Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
Suddenly Footybase.com took over your homepage and you cannot remove it.
As you could imagine, footybase.com is unsafe. This program promises to enhance your browsing experience. On theory, it generates safe and accurate search results, thus helping you surf the Web. If it sounds too good to be true, that is because it’s a lie. Footybase.com is nothing but a nasty browser hijacker. Despite its bogus functionalities, this program has one purpose. And it doesn’t in any way involve your online experience. On the other hand, it has a lot to do with hackers’ bank account. We’ve reached the reason why hijackers get developed in the first place. These programs help crooks gain effortless revenue. Becoming rich online is every cyber criminal’s dream. Hence, it shouldn’t come as shocking news that footybase.com helps hackers gain profit. Don’t underestimate the parasite’s malicious potential. Take action instead. The sooner you uninstall this intruder, the better. As you already figured out, what a hijacker does is, it hijacks your browsers. Yes, all of them. This makes footybase.com extremely irritating and obnoxious. As soon as your device gets infected, trouble begins. The hijacker starts wreaking havoc immediately. It modifies your default browser settings and adds a nasty extension. As a result, your browsers are no longer reliable. Both your search engine and browser homepage get replaced with the parasite’s domain. You see, though, this domain isn’t safe. At the end of the day, it was created by cyber criminals. There’s no plausible scenario in which it doesn’t jeopardize your safety. The virus forces its search engine on you and destroys your online activities. Apart from the fact you won’t be able to find what you search for, footybase.com also exposes you to malware. This nuisance redirects you and generates random pop-ups. It overall slows down the PC speed as well. Your browsers might start crashing and/or freezing too. As if that wasn’t enough, footybase.com poses a direct threat to your privacy. The virus steals personal data (browsing history, search queries, even passwords and usernames). In short, this thing is a complete and utter pest. It just doesn’t belong on your computer system. Keeping in on board also means you support hackers’ malicious online business. Don’t be a sponsor of crooks and don’t underestimate this parasite’s tricks.
How did I get infected with?
Have you installed unverified software? Was it by any chance bundled? There you go. Freeware/shareware bundling is among the most efficient virus distribution methods. That means all types of parasites apply it, including Trojans and ransomware. This time you got stuck with an annoying hijacker. However, next time you may fall victim to some devastating file-encrypting pest. To prevent that, always watch out for malware. A rule of thumb for the future – avoid illegitimate websites. More often than not, there’s some sneaky “bonus” virus attached to them. Opting for the Advanced or Custom option could help you protect your PC. Yes, this is more time-consuming that simply clicking “I accept”. However, clicking the “I accept” button provides you no information whatsoever. You might agree to install a whole bunch of viruses without even knowing it. Take your time in the installation and be careful. Deselect what you don’t trust. Remember that preventing installation is much easier than having to uninstall malware. Last but not least, avoid spam messages and random emails. Be cautious online and make sure you outwit hackers every time.
Why is this dangerous?
The hijacker successfully irritates you on a daily basis. It takes control over your entire browsing experience. As mentioned already, this program adds a malicious extension to your browsers. It’s compatible with Mozilla Firefox, Google Chrome and Internet Explorer. Every time you surf the Internet, footybase.com’s domain jumps out. This program redirects you and messes with your preferred browser settings. It might install additional toolbars as well. In addition, your computer now underperforms. At the least, you will be wasting your time dealing with useless web links and questionable pages. Restrain yourself from clicking ANYTHING brought to you by the hijacker. Chances are, it’s corrupted. To prevent further damage, you have to delete footybase.com. And you have to do so quickly. Please follow our detailed removal guide down below and get rid of the virus.
How to Remove Footybase.com virus
If you perform exactly the steps below you should be able to remove the Footybase.com infection. Please, follow the procedures in the exact order. Please, consider to print this guide or have another computer at your disposal. You will NOT need any USB sticks or CDs.
The Footybase.com adware is specifically designed to make money. It generates web traffic, collects sales leads for other dubious sites, and will display advertisements and sponsored links within your web browser.
Please, have in mind that SpyHunter offers a free 7-day Trial version with full functionality. Credit card is required, no charge upfront.
STEP 1: Uninstall Footybase.com from Add\Remove Programs
STEP 2: Clean Footybase.com from Chrome Firefox or Internet Explorer
STEP 3: Permanently Remove Footybase.com leftovers from the System
STEP 1 : Uninstall Footybase.com from your computer
Simultaneously press the Windows Logo Button and then “R” to open the Run Command Window
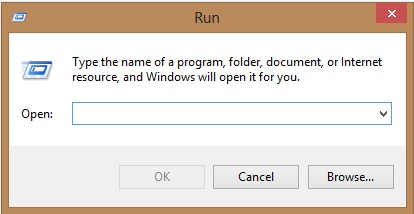
Type “regedit”
navigate to HKCU\software\Microsoft\Internet Explorer\Main
Modify the string with a value data and set it to google.com for example.
STEP 2 : Remove Footybase.com homepage from Chrome, Firefox and IE
-
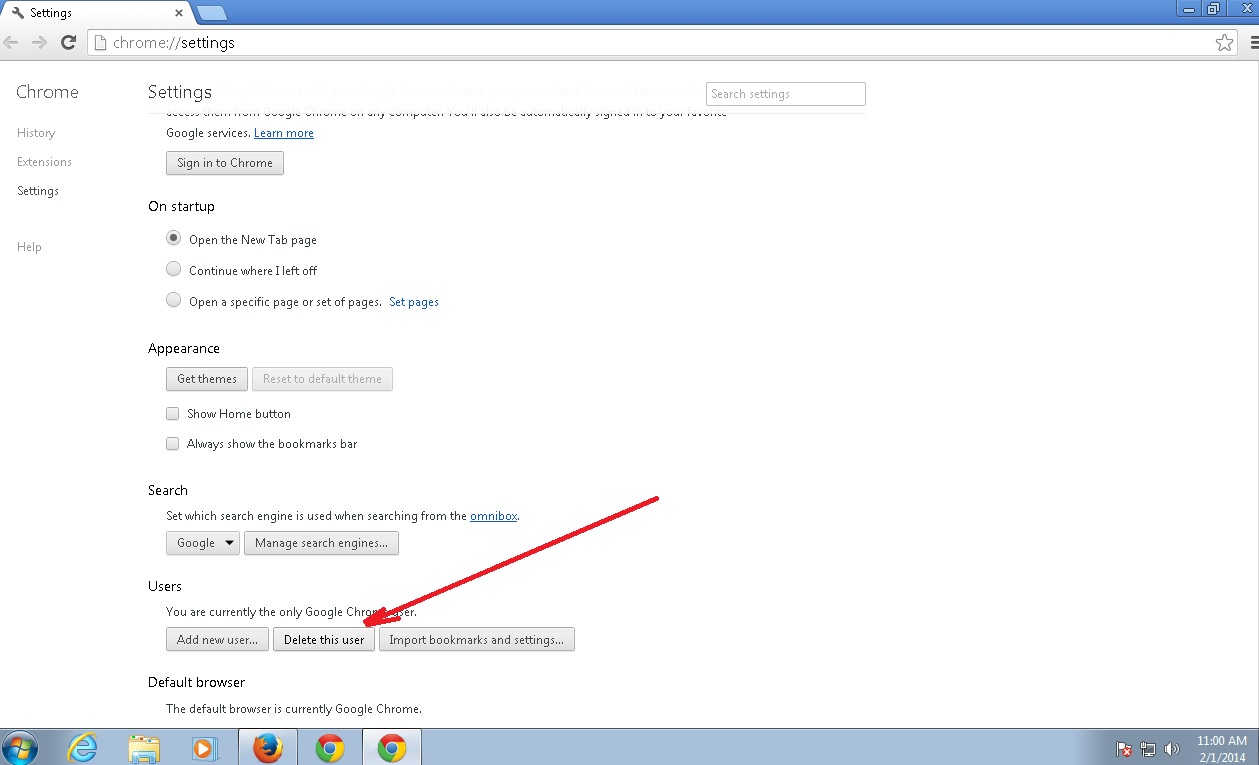
Open Google Chrome
- In the Main Menu, select Tools then Extensions
- Remove the Footybase.com by clicking on the little recycle bin
- Reset Google Chrome by Deleting the current user to make sure nothing is left behind
-
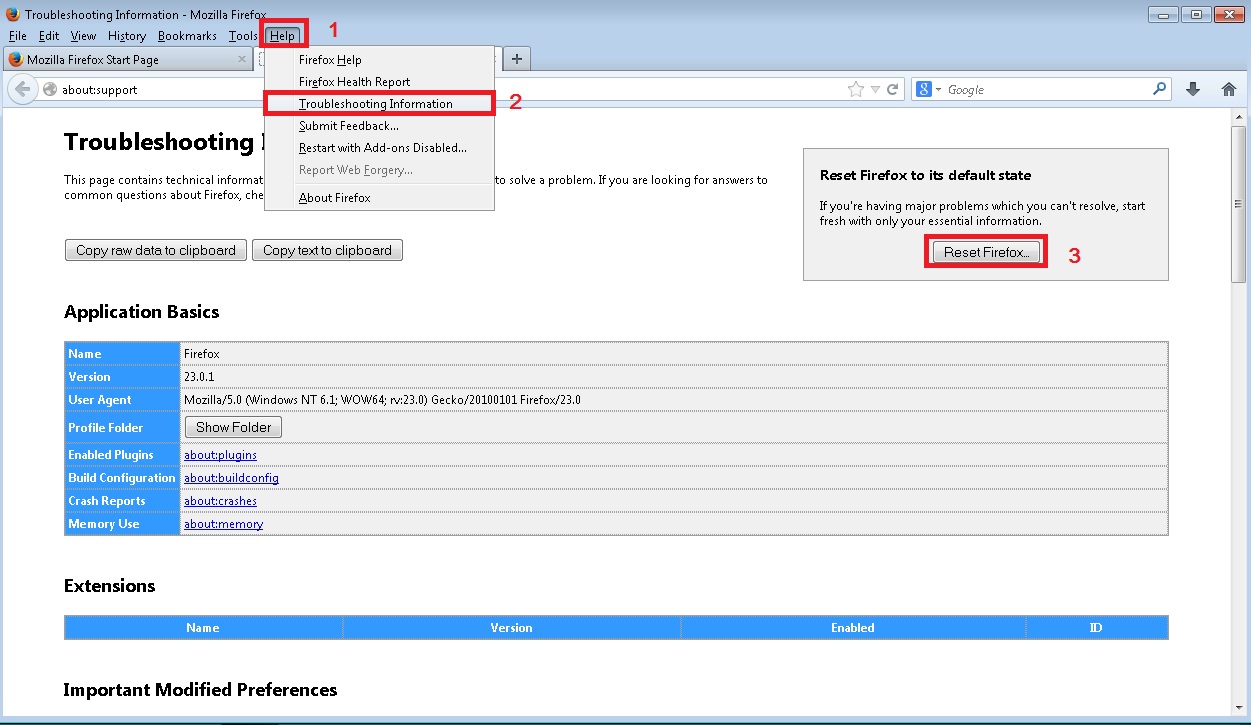
Open Mozilla Firefox
- Press simultaneously Ctrl+Shift+A
- Disable the unwanted Extension
- Go to Help
- Then Troubleshoot information
- Click on Reset Firefox
-
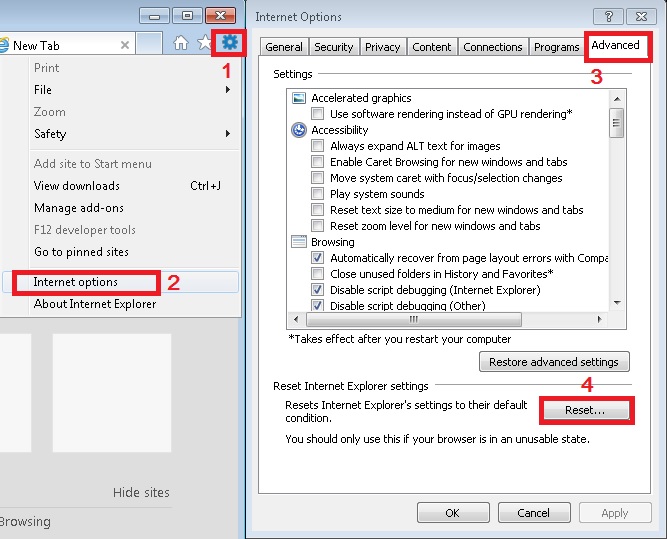
Open Internet Explorer
- On the Upper Right Corner Click on the Gear Icon
- Click on Internet options
- go to Toolbars and Extensions and disable the unknown extensions
- Select the Advanced tab and click on Reset
- Restart Internet Explorer
How to Permanently Remove Footybase.com Virus (automatic) Removal Guide
To make sure manual removal is successful, we recommend to use a free scanner of any professional antimalware program to identify possible registry leftovers or temporary files.