Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Can’t Remove Noreply@security.biz Malware pop-ups?
If Noreply@security.biz bombards you with emails, don’t panic. This email address is linked to a new sextortion scam campaign. Its scheme is quite simple. The cooks pretend to be hackers who have infected your computer with a Trojan. They claim that their virus has managed to copy your contact list, to steal your passwords, as well as to record a compromising video of you during private moments. The scammers threaten to leak the video and ruin your reputation if you don’t pay an astonishing ransom in Bitcoin. Their emails seem especially threatening as they often mention passwords that you’ve used in the past. Again, don’t panic! The noreply@security.biz scam email is just a text composed by crafty criminals. The scammers buy leaked login credential, as well as employ scamware to flood the web with their hoax messages. These people have no virus, much less a compromising video of you. They take advantage of common misconceptions and prey on your naivety. Don’t fall for their tricks! Recognize the noreply@security.biz email for what it is – a warning of how dangerous the web can be. Employ a strong password policy and keep your software up to date.

How did I get infected with?
Scamware is usually the cause of the noreply@security.biz emails. These parasites sneak into your computer and lure you into sharing your contact details, as well as flood you with deceptive content. Do not mistake the scamware for viruses, though. These parasites are simple apps that have standard limitations. They rely on trickery to lure you into unwanted actions. Even their infiltration process is dependent on their deceptive abilities. The thing about scamware is that these parasites can’t get installed without your (the user’s) approval. No permission no admission! The parasites, of course, know how to steal your “yes.” They do so through bundles, fake updates, corrupted links, and pirated software. The parasites lurk in the fine print and infect your computer when you let your guard down. Don’t make that mistake! No anti-virus app can protect you if you throw caution to the wind. The key to a secure and infection-free computer is diligence. Only your actions can prevent infections. The good news is that even a little extra attention goes a long way. So, don’t be lazy. Make the right decision – choose caution over carelessness. Don’t visit shady websites. Download software from reliable sources only. And, of course, don’t skip installation steps. Forget about the “Next-Next-Finish” setup strategy. Opt for the advanced/custom installation option. Deselect the bonus apps and go through the terms and conditions. Don’t hesitate to abort the installation process if you notice anything suspicious!
Why are these ads dangerous?
The noreply@security.biz scam is a nightmare. Its emails pop up out of the blue and ruin your day. They are threatening and highly alarming. If you, however, take a closer look at the emails, you’ll realize that they are full of lies. Note that the messages don’t mention your real name nor your username. They don’t specify which website infected your computer. And most importantly, they don’t provide proof of the video’s existence. You are dealing with manipulators. Don’t sponsor their criminal activities! Bear in mind that the Bitcoin currency is untraceable. Once you complete a transaction, no one can help you get your money back. So, don’t make mistakes. Don’t pay the ransom! You’ll only waste your time and money. Delete the scam emails! If you suspect that scamware or other malware lurks in the shadows of your OS, run a virus scan. Let your anti-virus app fix the detected issues and move on. Don’t let the noreply@security.biz scam email ruin your day!
How Can I Remove Noreply@security.biz Malware Pop-ups?
If you perform exactly the steps below you should be able to remove the infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
STEP 1: Uninstall suspicious software from your Add\Remove Programs
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 2: Delete unknown add-ons from Chrome, Firefox or IE
STEP 3: Permanently Remove Noreply@security.biz Malware from the windows registry.
STEP 1 : Uninstall unknown programs from Your Computer
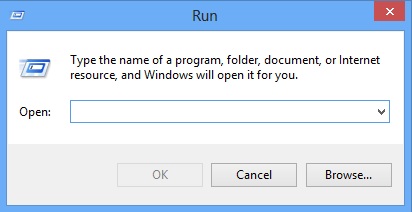
Simultaneously press the Windows Logo Button and then “R” to open the Run Command
Type “Appwiz.cpl”
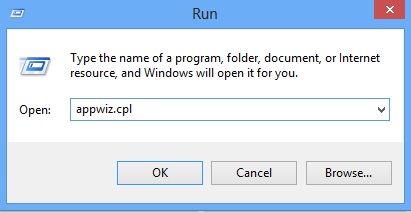
Locate the any unknown program and click on uninstall/change. To facilitate the search you can sort the programs by date. review the most recent installed programs first. In general you should remove all unknown programs.
STEP 2 : Remove add-ons and extensions from Chrome, Firefox or IE
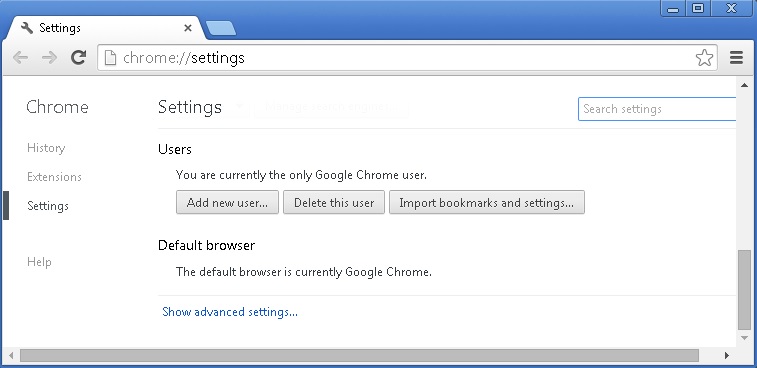
Remove from Google Chrome
- In the Main Menu, select Tools—> Extensions
- Remove any unknown extension by clicking on the little recycle bin
- If you are not able to delete the extension then navigate to C:\Users\”computer name“\AppData\Local\Google\Chrome\User Data\Default\Extensions\and review the folders one by one.
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
- If you are using the latest chrome version you need to do the following
- go to settings – Add person
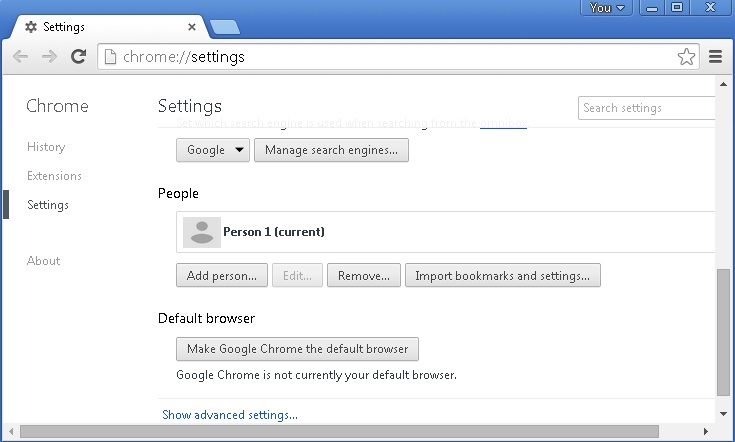
- choose a preferred name.
- then go back and remove person 1
- Chrome should be malware free now
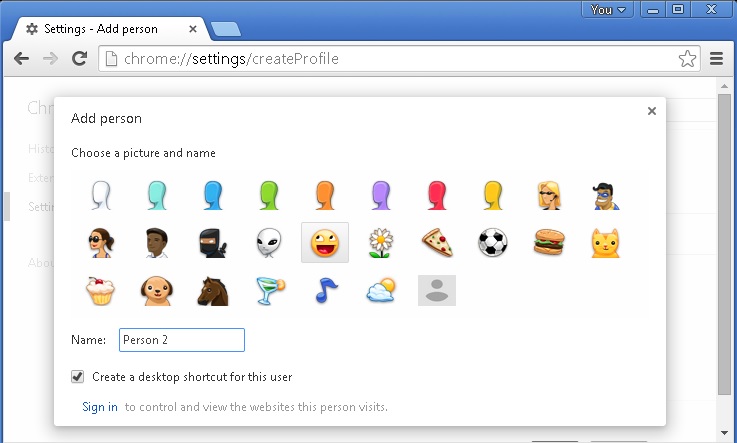
Remove from Mozilla Firefox
- Open Firefox
- Press simultaneously Ctrl+Shift+A
- Disable and remove any unknown add on
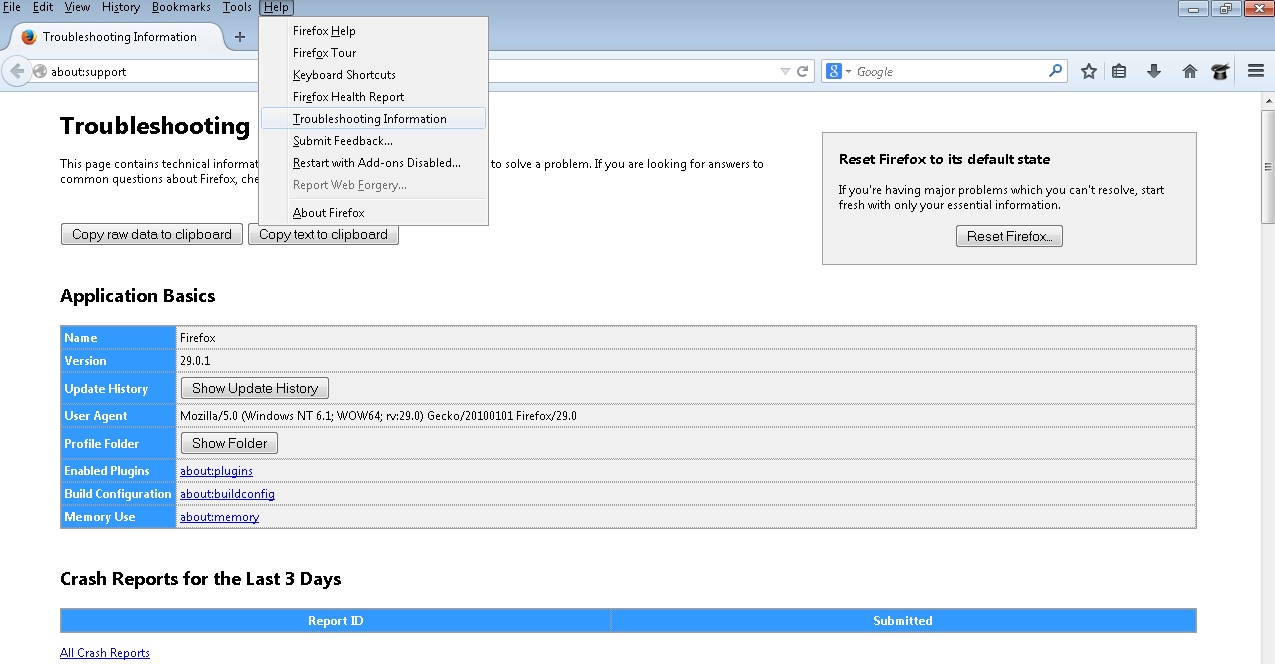
- Open the Firefox’s Help Menu
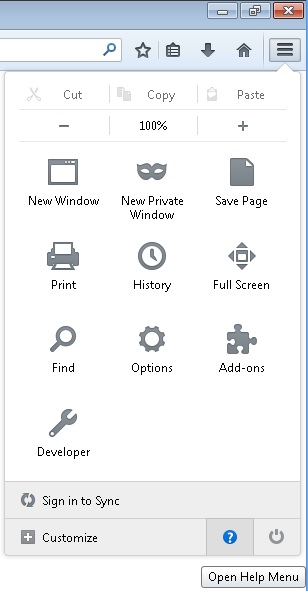
- Then Troubleshoot information
- Click on Reset Firefox
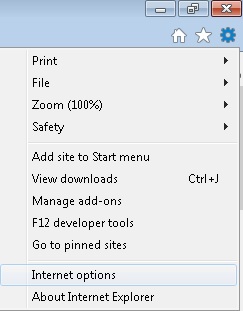
Remove from Internet Explorer
- Open IE
- On the Upper Right Corner Click on the Gear Icon
- Go to Toolbars and Extensions
- Disable any suspicious extension.
- If the disable button is gray, you need to go to your Windows Registry and delete the corresponding CLSID
- On the Upper Right Corner of Internet Explorer Click on the Gear Icon.
- Click on Internet options
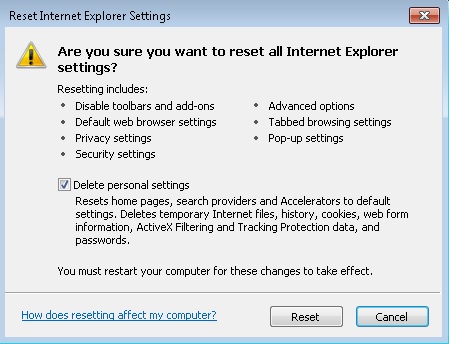
- Select the Advanced tab and click on Reset.
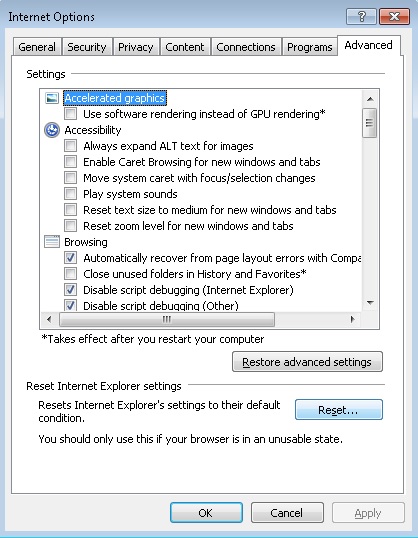
- Check the “Delete Personal Settings Tab” and then Reset
- Close IE
Permanently Remove Noreply@security.biz Malware Leftovers
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify any registry leftovers or temporary files.