Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly gomovix.searchalgo.com took over your homepage and you cannot remove it.
gomovix.searchalgo.com is a browser hijacker. One day as you turn on your PC and open your browser, you’re greeted by the page. Its appearance is unexpected, unwanted, and unwelcome. If you just shrug at its sudden display, you’re only setting yourself up for a bad time. The page’s sudden, seemingly unexplained, popping up is caused by malware. Oh, yes. Your system was infiltrated by a malicious tool that’s now starting to reveal its presence by continuously imposing the gomovix.searchalgo.com site upon you. It will replace your default search engine and homepage, and every time you try to go online, you’ll be redirected to it. So, you can either get used to seeing it incessantly and endure its daily interruptions or do what’s best for you, and stop it. If you decide to allow it to stay, you’ll most certainly regret it. You’ll be subjected to constant disruptions by the page and also by an endless waterfall of pop-up advertisements. You’ll be presented with a severe malware threat, and your personal and financial information will be in grave jeopardy. Does all that sound like a pleasant experience? Do yourself a favor, and avoid all of these grievances. As soon as the page pops up for the first time, take immediate action. Find where the malware that’s forcing the site upon you is hiding, and then delete it. The sooner you locate where it’s lurking and remove it, the better. The hijacker is not worth even half the hassle it ends up causing. Get rid of it as soon as you possibly can. It’s for the best.
How did I get infected with?
The tool hiding behind gomovix.searchalgo.com is immensely skilled in the arts of deceit. Through deception and finesse, it manages to slither into your system. And, not just that, but it does so without you even being aware of it. Oh, yes. The tool is bound to ask for your permission before it installs itself, but that doesn’t slow it down one bit. It successfully gets it without you even realizing it. Right now you’re probably wondering how that’s possible. Well, the malware resorts to every trick in the book. More often than not, it sneaks in undetected with the help of the old but gold means of invasion. That includes hiding behind freeware, corrupted links or sites, or spam email attachments. It can also pretend to be a bogus program or system update. For example, you may be utterly convinced you’re updating your Java or Adobe Flash Player, but, in actuality, you’re granting access to your PC to a malicious, intrusive tool. To keep that from happening and being forced to endure the endless waterfall of issues that carelessness inevitably leads to, be more attentive! Don’t throw caution to the wind, and don’t give into naivety and haste. Remember that a little extra attention today can save you a ton of troubles tomorrow.
Why is this dangerous?
Your system was infiltrated by a malevolent tool, which seeks to take advantage of you. The malware aims to generate revenue and web traffic for malicious, unknown third parties by flooding you with endless waterfalls of pop-up ads and continuously redirecting you to the gomovix.searchalgo.com page. If you idly stand by and allow these intrusions to continue, you’ll be forced to endure frequent system crashes and a slower computer performance. But these problems will seem like non-issues compared to the fact that the hijacker can implement any and all changes throughout your system it so wishes to perform. Oh, yes. For example, if the malicious tool wants to prevent you from visiting your favorite websites, it can block your access to them. Say goodbye to Facebook, Twitter, and who knows what else. But, what’s worse, is that the hijacker can approve the installation of as many malevolent tools as it so desires without bothering to ask for your permission or to inform you. That’s because once the malware behind gomovix.searchalgo.com gets you to approve its install, it’s no longer bound to ask for you agreement. It can reshuffle anything it feels like changing, and you’ll just have to deal with it. Does that sound like the hijacker is worth keeping? Don’t hold on to something that only causes you harm and headaches. After gomovix.searchalgo.com greets you, find the malware behind it, and remove it. It’s best to delete this hazardous, damaging infection the very first chance you get.
How to Remove gomovix.searchalgo.com virus
If you perform exactly the steps below you should be able to remove the gomovix.searchalgo.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The gomovix.searchalgo.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall gomovix.searchalgo.com from Add\Remove Programs
STEP 2: Clean gomovix.searchalgo.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove gomovix.searchalgo.com leftovers from the System
STEP 1 : Uninstall gomovix.searchalgo.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
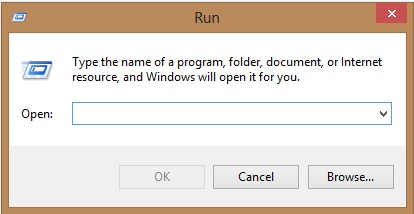
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove gomovix.searchalgo.com homepage from Chrome, Firefox and IE
-
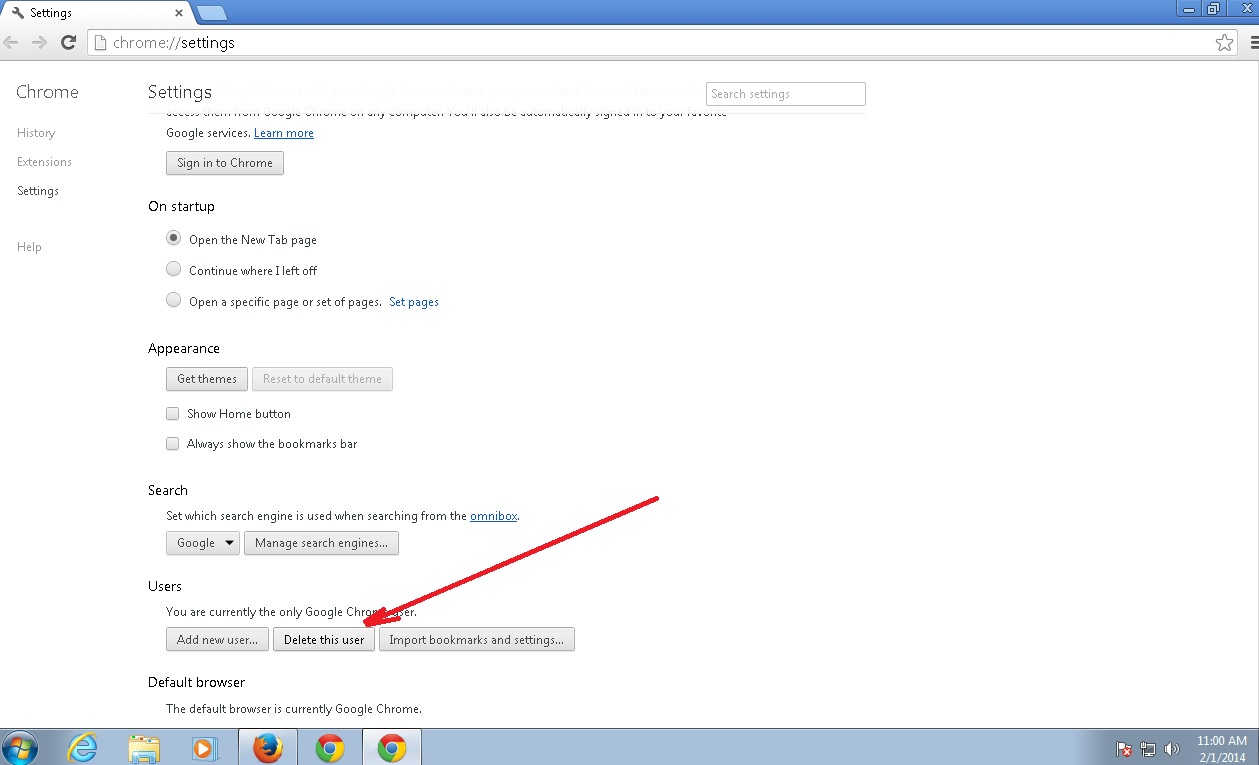
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the gomovix.searchalgo.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
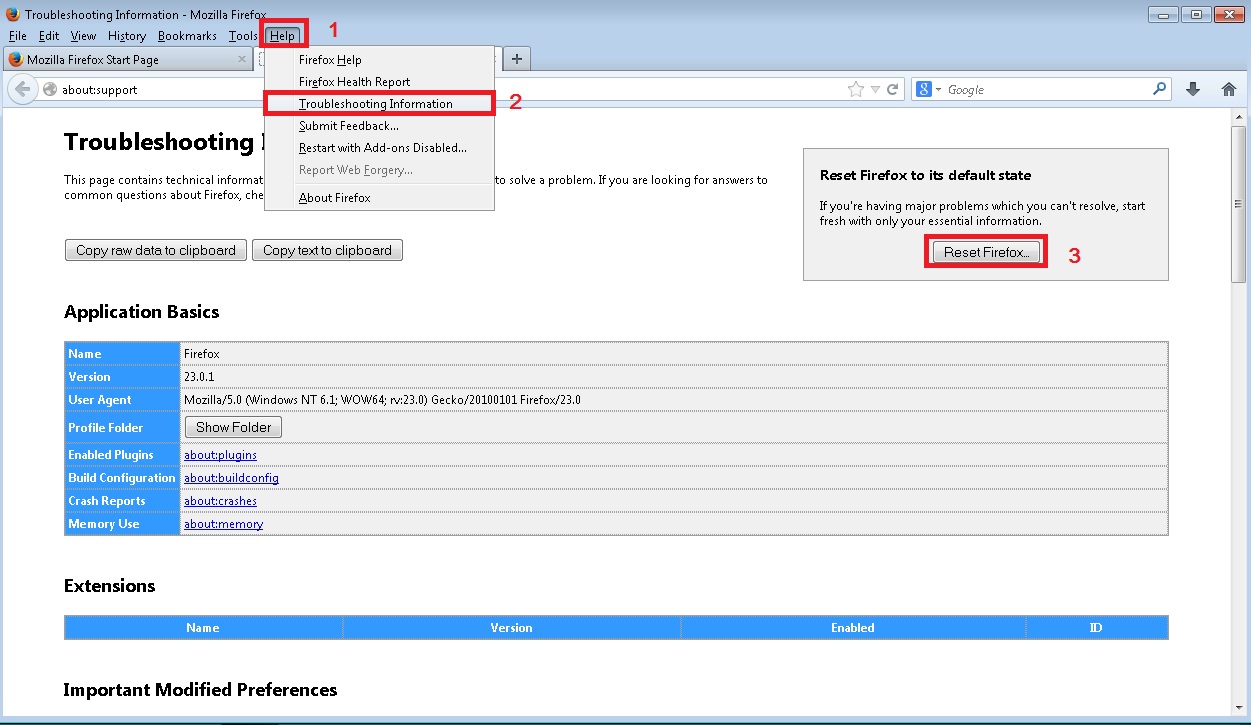
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
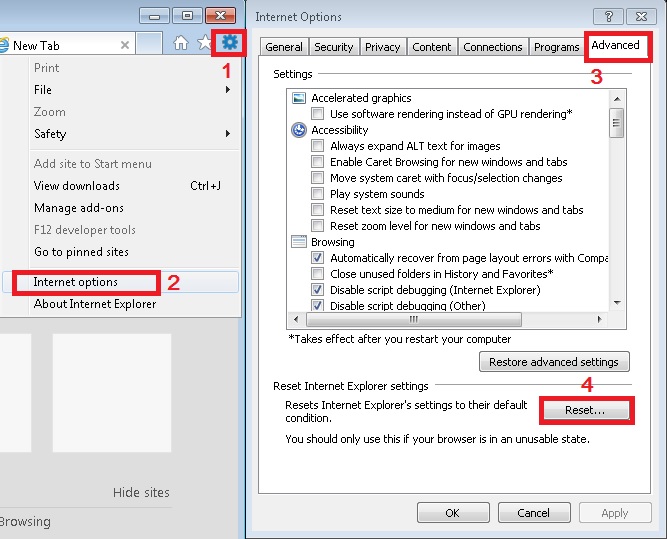
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove gomovix.searchalgo.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.