool keeps track of your browsing activities and catalogs you every online move. Then, after it determines it has gathered enough information, it sends it to the unknown third parties that support it. That means strangers will have access to your private data. The question is, are you going to allow it? Are you willing to place your personal and financial details into the hands of people you don’t know with most likely wicked intentions? Here’s a hint: don’t! Protect yourself and your system, and don’t let the hijacker remain on your computer long enough for it to cause you such grievances and headaches. As soon as it throws the Search.siviewer.com page your way, locate where the hijacker, which is using it as a shield to hide behind, is lurking. And, when you do find it – delete it! The sooner, the better.
How to Remove Search.siviewer.com virus
If you perform exactly the steps below you should be able to remove the Search.siviewer.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Search.siviewer.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Search.siviewer.com from Add\Remove Programs
STEP 2: Clean Search.siviewer.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Search.siviewer.com leftovers from the System
STEP 1 : Uninstall Search.siviewer.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
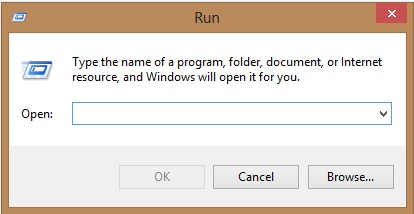
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Search.siviewer.com homepage from Chrome, Firefox and IE
-
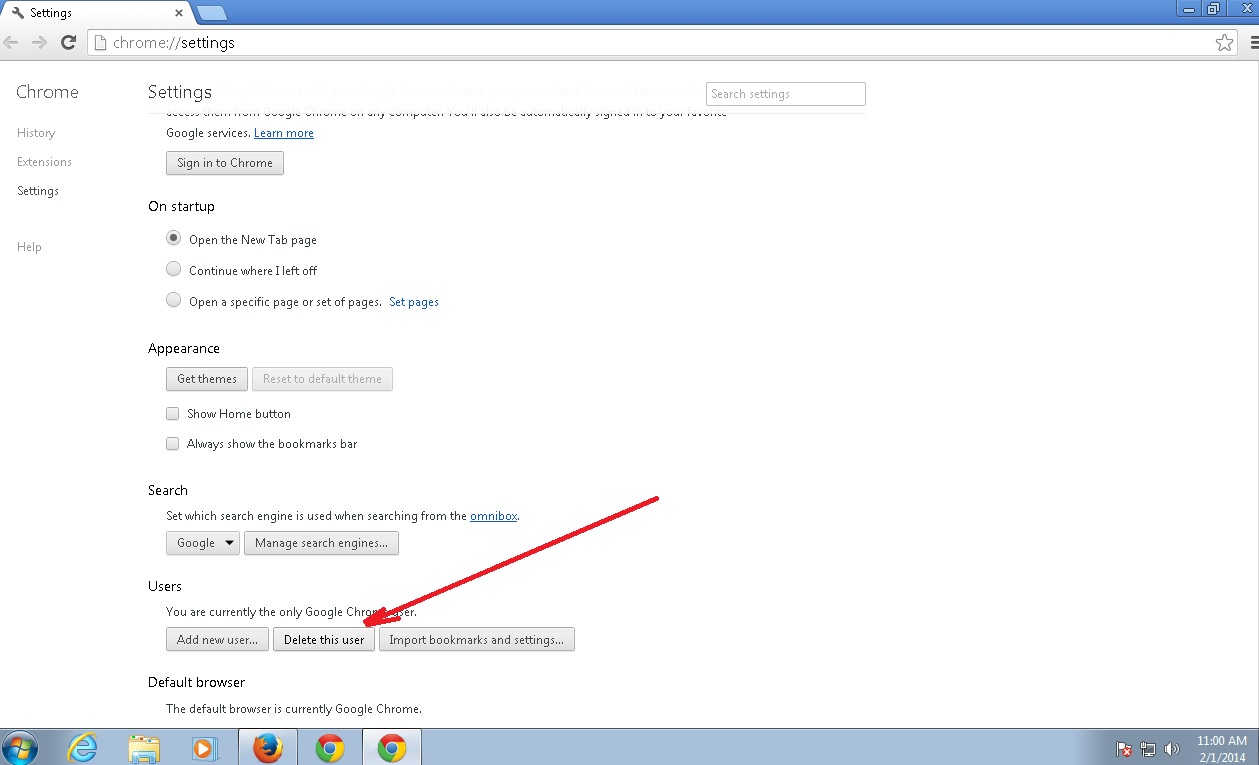
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Search.siviewer.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
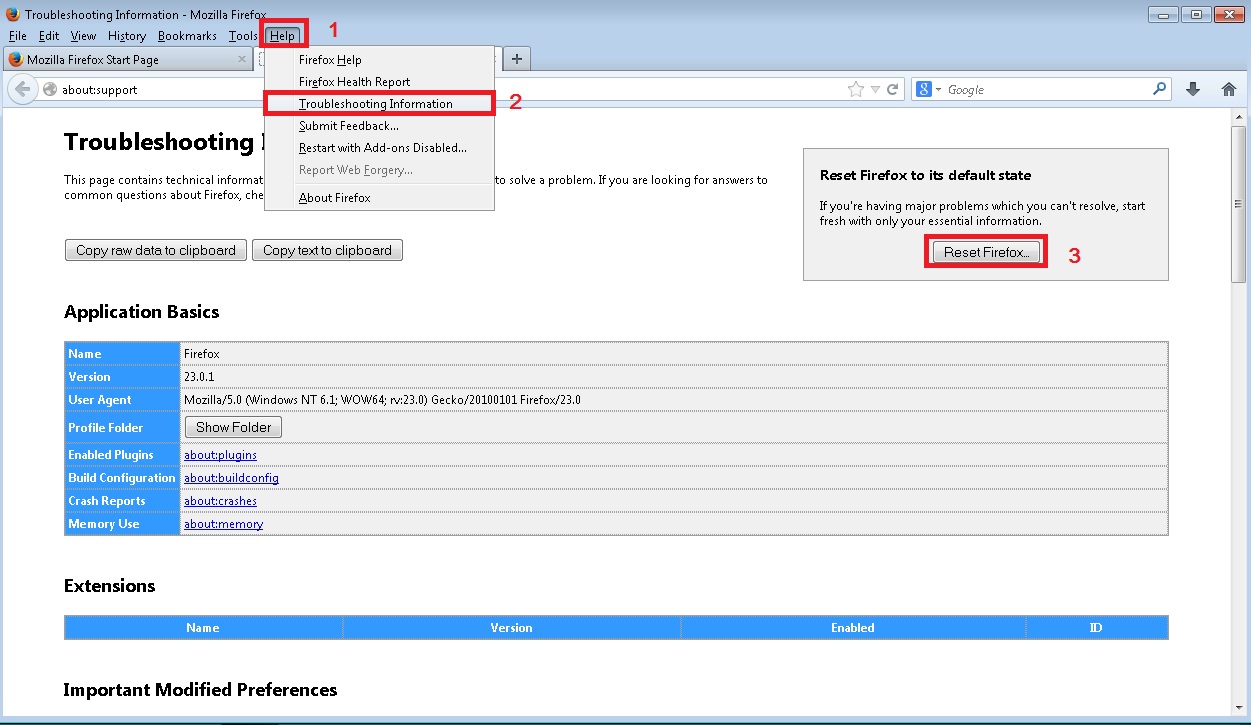
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
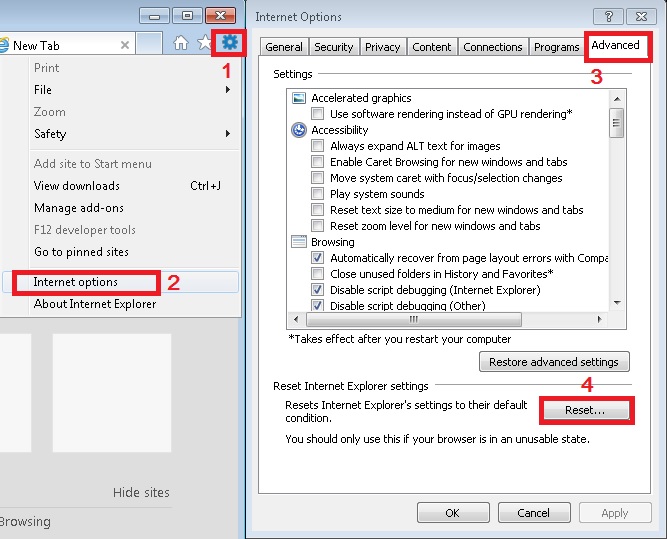
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove Search.siviewer.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.