Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove Helpme@freespeechmail.org Ransomware?
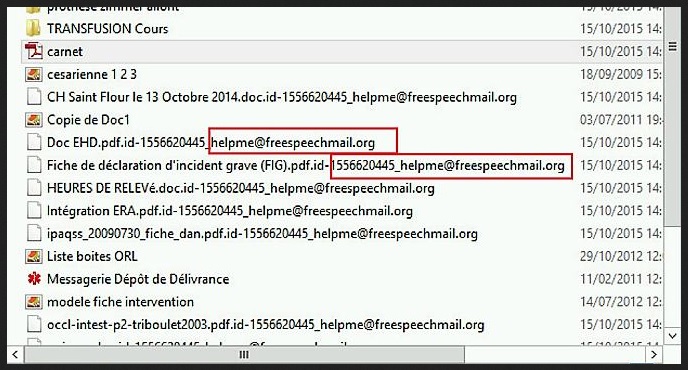
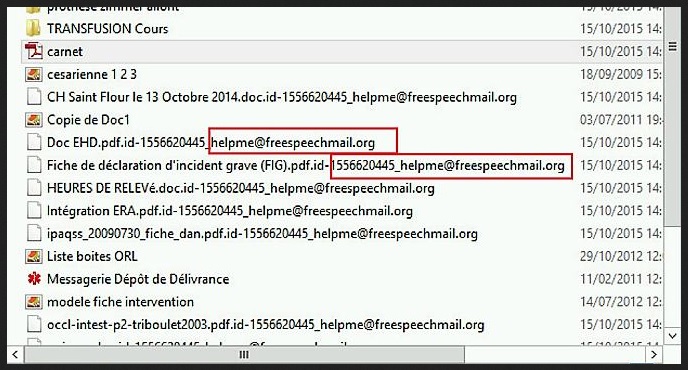
If you have been unlucky enough to get infected with ransomware, congratulations. You’ve managed to come across one of the nastiest, most vicious and most difficult to remove types of cyber parasites out there. Today our attention goes to a PC virus that not only sneaks its way into your machine via some highly unfair methods but then proceeds to encrypting your personal files thus denying you any access to your own data. It goes without saying that every single virus has to be properly uninstalled; let alone an incredibly harmful one that is shameless enough to directly demand money from you. The only reason why such infections were created in the first place was to help hackers generate profit via some illegal and highly unfair monetizing techniques. The bad news here is that crooks don’t hesitate much when it comes to profit so they will try every trick in the book in order to scam you. The good news is that you absolutely do NOT have to be a part of these shenanigans. However pesky ransomware could be, always keep in mind that there is an easy and quick way to handle the situation. Handle the parasite. These programs rely solely on the fact that you would be nervous enough to listen to the hackers’ instructions and of course, you shouldn’t allow them to manipulate you like that. Even though encrypting somebody’s private files and then having the impudence to ask for a ransom is an extremely dishonest move, that is exactly how this parasite works. And, unfortunately, it works pretty well. A lot of people lose money simply because they fail to think logically when they realize most of their data has suddenly changed file format (for example, you may notice that some random .fff format has replaced the original one). The parasite renames your files and includes “helpme@freespeechmail.org” in the name of every single file so it practically makes your data unusable. The ultimate goal here is for you to pay the sum of money demanded. To put it briefly, do NOT believe anything the virus claims and do NOT make the crucial mistake of obeying hackers. Trust us, such behavior will only result in you losing money. That’s it.
How did I get infected with?
As you probably already know (or at least you should), there are numerous ways to get infected while surfing the Web. Hackers don’t tend to give up their favorite tactics even though some of the tricks are very old and painfully unoriginal. Take for example spam email-attachments and spam messages. They are still very effective. By taking advantage of your distraction such techniques pose an immense threat to your safety and that threat is only a click away from you. Another thing you should watch out for are freeware bundles. If you have the habit of downloading free programs off of the Internet, you might want to reconsider your future online customs. First of all, avoid illegitimate websites because more often than not, their bundles include at least one potentially unwanted parasite. Secondly, don’t hesitate to uninstall every single piece of software that you don’t trust and don’t want to have installed. However, to make noticing a parasite possible, you have to select the Custom option in advance. This will allow you to pay close attention to all the programs that are trying to sneak in. Therefore, by opting for the custom installation you will not rush the download process and you will also be able to remain in control of your machine. It’s a win-win situation, isn’t it?
Why is Helpme-freespeechmail.org dangerous?
This parasite is extremely dangerous and it won’t need more than five minutes to convince you in its entire malicious potential. You may think that forcing its way into your machine via stealth and distraction is unfair enough but that is just the beginning of this program’s manipulations. Wait and see. The virus performs a full scan on your PC because it’s searching for your private information. Once it finds whatever .mp3, .gif, .xml, .txt, .jpg, .bin files you have stored on your PC, the infection encrypts them locking you out completely. From this moment on consider your files absolutely unreachable and as you can imagine, there might be some extremely important and valuable files that will fall victims to the ransomware’s harmful presence. The only way to regain access to your data, according to hackers, would be by paying some questionable sum of money in exchange for some questionable decryption key. Does it look like a scam yet? Because it is. The virus generates a message that gives you the malicious advice to pay the ransom and it also displays the helpme@freespeechmail.org email address. Stay away from it! It’s quite obvious that paying the ransom isn’t going to guarantee you anything other than the simple fact you will lose your money and hackers will get it. Cyber criminals have no reason whatsoever to take care of you and they don’t have the reputation of being people of their word so why would you take the bait so easily and let them fool you? Don’t. However stressed or worried crooks want to make you thanks to the constant pile of warning messages you will be seeing, remember – none of this is true. The parasite is nothing but a sad attempt for deceit and if you are aware of all malicious traits this virus exhibits, you will not allow its creators to scam you. You know that you cannot trust hackers, do you? Apart from the fact that paying the ransom will not give you access to your files, you should also know that all new files you install will get encrypted as well. This entire mess will affect your Internet experience and your patience so let’s discuss the current options you have. Or, should we say the ONE option you have. To put an end to this parasite’s sneaky manipulations, you have to uninstall this devious program. If you decide to do so manually, please follow the detailed removal manual guide below.
Helpme-freespeechmail.org Removal Instructions
STEP 1: Start Your Computer into Safe Mode with Networking
- Make sure you do not have any floppy disks, CDs, and DVDs inserted in your computer
- Restart the computer
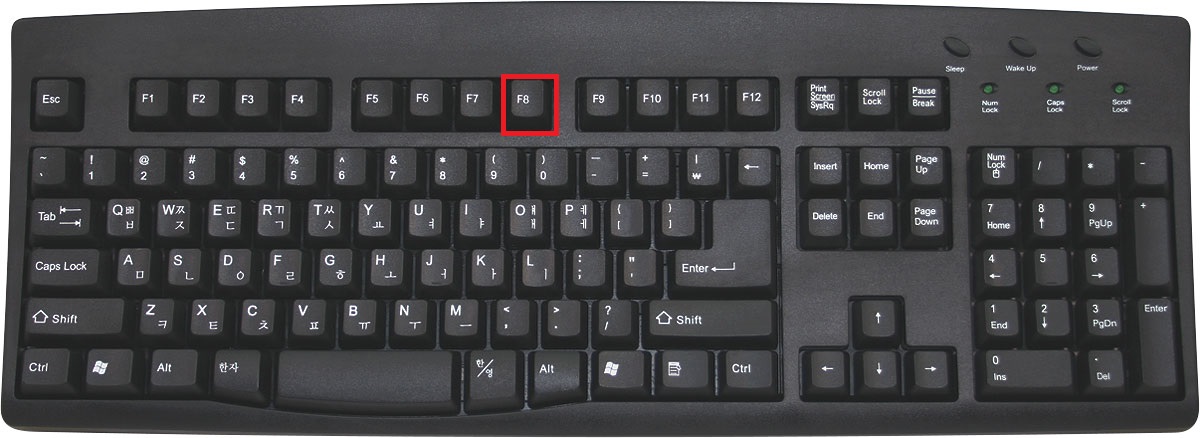
- When you see a table, start tapping the F8 key every second until you enter the Advanced Boot Options
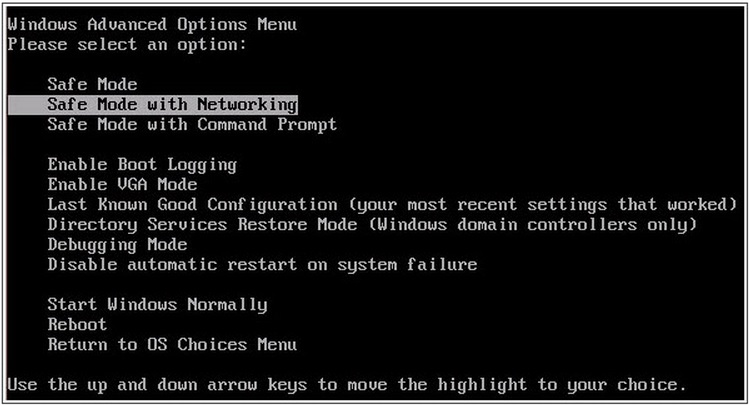
- in the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
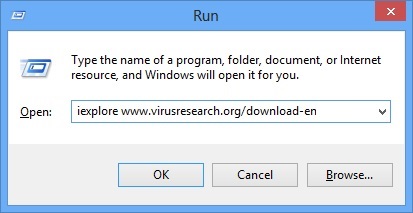
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type iexplore www.virusresearch.org/download-en
- Internet Explorer will open and a professional scanner will prompt to be downloaded
- Run the installer
- Follow the instruction and use the professional malware removal tool to detect the files of the virus.
- After performing a full scan you will be asked to register the software. You can do that or perform a manual removal.
Remove Helpme-freespeechmail.org Manually
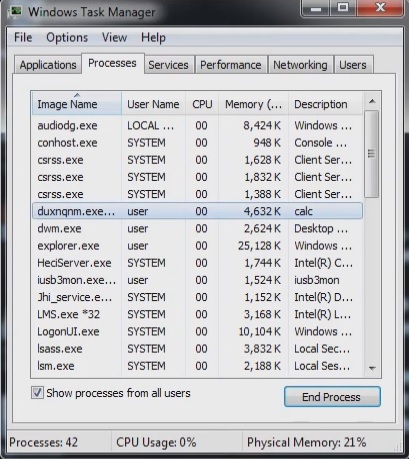
Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
Locate the process of teslacrypt. Have in mind that this is usually a random generated file.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Before you kill the process, type the name on a text document for later reference.
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you run the professional scanner to identify the files.
How to Decrypt Helpme@freespeechmail.org files
Fortunately, Kaspersky Lab has developed a program called Rakhni Decryptor that is capable of brute forcing the decryption key for the helpme@freespeechmail.org ransomware. To decrypt your files you need to download the utility directly from Kaspersky’s site and follow the instructions. You might be able to find the program elsewhere, however, we strongly suggest that you only download it from Kaspersky as they are constantly updating it for new members of this ransomware family.
It is always a good idea to use a reputable anti-malware program after manual removal, to prevent this from happening again.