Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
How to Remove hairullah@inbox.lv Ransomware?
hairullah@inbox.lv is a hazardous ransomware virus. Honestly, is there any other kind? The infection creeps into your system and encrypts everything you have stored on your computer. It makes it impossible for you to use it. You cannot browse the web, forget about accessing your data or even your Control Panel. The ransomware takes over your system entirely. After it’s done ith the encryption process, and you’re no longer in control, the situation gets even more dire. If you’re wondering how it can get any worse, it honestly can. The infection reshuffles your system settings and registry and leaves you exposed as a target for hackers. Oh, yes. Wicked, unknown third parties can, and most likely will, seek to exploit you in any way they can. They’ll gather data from you. For example, a repetitive scenario involves the tool stealing the email addresses of all of your contacts and then sending them emails bundled with viruses on your behalf. That’s how the ransomware expands its victim pool. Oh, and let’s not forget about the ‘best perk’ of all! After encrypting your files, the tool demands a ransom to decrypt it, hence its name. It’s a lose-lose situation. If you don’t pay, you lose your data. If you pay, there are no guarantees you’ll ever regain control of your system and files. Option one, the virus pulls a fast one on you and, even though you paid the ransom, it doesn’t give you a decryption key. So, you lose your data. Option two, you pay, and it gives you the key to regaining your information. But, nothing is stopping from doing the same travesty again the very next day. It can pop up and encrypt everything once more tomorrow, or the day after that. So, don’t risk it. Don’t pay! Don’t give a malicious, harmful tool access to any of your personal or financial details! Don’t be a fool! Do what’s best for you and your system, and cut your losses. It’s best to accept there’s nothing you can do, and move on than to hand over your private life to wicked strangers. Next time, create back-ups to all of your files. That way, should this situation occur, you needn’t worry.
How did I get infected with?
How do you suppose you got stuck with hairullah@inbox.lv? Well, there are a multitude of ways for this virus to slither its way into your system. However, bear in mind that each and every one of them requires you to be complicit to its installation. Oh, yes. Without you, the infection cannot gain access to your system in the first place. So, make peace with the fact that you played a significant role in its invasion. Accept you had a hand in your current predicament and misery. But don’t beat yourself up too hard. Ransomware tools are masterful when it comes to sneaking into your PC without you even realizing it. They’re immensely resourceful at finding ways to trick you into approving them in. For example, ransomware can dupe you into giving it the green light by hitching a ride with freeware, spam email attachments, corrupted sites, or links. Also, it can pretend to be a bogus update, like Java or Adobe Flash Player. Each method of infiltration, the tool turns to relies on your carelessness, which you are usually far too keen to provide. Then the tool enters your system and, once it’s in, your woes begin. To prevent the hazardous infection from invading your system, be more cautious and don’t rush. Try to remember that a little extra attention today can save you a lot of troubles tomorrow.
Why is hairullah@inbox.lv dangerous?
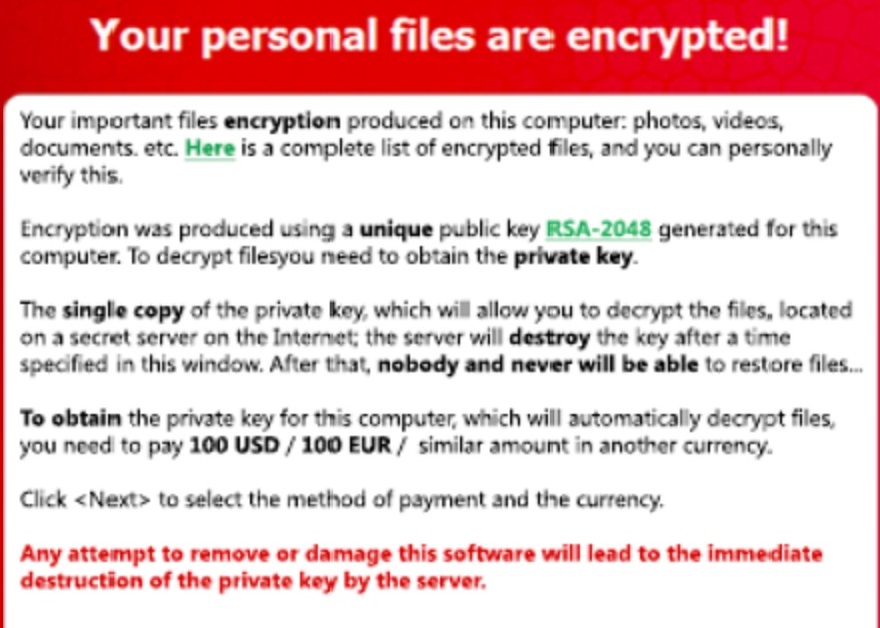
The ransomware’s attack is carried out in two phases. First one is infiltration. The tool sneaks into your system and lays low for a while. It performs a scan so as to determine its target files, i.e. every single file you have stored on your computer. It answers every question – what, when, where, which, how many, etc. The ransomware leaves no stone unturned. After it scans all of your hard drives and has a better sense of your data, it proceeds to phase two. It reveals itself. It does that by encrypting every single file you have – photos, videos, music, documents, everything. Nothing is safe. Then after it’s done, and you can no longer access anything on your PC, it displays a ransom note stating its demands. Regardless whether it wants you to pay an X amount of money, or in bitcoin, or whichever different type of payment method it requires, ignore it! Do NOT go through with the payment! Nothing good will come of it. As was already mentioned, it’s a lose-lose situation. The people behind the ransomware are not to be trusted. They’re hardly reliable, so you can’t expect them to go through with their end of the bargain. It’s best just to call it a day, and accept that hairullah@inbox.lv has won. And, you lost. Save yourself from even more headaches and unpleasantries, and just carry on knowing that your data is lost. It’s the best course of action you can take. After all, do you honestly expect anything positive to come from you paying up criminals and expecting them to keep their word? Don’t be naive.
hairullah@inbox.lv Removal Instructions
STEP 1: Start Your Computer into Safe Mode with Networking
- Make sure you do not have any floppy disks, CDs, and DVDs inserted in your computer
- Restart the computer
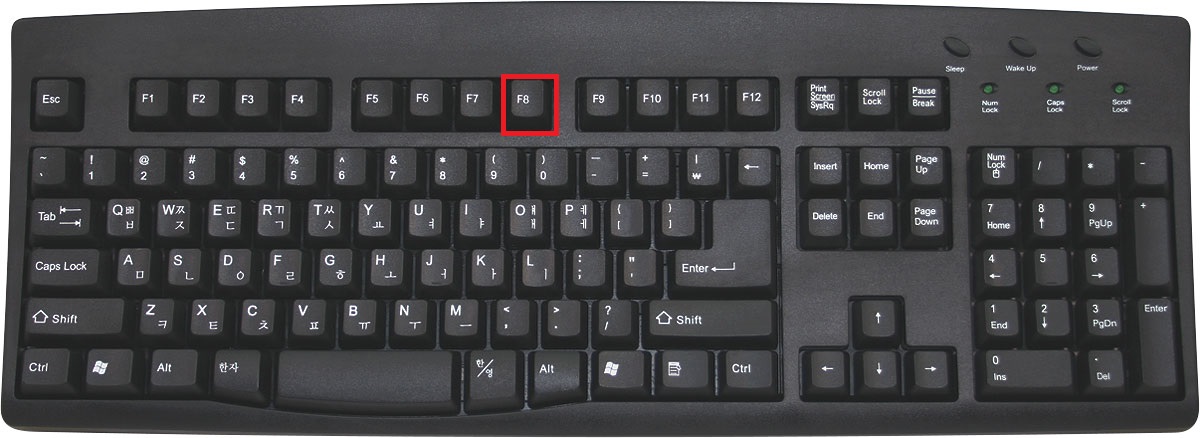
- When you see a table, start tapping the F8 key every second until you enter the Advanced Boot Options
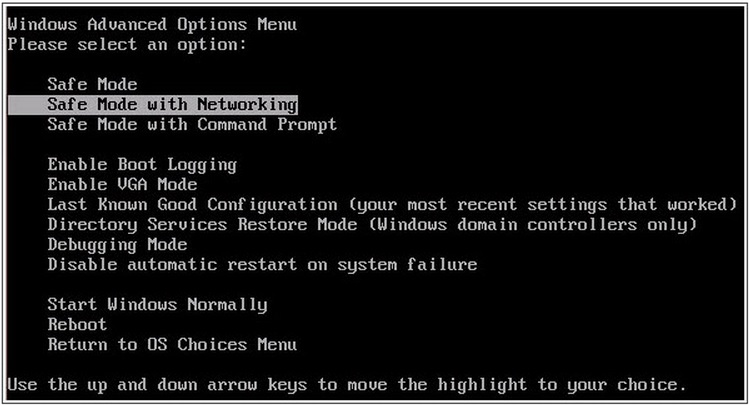
- in the Advanced Boot Options screen, use the arrow keys to highlight Safe Mode with Networking , and then press ENTER.
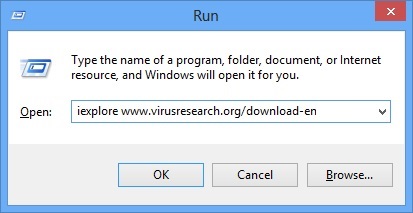
- Once the operating system loads press simultaneously the Windows Logo Button and the R key.
- A dialog box should open. Type iexplore www.virusresearch.org/download-en
- Internet Explorer will open and a professional scanner will prompt to be downloaded
- Run the installer
- Follow the instruction and use the professional malware removal tool to detect the files of the virus.
- After performing a full scan you will be asked to register the software. You can do that or perform a manual removal.
Remove hairullah@inbox.lv Manually
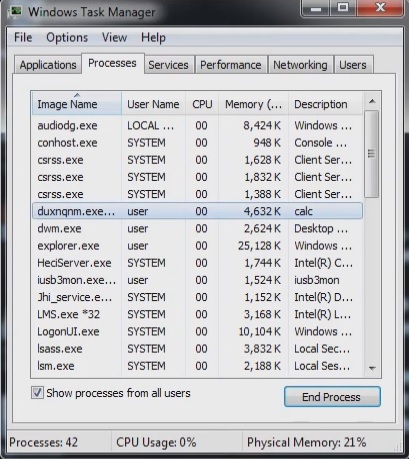
Open your task Manager by pressing CTRL+SHIFT+ESC keys simultaneously
Locate the process of teslacrypt. Have in mind that this is usually a random generated file.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Before you kill the process, type the name on a text document for later reference.
Navigate to your %appdata% folder and delete the executable.
You can alternatively use your msconfig windows program to double check the execution point of the virus. Please, have in mind that the names in your machine might be different as they might be generated randomly, that’s why you run the professional scanner to identify the files.
It is always a good idea to use a reputable anti-malware program after manual removal, to prevent this from happening again.