Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Lupny.com took over your homepage and you cannot remove it.
The Internet is full of irritating browser hijackers. And, unfortunately, you’ve fallen victim to one of them. Lupny.com is the nth pesky hijacker that’s been roaming the Web lately. It’s a relatively new infection. However, it’s already proved itself to be quite a nuisance. Hijackers mess with your default browser settings. This way, they manage to take complete control over your online experience. What did Lupny.com promise to do? Provide accurate, safe search results. The thing is, Lupny.com does none of that. Behind its beautiful and empty pledges, lies a sneaky, dangerous infection. Hackers aren’t famous for being honorable people. It comes as no surprise they constantly lie about this program’s functionalities. The parasite’s trickery starts immediately after installation. To begin with, Lupny.com forces its dubious search engine on you. Did you notice that both your default search engine and browser homepage are modified? They are now replaced with the hijacker’s own domain. Now, there are several malicious traits this domain exhibits. The only web links it generates are sponsored. By displaying sponsored links, Lupny.com actually helps its developers make money. Easy illegitimate profit – that’s what hijackers are all about. This particular infection doesn’t deviate from the rules. It generates web traffic to some websites so crooks could gain profit. Hackers take advantage of the pay-per-click mechanism. Eventually, they gain revenue at your expense. Instead of harmless search results, you’re now bombarded with dangerous links. You see, a sponsored link could take you to all sorts of pages – safe or not. Does that seem like a risk worth taking? It isn’t. One single careless click could bring upon you serious, irreversible harm. Make no mistake. Stay away from anything Lupny.com generates and be cautious. Remember, you’re dealing with a pesky parasite. There’s simply no plausible scenario in which your safety doesn’t end up jeopardized. In addition, the virus redirects you. It also slows down the PC speed and may cause your browsers to freeze/crash. Surfing the Internet becomes less and less of a fun activity, doesn’t it? To top it all, the hijacker exposes your private information. Yes, a virus collects all your browsing-related data. As a result, you may experience financial frauds and even identity theft. To learn how you could uninstall this pest for good, keep on reading.
How did I get infected with?
You didn’t download a virus on purpose, did you? As you probably know already, hijackers travel the Web in silence. They don’t ask for your active cooperation. No, they rely on your haste online instead. Do you now realize how easy it is to compromise your machine with all kinds of malware imaginable? Infections have a rich variety of infiltration techniques to choose from. For example, they often get attached to spam messages/emails. Next time you spot something suspicious in your inbox, don’t rush to click it open. It might turn out to be a secretive infection such as a Trojan horse. Or, if you’re unlucky enough, ransomware. Delete what you don’t trust and don’t be negligent. Also, stay away from unverified freeware bundles. They could include some nasty “bonus” program that needs to be deselected. To do so, though, you have to spot it first. We recommend opting for the Advanced or Custom option in the Setup Wizard. This way you will remain in control of the entire installation process. Don’t risk your security and don’t be careless online.
Why is this dangerous?
The Lupny.com Virus gets out of hand very quickly. In order to prevent that, you have to tackle this pest as soon as possible. Due to its shenanigans, all your browsers are no longer trustworthy. They have been hijacked. Lupny.com’s extension is compatible with all the most popular browsers on the Internet. It goes without saying Mozilla Firefox, Google Chrome and Internet Explorer are infected. They all generate unreliable, unsafe web links on a daily basis. Furthermore, they present these sponsored links as harmless search results. There’s nothing harmless about hijackers, though. This program might also generate various pop-ups in various shapes. You could stumble across fake software updates as well. As mentioned, your private information gets sent into the wrong hands too. All your IP addresses, email addresses, browsing history, passwords, etc. All of it is now being spied on. Hackers may sell your data to third parties with unclear intentions and cause trouble. To delete Lupny.com manually, please follow our detailed removal guide down below.
How to Remove Lupny.com virus
If you perform exactly the steps below you should be able to remove the Lupny.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Lupny.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Lupny.com from Add\Remove Programs
STEP 2: Clean Lupny.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Lupny.com leftovers from the System
STEP 1 : Uninstall Lupny.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
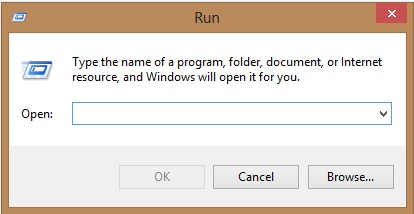
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Lupny.com homepage from Chrome, Firefox and IE
-
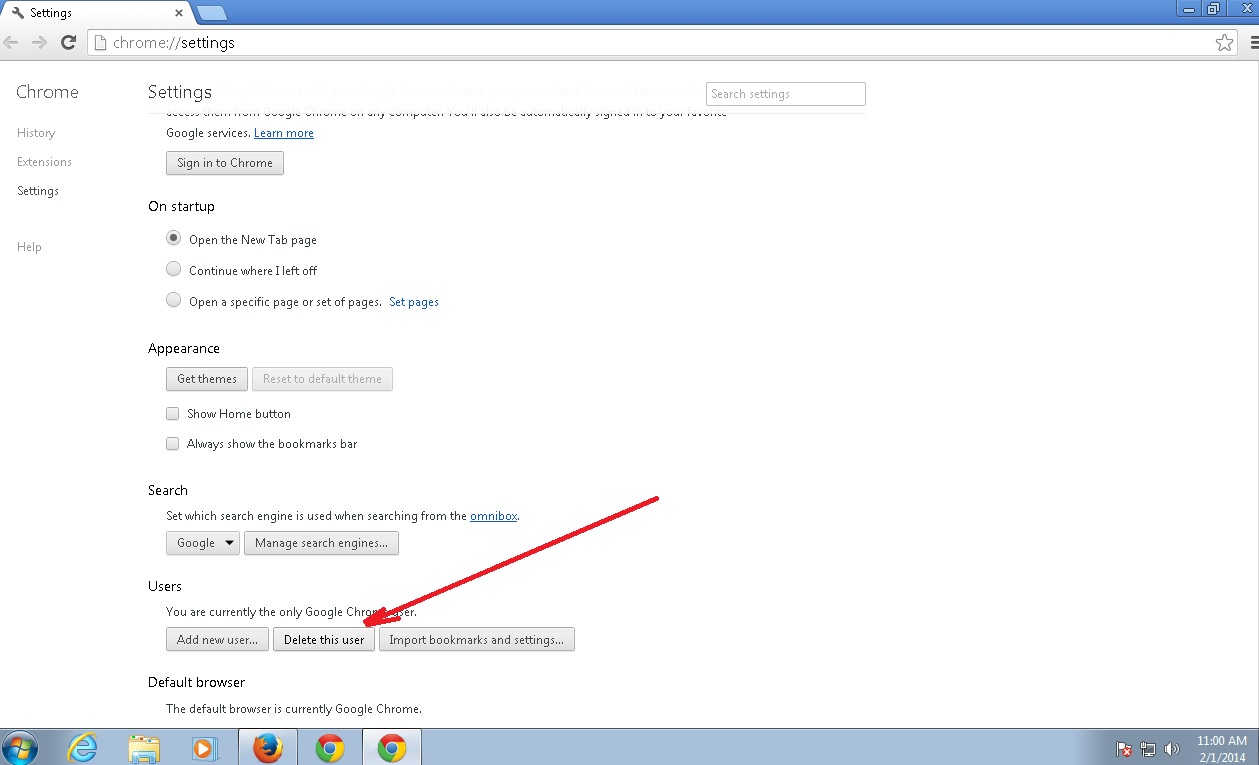
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Lupny.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
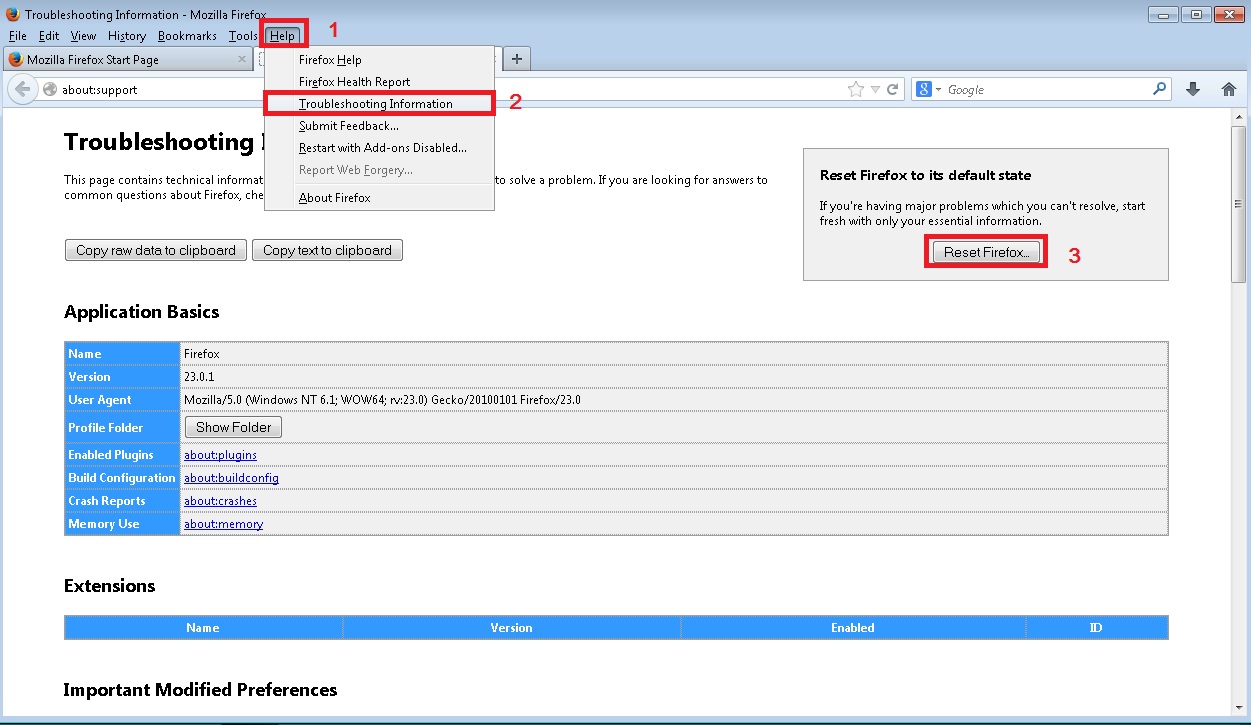
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
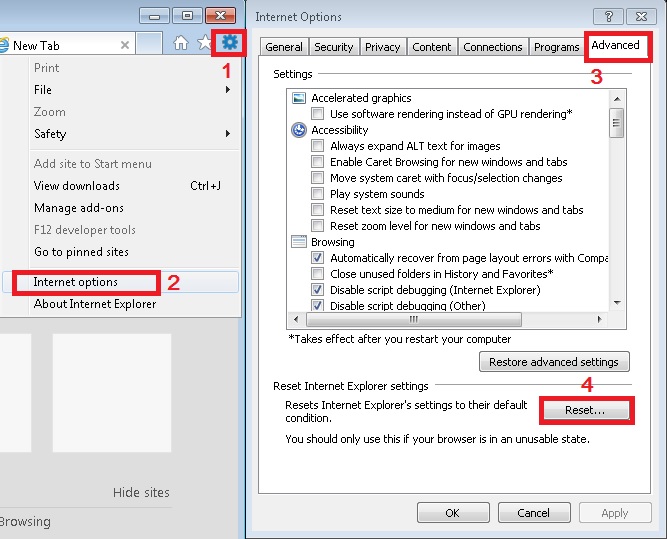
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
Make sure your Windows HOSTS file is clean
- open your explorer and Navigate to %windir%/system32/Drivers/etc/host
If you are hacked, there will be foreign IPs addresses connected to you at the bottom. Take a look below:

You need to remove the poisoned IPs and save the HOSTS file.
Check your internet connection settings
- Right-click on the active Network Adapter, Click on Properties
- Navigate to Internet Protocol Version 4 (ICP/IP), click Properties.
- Click on Advanced and then navigate to the DNS TAB. The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
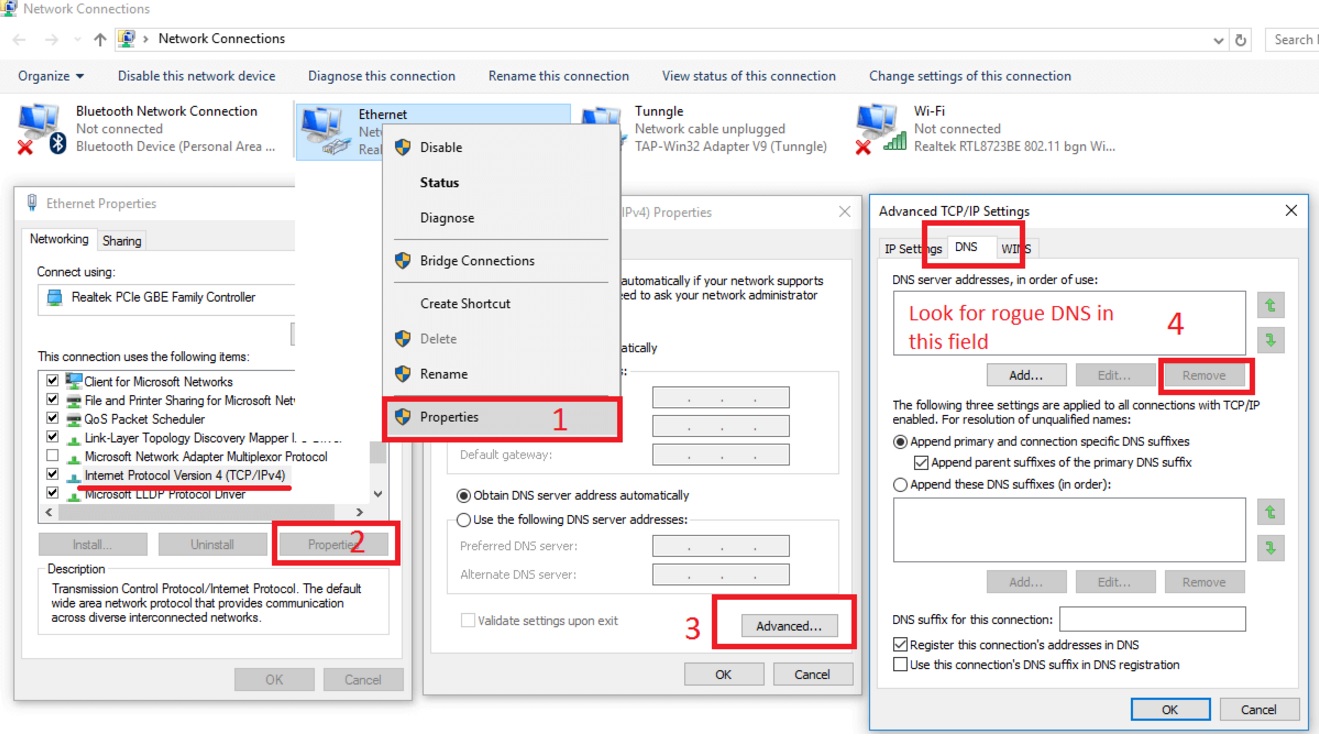
Double check your proxy settings as the malware is capable of modifying them.
Attention! this can break your internet connection. Before you change your DNS settings to use Google Public DNS for example, be sure to write down the current server addresses on a piece of paper.
To fix the damage done by the virus you need to do the following.
- Click the Windows Start button to open the Start Menu, type control panel in the search box and select Control Panel in the results displayed above.
- go to Network and Internet
- then Network and Sharing Center
- then Change Adapter Settings
- Right-click on your active internet connection and click properties. Under the Networking tab, find Internet Protocol Version 4 (TCP/IPv4). Left click on it and then click on properties. Both options should be automatic! By default it should be set to “Obtain an IP address automatically” and the second one to “Obtain DNS server address automatically!” If they are not just change them, however if you are part of a domain network you should contact your Domain Administrator to set these settings, otherwise the internet connection will break!!!
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware tool to identify possible registry leftovers or temporary files.